EC-Council Network Security Administrator (Exam 312-38)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Usability and Security of Personal Firewalls
Usability and Security of Personal Firewalls Almut Herzog^ and Nahid Shahmehri^ Dept. of Computer and Information Science, Linkopings universitet,Sweden {almhe, nahsh}@ida.liu.se Abstract. Effective security of a personal firewall depends on (1) the rule granularity and the implementation of the rule enforcement and (2) the correctness and granularity of user decisions at the time of an alert. A misconfigured or loosely configured firewall may be more dangerous than no firewall at all because of the user's false sense of security. This study assesses effective security of 13 personal firewalls by comparing possible granularity of rules as well as the usability of rule set-up and its influence on security. In order to evaluate usability, we have submitted each firewall to use cases that require user decisions and cause rule creation. In order to evaluate the firewalls' security, we analysed the created rules. In ad dition, we ran a port scan and replaced a legitimate, network-enabled application with another program to etssess the firewalls' behaviour in misuse cases. We have conducted a cognitive walkthrough paying special attention to user guidance and user decision support. We conclude that a stronger emphasis on user guidance, on conveying the design of the personal firewall application, on the principle of least privilege and on implications of default settings would greatly enhance both usability and security of personal firewalls. 1 Introduction In times where roaming users connect their laptops to a variety of public, pri vate and corporate wireless or wired networks and in times where more and more computers are always online, host-based firewalls implemented in soft ware, called personal firewalls, have become an important part of the security armour of a personal computer. -

Mikogo & Personal Firewalls
Mikogo & Personal Firewalls - ZoneAlarm Create an Exception Rule If you use ZoneAlarm personal firewall on your PC and you are having trouble using the Mikogo software you might have to first create an Exception Rule for Mikogo. In case you receive the following message and you use ZoneAlarm, please proceed as described below. Click on the ZoneAlarm icon in your system tray next to your computer clock. The ZoneAlarm main window will appear. In the vertical navigation on the left-hand side, click on Program Control. Mikogo & Personal Firewalls – ZoneAlarm Page 2 The ZoneAlarm Program Control will open. Click on the Programs tab. Click on Add. Browse to the mikogo-starter executable file, highlight it and click Open. Mikogo & Personal Firewalls – ZoneAlarm Page 3 Mikogo will then appear in the Programs list. Click in the Access column and choose Allow. Mikogo & Personal Firewalls – ZoneAlarm Page 4 Run a Connection Test Go to the Mikogo homepage and click on Join Session. When prompted enter 000-000-000 as the session ID and your name. Then click Join Session. Alternatively you can open the software on your computer. To do so, click on Start menu > Mikogo > Mikogo > to open and run the software. The panel will appear on your screen. Click on the button and enter the 000-000-000 session ID and your name. Then click Join Session. The following message will appear confirming that you can establish a connection with Mikogo: Mikogo & Personal Firewalls – ZoneAlarm Page 5 . -

Personal Firewalls Are a Necessity for Solo Users
Personal firewalls are a necessity for solo users COMPANY PRODUCT PLATFORM NOTES PRICE Aladdin Knowledge Systems Ltd. SeSafe Desktop Windows Combines antivirus with content filtering, blocking and $72 Arlington Heights, Ill. monitoring 847-808-0300 www.ealaddin.com Agnitum Inc. Outpost Firewall Pro Windows Blocks ads, sites, programs; limits access by specific times $40 Nicosia, Cyprus www.agnitum.com Computer Associates International Inc. eTrust EZ Firewall Windows Basic firewall available only by download $40/year Islandia, N.Y. 631-342-6000 my-etrust.com Deerfield Canada VisNetic Firewall Windows Stateful, packet-level firewall for workstations, mobile $101 (Canadian) St. Thomas, Ontario for Workstations users or telecommuters 519-633-3403 www.deerfieldcanada.ca Glucose Development Corp. Impasse Mac OS X Full-featured firewall with real-time logging display $10 Sunnyvale, Calif. www.glu.com Intego Corp. NetBarrier Personal Firewall Windows Full-featured firewall with cookie and ad blocking $50 Miami 512-637-0700 NetBarrier 10.1 Mac OS X Full-featured firewall $60 www.intego.com NetBarrier 2.1 Mac OS 8 and 9 Full-featured firewall $60 Internet Security Systems Inc. BlackIce Windows Consumer-oriented PC firewall $30 Atlanta 404-236-2600 RealSecure Desktop Windows Enterprise-grade firewall system for remote, mobile and wireless users Varies blackice.iss.net/ Kerio Technologies Inc. Kerio Personal Firewall Windows Bidirectional, stateful firewall with encrypted remote-management option $39 Santa Clara, Calif. 408-496-4500 www.kerio.com Lava Software Pty. Ltd. AdWare Plus Windows Antispyware blocks some advertiser monitoring but isn't $27 Falköping, Sweden intended to block surveillance utilities 46-0-515-530-14 www.lavasoft.de Network Associates Inc. -

