SECURE INTER-VLAN Ipv6 ROUTING: IMPLEMENTATION & EVALUATION
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Symbols Numerics A
I N D E X GLOP, 484–485 Symbols IP multicast, 480 limited-scope, 484 ! (exclamation point) character, 105 MAC address notification, 317–318 # (pound sign) character, 105 NAT, 649 reserved link local, 483–484 Numerics source-specific multicast, 484 virtual MAC, 573 10-Gigabit, 54 adjacencies, 393–394, 408 10-Mbps Ethernet, 48 ADSL (asymmetric digital subscriber line), 56 802.1D, compatibility with RSTP, 230 agents, relay (DHCP), 379 802.1Q, 156–158 aggregate policers, 448 802.1X Aggressive mode UDLD (A-UDLD), 336–338, 604 configuration exercise, 663–669 configuration exercises, 354 network access security, 639–641 versus Loop Guard, 272 AppleTalk Remote, 624 applications A Auto QoS, 463 Cisco AVVID, 16 AAA statistics, 291 accounting, 625, 629 voice, 596 authentication, 173, 623–626 Application-Specific Integrated Circuits. See ASICs authorization, 624, 627 applying RACLs, 643 configuration exercise, 663–669 Architecture for Voice, Video and integrated Data. configuring, 630–631 See Cisco AVVID aaa authentication login command, 626 ARP (Address Resolution Protocol), 12 aaa new-model command, 87, 626 DAI, 654–658 access as a security feature, 658–659 firewalls, 647–648 throttling, 396–398 hopping attacks (VLAN), 660–661 ASICs (Application-Specific Integrated Circuits), physical, 619 5–6, 275 unauthorized, 77 assured forwarding, 431–432 access control lists. See ACLs asymmetric digital subscriber line (ADSL), 56 access layer, 18 attacks, 655, 660–661 access-layer switches, 50 attenuation, 720 accounting, 625, 629 A-UDLD (Aggressive mode UDLD), ACLs (access control lists), 4, 618, 643 336–338, 604 PACLs, 646 configuration exercises, 354 RACLs, 643 versus Loop Guard, 272 security, 642 authentication, 173, 623–626 VACLs, 644 authorization, 624, 627 vty lines, 619 auth-proxy, 627 active keyword, 513 Auto QoS, 463 adding switches, 186 auto-negotiation, 53, 767 Address Resolution Protocol. -
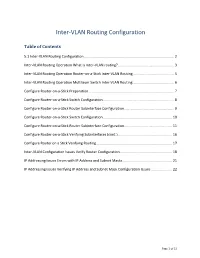
Inter-VLAN Routing Configuration
Inter-VLAN Routing Configuration Table of Contents 5.1 Inter-VLAN Routing Configuration ............................................................................................ 2 Inter-VLAN Routing Operation What is Inter-VLAN routing? ......................................................... 3 Inter-VLAN Routing Operation Router-on-a-Stick Inter-VLAN Routing .......................................... 5 Inter-VLAN Routing Operation Multilayer Switch Inter-VLAN Routing .......................................... 6 Configure Router-on-a-Stick Preparation ....................................................................................... 7 Configure Router-on-a-Stick Switch Configuration ........................................................................ 8 Configure Router-on-a-Stick Router Subinterface Configuration ................................................... 9 Configure Router-on-a-Stick Switch Configuration ...................................................................... 10 Configure Router-on-a-Stick Router Subinterface Configuration ................................................. 11 Configure Router-on-a-Stick Verifying Subinterfaces (cont.) ....................................................... 16 Configure Router on a Stick Verifying Routing ............................................................................. 17 Inter-VLAN Configuration Issues Verify Router Configuration ..................................................... 18 IP Addressing Issues Errors with IP Address and Subnet Masks .................................................. -

