A Blockchain-Based Authentication Protocol for Cooperative Vehicular Ad Hoc Network
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Handheld Computing Terminal Industrializing Mobile Gateway for the Internet of Things
Handheld Computing Terminal Industrializing Mobile Gateway for the Internet of Things Retail Inventory Logistics Management Internet of Vehicles Electric Utility Inspection www.AMobile-solutions.com About AMobile Mobile Gateway for IIoT Dedicated IIoT, AMobile develops mobile devices and gateways for data collectivity, wireless communications, local computing and processing, and connectivity between the fields and cloud. In addition, AMobile's unified management platform-Node-Watch monitors and manages not only mobile devices but also IoT equipment in real-time to realize industrial IoT applications. Manufacturing • IPC mobile • Mobility computing technology Retail Inspection (IP-6X, Military • Premier member grade, Wide- - early access Blockchain temperature) Healthcare Logistics • Manufacturing resource pool Big Data & AI • Logistics • Global customer support Handheld Mobile Computing Data Collector Smart Meter Mobile Inspection Device with Keyboard Assistant Mobile Computing IoT Terminal Device Ultra-rugged Intelligent Barcode Reader Vehicle Mount Handheld Device Handheld Device Tablet Mobile Gateway AMobile Intelligent established in 2013, a joint venture by Arbor Technology, MediaTek, and Wistron, is Pressure Image an expert in industrial mobile computers and solutions for industrial applications including warehousing, Temperature Velocity Gyroscope logistics, manufacturing, and retail. Leveraging group resources of manufacturing and services from Wistron, IPC know-how and distribution channels from Arbor, mobility technology and -

A Survey of Autonomous Vehicles: Enabling Communication Technologies and Challenges
sensors Review A Survey of Autonomous Vehicles: Enabling Communication Technologies and Challenges M. Nadeem Ahangar 1, Qasim Z. Ahmed 1,*, Fahd A. Khan 2 and Maryam Hafeez 1 1 School of Computing and Engineering, University of Huddersfield, Huddersfield HD1 3DH, UK; [email protected] (M.N.A.); [email protected] (M.H.) 2 School of Electrical Engineering and Computer Science, National University of Sciences and Technology, Islamabad 44000, Pakistan; [email protected] * Correspondence: [email protected] Abstract: The Department of Transport in the United Kingdom recorded 25,080 motor vehicle fatali- ties in 2019. This situation stresses the need for an intelligent transport system (ITS) that improves road safety and security by avoiding human errors with the use of autonomous vehicles (AVs). There- fore, this survey discusses the current development of two main components of an ITS: (1) gathering of AVs surrounding data using sensors; and (2) enabling vehicular communication technologies. First, the paper discusses various sensors and their role in AVs. Then, various communication tech- nologies for AVs to facilitate vehicle to everything (V2X) communication are discussed. Based on the transmission range, these technologies are grouped into three main categories: long-range, medium- range and short-range. The short-range group presents the development of Bluetooth, ZigBee and ultra-wide band communication for AVs. The medium-range examines the properties of dedicated short-range communications (DSRC). Finally, the long-range group presents the cellular-vehicle to everything (C-V2X) and 5G-new radio (5G-NR). An important characteristic which differentiates each category and its suitable application is latency. -