Master's Thesis
Eindhoven University of Technology MASTER Securing the home network Stelma, J. Award date: 2015 Link to publication Disclaimer This document contains a student thesis (bachelor's or master's), as authored by a student at Eindhoven University of Technology. Student theses are made available in the TU/e repository upon obtaining the required degree. The grade received is not published on the document as presented in the repository. The required complexity or quality of research of student theses may vary by program, and the required minimum study period may vary in duration. General rights Copyright and moral rights for the publications made accessible in the public portal are retained by the authors and/or other copyright owners and it is a condition of accessing publications that users recognise and abide by the legal requirements associated with these rights. • Users may download and print one copy of any publication from the public portal for the purpose of private study or research. • You may not further distribute the material or use it for any profit-making activity or commercial gain Department of Mathematics and Computer Science Architecture of Information Systems Research Group Securing the Home Network Master Thesis Jaap Stelma Supervisor: dr. D.S. (Dmitri) Jarnikov PDEng Graduation Committee: prof.dr. J.J. (Johan) Lukkien dr. D.S. (Dmitri) Jarnikov PDEng dr. J.I. (Jerry) Hartog, den Version: 1.2 (10 August 2015) Publication Date: 31 August 2016 Eindhoven, August 2015 Abstract Network security is protection and precaution taken against breaches of confidentiality, integrity, availability, authenticity, and accountability. The core technologies required to protect against the threads are identification and access control. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -
Sunbelt Personal Firewall User Guide
Use of this software is subject to the End User License Agreement found in this User Guide (the License Agreement). By installing the software, you agree to accept the terms of the License Agreement. Copyright (c) 2008 Sunbelt Software. All rights reserved. All products mentioned are trademarks or registered trademarks of their respective companies. Information in this document is subject to change without notice. No part of this publication may be reproduced, photocopied, stored in a retrieval system, transmitted, or translated into any language without the prior written permission of Sunbelt Software, Inc. Sunbelt Personal Firewall User Guide Contents Introduction .......................................................................................... 1-1 Before You Start .............................................................................................................1-2 Overview .........................................................................................................................1-2 Components ...................................................................................................................1-3 Functions and Features ..................................................................................................1-4 System Requirements ....................................................................................................1-4 Conflicting Software ........................................................................................................1-5 Styles and References -

NCP Dynamic Personal Firewall (Win32/64)
Data Sheet NCP Dynamic Net Guard Centrally administrable Personal Firewall for Windows 32/64 Bit operating systems . Central Management and Network Access Control . For company PCs and within the corporate network or at workstation PCs via VPN . Location awareness through Friendly Net Detection for dynamic adaption of firewall rules . Immediate protection of the end-device from system startup onwards . Silent Mode . Free-of-charge 30 day trial version Client (Local Awareness) and thus ensures recognition of a friendly network at any rate. Scope of supply and features Various firewall rules may be created for ports, IP addresses, segments or applications. Furthermore it is NCP’s Dynamic Net Guard (Win32/64) complements possible to define whether internet access is allowed NCP’s “Next Generation Network Access Technology”- (generally or for selected websites only) and/ or the holistic Secure Communications Solution. It whether the corporate network may be accessed protects laptops, notebooks, netbooks, tablet PCs and exclusively. It is possible for the administrator to lock desktop PCs with Windows 32/64 Bit operating all client settings so that the user may not alter any of systems - Windows 7, Windows Vista, Windows XP – them. This excludes deliberate manipulation or from unauthorized access. The end-device is always misconfiguration by the user. protected against attacks, be it mobile or stationary, Since the NCP firewall is immediately active at system be it on the internet, in a Wi-Fi network or in a LAN. startup of the mobile or stationary end-device, this Depending on the location different firewall rules severe security gap is tightly sealed. -