Grumpy Networkers Journal Documentation Release 0.0.7
Grumpy Networkers Journal Documentation Release 0.0.7 Head In The Cloud Oct 21, 2019 Contents: 1 Networking 3 1.1 Virtual Private Networks.........................................3 1.2 Network Protocols............................................ 56 2 Security 59 2.1 Common Network Attacks........................................ 59 2.2 Securing the Switch Infrastructure.................................... 60 2.3 Segregating Networks using Firewalls.................................. 60 2.4 Cryptography Overview......................................... 65 2.5 Authentication Services......................................... 67 3 Cloud Services 69 3.1 Cloud Deployment Models........................................ 69 3.2 Cloud Service Models.......................................... 69 4 Documentation 71 4.1 Sphinx.................................................. 71 5 Study Notes 73 5.1 Cisco CCNP - Implementing Cisco Secure Mobility Solutions (300-209 SIMOS)........... 73 5.2 Cisco CCNP - Implementing Cisco Edge Network Security Solutions (300-206 SENSS)....... 74 5.3 Cisco CCNP - Implementing Cisco IP Switched Networks (300-115 SWITCH)............ 76 6 Vendor Implementations 163 6.1 Cisco Implementations.......................................... 163 7 To Do 209 8 Glossary of Terms 213 9 External References 215 9.1 PPTP................................................... 215 9.2 Sphinx.................................................. 215 10 Indices and tables 217 Bibliography 219 i Index 221 ii Grumpy Networkers Journal Documentation, Release -

Switching, Routing, and Wireless Essentials Companion Guide (Ccnav7)
Switching, Routing, and Wireless Essentials Companion Guide (CCNAv7) Cisco Press Hoboken, New Jersey ii Switching, Routing, and Wireless Essentials Companion Guide (CCNAv7) Editor-in-Chief Switching, Routing, and Mark Taub Wireless Essentials Alliances Manager, Companion Guide (CCNAv7) Cisco Press Arezou Gol Copyright © 2020 Cisco Systems, Inc. Director, ITP Product Published by: Management Cisco Press Brett Bartow Hoboken, New Jersey Senior Editor All rights reserved. No part of this book may be reproduced or transmitted in James Manly any form or by any means, electronic or mechanical, including photocopying, Managing Editor recording, or by any information storage and retrieval system, without written Sandra Schroeder permission from the publisher, except for the inclusion of brief quotations in a review. Development Editor Marianne Bartow ScoutAutomatedPrintCode Senior Project Editor Library of Congress Control Number: 2020936826 Tonya Simpson ISBN-13: 978-0-13-672935-8 Copy Editor ISBN-10: 0-13-672935-5 Barbara Hacha Technical Editor Warning and Disclaimer Rick Graziani Editorial Assistant This book is designed to provide information about the Cisco Networking Cindy Teeters Academy Switching, Routing, and Wireless Essentials course. Every effort has been made to make this book as complete and as accurate as possible, but no Cover Designer warranty or fitness is implied. Chuti Prasertsith The information is provided on an “as is” basis. The authors, Cisco Press, and Composition Cisco Systems, Inc. shall have neither liability nor responsibility to any person codeMantra or entity with respect to any loss or damages arising from the information Indexer contained in this book or from the use of the discs or programs that may Cheryl Ann Lenser accompany it. -
Switching in an Enterprise Network
04_1587132117_ch03.qxd 3/31/08 10:52 PM Page 65 CHAPTER 3 Switching in an Enterprise Network Objectives Upon completion of this chapter, you should be able to answer the following questions: ■ What types of switches are found in an enter- ■ What is inter-VLAN routing and how is it con- prise network? figured? ■ How does Spanning Tree Protocol prevent ■ What is VLAN Trunking Protocol and how does switching loops? it help maintain VLANs in an enterprise net- work? ■ What is a VLAN and what purpose does it serve? ■ How is a VLAN configured on a Cisco switch? Key Terms This chapter uses the following key terms. You can find the definitions in the Glossary. wire speed page 67 availability page 72 content addressable memory (CAM) page 67 load balancing page 72 aging time page 67 switching loops page 72 microsegmentation page 67 broadcast storm page 72 virtual circuit page 68 Spanning Tree Protocol (STP) page 75 symmetric switching page 68 bridge protocol data units (BPDU) page 76 asymmetric switching page 68 blocking state page 77 uplink ports page 68 listening state page 77 multilayer switching page 69 learning state page 77 application-specific integrated circuit (ASIC) forwarding state page 77 page 69 disabled page 77 store-and-forward switching page 70 Access ports page 77 cut-through switching page 70 Trunking ports page 77 fast-forward switching page 70 root bridge page 78 fragment-free switching page 70 bridge page 78 runts page 70 ID (BID) page 78 adaptive cut-through switching page 70 Root ports page 79 Redundancy page 72 least-cost -

