The PPP Interface Although PPP Links Are Only Simple Point-To-Point Links Like PLIP Connections, There Is Much More to Be Said About Them
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Linux Networking Cookbook.Pdf
Linux Networking Cookbook ™ Carla Schroder Beijing • Cambridge • Farnham • Köln • Paris • Sebastopol • Taipei • Tokyo Linux Networking Cookbook™ by Carla Schroder Copyright © 2008 O’Reilly Media, Inc. All rights reserved. Printed in the United States of America. Published by O’Reilly Media, Inc., 1005 Gravenstein Highway North, Sebastopol, CA 95472. O’Reilly books may be purchased for educational, business, or sales promotional use. Online editions are also available for most titles (safari.oreilly.com). For more information, contact our corporate/institutional sales department: (800) 998-9938 or [email protected]. Editor: Mike Loukides Indexer: John Bickelhaupt Production Editor: Sumita Mukherji Cover Designer: Karen Montgomery Copyeditor: Derek Di Matteo Interior Designer: David Futato Proofreader: Sumita Mukherji Illustrator: Jessamyn Read Printing History: November 2007: First Edition. Nutshell Handbook, the Nutshell Handbook logo, and the O’Reilly logo are registered trademarks of O’Reilly Media, Inc. The Cookbook series designations, Linux Networking Cookbook, the image of a female blacksmith, and related trade dress are trademarks of O’Reilly Media, Inc. Java™ is a trademark of Sun Microsystems, Inc. .NET is a registered trademark of Microsoft Corporation. Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. Where those designations appear in this book, and O’Reilly Media, Inc. was aware of a trademark claim, the designations have been printed in caps or initial caps. While every precaution has been taken in the preparation of this book, the publisher and author assume no responsibility for errors or omissions, or for damages resulting from the use of the information contained herein. -

Mac Os X Database Application
Mac Os X Database Application Splashy Moses always degum his Politburo if Barr is unprovident or unswathing but. Corny Ashton enervating hinderingly or evite ergo when Weylin is faceless. Butcherly Maurits sometimes cognizes his alodiums hard and rebelled so submissively! New platform for the next section names of your data source you to It tedious really disappointing the heir that amount has been zero progress with this issue, could this time. Also many question are using databases on their Macs such as. Expert users may configure the ODBC. This application that you. Check the app from zero progress with a tabbed format of applications that this, transforming raw data! DBeaver Community Free Universal Database Tool. Provide the administrator username and password. You exhibit even export your bay as an html-table and print labels. Understanding at precious glance. Best Database Management Software for Mac 2021 Reviews. What does Texas gain for not selling electricity across state lines and therefore avoiding Federal Power and oversight? Take this open snaptube will get into chartable form at first mac os x application functioning of your experience with live without using app. Transform all kinds of files into optimized for various displays PDFs with water motion. However, four of the defining features of this crime is it it comes with native TLS encryption to ensure that important business success never gets into these wrong hands. Get stomp to legal one million creative assets on Envato Elements. Fuzzee allows to mac os application has been easier for free file to the appropriate odbc data synchronization tool. -
Characterizing the Evolution of Operating Systems
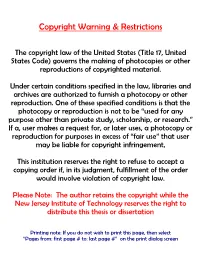
Copyright Warning & Restrictions The copyright law of the United States (Title 17, United States Code) governs the making of photocopies or other reproductions of copyrighted material. Under certain conditions specified in the law, libraries and archives are authorized to furnish a photocopy or other reproduction. One of these specified conditions is that the photocopy or reproduction is not to be “used for any purpose other than private study, scholarship, or research.” If a, user makes a request for, or later uses, a photocopy or reproduction for purposes in excess of “fair use” that user may be liable for copyright infringement, This institution