Alarm Monitoring User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Computer Essentials – Session 1 – Step-By-Step Guide
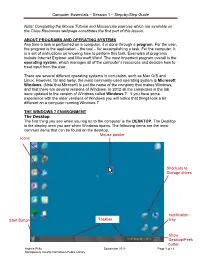
Computer Essentials – Session 1 – Step-by-Step Guide Note: Completing the Mouse Tutorial and Mousercise exercise which are available on the Class Resources webpage constitutes the first part of this lesson. ABOUT PROGRAMS AND OPERATING SYSTEMS Any time a task is performed on a computer, it is done through a program. For the user, the program is the application – the tool – for accomplishing a task. For the computer, it is a set of instructions on knowing how to perform this task. Examples of programs include Internet Explorer and Microsoft Word. The most important program overall is the operating system, which manages all of the computer’s resources and decides how to treat input from the user. There are several different operating systems in circulation, such as Mac O/S and Linux. However, far and away, the most commonly-used operating system is Microsoft Windows. (Note that Microsoft is just the name of the company that makes Windows, and that there are several versions of Windows. In 2012 all the computers in the lab were updated to the version of Windows called Windows 7. If you have some experience with the older versions of Windows you will notice that things look a bit different on a computer running Windows 7. THE WINDOWS 7 ENVIRONMENT The Desktop The first thing you see when you log on to the computer is the DESKTOP. The Desktop is the display area you see when Windows opens. The following items are the most common items that can be found on the desktop: Mouse pointer Icons Shortcuts to Storage drives Notification Start Button Taskbar tray Show Desktop/Peek button Andrea Philo September 2012 Page 1 of 13 Montgomery County-Norristown Public Library Computer Essentials – Session 1 – Step-by-Step Guide Parts of the Windows 7 Desktop Icon: A picture representing a program or file or places to store files. -

Crossmedia Adaptation and the Development of Continuity in the Dc Animated Universe
“INFINITE EARTHS”: CROSSMEDIA ADAPTATION AND THE DEVELOPMENT OF CONTINUITY IN THE DC ANIMATED UNIVERSE Alex Nader A Thesis Submitted to the Graduate College of Bowling Green State University in partial fulfillment of the requirements for the degree of MASTER OF ARTS May 2015 Committee: Jeff Brown, Advisor Becca Cragin © 2015 Alexander Nader All Rights Reserved iii ABSTRACT Jeff Brown, Advisor This thesis examines the process of adapting comic book properties into other visual media. I focus on the DC Animated Universe, the popular adaptation of DC Comics characters and concepts into all-ages programming. This adapted universe started with Batman: The Animated Series and comprised several shows on multiple networks, all of which fit into a shared universe based on their comic book counterparts. The adaptation of these properties is heavily reliant to intertextuality across DC Comics media. The shared universe developed within the television medium acted as an early example of comic book media adapting the idea of shared universes, a process that has been replicated with extreme financial success by DC and Marvel (in various stages of fruition). I address the process of adapting DC Comics properties in television, dividing it into “strict” or “loose” adaptations, as well as derivative adaptations that add new material to the comic book canon. This process was initially slow, exploding after the first series (Batman: The Animated Series) changed networks and Saturday morning cartoons flourished, allowing for more opportunities for producers to create content. References, crossover episodes, and the later series Justice League Unlimited allowed producers to utilize this shared universe to develop otherwise impossible adaptations that often became lasting additions to DC Comics publishing. -