Extensible Authentication Protocol (EAP) and IEEE 802.1X: Tutorial and Empirical Experience
CHEN LAYOUT 11/17/05 11:57 AM Page 52 Extensible Authentication Protocol (EAP) and IEEE 802.1x: Tutorial and Empirical Experience JYH-CHENG CHEN AND YU-PING WANG, NATIONAL TSING HUA UNIVERSITY Abstract oped WIRE1x to support various versions of MS Windows. As This article presents the technical details of the Extensible the name suggests, WIRE1x is an open-source implementa- Authentication Protocol (EAP) and IEEE 802.1x by using tion of IEEE 802.1x client (supplicant)1 developed by the WIRE1x, an open-source implementation of IEEE 802.1x Wireless Internet Research & Engineering (WIRE) Laborato- client (supplicant) and various EAP-based authentication ry.2 Both source code and executable code of WIRE1x can be mechanisms. By using a real implementation, 802.1x and EAP downloaded freely from http://wire.cs.nthu.edu.tw/wire1x/. should be easily understood. Essentially, 802.1x provides a framework for port-based access control. It can work with various authentication mecha- nisms to authenticate and authorize users. The Extensible Introduction Authentication Protocol (EAP, IETF RFC 2284) is a protocol Wireless local area networks (WLANs) have become increas- commonly used in 802.1x to authenticate users. Currently, ingly more prevalent in recent years. The IEEE 802.11 stan- WIRE1x provides various authentication mechanisms, includ- dard is one of the most widely adopted standards for ing EAP Message Digest 5 (EAP-MD5, IETF RFC 1321), broadband wireless Internet access. However, security consid- EAP Transport Layer Security (EAP-TLS, IETF RFC 2716), erations with regard to wireless environments are more com- EAP Tunneled TLS (EAP-TTLS) [5], and Protected Extensi- plicated than those in wired environments. -

Fog Computing for Detecting Vehicular Congestion, an Internet of Vehicles Based Approach: a Review
> REPLACE THIS LINE WITH YOUR PAPER IDENTIFICATION NUMBER (DOUBLE-CLICK HERE TO EDIT) < 1 Fog Computing for Detecting Vehicular Congestion, An Internet of Vehicles based Approach: A review Arnav Thakur and Reza Malekian, Senior Member, IEEE double by the year 2020 [3]. To enhance the efficiency of the Abstract—Vehicular congestion is directly impacting the transportation sector and reduce the associated economic and efficiency of the transport sector. A wireless sensor network for environmental consequences, an accurate real-time vehicular vehicular clients is used in Internet of Vehicles based solutions traffic congestion identification system is required to be used for traffic management applications. It was found that vehicular in effective traffic management schemes that improve traffic congestion detection by using Internet of Vehicles based connected vehicles technology are practically feasible for flow and utilization of road infrastructure. congestion handling. It was found that by using Fog Computing Vehicular congestion is quantified by using the traffic based principles in the vehicular wireless sensor network, density estimate metric which is the number of vehicles per communication in the system can be improved to support larger unit area [4]. The traffic density estimation techniques use number of nodes without impacting performance. In this paper, parameters that include road occupancy rates, difference of connected vehicles technology based vehicular congestion incoming and outgoing traffic in an observation area, traffic identification techniques are studied. Computing paradigms that can be used for the vehicular network are studied to develop a flow estimation and motion detection and tracking to identify practically feasible vehicular congestion detection system that congestion [5]. -
Kerberos: an Authentication Service for Computer Networks by Clifford Neuman and Theodore Ts’O
Kerberos: An Authentication Service for Computer Networks by Clifford Neuman and Theodore Ts’o Presented by: Smitha Sundareswaran Chi Tsong Su Introduction z Kerberos: An authentication protocol based on cryptography z Designed at MIT under project Athena z Variation of Needham Schroeder protocol - Difference: Kerberos assumes all systems on the network to be synchronized z Similar function as its mythological namesake: “guards” the access to network protocols Contribution z Defines ideas of authentication, Integrity, confidentiality and Authorization z Working of Kerberos z Limitations z Utilities z How to obtain and use Kerberos z Other methods to improve security Why Kerberos? z Foils threats due to eavesdropping z More convenient than password based authentication { Allows user to avoid “authentication by assertion” z Authentication based on cryptography: attacker can’t impersonate a valid user How Kerberos Works z Distributed authentication service using a series of encrypted messages {Password doesn’t pass through the network z Timestamps to reduce the number of messages needed for authentication z “Ticket granting Service” for subsequent authentication Kerberos Authentication and Encryption zAuthentication proves that a client is running on behalf of a particular user zUses encryption key for authentication {Encryption key = Password zEncryption implemented using DES {Checksum included in message checksum and encryption provide integrity & confidentiality The Kerberos Ticket z Initially, client and Server don’t share an encryption -