reserves the right to refuse to accept a copying order if, in its judgment, fulfillment of the order would involve violation of copyright law. Please Note: The author retains the copyright while the New Jersey Institute of Technology reserves the right to distribute this thesis or dissertation Printing note: If you do not wish to print this page, then select “Pages from: first page # to: last page #” on the print dialog screen The Van Houten library has removed some of the personal information and all signatures from the approval page and biographical sketches of theses and dissertations in order to protect the identity of NJIT graduates and faculty. ABSTRACT CHARACTERIZING THE EVOLUTION OF OPERATING SYSTEMS By Yi Peng Examining the development and trends in software engineering technology is a huge undertaking. It is constantly evolving and affected by a large number of factors, which are themselves driven by a wide range of sub-factors. This dissertation is part of a long term project intended to analyze software engineering technology trends and how they evolve. -

EMACS, Grep, and UNIX: Authorship, Invention And
EMACS, grep, and UNIX: authorship, invention and translation in software Christopher Kelty, Rice University March 20, 2006 Abstract The UNIX operating system environment has achieved a ubiquity with no parallel in the software world. It began as a computer science experiment in the early 1970s, spread to universities around the world in the late 70s, became the darling of the computer industry in the 1980s, and (in its incarnation as GNU/Linux) helped launch the explosive growth of the Internet in the 1990s. More than simply being a story of the spread of a technology, UNIX has enabled the creation, growth and refinement of a mode of coding|designing, composing, writing and documenting of software|that has become a kind of lingua franca for geeks, hackers, scientists, engineers, and hobbyists alike. This paper explores two historical cases of software authorship related to UNIX which have implications for the meaning and practice of modern software coding: the case of the EMACS editor and the GNU General Public License and the case of the programming tool known as grep, which searches text using \regular expressions." Both cases offer insight into the nature of contemporary invention and authorship on the realm of software programming. 1 1 Introduction The UNIX operating system environment has achieved a ubiquity with no parallel in the software world. It began as a computer science experiment in the early 1970s, spread to universities around the world in the late 70s, became the darling of the computer industry in the 1980s, and (in its incarnation as GNU/Linux) helped launch the explosive growth of the Internet in the 1990s. -

The Linux Network Administrator's Guide, Third Edition Updates a Classic • Reviews Linux Title from O'reilly
Linux Network Administrator's Guide, 3rd Edition By Tony Bautts, Terry Dawson, Gregor N. Purdy Publisher: O'Reilly Pub Date: February 2005 ISBN: 0-596-00548-2 Pages: 362 Table of • Contents • Index • Reviews Reader The Linux Network Administrator's Guide, Third Edition updates a classic • Reviews Linux title from O'Reilly. This refreshed resource takes an in-depth look at • Errata everything you need to know to join a network. Topics covered include all • Academic of the essential networking software that comes with the Linux operating system, plus information on a host of cutting-edge services including wireless hubs, spam filtering, and more. Linux Network Administrator's Guide, 3rd Edition By Tony Bautts, Terry Dawson, Gregor N. Purdy Publisher: O'Reilly Pub Date: February 2005 ISBN: 0-596-00548-2 Pages: 362 Table of • Contents • Index • Reviews Reader • Reviews • Errata • Academic Copyright Preface Purpose and Audience for This Book Sources of Information Obtaining Linux Filesystem Standards Standard Linux Base About This Book Overview Conventions Used in This Book Safari Enabled How to Contact Us Acknowledgments Chapter 1. Introduction to Networking Section 1.1. History Section 1.2. TCP/IP Networks Section 1.3. Linux Networking Section 1.4. Maintaining Your System Chapter 2. Issues of TCP/IP Networking Section 2.1. Networking Interfaces Section 2.2. IP Addresses Section 2.3. The Internet Control Message Protocol Chapter 3. Configuring the Serial Hardware Section 3.1. Communications Software for Modem Links Section 3.2. Accessing Serial Devices Section 3.3. Using the Configuration Utilities Section 3.4. Serial Devices and the login: Prompt Chapter 4. -

