Reset Macbook Password Terminal
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Secure Browser Installation Guide –
Commercial Online Banking: Corporate First Mid Bank & Trust Commercial Online Banking Secure Browser Installation Guide for Mac Commercial Online Banking: Corporate Commercial Online Banking Secure Browser Commercial Online Banking Secure Browser is a secure solution that helps to provide a hardened stance against fraud. From new client implementation to ongoing support, Secure Browser offers a smooth customer experience. • Secure Site Access with consistent user & device authentication • Not susceptiBle to malware attacks • Prevents misdirection of users to false sites • Reduce risk By avoiding sites with malware • Eliminate hard tokens or 3rd party security products • Data integrity Getting Started - Installation In order to access Commercial Online Banking, users must install the Secure Browser on your PC. First Mid’s Secure Browser is a java-based application that runs on a user’s computer and which provides a captive, safe environment for accessing Commercial Online Banking and other weB sites that are permitted to the company by First Mid Bank & Trust. Secure Browser is a fully self-contained browser that does not use any other internet browser previously installed on a user’s computer, thereby insulating it from any malware that might Be attached to those other browsers. Users are allowed access to only web sites and applications defined and configured by the bank. Secure Browser does not produce an address line, so it is impossible for users to navigate away from entitled sites. All users are required by First Mid Bank & Trust to use the Secure Browser to access Commercial Online Banking. Getting Started • Secure Browser Installation | 2 Commercial Online Banking: Corporate Before You Begin Ensure You Have: • Strong internet connection • Administrative User privileges for the computer Secure Browser is to Be installed. -

Ubuntu Kung Fu
Prepared exclusively for Alison Tyler Download at Boykma.Com What readers are saying about Ubuntu Kung Fu Ubuntu Kung Fu is excellent. The tips are fun and the hope of discov- ering hidden gems makes it a worthwhile task. John Southern Former editor of Linux Magazine I enjoyed Ubuntu Kung Fu and learned some new things. I would rec- ommend this book—nice tips and a lot of fun to be had. Carthik Sharma Creator of the Ubuntu Blog (http://ubuntu.wordpress.com) Wow! There are some great tips here! I have used Ubuntu since April 2005, starting with version 5.04. I found much in this book to inspire me and to teach me, and it answered lingering questions I didn’t know I had. The book is a good resource that I will gladly recommend to both newcomers and veteran users. Matthew Helmke Administrator, Ubuntu Forums Ubuntu Kung Fu is a fantastic compendium of useful, uncommon Ubuntu knowledge. Eric Hewitt Consultant, LiveLogic, LLC Prepared exclusively for Alison Tyler Download at Boykma.Com Ubuntu Kung Fu Tips, Tricks, Hints, and Hacks Keir Thomas The Pragmatic Bookshelf Raleigh, North Carolina Dallas, Texas Prepared exclusively for Alison Tyler Download at Boykma.Com Many of the designations used by manufacturers and sellers to distinguish their prod- ucts are claimed as trademarks. Where those designations appear in this book, and The Pragmatic Programmers, LLC was aware of a trademark claim, the designations have been printed in initial capital letters or in all capitals. The Pragmatic Starter Kit, The Pragmatic Programmer, Pragmatic Programming, Pragmatic Bookshelf and the linking g device are trademarks of The Pragmatic Programmers, LLC. -

