An A-Z Index of the Windows CMD Command Line
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Tools for Managing Acls Jesper M Johansson
Security watch Tools for managing ACLs Jesper M Johansson Before I go into how to save or re- In Windows, access control lists (ACLs) store ACLs, let me first explore why it is so difficult. Let’s say you have a hier- give you extremely fine control over archy containing user data for students at a local college. You save the ACL on the ability of users and processes to 1 February. On 17 April you discover that somehow the ACL has been cor- use resources such as files and folders. rupted and you go to restore it from the saved copy. What complications Managing ACLs can be one of the more could there be with this operation? First, the new quarter started on complicated tasks related to protecting the 2 April. About 15 per cent of your students graduated; consequently, security of your users’ systems. Fortunately, their directories no longer exist. Thus, you have ACLs in the backup file that there are a number of useful utilities are invalid. You also have a batch of new students, another 15 per cent, that that help automate and simplify tasks granular permissions introduced with started with the new quarter. They surrounding permissions and ACLs. Windows 2000, making this an update have home directories now, but no Most readers are familiar with the that is about seven years overdue. ACLs in the backup file. What should venerable cacls.exe tool that has been Surprisingly, in spite of being dep- their ACLs be? Then of course you in every version of Windows NT since recated, cacls.exe does actually include have the 70 per cent that are still there, it first came out. -
Restoration Onto Different Hardware (PDF)
Restoration onto different Hardware Quick and easy system restore with O&O DiskImage Table of contents System restoration using boot media ...................................................................................... 1 Restoration onto different hardware ....................................................................................... 2 Limitations when restoring onto different hardware ................................................................................................................. 3 Automatic update............................................................................................................................... ............................................. 3 Manual adaptation .......................................................................................................................................................................... 4 Enable automatic adaptation on changed hardware (M.I.R.) .................................................................................................... 4 Assistance when error messages occur during booting .......................................................... 7 I System restoration using boot media Disks where you save your private and business data can be quickly imaged and restored in the event of a crash or hardware damage. Creating an image of your entire computer or the system partition is also very easy. To restore an image of a Windows system, you’ll need to start O&O DiskImage directly from a bootable medium *. *Note You’ll need to -

Ubuntu Kung Fu
Prepared exclusively for Alison Tyler Download at Boykma.Com What readers are saying about Ubuntu Kung Fu Ubuntu Kung Fu is excellent. The tips are fun and the hope of discov- ering hidden gems makes it a worthwhile task. John Southern Former editor of Linux Magazine I enjoyed Ubuntu Kung Fu and learned some new things. I would rec- ommend this book—nice tips and a lot of fun to be had. Carthik Sharma Creator of the Ubuntu Blog (http://ubuntu.wordpress.com) Wow! There are some great tips here! I have used Ubuntu since April 2005, starting with version 5.04. I found much in this book to inspire me and to teach me, and it answered lingering questions I didn’t know I had. The book is a good resource that I will gladly recommend to both newcomers and veteran users. Matthew Helmke Administrator, Ubuntu Forums Ubuntu Kung Fu is a fantastic compendium of useful, uncommon Ubuntu knowledge. Eric Hewitt Consultant, LiveLogic, LLC Prepared exclusively for Alison Tyler Download at Boykma.Com Ubuntu Kung Fu Tips, Tricks, Hints, and Hacks Keir Thomas The Pragmatic Bookshelf Raleigh, North Carolina Dallas, Texas Prepared exclusively for Alison Tyler Download at Boykma.Com Many of the designations used by manufacturers and sellers to distinguish their prod- ucts are claimed as trademarks. Where those designations appear in this book, and The Pragmatic Programmers, LLC was aware of a trademark claim, the designations have been printed in initial capital letters or in all capitals. The Pragmatic Starter Kit, The Pragmatic Programmer, Pragmatic Programming, Pragmatic Bookshelf and the linking g device are trademarks of The Pragmatic Programmers, LLC. -

