An Interview With
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Oral History of Fernando Corbató
Oral History of Fernando Corbató Interviewed by: Steven Webber Recorded: February 1, 2006 West Newton, Massachusetts CHM Reference number: X3438.2006 © 2006 Computer History Museum Oral History of Fernando Corbató Steven Webber: Today the Computer History Museum Oral History Project is going to interview Fernando J. Corbató, known as Corby. Today is February 1 in 2006. We like to start at the very beginning on these interviews. Can you tell us something about your birth, your early days, where you were born, your parents, your family? Fernando Corbató: Okay. That’s going back a long ways of course. I was born in Oakland. My parents were graduate students at Berkeley and then about age 5 we moved down to West Los Angeles, Westwood, where I grew up [and spent] most of my early years. My father was a professor of Spanish literature at UCLA. I went to public schools there in West Los Angeles, [namely,] grammar school, junior high and [the high school called] University High. So I had a straightforward public school education. I guess the most significant thing to get to is that World War II began when I was in high school and that caused several things to happen. I’m meandering here. There’s a little bit of a long story. Because of the wartime pressures on manpower, the high school went into early and late classes and I cleverly saw that I could get a chance to accelerate my progress. I ended up taking both early and late classes and graduating in two years instead of three and [thereby] got a chance to go to UCLA in 1943. -
Topic a Dataflow Model of Computation
Department of Electrical and Computer Engineering Computer Architecture and Parallel Systems Laboratory - CAPSL Topic A Dataflow Model of Computation CPEG 852 - Spring 2014 Advanced Topics in Computing Systems Guang R. Gao ACM Fellow and IEEE Fellow Endowed Distinguished Professor Electrical & Computer Engineering University of Delaware CPEG852-Spring14: Topic A - Dataflow - 1 [email protected] Outline • Parallel Program Execution Models • Dataflow Models of Computation • Dataflow Graphs and Properties • Three Dataflow Models – Static – Recursive Program Graph – Dynamic • Dataflow Architectures CPEG852-Spring14: Topic A - Dataflow - 1 2 Terminology Clarification • Parallel Model of Computation – Parallel Models for Algorithm Designers – Parallel Models for System Designers • Parallel Programming Models • Parallel Execution Models • Parallel Architecture Models CPEG852-Spring14: Topic A - Dataflow - 1 3 What is a Program Execution Model? . Application Code . Software Packages User Code . Program Libraries . Compilers . Utility Applications PXM (API) . Hardware System . Runtime Code . Operating System CPEG852-Spring14: Topic A - Dataflow - 1 4 Features a User Program Depends On . Procedures; call/return Features expressed within .Access to parameters and a Programming language variables .Use of data structures (static and dynamic) But that’s not all !! . File creation, naming and access Features expressed Outside .Object directories a (typical) programming .Communication: networks language and peripherals .Concurrency: coordination; scheduling CPEG852-Spring14: Topic A - Dataflow - 1 5 Developments in the 1960s, 1970s Highlights 1960 Other Events . Burroughs B5000 Project . Project MAC Funded at MIT Started . Rice University Computer . IBM announces System 360 . Vienna Definition Method . Tasking introduced in Algol . Common Base Language, 1970 68 and PL/I Dennis . Burroughs builds Robert . Contour Model, Johnston Barton’s DDM1 . Book on the B6700, . -

SIGOPS Annual Report 2012
SIGOPS Annual Report 2012 Fiscal Year July 2012-June 2013 Submitted by Jeanna Matthews, SIGOPS Chair Overview SIGOPS is a vibrant community of people with interests in “operatinG systems” in the broadest sense, includinG topics such as distributed computing, storaGe systems, security, concurrency, middleware, mobility, virtualization, networkinG, cloud computinG, datacenter software, and Internet services. We sponsor a number of top conferences, provide travel Grants to students, present yearly awards, disseminate information to members electronically, and collaborate with other SIGs on important programs for computing professionals. Officers It was the second year for officers: Jeanna Matthews (Clarkson University) as Chair, GeorGe Candea (EPFL) as Vice Chair, Dilma da Silva (Qualcomm) as Treasurer and Muli Ben-Yehuda (Technion) as Information Director. As has been typical, elected officers agreed to continue for a second and final two- year term beginning July 2013. Shan Lu (University of Wisconsin) will replace Muli Ben-Yehuda as Information Director as of AuGust 2013. Awards We have an excitinG new award to announce – the SIGOPS Dennis M. Ritchie Doctoral Dissertation Award. SIGOPS has lonG been lackinG a doctoral dissertation award, such as those offered by SIGCOMM, Eurosys, SIGPLAN, and SIGMOD. This new award fills this Gap and also honors the contributions to computer science that Dennis Ritchie made durinG his life. With this award, ACM SIGOPS will encouraGe the creativity that Ritchie embodied and provide a reminder of Ritchie's leGacy and what a difference a person can make in the field of software systems research. The award is funded by AT&T Research and Alcatel-Lucent Bell Labs, companies that both have a strong connection to AT&T Bell Laboratories where Dennis Ritchie did his seminal work. -