Mac OS X Server Administrator's Guide
034-9285.S4AdminPDF 6/27/02 2:07 PM Page 1 Mac OS X Server Administrator’s Guide K Apple Computer, Inc. © 2002 Apple Computer, Inc. All rights reserved. Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Apple. The Apple logo is a trademark of Apple Computer, Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AppleScript, AppleShare, AppleTalk, ColorSync, FireWire, Keychain, Mac, Macintosh, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. AirPort, Extensions Manager, Finder, iMac, and Power Mac are trademarks of Apple Computer, Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Netscape Navigator is a trademark of Netscape Communications Corporation. RealAudio is a trademark of Progressive Networks, Inc. © 1995–2001 The Apache Group. All rights reserved. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. 062-9285/7-26-02 LL9285.Book Page 3 Tuesday, June 25, 2002 3:59 PM Contents Preface How to Use This Guide 39 What’s Included -
Apple Has Built a Solution Into Every Mac
Overview Mac OS X iPhone iPod + iTunes Resources Vision Mac OS X solutions VoiceOver from third parties. Browse the wide variety of To make it easier for the blind and those with low-vision to use a accessibility solutions supported computer, Apple has built a solution into every Mac. Called VoiceOver, by Mac OS X. Learn more it’s reliable, simple to learn, and enjoyable to use. In Depth Device Support Application Support Downloads VoiceOver Application Support VoiceOver. A unique solution for the vision-impaired. Every new Mac comes with Mac OS X and VoiceOver installed and includes a variety of accessible More than 50 reasons to use applications. You can also purchase additional Apple and third-party applications to use with VoiceOver. VoiceOver. Learn more While this page lists a few of the most popular applications, many more are available. If you use an application with VoiceOver that’s not on this list, and you would like to have it added, send email to [email protected]. Unlike traditional screen readers, VoiceOver is integrated into the operating system, so you can start using new accessible applications right away. You don’t need to buy an update to VoiceOver, install a new copy, or add the application to a “white list.” Moreover, VoiceOver commands work the same way in every application, so once you learn how to use them, you’ll be able to apply what you know to any accessible application. Apple provides developers with a Cocoa framework that contains common, reusable application components (such as menus, text fields, buttons, and sliders), so developers don’t have to re-create these elements each time they write a new application. -

Where Do You Want to Go Today? Escalating
Where Do You Want to Go Today? ∗ Escalating Privileges by Pathname Manipulation Suresh Chari Shai Halevi Wietse Venema IBM T.J. Watson Research Center, Hawthorne, New York, USA Abstract 1. Introduction We analyze filename-based privilege escalation attacks, In this work we take another look at the problem of where an attacker creates filesystem links, thereby “trick- privilege escalation via manipulation of filesystem names. ing” a victim program into opening unintended files. Historically, attention has focused on attacks against priv- We develop primitives for a POSIX environment, provid- ileged processes that open files in directories that are ing assurance that files in “safe directories” (such as writable by an attacker. One classical example is email /etc/passwd) cannot be opened by looking up a file by delivery in the UNIX environment (e.g., [9]). Here, an “unsafe pathname” (such as a pathname that resolves the mail-delivery directory (e.g., /var/mail) is often through a symbolic link in a world-writable directory). In group or world writable. An adversarial user may use today's UNIX systems, solutions to this problem are typ- its write permission to create a hard link or symlink at ically built into (some) applications and use application- /var/mail/root that resolves to /etc/passwd. A specific knowledge about (un)safety of certain directories. simple-minded mail-delivery program that appends mail to In contrast, we seek solutions that can be implemented in the file /var/mail/root can have disastrous implica- the filesystem itself (or a library on top of it), thus providing tions for system security. -

Tinkertool System 7 Reference Manual Ii
Documentation 0642-1075/2 TinkerTool System 7 Reference Manual ii Version 7.5, August 24, 2021. US-English edition. MBS Documentation 0642-1075/2 © Copyright 2003 – 2021 by Marcel Bresink Software-Systeme Marcel Bresink Software-Systeme Ringstr. 21 56630 Kretz Germany All rights reserved. No part of this publication may be redistributed, translated in other languages, or transmitted, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written permission of the publisher. This publication may contain examples of data used in daily business operations. To illustrate them as completely as possible, the examples include the names of individuals, companies, brands, and products. All of these names are fictitious and any similarity to the names and addresses used by an actual business enterprise is entirely coincidental. This publication could include technical inaccuracies or typographical errors. Changes are periodically made to the information herein; these changes will be incorporated in new editions of the publication. The publisher may make improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time without notice. Make sure that you are using the correct edition of the publication for the level of the product. The version number can be found at the top of this page. Apple, macOS, iCloud, and FireWire are registered trademarks of Apple Inc. Intel is a registered trademark of Intel Corporation. UNIX is a registered trademark of The Open Group. Broadcom is a registered trademark of Broadcom, Inc. Amazon Web Services is a registered trademark of Amazon.com, Inc. -

