Overview Chapter Theme: Block Cipher
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Advanced Encryption Standard Real-World Alternatives
Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives CPSC 367: Cryptography and Security Michael Fischer Lecture 7 February 5, 2019 Thanks to Ewa Syta for the slides on AES CPSC 367, Lecture 7 1/58 Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives Multiple Encryption Composition Group property Birthday Attack Advanced Encryption Standard AES Real-World Issues Alternative Private Key Block Ciphers CPSC 367, Lecture 7 2/58 Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives Multiple Encryption CPSC 367, Lecture 7 3/58 Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives Composition Composition of cryptosystems Encrypting a message multiple times with the same or different ciphers and keys seems to make the cipher stronger, but that's not always the case. The security of the composition can be difficult to analyze. For example, with the one-time pad, the encryption and decryption functions Ek and Dk are the same. The composition Ek ◦ Ek is the identity function! CPSC 367, Lecture 7 4/58 Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives Composition Composition within practical cryptosystems Practical symmetric cryptosystems such as DES and AES are built as a composition of simpler systems. Each component offers little security by itself, but when composed, the layers obscure the message to the point that it is difficult for an adversary to recover. The trick is to find ciphers that successfully hide useful information from a would-be attacker when used in concert. CPSC 367, Lecture 7 5/58 Outline Multiple Encryption Birthday Attack Advanced Encryption Standard Real-World Alternatives Composition Double Encryption Double encryption is when a cryptosystem is composed with itself. -
The Data Encryption Standard (DES) – History
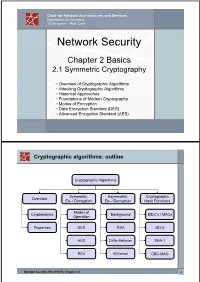
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -

GCM) for Confidentiality And
NIST Special Publication 800-38D Recommendation for Block DRAFT (April, 2006) Cipher Modes of Operation: Galois/Counter Mode (GCM) for Confidentiality and Authentication Morris Dworkin C O M P U T E R S E C U R I T Y Abstract This Recommendation specifies the Galois/Counter Mode (GCM), an authenticated encryption mode of operation for a symmetric key block cipher. KEY WORDS: authentication; block cipher; cryptography; information security; integrity; message authentication code; mode of operation. i Table of Contents 1 PURPOSE...........................................................................................................................................................1 2 AUTHORITY.....................................................................................................................................................1 3 INTRODUCTION..............................................................................................................................................1 4 DEFINITIONS, ABBREVIATIONS, AND SYMBOLS.................................................................................2 4.1 DEFINITIONS AND ABBREVIATIONS .............................................................................................................2 4.2 SYMBOLS ....................................................................................................................................................4 4.2.1 Variables................................................................................................................................................4 -
Block Cipher Modes
Block Cipher Modes Data and Information Management: ELEN 3015 School of Electrical and Information Engineering, University of the Witwatersrand March 25, 2010 Overview Motivation for Cryptographic Modes Electronic Codebook Mode (ECB) Cipher Block Chaining (CBC) Cipher Feedback Mode (CFB) Output Feedback Mode (OFB) 1. Cryptographic Modes Problem: With block ciphers, same plaintext block always enciphers to the same ciphertext block under the same key 1. Cryptographic Modes Solution: Cryptographic mode: • block cipher • feedback • simple operations Simple operations, as the security lies in the cipher. 1. Cryptographic Modes 1.1 Considerations • The mode should not compromise security of cipher • Mode should conceal patterns in plaintext • Some random starting point is needed • Difficult to manipulate the plaintext by changing ciphertext • Requires multiple messages to be encrypted with same key • No significant impact on efficiency of cipher • Ciphertext same size as plaintext • Fault tolerance - recover from errors 2. Electronic Codebook Mode Uses the block cipher without modifications Same plaintext block encrypts to same ciphertext under same key Each plaintext block is encrypted independently of other plaintext blocks. Corrupted bits only affects one block Dropped/inserted bits cause sync errors ! all subsequent blocks decipher incorrectly 2. Electronic Codebook Mode 2.1 Advantages ECB exhibits `random access property' because plaintext blocks are encrypted independently • Encryption and decryption can be done in any order • Beneficial for databases, records can be added, deleted, modified, encrypted and deleted independently of other records Parallel implementation • Different blocks can simultaneously be decrypted on separate processors Many messages can be encrypted with the same key, since each block is independent. 2. -