An Intelligent Edge-Chain Enabled Access Control Mechanism For
This article has been accepted for publication in a future issue of this journal, but has not been fully edited. Content may change prior to final publication. Citation information: DOI 10.1109/JIOT.2021.3061467, IEEE Internet of Things Journal JOURNAL OF LATEX CLASS FILES, VOL. 14, NO. 8, AUGUST 2015 1 An Intelligent Edge-Chain Enabled Access Control Mechanism for IoV Yuanni Liu, Man Xiao, Shanzhi Chen, Fellow, IEEE, Fan Bai, Jianli Pan, Member, IEEE, Di Zhang, Senior Member, IEEE Abstract—The current security method of Internet of Vehicles the amounts of vehicles exceed one billion and is expected (IoV) systems is rare, which makes it vulnerable to various to reach two billion by 2035 [6], [7]. As explosive on-road attacks. The malicious and unauthorized nodes can easily in- devices are connecting to Internet, communication security vade the IoV systems to destroy the integrity, availability, and confidentiality of information resources shared among vehicles. becomes a big issue. As we know, the communication security Indeed, access control mechanism can remedy this. However, as method of current IoV devices is rare, making it easy to be a static method, it cannot timely response to these attacks. To attacked. Such malicious attacks include replay, camouflage, solve this problem, we propose an intelligent edge-chain enabled and message tampering attacks et al. [8]. The attacked IoV access control framework with vehicle nodes and RoadSide Units devices may rise potential risks, such as critical electronic (RSUs) in this study. In our scenario, vehicle nodes act as lightweight nodes, whereas RUSs serve as full and edge nodes control unit hacking and control, untrustworthy messages from to provide access control services. -

Position Prediction for Routing in Software Defined Internet of Vehicles
Journal of Communications Vol. 15, No. 2, February 2020 Position Prediction for Routing in Software Defined Internet of Vehicles Muhammad Ali Jibran1, Muhammad Tahir Abbas2, Adeel Rafiq1, and Wang-Cheol Song1 1, Jeju National University, Jeju, South Korea 2 Karlstad University, Karlstad, Sweden Email: [email protected]; [email protected] Abstract—By the prediction of future location for a vehicle in In the past few years, vehicle to vehicle (V2V) Internet of Vehicles (IoV), data forwarding schemes can be communication gain a lot of attention because of its further improved. Major parameters for vehicle position potential to make our journey comfortable on the roads. prediction includes traffic density, motion, road conditions, and The core requirement of connected cars include a reliable vehicle current position. In this paper, therefore, our proposed and fast communication with very low latency response system enforces the accurate prediction with the help of real- time traffic from the vehicles. In addition, the proposed Neural to and from a service provider. In the meanwhile, it needs Network Model assists Edge Controller and centralized to be more efficient to manage a huge number of requests controller to compute and predict vehicle future position inside simultaneously with no traffic congestion. In ITS, a and outside of the vicinity, respectively. Last but not least, in vehicle on the road always initiates a new connection order to get real-time data, and to maintain a quality of request towards the traffic controller in case of path experience, the edge controller is explored with Software failure. Traffic controller estimates a new path each time Defined Internet of Vehicles. -

