Dipartimento Di Informatica E Scienze Dell'informazione
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

1.3 Μm Emitting Srf2:Nd3+ Nanoparticles for High Contrast In
Nano Research 1 DOINano 10.1007/s12274Res -014-0549-1 3+ 1.3 µm emitting SrF2:Nd nanoparticles for high contrast in vivo imaging in the second biological window. Irene Villa1, Anna Vedda1, Irene Xochilt Cantarelli2, Marco Pedroni2, Fabio Piccinelli2, Marco Bettinelli2, Adolfo Speghini2, Marta Quintanilla3, Fiorenzo Vetrone3, Ueslen Rocha4, Carlos Jacinto4, Elisa Carrasco5, Francisco Sanz Rodríguez5, Ángeles Juarranz de la Cruz5, Blanca del Rosal6, Dirk H. Ortgies6, Patricia Haro Gonzalez6, José García Solé6, and Daniel Jaque García6 () Nano Res., Just Accepted Manuscript • DOI: 10.1007/s12274-014-0549-1 http://www.thenanoresearch.com on July 29, 2014 © Tsinghua University Press 2014 Just Accepted This is a “Just Accepted” manuscript, which has been examined by the peer-review process and has been accepted for publication. A “Just Accepted” manuscript is published online shortly after its acceptance, which is prior to technical editing and formatting and author proofing. Tsinghua University Press (TUP) provides “Just Accepted” as an optional and free service which allows authors to make their results available to the research community as soon as possible after acceptance. After a manuscript has been technically edited and formatted, it will be removed from the “Just Accepted” Web site and published as an ASAP article. Please note that technical editing may introduce minor changes to the manuscript text and/or graphics which may affect the content, and all legal disclaimers that apply to the journal pertain. In no event shall TUP be held responsible for errors or consequences arising from the use of any information contained in these “Just Accepted” manuscripts. To cite this manuscript please use its Digital Object Identifier (DOI®), which is identical for all formats of publication. -
Ironpython in Action
IronPytho IN ACTION Michael J. Foord Christian Muirhead FOREWORD BY JIM HUGUNIN MANNING IronPython in Action Download at Boykma.Com Licensed to Deborah Christiansen <[email protected]> Download at Boykma.Com Licensed to Deborah Christiansen <[email protected]> IronPython in Action MICHAEL J. FOORD CHRISTIAN MUIRHEAD MANNING Greenwich (74° w. long.) Download at Boykma.Com Licensed to Deborah Christiansen <[email protected]> For online information and ordering of this and other Manning books, please visit www.manning.com. The publisher offers discounts on this book when ordered in quantity. For more information, please contact Special Sales Department Manning Publications Co. Sound View Court 3B fax: (609) 877-8256 Greenwich, CT 06830 email: [email protected] ©2009 by Manning Publications Co. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by means electronic, mechanical, photocopying, or otherwise, without prior written permission of the publisher. Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. Where those designations appear in the book, and Manning Publications was aware of a trademark claim, the designations have been printed in initial caps or all caps. Recognizing the importance of preserving what has been written, it is Manning’s policy to have the books we publish printed on acid-free paper, and we exert our best efforts to that end. Recognizing also our responsibility to conserve the resources of our planet, Manning books are printed on paper that is at least 15% recycled and processed without the use of elemental chlorine. -

Project Verona
Are we done? We now have a perfectly - secure cipher ! No ! are ! In fact as as the . - - if we can share of this can use same mechanism to Keys very long , long message keys length , " [ the itself ) • share " message One-time restriction Malleable Issues with the one-time pad: - : . Never . ! One-time Very important reuse the one-time pad to encrypt two messages Completely broken = ① = ① Mz C k M , and Cz k Suppose , = C +0 ④ k ⑦ Mz can this to recover Then , ④ Cz (k mi) ( ) , f- leverage messages = ← m ④ Mz learn the ✗or of two ! , messages One-time pad reuse : - Verona . Project (US counter-intelligence operation against U.s.sk during Cold War) ↳ ~ Soviets reused some in codebook to of ~ 3000 sent Soviet pages