Ethical Hacking and Countermeasures Version 6
Ethical Hacking and Countermeasures Version 6 Modu le LX Firewall Technologies News Source: http://www.internetnews.com/ Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Module Objective This modu le will fam iliar ize you wihith: • Firewalls • Hardware Firewalls • Software Firewalls • Mac OS X Firewall • LINUX Firewall • Windows Firewall Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Module Flow Firewalls Mac OS X Firewall Hardware Firewalls LINUX Firewall Software Firewalls Windows Firewall Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Firewalls: Introduction A firewall is a program or hardware device that protects the resources of a private netw ork from users of other networks It is responsible for the traffic to be allowed to pass, block, or refuse Firewall also works with the proxy server It helps in the protection of the private network from the users of the different network Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Hardware Firewalls Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Hardware Firewall Har dware Firewa lls are place d in the perime ter of the networ k It employs a technique of packet filtering It reads the header of a packet to find out the source and destination address The information is then compared with the set of predefined and/orand/ or user created rules that determine whether the packet is forwarded or dropped Copyright © by EC-Council EC-Council All Rights Reserved. Reproduction is Strictly Prohibited Netgear Firewall Features: • ItInterne t shar ing broa dbddband router and 4-port switch • 2x the speed and 4x times the coverage of a Wireless-G router • Configurable for private networks and public hotspots • Double Firewall protection from external hackers attacks • Touchless WiFi Security makes it easy to secure your network Copyright © by EC-Council EC-Council All Rights Reserved. -

Firewalls Firewall I Firewall Sono Una Componente O Un Insieme Di Componenti Che Limitano L'accesso Tra Una Rete Protetta Ed In
For TIC Pagina 1 di 4 Firewalls Firewall I firewall sono una componente o un insieme di componenti che limitano l'accesso tra una rete protetta ed Internet. Essi proteggono le organizzazioni in Internet fornendo accessi sicuri: garantendo che utenti validi possano accedere alle risorse di rete di cui hanno bisogno. Determinare chi sia un utente valido è compito del sistema di autenticazione; mentre determinare quali risorse un utente possa accedere è compito del sistema di autorizzazione (Access Control). Per fornire meccanismi di Access Control, un firewall richiede una comprensione profonda dei servizi e delle applicazioni utilizzati in rete. Ci sono fondamentalmente due tipi di firewall, quelli personali e quelli commerciali. I firewall personali I firewall personali sono programmi che proteggono un computer quando questo è collegato ad una rete. Un personal firewall analizza i canali di comunicazione, negando l'elaborazione del traffico ritenuto rischioso sia in ingresso che in uscita. Di seguito si analizzano le caratteristiche di alcuni prodotti molto diffusi e si riassumono le caratteristiche comparate, in una tabella. z Tiny Personal Firewall è un prodotto facile da configurare ed utilizzare che protegge completamente un computer dagli attacchi. Tiny Personal Firewall include dei wizard semplici per il rilevamento delle intrusioni che individuano attività sconosciute e chiedono all'utente di impostare i parametri del firewall. Appositi wizard rilevano i tentativi di connessione alle porte di comunicazione e creano delle regole di filtering in base all'indicazioni dell'utente. Per garantire che dei cavalli di Troia non si nascondano all'interno di applicazioni viene utilizzata la firma digitale con algoritmo MD5. -