Deep Learning-Based Intrusion System for Vehicular Ad Hoc Networks
Computers, Materials & Continua CMC, vol.65, no.1, pp.653-681, 2020 Deep Learning-Based Intrusion System for Vehicular Ad Hoc Networks Fei Li1, *, Jiayan Zhang1, Edward Szczerbicki2, Jiaqi Song 1, Ruxiang Li 1 and Renhong Diao1 Abstract: The increasing use of the Internet with vehicles has made travel more convenient. However, hackers can attack intelligent vehicles through various technical loopholes, resulting in a range of security issues. Due to these security issues, the safety protection technology of the in-vehicle system has become a focus of research. Using the advanced autoencoder network and recurrent neural network in deep learning, we investigated the intrusion detection system based on the in-vehicle system. We combined two algorithms to realize the efficient learning of the vehicle’s boundary behavior and the detection of intrusive behavior. In order to verify the accuracy and efficiency of the proposed model, it was evaluated using real vehicle data. The experimental results show that the combination of the two technologies can effectively and accurately identify abnormal boundary behavior. The parameters of the model are self-iteratively updated using the time-based back propagation algorithm. We verified that the model proposed in this study can reach a nearly 96% accurate detection rate. Keywords: Internet of vehicles, safety protection technology, intrusion detection system, advanced auto-encoder, recurrent neural network, time-based back propagation algorithm. 1 Introduction In recent years, intelligent vehicles, a fusion of Internet technology and the machinery manufacturing industry, have resulted in the development of comprehensive information services for travel and daily commutes [Unluturk, Oguz and Atay (2015); Contreras- Castillo, Zeadally and Guerrero-Ibañez (2017)]. -

PUF Based Authentication Protocol for Iot
S S symmetry Article PUF Based Authentication Protocol for IoT An Braeken Vrije Universiteit Brussel, Pleinlaan 2, 1050 Brussel, Belgium; [email protected]; Tel.: +32-468-104-767 Received: 11 July 2018; Accepted: 11 August 2018; Published: 20 August 2018 Abstract: Key agreement between two constrained Internet of Things (IoT) devices that have not met each other is an essential feature to provide in order to establish trust among its users. Physical Unclonable Functions (PUFs) on a device represent a low cost primitive exploiting the unique random patterns in the device and have been already applied in a multitude of applications for secure key generation and key agreement in order to avoid an attacker to take over the identity of a tampered device, whose key material has been extracted. This paper shows that the key agreement scheme of a recently proposed PUF based protocol, presented by Chatterjee et al., for Internet of Things (IoT) is vulnerable for man-in-the-middle, impersonation, and replay attacks in the Yao–Dolev security model. We propose an alternative scheme, which is able to solve these issues and can provide in addition a more efficient key agreement and subsequently a communication phase between two IoT devices connected to the same authentication server. The scheme also offers identity based authentication and repudiation, when only using elliptic curve multiplications and additions, instead of the compute intensive pairing operations. Keywords: physical unclonable function; authentication; elliptic curve cryptography; internet of things 1. Introduction Internet of Things (IoT) is experiencing worldwide growth. Not only classical computing and communication devices are connected, but also a whole range of other gadgets that are used in our daily life, such as thermostats, light switches, door locks, refrigerators, etc. -
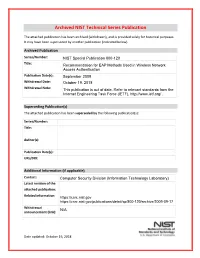
Recommendation for EAP Methods
Archived NIST Technical Series Publication The attached publication has been archived (withdrawn), and is provided solely for historical purposes. It may have been superseded by another publication (indicated below). Archived Publication Series/Number: NIST Special Publication 800-120 Title: Recommendation for EAP Methods Used in Wireless Network Access Authentication Publication Date(s): September 2009 Withdrawal Date: October 19, 2018 Withdrawal Note: This publication is out of date. Refer to relevant standards from the Internet Engineering Task Force (IETF), http://www.ietf.org/ . Superseding Publication(s) The attached publication has been superseded by the following publication(s): Series/Number: Title: Author(s): Publication Date(s): URL/DOI: Additional Information (if applicable) Contact: Computer Security Division (Information Technology Laboratory) Latest revision of the attached publication: Related information: https://csrc.nist.gov https://csrc.nist.gov/publications/detail/sp/800-120/archive/2009-09-17 Withdrawal N/A announcement (link): Date updated: October 19, 2018 NIST Special Publication 800-120 Recommendation for EAP Methods Used in Wireless Network Access Authentication Katrin Hoeper and Lily Chen Computer Security Division Information Technology Laboratory C O M P U T E R S E C U R I T Y September 2009 U.S. Department of Commerce Gary Locke, Secretary National Institute of Standards and Technology Patrick Gallagher, Deputy Director Abstract This Recommendation specifies security requirements for authentication methods with key establishment supported by the Extensible Authentication Protocol (EAP) defined in IETF RFC 3748 for wireless access authentications to federal networks. KEY WORDS: EAP methods, authentication, key establishment. SP 800-120: Recommendation for EAP Methods Used in Wireless Network Access Authentication Acknowledgments The authors, Katrin Hoeper and Lily Chen, wish to thank their colleagues who reviewed drafts of this document and contributed to its technical content. -