led decryption messages by intelligence over 37- year period [notably exposed espionage by Julius and Ethel Rosenberg ] - Microsoft Point-to-point Tunneling CMS- PPTP) in Windows 98 /NT (used for VPN) ↳ Same key (in stream cipher) used for both server → client communication AND for client → server ↳ communication (RCH) - 802.11 : client and server use WEP both same key to encrypt traffic one-time reuse (can even recover small many problems just beyond pad key after observing number of frames ! ) - : one-time no can the : M#ble pad provides integrity ; anyone modify ciphertext m ← K +0 C ← ' replace c with c. ④ m ' ' ⇒ = k ④ c ④ m ④ m ← 's cored into ( ) m adversary change now ✗ original message . a then tem If satisfies 114/3 / Ml . cipher perfect secrecy , : s to most . This that about Intuition Every ciphertext can decrypt at 1kt IMI messages means ciphertext leaks information the all Cannot be . -
Toolbox of Action
AlpInnoCT Toolbox of Action Solutions and approaches for Combined Transport in the Alpine Space Handbook with results from the AlpInnoCT Project Foreword 03 Combined Transport in the Alpine Space — RoLa – Rolling Highway. Source: www.ralpin.com/media/ Results from the AlpInnoCT Project The Alps are a sensitive ecosystem to be protected from pollutant emissions & climate change. Continued growth in freight traffic ModaLohr. Source: www.txlogistik.eu/ volume leads to environmental and social problems. These trends reinforce the need to review existing transport modes & develop innovative models to protect the Alpine Space. Therefore, the project Alpine Innovation for Combined Transport (AlpInnoCT) tackled the main challenges to raise CT efficiency and productivity. This included new approaches like the application of production industry knowhow as well as the analysis of existing strategies, policies and processes. Verona Quadrante Europa. Source:www.ferpress.it/ This Toolbox of Action summarizes the main results and aims transport-logistic2015- interporto-quadrante- to provide information for political and economic decision makers europa-presentazione- and the civil society, on how Combined Transport can be fostered progetto-easyconnecting/ in Europe and the Alpine Space for a successful shift of freight traffic, from road to rail. The AlpInnoCT project was carried out in the framework of the Alpine Space Programme – European Territorial Cooperation 2014 – 2020 (INTERREG VB), funded by the European Regional Development Fund (ERDF) and national -

Commerce Parkway, Verona, WI 53593 P608.845.7930 F608.845.5648 Engineeredconstruction.Com
ENGINEERED CONSTRUCTION, INC. 525 Commerce Parkway, Verona, WI 53593 p608.845.7930 f608.845.5648 engineeredconstruction.com 6515 Grand Teton Plaza, Suite 120, Madison, Wisconsin 53719 p608.829.4444 f608.829.4445 dimensionivmadison.com Beale Enterprises LLC 529 Commerce Parkway Verona, WI 53593 Architecture : Dimension IV − Madison Design Group 6515 Grand Teton Plaza, Suite 120, Madison, WI 53719 p: 608.829.4444 www.dimensionivmadison.com General Engineered Construction, Inc. Contractor: 525 Commerce Parkway, Verona, WI 53593 p: 608.845.7930 engineeredconstruction.com PROJECT/BUILDING DATA: CODE INFORMATION SUMMARY: NEW 1 STORY BUILDING APPLICABLE CODE 2009 WISCONSIN COMMERCIAL BUILDING CODE BUILDING AREAS 2009 INTERNATION BUILDING CODE TOTAL BUILDING AREA = 8,525SF FIRST FLOOR AREA = 8,125 SF CONSTRUCTION TYPE MEZZANINE FLOOR AREA = 400 SF TYPE VB = 1 STORY BUILDING PARKING COUNTS OCCUPANCY ARCHITECTURAL ABBREVIATIONS LEGEND TOTAL PARKING SPACES = 6 S1 - STORAGE (PRIVATE GARAGE) FIRE SPRINKLER + - AND FIN - FINISH PREFAB - PREFABRICATED BUILDING IS NON SPRINKLERED @ - AT FLR - FLOOR PERIM - PERIMETER AB - ANCHOR BOLT FND - FOUNDATION PC - PLUMBING CONTRACTOR AFF - ABOVE FINISH FLOOR FOM - FACE OF MASONRY P/C - PRECAST / PRESTRESSED FIRE RESISTANCE RATING BUILDING ELEMENTS RENDERING IS REPRESENTATIVE ONLY - SEE DOCUMENTS FOR ALL BUILDING INFORMATION LIST OF DRAWINGS ALT - ALTERNATE FOS - FACE OF STUD P/T - POST TENSIONED STRUCTURAL FRAME (COLUMNS & BEAMS) = 0 HOUR ALUM - ALUMINUM FTG - FOOTING PT - PRESSURE TREATED PROJECT PERSPECTIVE BEARING WALLS (EXTERIOR AND INTERIOR) = 0 HOUR ARCH - ARCHITECT / ARCHITECTURAL FUT - FUTURE NON-BEARING WALLS (EXTERIOR) = SHEET FV - FIELD VERIFY R - RADIUS 0 HOUR < 30' TO PROPERTY LINE BRD - BOARD RD - ROOF DRAIN NO RATING > 30' TO PROPERTY LINE NO. -