Virtualized Network Security with VPN-1 Power VSX
Virtualized Network Security with VPN-1A better approach Power to securing VSX networks Virtualized Network Security with VPN-1 Power VSX Contents Executive summary ………………………………………………………… 3 Introduction to virtualization ……………………………………………… 4 Check Point VPN-1 Power VSX …………………………………………… 4 Components virtualized by VPN-1 Power VSX code …………………… 5 Layer-2 security …………………………………………………………… 5 ARP poisoning ……………………………………………………………… 6 VLAN hopping ……………………………………………………………… 6 Platforms …………………………………………………………………… 6 Crossbeam Systems ……………………………………………………… 6 Check Point SecurePlatform ……………………………………………… 7 Virtual network environment ……………………………………………… 7 Application layer protection ……………………………………………… 8 Availability, reliability, and scalability ……………………………………… 8 Quality of Service …………………………………………………………… 10 Secure provisioning ………………………………………………………… 10 Secure Management Architecture ………………………………………… 11 Management challenges …………………………………………………… 11 Security classes …………………………………………………………… 13 Permission enforcement …………………………………………………… 14 Conclusion ………………………………………………………………… 15 Virtualized Network Security with VPN-1 Power VSX Executive summary Network complexity is growing rapidly. Dynamic business requirements, mergers, spinoffs, new services, new business units, new threats, and compliance considerations are driving an ever-increasing investment in network resources, equipment, and invasive infrastructure changes. The result is often a higher cost structure combined with lower network and service availability. Companies are realizing the advantages -
Guidelines on Firewalls and Firewall Policy
Special Publication 800-41 Revision 1 Guidelines on Firewalls and Firewall Policy Recommendations of the National Institute of Standards and Technology Karen Scarfone Paul Hoffman NIST Special Publication 800-41 Guidelines on Firewalls and Firewall Revision 1 Policy Recommendations of the National Institute of Standards and Technology Karen Scarfone Paul Hoffman C O M P U T E R S E C U R I T Y Computer Security Division Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899-8930 September 2009 U.S. Department of Commerce Gary Locke, Secretary National Institute of Standards and Technology Patrick D. Gallagher, Deputy Director GUIDELINES ON FIREWALLS AND FIREWALL POLICY Reports on Computer Systems Technology The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the U.S. economy and public welfare by providing technical leadership for the nation’s measurement and standards infrastructure. ITL develops tests, test methods, reference data, proof of concept implementations, and technical analysis to advance the development and productive use of information technology. ITL’s responsibilities include the development of technical, physical, administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. This Special Publication 800-series reports on ITL’s research, guidance, and outreach efforts in computer security and its collaborative activities with industry, government, and academic organizations. National Institute of Standards and Technology Special Publication 800-41 Revision 1 Natl. Inst. Stand. Technol. Spec. Publ. 800-41 rev1, 48 pages (Sep. 2009) Certain commercial entities, equipment, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. -
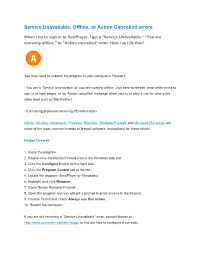
"Service Unavailable" Error, Contact Norton at to Find out How to Configure It Correctly
Service Unavailable, Offline, or Action Cancelled errors When I try to sign in to RealPlayer, I get a "Service Unavailable," "You are currently offline," or "Action cancelled" error. How can I fix this? You may need to unblock the program in your computer's firewall if: - You get a 'Service Unavailable' or 'you are working offline, click here to refresh' error while trying to sign in or view pages, or an 'Action cancelled' message when you try to play a clip (or view a live video feed such as Big Brother). - It is having problems retrieving CD information Norton, McAfee, ZoneAlarm, Freedom, BlackIce, Windows Firewall, and Microsoft ISA server are some of the most common brands of firewall software. Instructions for these follow: Norton Firewall: 1. Close the program. 2. Double-click the Norton Firewall icon in the Windows task bar. 3. Click the Configure button on the right side. 4. Click the Program Control tab at the top. 5. Locate the program (RealPlayer or Rhapsody). 6. Highlight and click Remove. 7. Close Norton Personal Firewall. 8. Open the program and you will get a prompt to grant access to the Internet. 9. Choose Permit and check Always use this action. 10. Restart the computer. If you are still receiving a "Service Unavailable" error, contact Norton at http://www.symantec.com/techsupp/ to find out how to configure it correctly. McAfee Personal Firewall: There are two possible methods for McAfee Personal Firewall. You can choose either one: First method: 1. Double-click the firewall icon in the Windows task bar.