Reversing the Nintendo 64
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

THE SUPER WILDCARD DX2 FAQ V1.3 by Vincent Charbonneau
THE SUPER WILDCARD DX2 FAQ V1.3 By Vincent Charbonneau (AKA Fat_Mike) Last Update: January 8th 2003 This FAQ was written for the purpose of helping Super WildCard DX2 owners to get the most out of their unit. It is also supposed to help those of you who are new to the backup unit world. If you have a problem that isn’t listed in this document, be sure to e-mail me. If I, or someone, manage to solve it, I will add it in the next update of the FAQ with the proper credits given. And this is about the Super WildCard DX2, so if you are using another SNES backup unit, the information given in this FAQ are darn useless to you. When I talk about the SWC DX2, I refer to the Super WildCard DX2 (in case you didn’t know). And English is not my native language, so there might be grammar errors and such (even though the FAQ was corrected). If you don’t understand something or want me to correct something, again be sure to e-mail me ([email protected])! For those who are totally new to the copier world and don’t know what the hell I’m talking about, a Super WildCard is a Super Nintendo backup unit. With a SWC DX2, you can copy your game cartridges and play these copies (ROMs) without the need of the actual cart. You can also play a downloaded ROM image directly on your SNES just like the real cartridge. And there’s far more the SWC DX2 can do, but I can’t list all the possibilities of this copier, it would take a while. -

NES Specifications
Everynes - Nocash NES Specs Everynes Hardware Specifications Tech Data Memory Maps I/O Map Picture Processing Unit (PPU) Audio Processing Unit (APU) Controllers Cartridges and Mappers Famicom Disk System (FDS) Hardware Pin-Outs CPU 65XX Microprocessor About Everynes Tech Data Overall Specs CPU 2A03 - customized 6502 CPU - audio - does not contain support for decimal The NTSC NES runs at 1.7897725MHz, and 1.7734474MHz for PAL. NMIs may be generated by PPU each VBlank. IRQs may be generated by APU and by external hardware. Internal Memory: 2K WRAM, 2K VRAM, 256 Bytes SPR-RAM, and Palette/Registers The cartridge connector also passes audio in and out of the cartridge, to allow for external sound chips to be mixed in with the Famicom audio. Original Famicom (Family Computer) (1983) (Japan) 60-pin cartridge slot, with external sound-input, without lockout chip. Two joypads directly attached to console, Joypad 1 with Start/Select buttons, Joypad 2 with microphone, but without Start/Select. 15pin Expansion port for further controllers. Video RF-Output only. "During its first year, people found the Famicom to be unreliable, with programming errors and freezing rampant. Yamauchi recalled all sold Famicom systems, and put the Famicom out of production until the errors were fixed. The Famicom was re-released with a new motherboard." Original NES (Nintendo Entertainment System) (1985) (US, Europe, Australia) Same as Famicom, but with slightly different pin-outs on cartridge slot, and controllers/expansion ports: Front-loading 72-pin cartridge slot, without external sound-input on cartridge slot, without microphone on joypads, with lockout chip. Newer Famicom, AV Famicom (1993-1995) 60-pin cartridge slot, with external sound-input, without lockout chip. -
United States Patent (19) 11 Patent Number: 6,071,191 Takeda Et Al