Working with Ironpython and WPF
Working with IronPython and WPF Douglas Blank Bryn Mawr College Programming Paradigms Spring 2010 With thanks to: http://www.ironpython.info/ http://devhawk.net/ IronPython Demo with WPF >>> import clr >>> clr.AddReference("PresentationFramework") >>> from System.Windows import * >>> window = Window() >>> window.Title = "Hello" >>> window.Show() >>> button = Controls.Button() >>> button.Content = "Push Me" >>> panel = Controls.StackPanel() >>> window.Content = panel >>> panel.Children.Add(button) 0 >>> app = System.Windows.Application() >>> app.Run(window) XAML Example: Main.xaml <Window xmlns="http://schemas.microsoft.com/winfx/2006/xaml/presentation" xmlns: x="http://schemas.microsoft.com/winfx/2006/xaml" Title="TestApp" Width="640" Height="480"> <StackPanel> <Label>Iron Python and WPF</Label> <ListBox Grid.Column="0" x:Name="listbox1" > <ListBox.ItemTemplate> <DataTemplate> <TextBlock Text="{Binding Path=title}" /> </DataTemplate> </ListBox.ItemTemplate> </ListBox> </StackPanel> </Window> IronPython + XAML import sys if 'win' in sys.platform: import pythoncom pythoncom.CoInitialize() import clr clr.AddReference("System.Xml") clr.AddReference("PresentationFramework") clr.AddReference("PresentationCore") from System.IO import StringReader from System.Xml import XmlReader from System.Windows.Markup import XamlReader, XamlWriter from System.Windows import Window, Application xaml = """<Window xmlns="http://schemas.microsoft.com/winfx/2006/xaml/presentation" Title="XamlReader Example" Width="300" Height="200"> <StackPanel Margin="5"> <Button -

Visual Studio 2010 Tools for Sharepoint Development
Visual Studio 2010 for SharePoint Open XML and Content Controls COLUMNS Toolbox Visual Studio 2010 Tools for User Interfaces, Podcasts, Object-Relational Mappings SharePoint Development and More Steve Fox page 44 Scott Mitchell page 9 CLR Inside Out Profi ling the .NET Garbage- Collected Heap Subramanian Ramaswamy & Vance Morrison page 13 Event Tracing Event Tracing for Windows Basic Instincts Collection and Array Initializers in Visual Basic 2010 Generating Documents from SharePoint Using Open XML Adrian Spotty Bowles page 20 Content Controls Data Points Eric White page 52 Data Validation with Silverlight 3 and the DataForm John Papa page 30 Cutting Edge Data Binding in ASP.NET AJAX 4.0 Dino Esposito page 36 Patterns in Practice Functional Programming Core Instrumentation Events in Windows 7, Part 2 for Everyday .NET Developers MSDN Magazine Dr. Insung Park & Alex Bendetov page 60 Jeremy Miller page 68 Service Station Building RESTful Clients THIS MONTH at msdn.microsoft.com/magazine: Jon Flanders page 76 CONTRACT-FIRST WEB SERVICES: Schema-Based Development Foundations with Windows Communication Foundation Routers in the Service Bus Christian Weyer & Buddihke de Silva Juval Lowy page 82 TEST RUN: Partial Anitrandom String Testing Concurrent Affairs James McCaffrey Four Ways to Use the Concurrency TEAM SYSTEM: Customizing Work Items Runtime in Your C++ Projects Rick Molloy page 90 OCTOBER Brian A. Randell USABILITY IN PRACTICE: Getting Inside Your Users’ Heads 2009 Charles B. Kreitzberg & Ambrose Little Vol 24 No 10 Vol OCTOBER 2009 VOL 24 NO 10 OCTOBER 2009 VOLUME 24 NUMBER 10 LUCINDA ROWLEY Director EDITORIAL: [email protected] HOWARD DIERKING Editor-in-Chief WEB SITE MICHAEL RICHTER Webmaster CONTRIBUTING EDITORS Don Box, Keith Brown, Dino Esposito, Juval Lowy, Dr. -
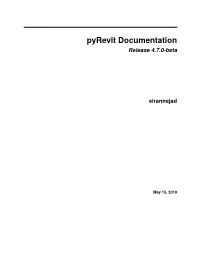
Pyrevit Documentation Release 4.7.0-Beta
pyRevit Documentation Release 4.7.0-beta eirannejad May 15, 2019 Getting Started 1 How To Use This Documents3 2 Create Your First Command5 3 Anatomy of a pyRevit Script 7 3.1 Script Metadata Variables........................................7 3.2 pyrevit.script Module...........................................9 3.3 Appendix A: Builtin Parameters Provided by pyRevit Engine..................... 12 3.4 Appendix B: System Category Names.................................. 13 4 Effective Output/Input 19 4.1 Clickable Element Links......................................... 19 4.2 Tables................................................... 20 4.3 Code Output............................................... 