Icons of Survival: Metahumanism As Planetary Defense." Nerd Ecology: Defending the Earth with Unpopular Culture
Lioi, Anthony. "Icons of Survival: Metahumanism as Planetary Defense." Nerd Ecology: Defending the Earth with Unpopular Culture. London: Bloomsbury Academic, 2016. 169–196. Environmental Cultures. Bloomsbury Collections. Web. 25 Sep. 2021. <http:// dx.doi.org/10.5040/9781474219730.ch-007>. Downloaded from Bloomsbury Collections, www.bloomsburycollections.com, 25 September 2021, 20:32 UTC. Copyright © Anthony Lioi 2016. You may share this work for non-commercial purposes only, provided you give attribution to the copyright holder and the publisher, and provide a link to the Creative Commons licence. 6 Icons of Survival: Metahumanism as Planetary Defense In which I argue that superhero comics, the most maligned of nerd genres, theorize the transformation of ethics and politics necessary to the project of planetary defense. The figure of the “metahuman,” the human with superpowers and purpose, embodies the transfigured nerd whose defects—intellect, swarm-behavior, abnormality, flux, and love of machines—become virtues of survival in the twenty-first century. The conflict among capitalism, fascism, and communism, which drove the Cold War and its immediate aftermath, also drove the Golden and Silver Ages of Comics. In the era of planetary emergency, these forces reconfigure themselves as different versions of world-destruction. The metahuman also signifies going “beyond” these economic and political systems into orders that preserve democracy without destroying the biosphere. Therefore, the styles of metahuman figuration represent an appeal to tradition and a technique of transformation. I call these strategies the iconic style and metamorphic style. The iconic style, more typical of DC Comics, makes the hero an icon of virtue, and metahuman powers manifest as visible signs: the “S” of Superman, the tiara and golden lasso of Wonder Woman. -
Thomson Reuters Spreadsheet Link User Guide
THOMSON REUTERS SPREADSHEET LINK USER GUIDE MN-212 Date of issue: 13 July 2011 Legal Information © Thomson Reuters 2011. All Rights Reserved. Thomson Reuters disclaims any and all liability arising from the use of this document and does not guarantee that any information contained herein is accurate or complete. This document contains information proprietary to Thomson Reuters and may not be reproduced, transmitted, or distributed in whole or part without the express written permission of Thomson Reuters. Contents Contents About this Document ...................................................................................................................................... 1 Intended Readership ................................................................................................................................. 1 In this Document........................................................................................................................................ 1 Feedback ................................................................................................................................................... 1 Chapter 1 Thomson Reuters Spreadsheet Link .......................................................................................... 2 Chapter 2 Template Library ........................................................................................................................ 3 View Templates (Template Library) .............................................................................................................................................. -

Superman: What Makes Him So Iconic?
SUPERMAN: WHAT MAKES HIM SO ICONIC? Superman: What makes him so Iconic? Myriam Demers-Olivier George Brown College © 2009, Myriam Demers-Olivier SUPERMAN: WHAT MAKES HIM SO ICONIC? Introduction “Faster than a speeding bullet, more powerful than a locomotive, able to leap tall buildings in a single bound. Look! Up in the sky! It’s a bird, it’s a plane, it’s Superman! “ (Daniels, 1998, p. 1-7). Some people might not recognize the reference to early radio shows and cartoons, but most people will recognize the name Superman. Superman has become such an amazing cultural icon, that almost everyone knows his name, and often his weakness, his powers, the colors of his suit and the name of his arch nemesis. It’s part of common knowledge and everyone has been exposed to him at some time or another. Since the creation of Superman in 1938, comic book research and literary studies have come along way. These allows us to more deeply analyze and understand, as well as unravel the deeper signified meanings associated with the iconic Superman (Wandtke, 2007, p. 25). He is seen as a superhero, but also upholds “truth, justice and the American way” (Watt-Evans, 2006, p. 1). Some see him as Christ-like or Jewish, and even as a fascist. He fulfills some of our needs from the Maslow’s hierarchy of needs, and also expresses different messages depending on the medium in which he is portrayed. There is no end to the Superman merchandise, but Superman as an icon, can change a person. -
ALGE Displaystudio Manual
ALGE DisplayStudio Manual DisplayStudio Table of Content 1 General .............................................................................................................................3 2 Getting started...................................................................................................................3 2.1 Main Window ............................................................................................................3 2.2 Tree view for project navigation................................................................................4 3 Lists...................................................................................................................................5 3.1 List Builder................................................................................................................5 3.1.1 Text panel.............................................................................................................6 3.1.2 Animation..............................................................................................................6 3.1.3 List compiling........................................................................................................7 4 Animations and wipes .......................................................................................................7 4.1 Adding animation/wipe to the project........................................................................8 4.2 Animation/wipe editing..............................................................................................8 -