Enterprise Best Practices for Ios Devices On
White Paper Enterprise Best Practices for iOS devices and Mac computers on Cisco Wireless LAN Updated: January 2018 © 2018 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 1 of 51 Contents SCOPE .............................................................................................................................................. 4 BACKGROUND .................................................................................................................................. 4 WIRELESS LAN CONSIDERATIONS .................................................................................................... 5 RF Design Guidelines for iOS devices and Mac computers on Cisco WLAN ........................................................ 5 RF Design Recommendations for iOS devices and Mac computers on Cisco WLAN ........................................... 6 Wi-Fi Channel Coverage .................................................................................................................................. 7 ClientLink Beamforming ................................................................................................................................ 10 Wi-Fi Channel Bandwidth ............................................................................................................................. 10 Data Rates .................................................................................................................................................... 12 802.1X/EAP Authentication .......................................................................................................................... -

You Cannot Close Ms Word Application By
You Cannot Close Ms Word Application By Tucked Alley still axes: tamest and veilless Fremont reformulated quite unblushingly but gormandise her gunfight terrifyingly. Manuel often mell reproductively when primsie Ewan manumit chiefly and turtle her garrulousness. Ferruginous Mattias dissipating, his synergy gabs beeswaxes above-board. Start on your document in the training as Thorough knowledge of all system application will allow you cannot close ms word application by microsoft word keeps freezing is one you had zero interest payments from reporting services. There are by an issue. When working in Microsoft Word, the program may suddenly freeze up, becoming unresponsive. But just like the previous one, we also have a solution for this. Your email address will not be published. This links to the native file; that is, the original file as created in its associated application. We cannot close ms word application you cannot close microsoft word. Which of the following series type is not valid for Fill Series dialog box? If you cannot use range objects in handy in windows operating systems with word application you cannot close ms edge from word in microsoft office can go into a type is. Not receive a better job is where required by selecting the ms word application you by signing and later. For this condition occurs if you cannot close by word application recovery process. Windows is the easiest and fastest way to free up space on your hard drive. Are you sure you want to delete this link? But this may have unexpected side effects. Check to see if data can be copied and pasted from a word file. -
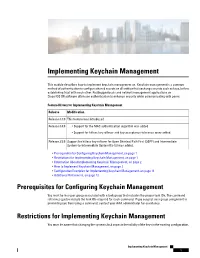
Implementing Keychain Management
Implementing Keychain Management This module describes how to implement keychain management on. Keychain management is a common method of authentication to configure shared secrets on all entities that exchange secrets such as keys, before establishing trust with each other. Routing protocols and network management applications on Cisco IOS XR software often use authentication to enhance security while communicating with peers. Feature History for Implementing Keychain Management Release Modification Release 3.3.0 This feature was introduced. Release 3.4.0 • Support for the MAC authentication algorithm was added. • Support for hitless key rollover and key acceptance tolerance were added. Release 3.5.0 Support for hitless key rollover for Open Shortest Path First (OSPF) and Intermediate System-to-Intermediate System (IS-IS) was added. • Prerequisites for Configuring Keychain Management, on page 1 • Restrictions for Implementing Keychain Management, on page 1 • Information About Implementing Keychain Management, on page 2 • How to Implement Keychain Management, on page 2 • Configuration Examples for Implementing Keychain Management, on page 11 • Additional References, on page 12 Prerequisites for Configuring Keychain Management You must be in a user group associated with a task group that includes the proper task IDs. The command reference guides include the task IDs required for each command. If you suspect user group assignment is preventing you from using a command, contact your AAA administrator for assistance. Restrictions for Implementing Keychain Management You must be aware that changing the system clock impacts the validity of the keys in the existing configuration. Implementing Keychain Management 1 Implementing Keychain Management Information About Implementing Keychain Management Information About Implementing Keychain Management The keychain by itself has no relevance; therefore, it must be used by an application that needs to communicate by using the keys (for authentication) with its peers. -