21 4.4 Progress bars............................................... 21 4.5 Standard Prompts............................................. 22 4.6 Standard Dialogs............................................. 26 4.7 Base Forms................................................ 35 4.8 Graphs.................................................. 37 5 Keyboard Shortcuts 45 5.1 Shift-Click: Alternate/Config Script................................... 45 5.2 Ctrl-Click: Debug Mode......................................... 45 5.3 Alt-Click: Show Script file in Explorer................................. 46 5.4 Ctrl-Shift-Alt-Click: Reload Engine................................... 46 5.5 Shift-Win-Click: pyRevit Button Context Menu............................. 46 6 Extensions and Commmands 47 6.1 Why do I need an Extension....................................... 47 6.2 Extensions............................................... -

Developers Toolkit Quickstart Guide
Developers Toolkit QuickStart Guide Generic steps for all projects: Create a new project Import the Kratos_3.dll .NET assembly The Newtonsoft.Json.dll is also required Refer to the sample projects for the following steps Create a FactSetOnDemand object from the Kratos_3.RunTimePlatform namespace Set-up configuration data Create FactSet calls to retrieve data .NET Languages .NET language (C++/CLI, C#, Visual Basic, Java) Example Open Visual Studio Create a new project of the appropriate language type Add a reference to the Kratos_3 dll Configure the build to the appropriate architecture (x86 if using the 32-bit dll or x64 if using the 64-bit dll) Create a new code file (Refer to the sample projects for the following steps) Import the Kratos_3.RunTimePlatform namespace Create a FactSetOnDemand object Set-up configuration data Create FactSet calls to retrieve data IronPython For IronPython Put the Kratos_3.dll NET assembly somewhere your program will be able to reference it. Make sure your dll architecture matches your IronPython architecture. If you installed the 32-bit IronPython, use the x86 Kratos_3 dll. If you installed the 64-bit version of IronPython, use the x64 dll. Make a new Python file Import the clr module. (The steps below can be viewed in the IronPython sample program) Use the clr reference to load the Kratos_3 dll Import the Kratos_#.RunTimePlatform namespace Create a FactSetOnDemand object Set-up the configuration data Create FactSet calls to retrieve data To run an IronPython project Open the windows command console (not the IronPython console) Type: “ipy <path to python program>” FactSet Research Systems Inc. -

Programming with Windows Forms
A P P E N D I X A ■ ■ ■ Programming with Windows Forms Since the release of the .NET platform (circa 2001), the base class libraries have included a particular API named Windows Forms, represented primarily by the System.Windows.Forms.dll assembly. The Windows Forms toolkit provides the types necessary to build desktop graphical user interfaces (GUIs), create custom controls, manage resources (e.g., string tables and icons), and perform other desktop- centric programming tasks. In addition, a separate API named GDI+ (represented by the System.Drawing.dll assembly) provides additional types that allow programmers to generate 2D graphics, interact with networked printers, and manipulate image data. The Windows Forms (and GDI+) APIs remain alive and well within the .NET 4.0 platform, and they will exist within the base class library for quite some time (arguably forever). However, Microsoft has shipped a brand new GUI toolkit called Windows Presentation Foundation (WPF) since the release of .NET 3.0. As you saw in Chapters 27-31, WPF provides a massive amount of horsepower that you can use to build bleeding-edge user interfaces, and it has become the preferred desktop API for today’s .NET graphical user interfaces. The point of this appendix, however, is to provide a tour of the traditional Windows Forms API. One reason it is helpful to understand the original programming model: you can find many existing Windows Forms applications out there that will need to be maintained for some time to come. Also, many desktop GUIs simply might not require the horsepower offered by WPF. -

Bounded Model Checking of Pointer Programs Revisited?