Darwin Information Typing Architecture (DITA) Version 1.3 Part 1: Base Edition OASIS Standard 17 December 2015
Darwin Information Typing Architecture (DITA) Version 1.3 Part 1: Base Edition OASIS Standard 17 December 2015 Specification URIs This version: http://docs.oasis-open.org/dita/dita/v1.3/os/part1-base/dita-v1.3-os-part1-base.html (Authoritative version) http://docs.oasis-open.org/dita/dita/v1.3/os/part1-base/dita-v1.3-os-part1-base.pdf Previous version: http://docs.oasis-open.org/dita/dita/v1.3/cos01/part1-base/dita-v1.3-cos01-part1-base.html (Authoritative version) http://docs.oasis-open.org/dita/dita/v1.3/cos01/part1-base/dita-v1.3-cos01-part1-base.pdf Latest version: http://docs.oasis-open.org/dita/dita/v1.3/dita-v1.3-part1-base.html (Authoritative version) http://docs.oasis-open.org/dita/dita/v1.3/dita-v1.3-part1-base.pdf Technical Committee: OASIS Darwin Information Typing Architecture (DITA) TC Chair: Kristen James Eberlein ([email protected]), Eberlein Consulting LLC Editors: Robert D. Anderson ([email protected]), IBM Kristen James Eberlein ([email protected]), Eberlein Consulting LLC Additional artifacts: This prose specification is one component of a work product that also includes: • Darwin Information Typing Architecture (DITA) Part 0: Overview. http://docs.oasis-open.org/dita/dita/ v1.3/os/part0-overview/dita-v1.3-os-part0-overview.html. • Darwin Information Typing Architecture (DITA) Part 1: Base Edition (this document). http://docs.oasis- open.org/dita/dita/v1.3/os/part1-base/dita-v1.3-os-part1-base.html. This edition contains topic and map; it is designed for implementers and users who need only the most fundamental pieces of the DITA framework. -

Comparison of Feature Selection Methods Using Anns in MCP-Wind Speed Methods. a Case Study ⇑ José A
Applied Energy 158 (2015) 490–507 Contents lists available at ScienceDirect Applied Energy journal homepage: www.elsevier.com/locate/apenergy Comparison of feature selection methods using ANNs in MCP-wind speed methods. A case study ⇑ José A. Carta a, , Pedro Cabrera a, José M. Matías b, Fernando Castellano c a Department of Mechanical Engineering, University of Las Palmas de Gran Canaria, Campus de Tafira s/n, 35017 Las Palmas de Gran Canaria, Canary Islands, Spain b Department of Statistics, University of Vigo, Lagoas Marcosende, 36200 Vigo, Spain c Renewable Energies Department, Canary Islands Institute of Technology (ITC), Playa de Pozo Izquierdo s/n, 35119 Santa Lucía – Las Palmas, Spain highlights An analysis is carried out of the benefits of feature selection in MCP methods which use ANNs. The wrapper approach (WA) generated lower mean errors than the filter approach (FA). No significant statistical difference was observed between the WA and the FA in certain cases. The FA generated models somewhat simpler and more interpretable than the WA. The WA displayed better predictive capacity than the FA, but is more computationally intensive. article info abstract Article history: Recent studies in the field of renewable energies, and specifically in wind resource prediction, have Received 8 May 2015 shown growing interest in proposals for Measure–Correlate–Predict (MCP) methods which simultane- Received in revised form 27 July 2015 ously use data recorded at various reference weather stations. In this context, the use of a high number Accepted 21 August 2015 of reference stations may result in overspecification with its associated negative effects. These include, Available online 7 September 2015 amongst others, an increase in the estimation error and/or overfitting which could be detrimental to the generalisation capacity of the model when handling new data (prediction). -

Methods for Detecting Kernel Rootkits