USOO6071191A United States Patent (19) 11 Patent Number: 6,071,191 Takeda et al. (45) Date of Patent: Jun. 6, 2000 54 SYSTEMS AND METHODS FOR PROVIDING OTHER PUBLICATIONS SECURITY IN A WIDEO GAME SYSTEM Open Programming Guide, “The Official Guide to Learning 75 Inventors: Genyo Takeda, Kyoto; Shuhei Kato, OpenGL, Release 1. OpenGL Architecture Review Board, Otsu; Satoshi Nishiumi, Kyoto, all of Jackie Neider, Tom Davis, Mason Woo, Copyright 1993 by Japan Silicon Graphics, Inc. Open GL Reference Manual, “The Official Reference Docu 73 Assignee: Nintendo Co., Ltd., Kyoto, Japan ment for OpenGL, Release 1,” OpenGL Architecture Review Board, Copyright 1992 by Silicon Graphics, Inc. 21 Appl. No.: 08/850,676 MIPS Microprocessor R4000 User's Manual, First Edition, by Joe Heinrich, Copyright 1993 by MIPS Technologies, 22 Filed: May 2, 1997 Inc. Related U.S. Application Data (List continued on next page.) 63 Continuation-in-part of application No. 08/562,288, Nov. Primary Examiner Valencia Martin-Wallace 22, 1995. Attorney, Agent, or Firm Nixon & Vanderhye P.C. (51) Int. Cl. .................................................. G06F 1700 57 ABSTRACT 52 U.S. Cl. .................................. 463/29: 463/36; 463/43 58 Field of Search .................................. 463,29, 36,43, A video game System includes a game cartridge which is 463/44, 45, 46, 47 pluggably attached to a main console having a main processor, a 3D graphics generating coprocessor, expand 56) References Cited able main memory and player controllers. A multifunctional peripheral processing Subsystem external to the game micro U.S. PATENT DOCUMENTS processor and coprocessor is described which executes Re. 31,200 4/1983 Sukonick et al. -
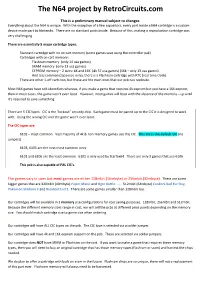
The N64 Project by Retrocircuits.Com
The N64 project by RetroCircuits.com This is a preliminary manual subject to changes. Everything about the N64 is unique. With the exception of a few capacitors, every part inside a N64 cartridge is a custom device made part by Nintendo. There are no standard parts inside. Because of this, making a reproduction cartridge was very challenging. There are essentially 5 major cartridge types: Standard cartridge with no on cart memory (some games save using the controller pak) Cartridges with on cart memory: Flashram memory (only 14 usa games) SRAM memory (only 13 usa games) EEPROM memory – 2 sizes: 4K and 16K (4k 57 usa games) (16k – only 13 usa games) And less common (Japanese only), there is a Flashram cartridge with RTC (real time clock). There are other 1-off carts too, but these are the main ones that our pcb can replicate. Most N64 games have self-identifiers whereas, if you make a game that requires 4k eeprom but you have a 16k eeprom, then in most cases, the game won’t even boot. However, most games will boot with the absence of the memory – up until it’s required to save something. There are 5 CIC types. CIC is the “lockout” security chip. Each game must be paired up to the CIC it is designed to work with. Using the wrong CIC and the game won’t even boot. The CIC types are: 6102 – most common. Vast majority of 4k & non-memory games use this CIC. This CIC is the default CIC (no jumpers) 6103, 6105 are the next most common ones. -
Mass-Effect-3-Special-Edition-Wii-U
Contents Complete Controls Complete Controls 3 NOTE: You can also play Mass Effect™ 3 Special Edition exclusively on the Control Scheme . 3 Wii U GamePad, without the need for a TV . At any time press and hold the Wii U GamePad Controls . 4 . - Button for three seconds to enter or exit play on the Wii U GamePad . Single Player 5 The Main Menu . 5 Starting a New Game . 7. Control Scheme Mission Computer . .9 . The following controls are for both the Wii U GamePad™ and the 2D Level Maps . .10 . Wii U™ Pro Controller . Squad Screen . .11 . Movement Left Stick The Game Journal . 14. 90˚ cover turn Press the Left Stick The HUD . 15. Basic Controls . 17 Camera Right Stick Cover Use . .18 . Navigation Press the Left Stick/press the Right Stick/ Squad Commands . .20 . Touch Screen Powers . 22 Reload weapon Y Button (tap) Weapons, Mods, and Armor . 24 . Switch weapon Y Button (hold) Galaxy Map . 27 . Use/Take cover A Button (tap) Multiplayer 31 Quick vault A Button (tap twice) Galaxy at War . 31 Storm A Button (hold) The Multiplayer Menu . .33 . Melee B Button Joining or Creating a Game . 34 Heavy melee B Button (hold) Missions . 35. Mapped power X Button Multiplayer Lobby . 38. Power Wheel R Button (hold) Character Screen . 41. Weapon Wheel L Button (hold) Reinforcement Packs . 42 The HUD . 44. Select weapon/power L Button (hold for weapons)/ R Button (hold for powers), Tips and Help 46 move the Left Stick to highlight an item, Combat Tips . 46 press the A Button to select, and Enemy Tips . -