Užitečné Postupy Pro Windows a Office Nepublikované V Oficiální Literatuře Artur Cimbálník
UNIVERZITA PARDUBICE Fakulta elektrotechniky a informatiky Užitečné postupy pro Windows a Office nepublikované v oficiální literatuře Artur Cimbálník Bakalářská práce 2011 Prohlášení autora Prohlašuji, ţe jsem tuto práci vypracoval samostatně. Veškeré literární prameny a informace, které jsem v práci vyuţil, jsou uvedeny v seznamu pouţité literatury. Byl jsem seznámen s tím, ţe se na moji práci vztahují práva a povinnosti vyplývající ze zákona č. 121/2000 Sb., autorský zákon, zejména se skutečností, ţe Univerzita Pardubice má právo na uzavření licenční smlouvy o uţití této práce jako školního díla podle § 60 odst. 1 autorského zákona, a s tím, ţe pokud dojde k uţití této práce mnou nebo bude poskytnuta licence o uţití jinému subjektu, je Univerzita Pardubice oprávněna ode mne poţadovat přiměřený příspěvek na úhradu nákladů, které na vytvoření díla vynaloţila, a to podle okolností aţ do jejich skutečné výše. Souhlasím s prezenčním zpřístupněním své práce v Univerzitní knihovně. V Pardubicích dne 29. 04. 2011 Artur Cimbálník Poděkování Tímto bych chtěl poděkovat doc. Ing Milanu Javůrkovi, CSc., vedoucímu mé bakalářské práce za pomoc při shánění materiálu a jeho rady při psaní tohoto textu. Anotace Práce se zabývá testováním postupů racionalizujících práci ve Windows a programech Microsoft Office. Jsou zde popsány jednotlivé pracovní postupy doplněné grafickými obrazovkami a popisem dané problematiky. Dále hodnotí jednotlivé verze kancelářských balíků Microsoft Office. Klíčová slova Office, Word, Excel, Windows, tipy, postupy, rady Title Useful procedures for Windows and Office unpublished in the official literature. Annotation Bachelor thesis deals with the testing of procedures rationalizing work in Windows and Microsoft Office. There are describing individual work procedures with graphic screens. -

Exam 70-797: Configuring Windows Devices (Pilot) – Skills Measured
Exam 70-797: Configuring Windows Devices (pilot) – Skills Measured Audience Profile This exam validates a candidate’s fundamental knowledge and skills for building solid identities, protection of content (data loss protection), mobile device management policy, virtualization with Hyper-V, application management using the Company Portal and the Windows Store. Candidates will be evaluated on Windows 10 security and integrated Azure features. In addition to their professional experience, candidates who take this exam should already have the following technical knowledge: Experience with Windows desktop administration, maintenance, and troubleshooting Basic experience and understanding of Windows networking technologies Introductory-level knowledge of Active Directory and Microsoft Intune Candidates can take this exam and meet the prerequisites by obtaining equivalent knowledge and skills through practical experience as a Windows device support technician or a Windows device system administrator. Skills Measured NOTE: The bullets that appear below each of the skills measured are intended to illustrate how we are assessing that skill. This list is not definitive or exhaustive. NOTE: In most cases, exams do NOT cover preview features, and some features will only be added to an exam when they are GA (General Availability). Manage identity (13%) Support Windows Store and cloud apps install and manage software by using Microsoft Office 365 and Windows Store apps, sideload apps by using Microsoft Intune, sideload apps into online and offline images, deeplink apps by using Microsoft Intune, integrate Microsoft account including personalization settings Support authentication and authorization identifying and resolving issues related to the following: Multi-factor authentication including certificates, Microsoft Passport, virtual smart cards, picture passwords, and biometrics; workgroup vs. -

Eaton Intelligent Power® Protector User’S Guide
Eaton Intelligent Power® Protector User’s Guide Eaton Intelligent Power® Protector – User’s Guide – / AI-1.28 www.eaton.com Table of Contents 1 Introduction .................................................................................................................. 4 2 Installation .................................................................................................................... 5 2.1 Installation Prerequisites .................................................................................................................. 5 2.1.1 On the System Hosting « Intelligent Power® Protector » .............................................................. 5 2.1.2 On the System that Displays Web-based Graphical User Interface............................................. 6 2.2 Quick Start & Installation .................................................................................................................. 7 2.3 Windows Installation ......................................................................................................................... 9 2.3.1 Graphical installation .................................................................................................................... 9 2.3.2 Installation / Uninstallation from command line .......................................................................... 10 2.3.3 Uninstalling the Product .............................................................................................................. 11 2.4 Linux Installation ............................................................................................................................. -