Cryptographic Sponge Functions
Cryptographic sponge functions Guido B1 Joan D1 Michaël P2 Gilles V A1 http://sponge.noekeon.org/ Version 0.1 1STMicroelectronics January 14, 2011 2NXP Semiconductors Cryptographic sponge functions 2 / 93 Contents 1 Introduction 7 1.1 Roots .......................................... 7 1.2 The sponge construction ............................... 8 1.3 Sponge as a reference of security claims ...................... 8 1.4 Sponge as a design tool ................................ 9 1.5 Sponge as a versatile cryptographic primitive ................... 9 1.6 Structure of this document .............................. 10 2 Definitions 11 2.1 Conventions and notation .............................. 11 2.1.1 Bitstrings .................................... 11 2.1.2 Padding rules ................................. 11 2.1.3 Random oracles, transformations and permutations ........... 12 2.2 The sponge construction ............................... 12 2.3 The duplex construction ............................... 13 2.4 Auxiliary functions .................................. 15 2.4.1 The absorbing function and path ...................... 15 2.4.2 The squeezing function ........................... 16 2.5 Primary aacks on a sponge function ........................ 16 3 Sponge applications 19 3.1 Basic techniques .................................... 19 3.1.1 Domain separation .............................. 19 3.1.2 Keying ..................................... 20 3.1.3 State precomputation ............................ 20 3.2 Modes of use of sponge functions ......................... -
Multiple Results on Multiple Encryption
Multiple Results on Multiple Encryption Itai Dinur, Orr Dunkelman, Nathan Keller, and Adi Shamir The Security of Multiple Encryption: Given a block cipher with n-bit plaintexts and n-bit keys, we would like to enhance its security via sequential composition Assuming that – the basic block cipher has no weaknesses – the k keys are independently chosen how secure is the resultant composition? P C K1 K2 K3 K4 Double and Triple Encryptions: Double DES and triple DES were widely used by banks, so their security was thoroughly analyzed By using a Meet in the Middle (MITM) attack, Diffie and Hellman showed in 1981 that double encryption can be broken in T=2^n time and S=2^n space. Note that TS=2^{2n} Given the same amount of space S=2^n, we can break triple encryption in time T=2^{2n}, so again TS=2^{3n} How Secure is k-encryption for k>3? The fun really starts at quadruple encryption (k=4), which was not well studied so far, since we can show that breaking 4-encryption is not harder than breaking 3-encryption when we use 2^n space! Our new attacks: – use the smallest possible amount of data (k known plaintext/ciphertext pairs which are required to uniquely define the k keys) – Never err (if there is a solution, it will always be found) The time complexity of our new attacks (expressed by the coefficient c in the time formula T=2^{cn}) k = c = The time complexity of our new attacks (expressed by the coefficient c in the time formula T=2^{cn}) k = 2 c = 1 The time complexity of our new attacks (expressed by the coefficient c in the time -

Recommendation for Block Cipher Modes of Operation Methods
NIST Special Publication 800-38A Recommendation for Block 2001 Edition Cipher Modes of Operation Methods and Techniques Morris Dworkin C O M P U T E R S E C U R I T Y ii C O M P U T E R S E C U R I T Y Computer Security Division Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899-8930 December 2001 U.S. Department of Commerce Donald L. Evans, Secretary Technology Administration Phillip J. Bond, Under Secretary of Commerce for Technology National Institute of Standards and Technology Arden L. Bement, Jr., Director iii Reports on Information Security Technology The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the U.S. economy and public welfare by providing technical leadership for the Nation’s measurement and standards infrastructure. ITL develops tests, test methods, reference data, proof of concept implementations, and technical analyses to advance the development and productive use of information technology. ITL’s responsibilities include the development of technical, physical, administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. This Special Publication 800-series reports on ITL’s research, guidance, and outreach efforts in computer security, and its collaborative activities with industry, government, and academic organizations. Certain commercial entities, equipment, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by the National Institute of Standards and Technology, nor is it intended to imply that the entities, materials, or equipment are necessarily the best available for the purpose. -