18545 Final Report Fall 2013 Team Onemorething Project: Super Nintendo Entertainment System Team Members
18545 Final Report Fall 2013 Team OneMoreThing Project: Super Nintendo Entertainment System Team Members: Saketh Pothireddy Niharika Singh Delvis Taveras {spothire, niharika, dtaveras} @andrew.cmu.edu We give Professor Nace and the 18-545 staff permission to post this report online. 1 Contents Contents The Original System The SNES The Original Block Diagram The Video System The Audio System The Cartridge The Lock-Out Chip The Memory Addressing The Controller Inputs The CPU Our Implementation The Modified Block Diagram The Modified Modified Block Diagram The Video System The Audio System The Cartridge The Controller Inputs The CPU Memory Accesses DMA and HDMA Logistics Partitioning the Work Scheduling Tools Used Design Methodology Testing and Verification Methodology Status Lessons Learnt Pivotal Decisions and Their Results Words of Wisdom Individual Pages Saketh Pothireddy Niharika Singh Delvis Taveras Code 2 The Original System The SNES The Super Nintendo Entertainment System was released by Nintendo in 1990-1992 in different parts of the world. This is a 16-bit gaming console that can support two players. It also supports a variety of cartridges The Original Block Diagram The Video System The on-board video is implemented by two Picture Processing Units (PPUs). One PPU is primarily responsible for the background while the other is responsible for sprites. These PPUs are supported by three types of RAM: 64 kB of video RAM (VRAM), 544 bytes of object attribute memory (OAM) and 512 bytes of color generator RAM (CGRAM). 3 The maximum resolution possible is 512 x 478 pixels. However, smaller resolutions are possible. Super Tennis, for example, has a resolution of 256 x 240 pixels. -
User's Manual
USER’S MANUAL Updated for HW2 012219 COPYRIGHT INFORMATION Product comprising physical circuit board, software and related IP © 2010-2019 Retroactive “Nintendo” is a registered trademark of Nintendo of America Inc. Nintendo 64 is a registered trademark of Nintendo Company, Limited. Disclaimer: This document is for informational use only. The user of this device assumes full responsbility ensuring its use in accor- dance with local and federal laws. The software and hardware of the prod- uct are provided “as-is”, without any ex- press or implied warranty or guarantee. NOTICES Information contained herein reflects the current state of the product at the time of writing. For the most current document please see the Support page on the product website at: http://64drive.retroactive.be See the About tab in the product Menu to see more specific attributions and software revision information. ii CONTENTS COPYRIGHT INFORMATION ii Considerations 6 Tools 7 NOTICES ii TECH DETAILS 8 CONTENTS iii Region Information 8 INTRODUCTION 1 Saving Methods 8 Physical Considerations 1 Lockout Chips 9 In Case of a Problem 1 FAQ 10 GETTING STARTED 1 SPECIFICATIONS 11 Check Formatting 1 Hardware (HW2) 11 Install the Menu 1 Hardware (HW1) 11 Copy Image Files 2 Transfer Rates (HW2) 11 Turn It On 2 Transfer Rates (HW1) 11 Getting Around the Menu 2 Supported Save Types 11 Loading an Image 2 After You’re Done 2 TROUBLESHOOTING 11 Startup Problems 11 MENU - OPTIONS 3 In Menu Use ‘Saves’ Folder 3 Reset Button Action 3 SUPPORT INFO Font Size 3 Website Controller Pak Saving 3 E-mail MENU - ABOUT 3 Menu 3 Firmware 3 Bootloader 3 OTHER FEATURES 3 Background Skinning 3 Quick-Start 4 Controller Pak Saving 4 Force NTSC Menu Mode 4 Using Saves From an Emulator 5 NES Emulation 5 MP3 Playback 5 USB MODE 6 How it Works 6 iii DEVELOPMENT TOOL INTRODUCTION GETTING STARTED The 64drive is a tool designed to be used Check Formatting with the Nintendo 64 video game console for the ends of game development and/or The 64drive only works with memory modification. -