This Document Explains How to Copy Ondemand5 Data to Your Hard Drive
Copying Your Repair DVD Data To Your Hard Drive Introduction This document explains how to copy OnDemand5 Repair data to your hard drive, and how to configure your OnDemand software appropriately. The document is intended for your network professional as a practical guide for implementing Mitchell1’s quarterly updates. The document provides two methods; one using the Xcopy command in a DOS window, and the other using standard Windows Copy and Paste functionality. Preparing your System You will need 8 Gigabytes of free space per DVD to be copied onto a hard drive. Be sure you have the necessary space before beginning this procedure. Turn off screen savers, power down options or any other program that may interfere with this process. IMPORTANT NOTICE – USE AT YOUR OWN RISK: This information is provided as a courtesy to assist those who desire to copy their DVD disks to their hard drive. Minimal technical assistance is available for this procedure. It is not recommended due to the high probability of failure due to DVD drive/disk read problems, over heating, hard drive write errors and memory overrun issues. This procedure is very detailed and should only be performed by users who are very familiar with Windows and/or DOS commands. Novice computers users should not attempt this procedure. Copying Repair data from a DVD is a time-consuming process. Depending on the speed of your processor and/or network, could easily require two or more hours per disk. For this reason, we recommend that you perform the actual copying of data during non-business evening or weekend hours. -
Vmware ESX Host Utilities 5.2.1 Installation and Setup Guide
IBM System Storage N series VMWare ESX Host Utilities 5.2.1 Installation and Setup Guide GC53-1173-03 NA 210-05158_A0 Table of Contents | 3 Contents Supported features ....................................................................................... 7 Getting information, help, and services ...................................................... 9 Before you call ............................................................................................................ 9 Using the documentation ............................................................................................. 9 Web sites ................................................................................................................... 10 Accessing online technical support ........................................................................... 10 Hardware service and support ................................................................................... 10 Supported servers and operating systems .................................................................. 10 Firmware updates ...................................................................................................... 10 How to send your comments ...................................................................... 13 Changes to this document: March 2011 ................................................... 15 Introduction to Host Utilities ..................................................................... 17 What the Host Utilities are ....................................................................................... -

1. Xcopy 2. No, You Cannot Use the Xcopy Command in Your Assignment
Intro to Operating Systems CNET 173 Assignment #4 Windows / LINUX Command Line Commands You are to list twenty-five command line commands of each operating system (WINDOWS and LINUX). That’s twenty- five WINDOWS commands and twenty-five LINUX commands. For each command you are to give: 1. The command a. Description/Attribute of the command b. Syntax of the command and c. A maximum of five Parameters used with the command and a description of the parameter. (If there are less than five parameters, list all parameters associated with the command.) Each command should be numbered and grouped (all WINDOWS commands with WINDOWS commands). Command information should be listed in the 1, a, b, c order listed above (i.e. command, description, syntax and parameters). This assignment must be typed and submitted through CANVAS. It should include a title page consisting of your name, course name, number, day and time, assignment name, instructor’s name, and due date and the assignment instructions. Example listed below. Windows Command Line Commands 1. xcopy a) Description - Copies files and directories, including subdirectories. b) Syntax xcopy Source [Destination] [/w] [/p] [/c] [/v] [/q] [/f] [/l] [/g] [/d[:mm-dd-yyyy]] [/u] [/i] [/s [/e]] [/t] [/k] [/r] [/h] [{/a|/m}] [/n] [/o] [/x] [/exclude:file1[+[file2]][+[file3]] [{/y|/-y}] [/z] c) Parameters /w : Displays the following message and waits for your response before starting to copy files: Press any key to begin copying file(s) /p : Prompts you to confirm whether you want to create each destination file. /c : Ignores errors. /v : Verifies each file as it is written to the destination file to make sure that the destination files are identical to the source files. -

LAB MANUAL for Computer Network
LAB MANUAL for Computer Network CSE-310 F Computer Network Lab L T P - - 3 Class Work : 25 Marks Exam : 25 MARKS Total : 50 Marks This course provides students with hands on training regarding the design, troubleshooting, modeling and evaluation of computer networks. In this course, students are going to experiment in a real test-bed networking environment, and learn about network design and troubleshooting topics and tools such as: network addressing, Address Resolution Protocol (ARP), basic troubleshooting tools (e.g. ping, ICMP), IP routing (e,g, RIP), route discovery (e.g. traceroute), TCP and UDP, IP fragmentation and many others. Student will also be introduced to the network modeling and simulation, and they will have the opportunity to build some simple networking models using the tool and perform simulations that will help them evaluate their design approaches and expected network performance. S.No Experiment 1 Study of different types of Network cables and Practically implement the cross-wired cable and straight through cable using clamping tool. 2 Study of Network Devices in Detail. 3 Study of network IP. 4 Connect the computers in Local Area Network. 5 Study of basic network command and Network configuration commands. 6 Configure a Network topology using packet tracer software. 7 Configure a Network topology using packet tracer software. 8 Configure a Network using Distance Vector Routing protocol. 9 Configure Network using Link State Vector Routing protocol. Hardware and Software Requirement Hardware Requirement RJ-45 connector, Climping Tool, Twisted pair Cable Software Requirement Command Prompt And Packet Tracer. EXPERIMENT-1 Aim: Study of different types of Network cables and Practically implement the cross-wired cable and straight through cable using clamping tool. -