Xcelsius 2008 FP3.1 Fixed Issues
SAP BusinessObjects Xcelsius 2008 FP3.1 What's Fixed ■ Xcelsius 2008 FP3.1 2010-03-09 Copyright © 2010 SAP AG. All rights reserved.SAP, R/3, SAP NetWeaver, Duet, PartnerEdge, ByDesign, SAP Business ByDesign, and other SAP products and services mentioned herein as well as their respective logos are trademarks or registered trademarks of SAP AG in Germany and other countries. Business Objects and the Business Objects logo, BusinessObjects, Crystal Reports, Crystal Decisions, Web Intelligence, Xcelsius, and other Business Objects products and services mentioned herein as well as their respective logos are trademarks or registered trademarks of Business Objects S.A. in the United States and in other countries. Business Objects is an SAP company.All other product and service names mentioned are the trademarks of their respective companies. Data contained in this document serves informational purposes only. National product specifications may vary.These materials are subject to change without notice. These materials are provided by SAP AG and its affiliated companies ("SAP Group") for informational purposes only, without representation or warranty of any kind, and SAP Group shall not be liable for errors or omissions with respect to the materials. The only warranties for SAP Group products and services are those that are set forth in the express warranty statements accompanying such products and services, if any. Nothing herein should be construed as constituting an additional warranty. 2010-03-09 Contents Chapter 1 Welcome to Xcelsius 2008 -

Comparing Autocad and Autocad LT Autocad LT’S Advantages Are Its Lower Cost and Its Compatibility with Autocad
07_260173 ch01.qxp 5/21/08 9:08 AM Page 13 Starting to Draw n this chapter, I explain the essentials that you need to start drawings. After a little background, I discuss the basics of the screen that you see when you IN THIS CHAPTER open AutoCAD or AutoCAD LT, and how to use it. If you’ve never used I Getting acquainted with AutoCAD before, do the “Quick Start: Drawing a Window” chapter first. AutoCAD and AutoCAD LT AutoCAD and its younger brother, AutoCAD LT, are both created by Autodesk. Together they are the most widely used technical drawing programs anywhere. Starting AutoCAD and AutoCAD alone has more than 6,000,000 registered users. According to Autodesk, AutoCAD LT CAD stands for computer-aided design, but it can also stand for computer-aided drafting or drawing. Creating a new drawing The first version of AutoCAD, running under DOS, came out in 1982. AutoCAD Using the AutoCAD and was the first significant CAD program to run on a desktop computer. At the time, AutoCAD LT interface most other technical drawing programs ran on high-end workstations or even mainframes. AutoCAD LT was introduced in 1993, as a less expensive alternative Saving your drawing to AutoCAD, for people who don’t need all of AutoCAD’s advanced features. Closing a drawing and exiting AutoCAD and AutoCAD LT AutoCAD’s Advantages AutoCAD’s success has been attributed to its famous open architecture — the flexi- bility that the end user has to customize the program using source code files in plain text (ASCII) format — andCOPYRIGHTED programming languages (such as AutoLISP MATERIAL and Visual Basic for Applications). -

Visual Validation of SSL Certificates in the Mozilla Browser Using Hash Images
CS Senior Honors Thesis: Visual Validation of SSL Certificates in the Mozilla Browser using Hash Images Hongxian Evelyn Tay [email protected] School of Computer Science Carnegie Mellon University Advisor: Professor Adrian Perrig Electrical & Computer Engineering Engineering & Public Policy School of Computer Science Carnegie Mellon University Monday, May 03, 2004 Abstract Many internet transactions nowadays require some form of authentication from the server for security purposes. Most browsers are presented with a certificate coming from the other end of the connection, which is then validated against root certificates installed in the browser, thus establishing the server identity in a secure connection. However, an adversary can install his own root certificate in the browser and fool the client into thinking that he is connected to the correct server. Unless the client checks the certificate public key or fingerprint, he would never know if he is connected to a malicious server. These alphanumeric strings are hard to read and verify against, so most people do not take extra precautions to check. My thesis is to implement an additional process in server authentication on a browser, using human recognizable images. The process, Hash Visualization, produces unique images that are easily distinguishable and validated. Using a hash algorithm, a unique image is generated using the fingerprint of the certificate. Images are easily recognizable and the user can identify the unique image normally seen during a secure AND accurate connection. By making a visual comparison, the origin of the root certificate is known. 1. Introduction: The Problem 1.1 SSL Security The SSL (Secure Sockets Layer) Protocol has improved the state of web security in many Internet transactions, but its complexity and neglect of human factors has exposed several loopholes in security systems that use it. -