June 29, 2012 David O. Carson General Counsel U.S. Copyright
June 29, 2012 David O. Carson General Counsel U.S. Copyright Office P.O. Box 70400 Washington, DC 20024 Re: Docket No. RM 2011-7 Exemptions to Prohibition on Circumvention of Technological Measures that Control Access to Copyrighted Works Dear Mr. Carson: Thank you for the opportunity to participate in the recent hearings in the Copyright Office’s 1201 rulemaking proceeding, and for your follow-up questions on proposed Class 3. We appreciate the opportunity to supplement the factual record. 1. The proposed class of works for video game consoles appears to be broad enough to encompass all past, present, and future video game systems. Is there any evidence that scientists and homebrewers need an exemption to circumvent technological protection measures on the original Playstation, the Playstation 2, XBOX, all iterations of Nintendo’s video game consoles prior to the Wii, and any other legacy videogame console? Yes. Various legacy consoles have strong communities dedicated to homebrew game development, among other non-infringing uses.1 For example, users have modified the unique synthesizers in the Nintendo Entertainment System and the Game Boy handheld to transform these devices into musical “chiptune” instruments.2 Artists have also created real-time audio-visual displays on older consoles.3 1 For a summary of homebrew activity related to a wide variety of legacy consoles, see Homebrew (video games), http://en.wikipedia.org/w/index.php?title=Homebrew_(video_games)&oldid=497847311/ (last visited June 29, 2012); see also, e.g., Retrozone, http://www.retrousb.com/index.php?cPath=30&osCsid=f1b806b793d7c4dc57832f0bd1a8d40c (last visited June 29, 2012) (examples of Nintendo Entertainment System homebrew games). -

Digital Rights Management in Video Games: Their Impact on Performance and the Legal Structure Connected to Them
Digital Rights Management in video games: their impact on performance and the legal structure connected to them Timothy Colangelo Bachelor’s Thesis Degree Programme in Busi- ness Information Technology 2020 Abstract Date Author(s) Timothy Colangelo Degree programme Degree Programme in Business Information Technology Report/thesis title Number of pages Digital Rights Management in video games: their impact on perfor- and appendix pages mance and the legal structure connected to them 36 + 3 Video games in the past few years have become the biggest entertainment market indus- try, raking in over tens of billions of dollars in the past five years. This thesis focuses on Digital Rights Management functions in videogames and how DRM intertwines with video games in order to avoid piracy. The research goes into detail about the history and concepts of DRM and anti-piracy measures in both the past and present. However, the main focus of this research is DRM relating hinderances in video game per- formance. The study conducted focused on six video games, using four criteria to deter- mine whether video games equipped with DRM perform worse than their DRM-free coun- terparts. This research uses a correlationall quantitative approach: the data gathered, as mentioned earlier, comes from a pool of six games, using four different criteria, and compare results by using mathematical averages to empirically describe increase and decrease. The research shows that performance in DRM-free video games is marginally better com- paring to video games using DRM technologies, while the size of DRM-free video games shrunk significantly after DRM removal.