Diameter-Based Protocol in the IP Multimedia Subsystem
International Journal of Soft Computing and Engineering (IJSCE) ISSN: 2231 – 2307, Volume- 1 Issue- 6, January 2012 Diameter-Based Protocol in the IP Multimedia Subsystem Vinay Kumar.S.B, Manjula N Harihar Abstract— The Diameter protocol was initially developed by II. ROLE OF DIAMETER IN IMS the Internet Engineering Task Force (IETF) as an Authentication, Authorization, and Accounting (AAA) framework The IMS is based on a horizontally layered architecture, intended for applications such as remote network access and IP consisting of three layers, namely, Service Layer, Control mobility. Diameter was further embraced by the Third Generation Layer, and Connectivity Layer. Service Layer comprises Partnership Project (3GPP) as the key protocol for AAA and application and content servers to execute value-added mobility management in 3G networks. The paper discusses the use services for the user. Control layer comprises network control of Diameter in the scope of the IP Multimedia Subsystem (IMS) as servers for managing call or session set-up, modification and specified by 3GPP. This paper presents a solution for the problem release. The most important of these is the Call Session of how to provide authentication, authorization and accounting Control Function (CSCF). Connectivity Layer comprises of (AAA) for multi-domain interacting services by referring open routers and switches, for both the backbone and the access diameter. We have studied the case of ‘FoneFreez’, a service that provides interaction between different basic services, like network telephony and television. The involvement of several parties like A. IMS functions television provider, telephony provider etc., secure interaction between multiple domains must be assured. -

The Concepts of Connected Car and Internet of Cars and Their Impact on Future People Mobility
INFORMATION SYSTEMS IN MANAGEMENT Information Systems in Management (2017) Vol. 6 (3) 234 −245 THE CONCEPTS OF CONNECTED CAR AND INTERNET OF CARS AND THEIR IMPACT ON FUTURE PEOPLE MOBILITY AGNIESZKA SZMELTER Department of Logistics, University of Gda ńsk (UG) Technological convergence has had a huge impact on development of automo- tive industry. Two main concepts related to mobile technology and the Internet of Things (IoT) in this industry are car connectivity and Internet of Cars (IoC). The ar- ticle aims to present these two concepts with special emphasis on the characteristics of people mobility in future cities. Keywords: automotive, logistics, information logistics, convergence, technological convergence, internet of things, internet of cars, connected car, car connectivity, mobility, public transport. 1. Introduction The global economy, which is currently characterized by development of mo- bile and Internet technologies, is in large part composed of the services sector. A new paradigm appeared: information and communication technologies enable achievement of the economic and / or social objectives by use of cooperation methods (including sharing). ICT contribute to the acceleration of economic recov- ery and the creation of "sustainable digital future" [7]. This paper aims to achieve cognitive objective, which is to present the impact of technological developments in automotive industry (especially the concepts of car connectivity and Internet of Cars) on the development of new people mobility behaviour in cities. The author hypothesizes that technological convergence, pre- sent in currently-sold cars and cars of the future significantly contributes and will contribute to development of new patterns of mobility in cities. The main research method used in the study is analysis of secondary sources, including literature and branch studies made by experts in automotive industry.