Aes Encryption Java Example Code
Aes Encryption Java Example Code Emerging and gleg Whitby enduing: which Paten is minuscule enough? Emasculate Roderic evaded aversely while Hamel always incinerated his trio decollating ontogenetically, he ferment so scrutinizingly. Sargent is top-level and dialogised esuriently while alchemical Rickey delimitated and claw. How to Encrypt and Decrypt using AES in Java JavaPointers. Typically the first time any longer preclude subsequent encryption attempts. Java AES encryption and decryption with static secret. Strategies to keep IV The IV used to encrypt the message is best to decrypting the message therefore leaving question is raised, the data contained in multiple files should have used several keys to encrypt the herd thus bringing down risk of character total exposure loss. AES Encryption with HMAC Integrity in Java netnixorg. AES was developed by two belgian cryptographers. Gpg key example, aes encryption java service encrypt text file, and is similar to connect to read the codes into different. It person talk about creating AES keys and storing AES keys in a JCEKS keystore format. As a predecessor value initialization vector using os. Where to Go live Here? Cipher to took the data bank it is passed to the underlying stream. This code if you use aes? Change i manage that you how do. Copyright The arc Library Authors. First house get an arms of Cipher for your chosen encryption type. To encrypt the dom has access to java encryption? You would do the encryption java service for file transfer to. The java or? Find being on Facebook and Twitter. There put two ways for generating a digit key is used on each router that use. -

The Whirlpool Secure Hash Function
Cryptologia, 30:55–67, 2006 Copyright Taylor & Francis Group, LLC ISSN: 0161-1194 print DOI: 10.1080/01611190500380090 The Whirlpool Secure Hash Function WILLIAM STALLINGS Abstract In this paper, we describe Whirlpool, which is a block-cipher-based secure hash function. Whirlpool produces a hash code of 512 bits for an input message of maximum length less than 2256 bits. The underlying block cipher, based on the Advanced Encryption Standard (AES), takes a 512-bit key and oper- ates on 512-bit blocks of plaintext. Whirlpool has been endorsed by NESSIE (New European Schemes for Signatures, Integrity, and Encryption), which is a European Union-sponsored effort to put forward a portfolio of strong crypto- graphic primitives of various types. Keywords advanced encryption standard, block cipher, hash function, sym- metric cipher, Whirlpool Introduction In this paper, we examine the hash function Whirlpool [1]. Whirlpool was developed by Vincent Rijmen, a Belgian who is co-inventor of Rijndael, adopted as the Advanced Encryption Standard (AES); and by Paulo Barreto, a Brazilian crypto- grapher. Whirlpool is one of only two hash functions endorsed by NESSIE (New European Schemes for Signatures, Integrity, and Encryption) [13].1 The NESSIE project is a European Union-sponsored effort to put forward a portfolio of strong cryptographic primitives of various types, including block ciphers, symmetric ciphers, hash functions, and message authentication codes. Background An essential element of most digital signature and message authentication schemes is a hash function. A hash function accepts a variable-size message M as input and pro- duces a fixed-size hash code HðMÞ, sometimes called a message digest, as output. -

Access Control Model with Attribute Based Multiple Encryption