Bounded Model Checking of Pointer Programs Revisited? Witold Charatonik1 and Piotr Witkowski2 1 Institute of Computer Science, University of Wroclaw, [email protected] 2 [email protected] Abstract. Bounded model checking of pointer programs is a debugging technique for programs that manipulate dynamically allocated pointer structures on the heap. It is based on the following four observations. First, error conditions like dereference of a dangling pointer, are express- ible in a fragment of first-order logic with two-variables. Second, the fragment is closed under weakest preconditions wrt. finite paths. Third, data structures like trees, lists etc. are expressible by inductive predi- cates defined in a fragment of Datalog. Finally, the combination of the two fragments of the two-variable logic and Datalog is decidable. In this paper we improve this technique by extending the expressivity of the underlying logics. In a sequence of examples we demonstrate that the new logic is capable of modeling more sophisticated data structures with more complex dependencies on heaps and more complex analyses. 1 Introduction Automated verification of programs manipulating dynamically allocated pointer structures is a challenging and important problem. In [11] the authors proposed a bounded model checking (BMC) procedure for imperative programs that manipulate dynamically allocated pointer struc- tures on the heap. Although in this procedure an explicit bound is assumed on the length of the program execution, the size of the initial data structure is not bounded. Therefore, such programs form infinite and infinitely branching transition systems. The procedure is based on the following four observations. First, error conditions like dereference of a dangling pointer, are expressible in a fragment of first-order logic with two-variables. -

NET Hacking & In-Memory Malware
.NET Hacking & In-Memory Malware Shawn Edwards Shawn Edwards Cyber Adversarial Engineer The MITRE Corporation Hacker Maker Learner Take stuff apart. Change it. Put Motivated by an incessant Devoted to a continuous effort it back together. desire to create and craft. of learning and sharing knowledge. Red teamer. Adversary Numerous personal and emulator. professional projects. B.S. in Computer Science. Adversary Emulation @ MITRE • Red teaming, but specific threat actors • Use open-source knowledge of their TTPs to emulate their behavior and operations • Ensures techniques are accurate to real world • ATT&CK (Adversarial Tactics Techniques and Common Knowledge) • Public wiki of real-world adversary TTPs, software, and groups • CALDERA • Modular Automated Adversary Emulation framework Adversary Emulation @ MITRE • ATT&CK • Adversarial Tactics Techniques and Common Knowledge • Public wiki of real-world adversary TTPs, software, and groups • Lets blue team and red team speak in the same language • CALDERA • Modular Automated Adversary Emulation framework • Adversary Mode: • AI-driven “red team in a box” • Atomic Mode: • Define Adversaries, give them abilities, run operations. Customize everything at will. In-Memory Malware • Is not new • Process Injection has been around for a long time • Typically thought of as advanced tradecraft; not really • Surged in popularity recently • Made easier by open-source or commercial red team tools • For this talk, only discuss Windows malware • When relevant, will include the ATT&CK Technique ID In-Memory