NASA Contrattbr 4Report 178229 S E M I a N N U a L R E P O
NASA Contrattbr 4Report 178229 ICASE SEMIANNUAL REPORT April 1, 1986 through September 30, 1986 Contract No. NAS1-18107 January 1987 INSTITUTE FOR COMPUTER APPLICATIONS IN SCIENCE AND ENGINEERING NASA Langley Research Center, Hampton, Virginia 23665 Operatsd by the Universities Space Research Association National Aeronautics and Space Ad minis t rat ion bnglay Research Center HamDton,Virginia23665 CONTENTS Page Introduction .............................................................. iii Research in erogress ...................................................... 1 Reports and Abstracts ..................................................... 32 ICASE Colloquia........................................................... 49 ICASE Summer Activities ................................................... 52 Other Activities .......................................................... 58 ICASE Staff ............................................................... 60 i INTRODUCTION The Institute for Computer Applications in Science and Engineering (ICASE) is operated at the Langley Research Center (LaRC) of NASA by the Universities Space Research Associat€on (USRA) under a contract with the Center. USRA is a nonpro€it consortium of major U. S. colleges and universities. The Institute conducts unclassified basic research in applied mathematics, numerical analysis, and computer science in order to extend and improve problem-solving capabilities in science and engineering, particularly in aeronautics and space. ICASE has a small permanent staff. Research -

July 1St Century and a Half Later by 1960S
The underlying technology, the After CTSS, he moved onto Leibniz wheel, was reused a Multics [Nov 30] during the mid- July 1st century and a half later by 1960s. That OS is often deemed Thomas de Colmar [May 5] in his a commercial failure, but arithmometer, the first mass- nevertheless had an enormous Gottfried Wilhelm produced mechanical calculator. influence on the design of later systems. For example, UNIX was In 1961, Norbert Wiener [Nov written by two ex-Multics (von) Leibni[t]z 26] suggested that Leibniz programmers, Ken Thompson should be considered the patron Born: July 1, 1646; [Feb 4] and Dennis Ritchie [Sept saint of cybernetics. Leipzig, Saxony 9]. Died: Nov. 14, 1716 Corbató is credited with the first During the 1670s, Leibniz use of passwords (to secure independently developed a very Hans Peter Luhn access to CTSS), although he similar theory of calculus to that Born: July 1, 1896; himself suggested that they first of Issac Newton. More appeared in IBM’s SABRE Barmen, Germany importantly for us, at around the ticketing system [Nov 5]. same time, in 1672, Leibniz cam Died: August 19, 1964 Corbató’s Law: The number of up with the first practical Luhn is sometimes called “the lines of code a programmer can calculating machine, which he father of information retrieval”, write in a fixed period of time is called the “Step Reckoner”. He due to his invention of the Luhn the same independent of the had the initial idea from algorithm, KWIC (Key Words In language used. examining a pedometer. Context) indexing, and Selective It was the first calculator that Dissemination of Information could perform all four arithmetic (“SDI”) operations, although the carry The Luhn algorithm is a Project MAC operation wasn't fully checksum formula used to July 1, 1963 mechanized. -
Introduction
Introduction J. M. P. Alves Laboratory of Genomics & Bioinformatics in Parasitology Department of Parasitology, ICB, USP BMP0260 / ICB5765 / IBI5765 ● Introduction to computers and computing (UNIX) ● Linux basics ● Introduction to the Bash shell ● Connecting to this course’s virtual machine J.M.P. Alves 2 / 82 BMP0260 / ICB5765 / IBI5765 TuxThe Linux mascot “TUXedo”... By Larry Ewing, 1996 ...or Torvalds UniX Tux's ancestor J.M.P. Alves 3 / 82 BMP0260 / ICB5765 / IBI5765 Linux (Unix) & science Why so popular together? ● Historical reasons (programs made for Unix/Linux) ● Available on any kind of computer, especially powerful servers ● Works efficiently with humongous text files (head, tail, sort, cut, paste, grep, etc.) ● Complicated tasks can be made easy by concatenating simpler commands (piping) ● Creating new programs is easy – tools just one or two commands (or clicks) away (gcc, g++, python, perl) ● Stable, efficient, open (free software), no cost (software for free) J.M.P. Alves 4 / 82 BMP0260 / ICB5765 / IBI5765 What IS this Linux, anyway? J.M.P. Alves 5 / 82 BMP0260 / ICB5765 / IBI5765 Operating system J.M.P. Alves 6 / 82 BMP0260 / ICB5765 / IBI5765 An operating system is a collection of programs that initialize the computer's hardware, providing basic instructions for the control of devices, managing and scheduling tasks, and regulating their interactions with each other. J.M.P. Alves 7 / 82 BMP0260 / ICB5765 / IBI5765 You WhatsApp Android Phone J.M.P. Alves 8 / 82 BMP0260 / ICB5765 / IBI5765 You MUSCLE Linux Computer J.M.P. Alves 9 / 82 BMP0260 / ICB5765 / IBI5765 formerly: J.M.P. Alves 10 / 82 BMP0260 / ICB5765 / IBI5765 History J.M.P. -