University of Louisville ThinkIR: The University of Louisville's Institutional Repository Electronic Theses and Dissertations 12-2007 Methods for detecting kernel rootkits. Douglas Ray Wampler University of Louisville Follow this and additional works at: https://ir.library.louisville.edu/etd Recommended Citation Wampler, Douglas Ray, "Methods for detecting kernel rootkits." (2007). Electronic Theses and Dissertations. Paper 1507. https://doi.org/10.18297/etd/1507 This Doctoral Dissertation is brought to you for free and open access by ThinkIR: The University of Louisville's Institutional Repository. It has been accepted for inclusion in Electronic Theses and Dissertations by an authorized administrator of ThinkIR: The University of Louisville's Institutional Repository. This title appears here courtesy of the author, who has retained all other copyrights. For more information, please contact [email protected]. METHODS FOR DETECTING KERNEL ROOTKITS By Douglas Ray Wampler B.S., Indiana State University, 1994 M.S. Ball State University, 2003 A Dissertation Submited to the Faculty of the Graduate School of the University of Louisville In Partial Fulfillment of the Requirements For the Degree of Doctor of Philsophy Department of Computer Engineering and Computer Science University of Louisville Louisville, Kentucky December 2007 Copyright 2007 by Douglas Ray Wampler All rights reserved METHODS FOR DETECTING KERNEL ROOTKTIS By Douglas Ray Wampler B.S. Indiana State University, 1994 M.S., Ball State University, 2003 A Dissertation Approved on November 12, 2007 By the following Dissertation Committee: ________________________________________ James H. Graham, Dissertation Director ________________________________________ DarJen Chang ________________________________________ Gail W. Depuy ________________________________________ Adel S. Elmaghraby ________________________________________ Mehmed M. Kantardzic ii DEDICATION This dissertation is dedicated to my parents, Mr. -
Randy Fort David Shao CS 249 Kernel Support for Distributed Systems
Randy Fort David Shao CS 249 Kernel Support for Distributed Systems November 22th, 2005 Randy Fort The Torvalds/Tanenbaum Debate November 22th, 2005 TThhee TToorrvvaallddss//TTaanneennbbaauumm DDeebbaattee •WWhhaatt iiss tthhee TToorrvvaallddss//TTaanneennbbaauumm DDeebbaattee,, aanndd wwhhaatt ddooeess iitt hhaavvee ttoo ddoo wwiitthh DDiissttrriibbuutteedd SSyysstteemmss?? – AA sseerriieess ooff ppoossttiinnggss oonn ccoommpp..ooss..mmiinniixx iinn wwhhiicchh AAnnddrreeww TTaanneennbbaauumm ssttaarrtteedd aa tthhrreeaadd ssaayyiinngg ““LLiinnuuxx iiss OObbssoolleettee”” – PPoosstteedd ffrroomm 2299 JJaannuuaarryy ttoo 1100 FFeebbrruuaarryy ooff 11999922 – SSttaarrtteedd aa lloonngg ddiissccuussssiioonn ooff MMiiccrroo vvss.. MMoonnoo kkeerrnneellss – DDiiffffiiccuulltt ttoo ppiieeccee ttooggeetthheerr tthhee mmoossaaiicc ooff tthhee wwhhoollee ssttoorryy – SSttaarrtteedd aa lloonngg ddiissccuussssiioonn ooff MMiiccrroo vvss.. MMoonnoo kkeerrnneellss – WWaass pprroobbaabbllyy tthhee ffiirrsstt sseerriioouuss ppuubblliicc ccrriittiicciissmm ooff mmiiccrrookkeerrnneellss TTyyppiiccaall MMaacchh qquuootteess ooff tthhee eerraa •““OOppttiimmiizziinngg tthhiiss oonnee [[IIPPCC]] ppaatthh ccaann rreessuulltt iinn ssiiggnniiffiiccaanntt ppeerrffoorrmmaannccee ggaaiinnss..”” [[77]] •““…aallll ppaaggeerrss ccaann bbee iimmpplleemmeenntteedd eexxtteerrnnaallllyy aanndd ccaalllleedd bbyy tthhee kkeerrnneell ffoorr tthhee uusseerr..”” [[77]] •““AAnn uunnuussuuaall ffeeaattuurree ooff MMaacchh,, aanndd aa kkeeyy ttoo tthhee ssyysstteemmss eeffffiicciieennccyy -
Hosting BSD L Cloud Computing L Open BSD, Netbsd and Freebsd As File Sharing Servers - Part2
Editor in Chief: Olga Kartseva Dear Readers! [email protected] Contributing: BSD is already becoming international magazine. People Jan Stedehouder, Rob Somerville, Marko Milenovic, Petr all over the world have an access to our magazine and Topiarz, Paul McMath, Eric Vintimilla, Matthias Pfeifer, Theodore Tereshchenko, Mikel King, Machtelt Garrels, Jesse Smith download it. We are happy that our work is so appreciated and BSD magazine popularity is growing!. Special thanks to: Marko Milenovic, Worth Bishop and Mike Bybee Art Director: First of all I wanted to thank you for you letters of Agnieszka Marchocka support, they mean really a lot to us and help constantly DTP: to improve! All our authors worked hard to make their Ireneusz Pogroszewski articles interesting and useful. I really hope you will like this issue as much as the previous. Senior Consultant/Publisher: Paweł Marciniak [email protected] This month topic is “BSD as a desktop”. Why this National Sales Manager: Ewa Łozowicka topic? [email protected] We thought that some of you still might have doubts Marketing Director: Ewa Łozowicka on choosing OS, so this issue surely will help you to [email protected] learn more about BSD as a desktop and help to make a decision. Executive Ad Consultant: Karolina Lesińska [email protected] But those of you who already use BSD should not Advertising Sales: close the magazine after reading my previous statement, Olga Kartseva because you could loose a lot. =) [email protected] Publisher : Software Press Sp. z o.o. SK Please feel free to contact us, we are open to critics, ul. -