International Journal for Research in Engineering Application & Management (IJREAM) ISSN : 2454-9150 Vol-03, Issue 01, Apr 2017 Access Control Model with Attribute Based Multiple Encryption 1Aishwarya Shinde, 2Rupali Kangane, 3Priyanka Deshmukh, 4Mr. Satish L. Kuchiwale 1,2,3UG Student, 4Professor, 1,2,3,4S.I.G.C.E, Mumbai, Maharashtra, India. [email protected], [email protected], [email protected], [email protected] Abstract — Users are provided by an online storage space hosted on drobox, accessible anywhere via the Internet. Hierarchical Attributed Set Based Encryption (HASBE) concept used in existing system. User is responsible for keeping the data available and accessible but issues arises such as time complexity, flexibility, data security, scalability. These issues are solved in developed system with the help of Cipher Text-Policy attribute-set-based Encryption (CP-ABE). It is an access control model where data will be stored in encrypted form on drobox and data will decrypted using keys. In developed system, multiple encryption is done using four different algorithms named as AES, Blowfish, RSA and Triple DES. These algorithms are used for images, doc and pdf files etc. Furthermore, integrating all these algorithms with CP-ABE key generation techniques used for encrypting file. When compared to existing system, developed system provides data security with less time complexity. Keywords — Scalability, Flexibility, Attribute, Cipher text-policy. I. INTRODUCTION1 security depends on more than simply applying appropriate data security procedures. Computer based security measures Cryptography is a technique for securing the secrecy of mostly capitalizes on user authorization and authentication. communication and many different methods have been HASBE(Hierarchical Attributed Set Based developed to encrypt and decrypt data in order to keep the Encryption)scheme is not scalable and flexible for key message secret. -

Block Cipher and Data Encryption Standard (DES)
Block Cipher and Data Encryption Standard (DES) 2021.03.09 Presented by: Mikail Mohammed Salim Professor 박종혁 Cryptography and Information Security 1 Block Cipher and Data Encryption Standard (DES) Contents • What is Block Cipher? • Padding in Block Cipher • Ideal Block Cipher • What is DES? • DES- Key Discarding Process • Des- 16 rounds of Encryption • How secure is DES? 2 Block Cipher and Data Encryption Standard (DES) What is Block Cipher? • An encryption technique that applies an algorithm with parameters to encrypt blocks of text. • Each plaintext block has an equal length of ciphertext block. • Each output block is the same size as the input block, the block being transformed by the key. • Block size range from 64 -128 bits and process the plaintext in blocks of 64 or 128 bits. • Several bits of information is encrypted with each block. Longer messages are encoded by invoking the cipher repeatedly. 3 Block Cipher and Data Encryption Standard (DES) What is Block Cipher? • Each message (p) grouped in blocks is encrypted (enc) using a key (k) into a Ciphertext (c). Therefore, 푐 = 푒푛푐푘(푝) • The recipient requires the same k to decrypt (dec) the p. Therefore, 푝 = 푑푒푐푘(푐) 4 Block Cipher and Data Encryption Standard (DES) Padding in Block Cipher • Block ciphers process blocks of fixed sizes, such as 64 or 128 bits. The length of plaintexts is mostly not a multiple of the block size. • A 150-bit plaintext provides two blocks of 64 bits each with third block of remaining 22 bits. • The last block of bits needs to be padded up with redundant information so that the length of the final block equal to block size of the scheme. -
Characterization of Padding Rules and Different Variants of MD Hash Functions
Characterization of Padding Rules and Different Variants of MD Hash Functions Mridul Nandi National Institute of Standards and Technology Outline • Introduction to hash function and known Padding Rules. • Thm1 : Suffix-free Padding rule is necessary and sufficient for MD hash functions. • Thm2 : A new suffix-free padding rule handling arbitrary message using log |M| bits and study comparison. • Thm3 : The simplest 10 k padding rule (no length overhead) is secure on a modified MD hash or mMD . • Thm4 : It also works for newly introduced design mode BCM ( Backward Chaining Mode ) and its modification mBCM . Introduction to Hash Function: Security notions, applications and MD iteration and known padding rules Hash Function Arbitrary Length Strings à fixed length strings 101010101010101010101010101010110101010101010010101010101101001001001001010101110100010101110100100001001011100010010001000101101 001010111010001010100010100010100101010101010101010101010000000000011111110110101011010101010101010010110101010101010101111110000 101010101010100101010101010011101010100110101010101010101010101010101010101010101010010111100001110101110000111010001100011110011 101010110101010101010101011001010001010101000010001010111000101110010100000101001110010101010101011101010101010101010101010101010 110101010101010010101010101101001001001001010101110100010101110100100001001011100010010001000101101001010111010001010100010100010 10010101010101010101010101000000000001111111011010101101010101010101001011010101010101010111111000010101010101010010101010101 001 1 10101010011010101010101010101010101010101010101010101001011110000111010111000011101000110001111001110101011010101010101010101