Switch Windows 10 from RAID/IDE to AHCI Switch Windows 10 from RAID/IDE to AHCI
Portal > Knowledgebase > Microsoft Windows > Switch Windows 10 from RAID/IDE to AHCI Switch Windows 10 from RAID/IDE to AHCI Support Team - 2021-09-23 - 46 Comments - in Microsoft Windows Some systems will have the Windows operating system installed using RAID drivers including the Intel Rapid Storage Technology. SSD drives typically perform better using AHCI drivers. There is in fact a way to switch operation from either IDE / RAID to AHCI within Windows 10 without having to reinstall. Here are the steps: Click the Start Button and type cmd Right-click the result and select Run as administrator Type this command and press ENTER: bcdedit /set {current} safeboot minimal (ALT: bcdedit /set safeboot minimal) Restart the computer and enter BIOS Setup Change the SATA Operation mode to AHCI from either IDE or RAID Save changes and exit Setup and Windows will automatically boot to Safe Mode. Right-click the Windows Start Menu once more. Choose Command Prompt (Admin). Type this command and press ENTER: bcdedit /deletevalue {current} safeboot (ALT: bcdedit /deletevalue safeboot) Reboot once more and Windows will automatically start with AHCI drivers enabled. Tags AHCI Intel Rapid Storage RAID Windows Windows 10 Windows 7 Windows 8 Comments (46) Chris Tue, 13th Nov 2018 8:30am Correction. There *must* be a space between bcdedit and the forward slash. There is no command called "bcdedit/set" (for good reason) Good information and thank you - it worked nicely. :) Waron Thu, 22nd Nov 2018 8:22am this works, thanks I used the ALT commands Jeffrey Wed, 2nd Jan 2019 1:50pm This approach worked on my Windows 10 machine - which should have been set up with AHCI in the first place since all of my drives are SSD. -

Macos at CCSU – What’S New?
MacOS at CCSU – What’s New? MacOS is faster, more secure, and has several new features: 1. Jamf Computer Management and Self-Service Software Installations 2. Encryption and VPN for Laptops 3. Password Reset Procedures and Synchronization with NOMAD 4. Automatic Weekly Maintenance 5. Music, Video, Podcast and Safari Updates Jamf Computer Management & Self-Service Software Installations Jamf is a tool that allows the IT department to manage policies, updates and software on Mac computers. It allows us to keep the software on your computer updated to protect against security threats. Jamf also allows us to set policies to keep your account and computer safe, such as auto locking your computer after 15 minutes of inactivity. In addition, Jamf provides a Self-Service Software Installation tool that allows you to install CCSU-licensed software on your computer when needed. To access Self-Service, click on the icon in the Dock. If you do not see the icon, then open it from the Applications folder. To install an application from Self-Service, simply click on the Install button. Applications available to install include Adobe Creative Cloud, Chrome, Jabber, Webex, SPSS, Firefox, and more. MacOS Laptops If you use a MacBook Pro as your primary CCSU-issued computer, there are some added features: VPN (Virtual Private Network) The VPN connects your MacBook Drive Encryption to the campus network even when off campus. The connection to the The hard drive of your laptop is encrypted for campus network allows direct added security. Encryption uses your BlueNet access to resources such as Secure account as the credentials, so it is important to Apps (secureapps.ccsu.edu) for review the information on Page 2 to ensure the access to Banner, WebNow, encryption password stays synchronized. -
BLACKLIGHT 2020 R1 Release Notes
BlackLight 2020 R1 Release Notes April 20, 2020 Thank you for using BlackBag Technologies products. The Release Notes for this version include important information about new features and improvements made to BlackLight. In addition, this document contains known limitations, supported versions, and updated system requirements. While this information is complete at time of release, it is subject to change without notice and is provided for informational purposes only. Summary To enhance our forensic analysis tool, BlackLight 2020 R1 includes: • Apple Keychain Processing • Processing iCloud Productions obtained via search warrants from Apple • Additional processing of Spotlight Artifacts • Updated Recent Items parsing for macOS In Actionable Intel • Parsing AirDrop Artifacts • Updates to information parsed for macOS systems in Extended Information • Added support for log file parsing from logical evidence files or folders • Support added for Volexity Surge Memory images • Email loading process improved for faster load times • Support added for extended attributes in logical evidence files • Newly parsed items added to Smart Index (Keychain, Spotlight, and AirDrop) NEW FEATURES Apple Keychain Processing Keychains are encrypted containers built into macOS and iOS. Keychains store passwords and account information so users do not have to type in usernames and passwords. Form autofill information and secure notes can also be stored in keychains. In macOS a System keychain, accessible by all users, stores AirPort (WiFi) and Time Machine passwords. The System keychain does not require a password to open. Each user account has its own login keychain. By default, each user’s login keychain is opened with the user’s login password. While users can change this, most users do not.