How Can Configure Five Different Networks/Vlans with One Port of Router
European Journal of Engineering and Technology Vol. 7 No. 6, 2019 ISSN 2056-5860 HOW CAN CONFIGURE FIVE DIFFERENT NETWORKS/VLANS WITH ONE PORT OF ROUTER Edmira Xhaferra Luciana Toti Eriselda Malaj Amarildo Rista Department of Information Department of Information Department of Information Department of Information Technology, Faculty of Information Technology, Faculty of Technology, Faculty of Technology, Faculty of Information Technology, “Aleksander Moisiu” Information Technology, Information Technology, Technology, “Aleksander Moisiu” University “Aleksander Moisiu” University “Aleksander Moisiu” University University DURRES, ALBANIA DURRES, ALBANIA DURRES, ALBANIA DURRES, ALBANIA [email protected] [email protected] [email protected] [email protected] ABSTRACT In this paper, we will set up five different Networks/ VLANS, and each of them will be configured to the same router’s port. Usually when we have some networks or VLANS, they are configured each of them in different ports of router. The network will be designed and simulated by using the Cisco Packet Tracer 7.2 simulator. This is a technical knowledge that is harder to configure but is usable when we have fewer router’s port or fewer network cards in the router. One way is to connect several networks to a single port. This technique called Router on a Stick, and between router and the switch used one Ethernet link that is configured like as an 802.1q trunk link. It is clear that as many ports or network cards have a router, this means higher cost, so with a simple technique we can buy a router more chipper and make this configuration. -

A Simulation Based Study on Network Architecture Using Inter-VLAN Routing and Secure Campus Area Network (CAN)
International Journal of Computer Sciences and Engineering Open Access Research Paper Volume-6, Issue-3 E-ISSN: 2347-2693 A Simulation based study on Network Architecture Using Inter-VLAN Routing and Secure Campus Area Network (CAN) S.Somasundaram1*, M.Chandran2 1* Department of Computer Applications, SRMV College of Arts & Science, Coimbatore, Tamilnadu ,India 2 Department of Computer Applications, SRMV College of Arts & Science, Coimbatore, Tamilnadu ,India *Corresponding Author: [email protected] Available online at: www.ijcseonline.org Received: 20/Feb//2018, Revised: 26/Feb2018, Accepted: 19/Mar/2018, Published: 30/Mar/2018 Abstract—Today development of computer and information technology, computer and network have been very popular. At the same time, security is important to secure the data, especially in campus environment. A campus network faces, many challenges such as IP address allocation, network failure, detecting rogue system user and determining slowing network etc., This research is mainly targeted towards campus networks which deliver the required security and best performance. To reduce the maximum wastage of IP address space using VLSM technique. A network is divided into different subnets. This technique will improve the security and traffic isolation. To improve the network speed on campus area network using etherchannel technique. This technique increases the network speed and redundant path between two devices. To multiple smaller broadcast domain using VLAN. To Communicate different VLAN using Inter-VLAN technique. This technique is implemented using multilayer switch. To secure and control a network traffic using VLAN Access Control List (VACL). Secured network protects an institution from security attacks associated with network. A campus network has a number of uses, such as education, research, learning, supervision, e-library, result publishing and association with the external users. -