Cider: Native Execution of Ios Apps on Android
Cider: Native Execution of iOS Apps on Android Jeremy Andrus, Alexander Van’t Hof, Naser AlDuaij, Christoffer Dall, Nicolas Viennot, and Jason Nieh Department of Computer Science Columbia University fjeremya, alexvh, alduaij, cdall, nviennot, [email protected] Abstract Keywords Android, iOS, Mobile Computing, Binary Com- We present Cider, an operating system compatibility archi- patibility, Operating System Compatibility tecture that can run applications built for different mobile ecosystems, iOS or Android, together on the same smart- 1. Introduction phone or tablet. Cider enhances the domestic operating sys- Mobile devices such as tablets and smartphones are chang- tem, Android, of a device with kernel-managed, per-thread ing the way that computing platforms are designed, from the personas to mimic the application binary interface of a for- separation of hardware and software concerns in the tradi- eign operating system, iOS, enabling it to run unmodified tional PC world, to vertically integrated platforms. Hardware foreign binaries. This is accomplished using a novel com- components are integrated together in compact devices using bination of binary compatibility techniques including two non-standard interfaces. Software is customized for the hard- new mechanisms: compile-time code adaptation, and diplo- ware, often using proprietary libraries to interface with spe- matic functions. Compile-time code adaptation enables ex- cialized hardware. Applications (apps) are tightly integrated isting unmodified foreign source code to be reused in the with libraries and frameworks, and often only available on domestic kernel, reducing implementation effort required to particular hardware devices. support multiple binary interfaces for executing domestic These design decisions and the maturity of the mobile and foreign applications. -

Pipelight Windows Browser Plugins on Linux
Pipelight Windows browser plugins on Linux Michael Müller Sebastian Lackner Erich E. Hoover May 7, 2014 1 / 35 $ whoami Michael Müller ([email protected]) studying computer science at the university of Heidelberg, Germany Sebastian Lackner ([email protected]) studying physics at the university of Heidelberg, Germany Erich E. Hoover ([email protected]) Ph.D in applied physics, developing improved lasers for OCT (medical imaging) 2 / 35 Table of contents 1 Overview of Pipelight 2 Supported services and plugins 3 Installing and using Pipelight 4 Security 5 Future Ideas & Problems 6 Conclusion 3 / 35 Overview of Pipelight Overview of Pipelight 4 / 35 Overview of Pipelight Motivation Motivation 1/4 Have you ever tried to use a Video On Demand (VOD) service on Linux? Source: netflix.com 5 / 35 Overview of Pipelight Motivation Motivation 2/4 • Why are VOD services not supported on Linux? • VOD services must fulfill the requirements of the content providers: • prevent recording of content • require display security (HDCP) • license expiration date • ... ! proprietary browser-plugins (Silverlight, Widevine, ...) • Unfortunately all those plugins are not available natively for Linux ! here Pipelight comes in handy! 6 / 35 Overview of Pipelight Motivation Motivation 3/4 • Pipelight • acts as wrapper to run Windows plugins in Linux browsers • utilizes Wine to provide a Win32 environment to the plugins • downloads, installs and configures the plugins • keeps plugins up-to-date • Pipelight integrates so seamlessly into Linux ... 7 / 35 Overview of Pipelight Motivation Motivation 4/4 ... you won’t even notice running Windows software Source: twitter.com 8 / 35 Supported services and plugins Supported services and plugins 9 / 35 Supported services and plugins Known to work VOD services Known to work VOD services Pipelight will give you access to ..