How to Cheat at Windows System Administration Using Command Line Scripts
www.dbebooks.com - Free Books & magazines 405_Script_FM.qxd 9/5/06 11:37 AM Page i How to Cheat at Windows System Administration Using Command Line Scripts Pawan K. Bhardwaj 405_Script_FM.qxd 9/5/06 11:37 AM Page ii Syngress Publishing, Inc., the author(s), and any person or firm involved in the writing, editing, or produc- tion (collectively “Makers”) of this book (“the Work”) do not guarantee or warrant the results to be obtained from the Work. There is no guarantee of any kind, expressed or implied, regarding the Work or its contents.The Work is sold AS IS and WITHOUT WARRANTY.You may have other legal rights, which vary from state to state. In no event will Makers be liable to you for damages, including any loss of profits, lost savings, or other incidental or consequential damages arising out from the Work or its contents. Because some states do not allow the exclusion or limitation of liability for consequential or incidental damages, the above limitation may not apply to you. You should always use reasonable care, including backup and other appropriate precautions, when working with computers, networks, data, and files. Syngress Media®, Syngress®,“Career Advancement Through Skill Enhancement®,”“Ask the Author UPDATE®,” and “Hack Proofing®,” are registered trademarks of Syngress Publishing, Inc.“Syngress:The Definition of a Serious Security Library”™,“Mission Critical™,” and “The Only Way to Stop a Hacker is to Think Like One™” are trademarks of Syngress Publishing, Inc. Brands and product names mentioned in this book are trademarks or service marks of their respective companies. -
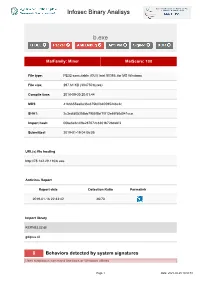
Infosec Binary Analisys B.Exe
Infosec Binary Analisys b.exe MalFamily: Miner MalScore: 100 File type: PE32 executable (GUI) Intel 80386, for MS Windows File size: 297.61 KB (304750 bytes) Compile time: 2018-09-30 20:01:44 MD5: 41b6655aa0e36a375b0f840595248c2c SHA1: 2c3cdfd05356bb7955f5bf1f013e65f58d041cca Import hash: 00be6e6c4f9e287672c8301b72bdabf3 Submitted: 2019-01-19 04:06:05 URL(s) file hosting http://78.142.29.110/b.exe Antivirus Report Report date Detection Ratio Permalink 2019-01-16 22:33:42 46/70 Import library KERNEL32.dll gdiplus.dll 8 Behaviors detected by system signatures Uses suspicious command line tools or Windows utilities Page 1 Date: 2021-09-25 18:50:51 Infosec Binary Analisys - command: taskkill /f /im help.exe /im doc001.exe /im dhelllllper.exe /im DOC001.exe /im dhelper.exe /im conime.exe /im a.exe /im docv8.exe /im king.exe /im name.exe /im doc.exe /im wodCmdTerm.exe /im win1ogins.exe.exe /im win1ogins.exe.exe /im lsaus.exe /im lsars.exe /im lsacs.exe /im regedit.exe /im lsmsm.exe /im v5.exe /im anydesk.exe /im sqler.exe /im sqlservr.exe /im NsCpuCNMiner64.exe /im NsCpuCNMiner32.exe /im tlscntr.exe /im eter.exe /im lsmo.exe /im lsarr.exe /im convert.exe /im WinSCV.exe im ctfmonc.exe /im lsmose.exe /im svhost.exe - command: cacls "C:\Program Files\RemoteDesk\*.exe" /e /d everyone - command: cacls "C:\Program Files\RemoteDesk\*.exe" /e /d system - command: cacls "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe" /e /d everyone - command: cacls "C:\Program Files\Microsoft SQL Server\110\Shared\*.exe" /e /d system - command: cacls "C:\Program