19(A). Router on a Stick Ccnacookbook .C Om
Rev. 20181113.124935 19(A). Router On A Stick ccnacookbook .c om ROAS (Router On A Stick)—a conceptually simple approach to routing between L !"# $e !" are %eli&ere% to the router &ia an Ethernet trunk( separate% by )*+#,-# On arrival( Gi 0/0.10 they are shunte% to subinterfaces base% on their )*+#,- ! 10.10.0.1 /24 tags an% the router routes between those subinterfaces base% Gi 0/0.20 on %estination /0 a%%ress( 1ust like normal# 10.20.0.1 /24 )*+#,- tags stretch the hea%er by inserting a 32-bit (4-byte) tag into a normal Ethernet hea%er# )*+#,--compliant recipients know to e5pect that an )*+#,- .rame may occasionally be o&ersize% by up to those 4 bytes# 7ative VLA7—one of the !" on the trunk can be %esignate% as "native#9 Its .rames will receive no tag an% will be 1ust a normal Ethernet .rame# $is copes with %e&ices that %on't Fa 0/24 un%erstan% !"( yet are on the trunk's network segment (perhaps a hub between the router an% switch has a printer on VLAN 10 H1 one of its ports)# <onus In.ormation—De&ices can tell the %ifference between an Address: 10.10.0.2 /24 Gateway: 10.10.0.1 )*+#,- .rame an% a normal Ethernet .rame because the 43 byte hea%er happens to be inserte% right be.ore the Ether?ype VLAN 20 H2 hea%er @el%( pushing it to the right. $e @rst part of the )*+#,- tag is 1ust a Aag( sitting where the Ether?ype @el% Address: 10.20.0.2 /24 woul% ha&e been( screaming "I'm an )*+#,- .rame#9 Gateway: 10.20.0.1 EXAMPLE One possible con@guration to support the %iagram at the top-right of this page follows# VLA7 10 is %esignate% as -

Intervlan Routing and Various Configurations on Vlan in a Network Using Cisco Packet Tracer
IJIRST –International Journal for Innovative Research in Science & Technology| Volume 2 | Issue 11 | April 2016 ISSN (online): 2349-6010 Intervlan Routing and Various Configurations on Vlan in a Network using Cisco Packet Tracer 6.2 N.Hari Prasad B. Karunakar Reddy UG Students UG Students Department of Electronics & Communication Engineering Department of Electronics & Communication Engineering Saveetha School of Engineering, Saveetha University Saveetha School of Engineering, Saveetha University Thandalam, Chennai- 602105, India Thandalam, Chennai- 602105, India B. Amarnath M. Puthanial UG Students Associate Professor Department of Electronics & Communication Engineering Department of Electronics & Communication Engineering Saveetha School of Engineering, Saveetha University Saveetha School of Engineering, Saveetha University Thandalam, Chennai- 602105, India Thandalam, Chennai- 602105, India Abstract The purpose of this paper is to communicate between different Virtual-LANS and to learn more about VLAN Trunking and its operations. VLAN (virtual local area network) is used for configuring Layer-2 network. In this paper we have done an INTER- VLAN routing configured to connect different VLANs in a network whereas connecting in the same VLAN is also possible. INTER-VLAN ROUTING is also known as ROUTER-ON-A-STICK. Generally to communicate between two departments we need a Layer-3 device in place. Layer-3 switch is used on the network to configure INTER-VLAN routing without the need of a router. It is also configured to connect the different VLANS using some of the routing protocol, such as RIP and OSPF. We can also include a DHCP server in topology; the DHCP (dynamic host configuration protocol) is also invoked in this paper, to automatically configure an IP address for the each host. -