The Evolution of Batman and His Audiences
Georgia State University ScholarWorks @ Georgia State University English Theses Department of English 12-2009 Static, Yet Fluctuating: The Evolution of Batman and His Audiences Perry Dupre Dantzler Georgia State University Follow this and additional works at: https://scholarworks.gsu.edu/english_theses Part of the English Language and Literature Commons Recommended Citation Dantzler, Perry Dupre, "Static, Yet Fluctuating: The Evolution of Batman and His Audiences." Thesis, Georgia State University, 2009. https://scholarworks.gsu.edu/english_theses/73 This Thesis is brought to you for free and open access by the Department of English at ScholarWorks @ Georgia State University. It has been accepted for inclusion in English Theses by an authorized administrator of ScholarWorks @ Georgia State University. For more information, please contact [email protected]. STATIC, YET FLUCTUATING: THE EVOLUTION OF BATMAN AND HIS AUDIENCES by PERRY DUPRE DANTZLER Under the Direction of H. Calvin Thomas ABSTRACT The Batman media franchise (comics, movies, novels, television, and cartoons) is unique because no other form of written or visual texts has as many artists, audiences, and forms of expression. Understanding the various artists and audiences and what Batman means to them is to understand changing trends and thinking in American culture. The character of Batman has developed into a symbol with relevant characteristics that develop and evolve with each new story and new author. The Batman canon has become so large and contains so many different audiences that it has become a franchise that can morph to fit any group of viewers/readers. Our understanding of Batman and the many readings of him gives us insight into ourselves as a culture in our particular place in history. -

Microsoft Excel 2013: Headers and Footers
Microsoft Excel 2013: Headers and Footers You can add headers or footers at the top or bottom of a printed worksheet. For example, you might create a footer that has page numbers, along with the date and time. You also might want a Header that has a title of your file. These are both done using Headers and Footer. Using the Headers and Footers in Excel will keep you sheet with data only which will help when you use the data for formulas and merges. Headers and footers are not displayed on the worksheet in Normal view — they are only displayed in Page Layout view and on the printed pages. You can insert headers or footers in Page Layout view where you can see them, or you can use the Page Setup dialog box if you want to insert headers or footers for more than one worksheet at the same time. For other sheet types, such as chart sheets, you can only insert headers and footers by using the Page Setup dialog box. Add Or Change The Header Or Footer Text In the Page Layout View Add Or Change The Header Or Footer Text In The Page Setup Dialog Box Add A Predefined Header Or Footer Insert Specific Elements In A Header Or Footer Specify Header And Footer Options Close Headers And Footers Remove The Header Or Footer Text From A Worksheet Add or Change the Header or Footer Text in the Page Layout View 1. Click the worksheet to which you want to add headers or footers, or that contains headers or footers that you want to change. -
Basic Computer Lesson
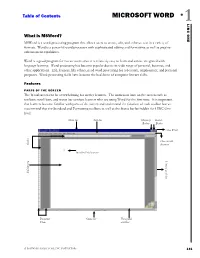
Table of Contents MICROSOFT WORD 1 ONE LINC What is MSWord? MSWord is a word-processing program that allows users to create, edit, and enhance text in a variety of formats. Word is a powerful word processor with sophisticated editing and formatting as well as graphic- enhancement capabilities. Word is a good program for novice users since it is relatively easy to learn and can be integrated with language learning. Word processing has become popular due to its wide range of personal, business, and other applications. ESL learners, like others, need word processing for job search, employment, and personal purposes. Word-processing skills have become the backbone of computer literacy skills. Features PARTS OF THE SCREEN The Word screen can be overwhelming for novice learners. The numerous bars on the screen such as toolbars, scroll bars, and status bar confuse learners who are using Word for the first time. It is important that learners become familiar with parts of the screen and understand the function of each toolbar but we recommend that the Standard and Formatting toolbars as well as the Status bar be hidden for LINC One level. Menu bar Title bar Minimize Restore Button Button Close Word Close current Rulers document Insertion Point (cursor) Vertical scroll bar Editing area Document Status bar Horizontal Views scroll bar A SOFTWARE GUIDE FOR LINC INSTRUCTORS 131 1 MICROSOFT WORD Hiding Standard toolbar, Formatting toolbar, and Status bar: • To hide the Standard toolbar, click View | Toolbars on the Menu bar. Check off Standard. LINC ONE LINC • To hide the Formatting toolbar, click View | Toolbars on the Menu bar.