Appendix a Solutions to Selected Exercises
Appendix A Solutions to Selected Exercises Overview There are a few things you should keep in mind: 1. Networking problems sometimes have multiple correct solutions. Given is one solution and there may be others that are equally correct. 2. If there is a mistake in the solution, please check the website for errata, double– check your work and discuss it with a local expert. 3. If you have need of an additional solution and the steps above have not helped (or you can’t find a solution anywhere) you may contact me for a solution as long as you keep in mind I may not respond quickly or at all. Do not take this as a rejection, but rather as a sign I am having a delay getting to your request. I will eventually respond, I hope. This appendix will give the solutions to some exercises in this book. At some point there may be additional solutions on line at https://www.springer.com/us/book/ 9783030344955 and www.gerryhowser.com/book/9783030344955/solutions, both of which are under construction at the time of this writing. © Springer Nature Switzerland AG 2020 425 G. Howser, Computer Networks and the Internet, https://doi.org/10.1007/978-3-030-34496-2 Appendix B Request For Comments The RFCs below are relevant to this book. This is not an exhaustive list and most RFCs are typically dense and hard to read. Normally RFCs are most useful when writing a process to implement a specific protocol. AppleTalk AppleTalk Title RFC 1378 The PPP AppleTalk Control Protocol (ATCP) RFC 1504 Appletalk Update-Based Routing Protocol: Enhanced Appletalk Routing RFC 6281 -

Communication Cisco Ccxx.Docx Last Update: 01.10.2020 Author: Albert Balogh
Cisco CCENT, CCNA, CCNP (CCIE) © Copyright 2020 Document name : Communication Cisco CCxx.docx Last update: 01.10.2020 Author: Albert Balogh Table of Content Introduction ...................................................................................................................................................... 13 Certification ...................................................................................................................................................... 13 Cisco Certified Entry Network Technician (CCENT®) .................................................................................. 15 Cisco Certified Network Associate Routing and Switching (CCNA®) .......................................................... 16 Cisco Certified Network Professional (CCNP®) ........................................................................................... 16 Cisco Certified Internetwork Expert (CCIE®) ................................................................................................ 17 Cisco Certified Systems Instructor (CCSI®) ................................................................................................. 17 Authorities ........................................................................................................................................................ 17 Network Design Steps ..................................................................................................................................... 18 Cable Questions .......................................................................................................................................... -

The Proposed Roles of VLAN and Inter-VLAN Routing in Effective Distribution of Network Services in Ebonyi State University
International Journal of Science and Research (IJSR) ISSN (Online): 2319-7064 Index Copernicus Value (2013): 6.14 | Impact Factor (2013): 4.438 The Proposed Roles of VLAN and Inter-VLAN Routing in Effective Distribution of Network Services in Ebonyi State University Agwu Chukwuemeka Odi1, Nweso Emmanuel Nwogbaga2, Ojiugwo Chukwuka N. 3 1Lecturer 1, Department of Computer Science, Ebonyi State University – Abakaliki, Nigeria 2Lecturer 11, Department of Computer Science, Ebonyi State University – Abakaliki, Nigeria 3Undergraduate Student, Department of Computer Science, Ebonyi State University – Abakaliki, Nigeria Abstract: In traditional Local Area Network (LAN), all devices connected on switches belong to one broadcast domain. Virtual Private Local Area Network (VLAN) technology segments a physical LAN into different groups called VALNs and allows only devices on the same VLAN to communicate with one another while restricting devices on other VLANs from sending network traffic. This technology adds security in the LAN and controls network broadcast domain. Virtual LANs (VLANs) offer a method of dividing one physical LAN into multiple broadcast domains. However, VLAN-enabled switches cannot, by themselves, forward traffic across VLAN boundaries. For inter-VLAN communication, a Layer 3 router is required. This research paper discusses the VLAN protocol and different ways and possible protocols involved in creating and implementing Inter-VLAN routing for effective distribution of network services in Ebonyi State University. Keywords: Virtual LAN (VLAN), Inter-VLAN, Local Area Network (LAN), Routing, Inter-Routing, Network Services. 1. Introduction from any other network groups within the University. By default, hosts in a specific VLAN can’t communicate with Local Area Network (LAN) is built with the help of network hosts that are members of another VLAN.