Mount Litera Zee School Grade-VIII G.K Computer and Technology Read and Write in Notebook: 1
Mount Litera Zee School Grade-VIII G.K Computer and Technology Read and write in notebook: 1. Who is called as ‘Father of Computer’? a. Charles Babbage b. Bill Gates c. Blaise Pascal d. Mark Zuckerberg 2. Full Form of virus is? a. Visual Information Resource Under Seize b. Virtual Information Resource Under Size c. Vital Information Resource Under Seize d. Virtue Information Resource Under Seize 3. How many MB (Mega Byte) makes one GB (Giga Byte)? a. 1025 MB b. 1030 MB c. 1020 MB d. 1024 MB 4. Internet was developed in _______. a. 1973 b. 1993 c. 1983 d. 1963 5. Which was the first virus detected on ARPANET, the forerunner of the internet in the early 1970s? a. Exe Flie b. Creeper Virus c. Peeper Virus d. Trozen horse 6. Who is known as the Human Computer of India? a. Shakunthala Devi b. Nandan Nilekani c. Ajith Balakrishnan d. Manish Agarwal 7. When was the first smart phone launched? a. 1992 b. 1990 c. 1998 d. 2000 8. Which one of the following was the first search engine used? a. Google b. Archie c. AltaVista d. WAIS 9. Who is known as father of Internet? a. Alan Perlis b. Jean E. Sammet c. Vint Cerf d. Steve Lawrence 10. What us full form of GOOGLE? a. Global Orient of Oriented Group Language of Earth b. Global Organization of Oriented Group Language of Earth c. Global Orient of Oriented Group Language of Earth d. Global Oriented of Organization Group Language of Earth 11. Who developed Java Programming Language? a. -

Operating Systems & Virtualisation Security Knowledge Area
Operating Systems & Virtualisation Security Knowledge Area Issue 1.0 Herbert Bos Vrije Universiteit Amsterdam EDITOR Andrew Martin Oxford University REVIEWERS Chris Dalton Hewlett Packard David Lie University of Toronto Gernot Heiser University of New South Wales Mathias Payer École Polytechnique Fédérale de Lausanne The Cyber Security Body Of Knowledge www.cybok.org COPYRIGHT © Crown Copyright, The National Cyber Security Centre 2019. This information is licensed under the Open Government Licence v3.0. To view this licence, visit: http://www.nationalarchives.gov.uk/doc/open-government-licence/ When you use this information under the Open Government Licence, you should include the following attribution: CyBOK © Crown Copyright, The National Cyber Security Centre 2018, li- censed under the Open Government Licence: http://www.nationalarchives.gov.uk/doc/open- government-licence/. The CyBOK project would like to understand how the CyBOK is being used and its uptake. The project would like organisations using, or intending to use, CyBOK for the purposes of education, training, course development, professional development etc. to contact it at con- [email protected] to let the project know how they are using CyBOK. Issue 1.0 is a stable public release of the Operating Systems & Virtualisation Security Knowl- edge Area. However, it should be noted that a fully-collated CyBOK document which includes all of the Knowledge Areas is anticipated to be released by the end of July 2019. This will likely include updated page layout and formatting of the individual Knowledge Areas KA Operating Systems & Virtualisation Security j October 2019 Page 1 The Cyber Security Body Of Knowledge www.cybok.org INTRODUCTION In this Knowledge Area, we introduce the principles, primitives and practices for ensuring se- curity at the operating system and hypervisor levels. -
UC Berkeley Previously Published Works
UC Berkeley UC Berkeley Previously Published Works Title Building the Second Mind, 1961-1980: From the Ascendancy of ARPA-IPTO to the Advent of Commercial Expert Systems Permalink https://escholarship.org/uc/item/7ck3q4f0 ISBN 978-0-989453-4-6 Author Skinner, Rebecca Elizabeth Publication Date 2013-12-31 eScholarship.org Powered by the California Digital Library University of California Building the Second Mind, 1961-1980: From the Ascendancy of ARPA to the Advent of Commercial Expert Systems copyright 2013 Rebecca E. Skinner ISBN 978 09894543-4-6 Forward Part I. Introduction Preface Chapter 1. Introduction: The Status Quo of AI in 1961 Part II. Twin Bolts of Lightning Chapter 2. The Integrated Circuit Chapter 3. The Advanced Research Projects Agency and the Foundation of the IPTO Chapter 4. Hardware, Systems and Applications in the 1960s Part II. The Belle Epoque of the 1960s Chapter 5. MIT: Work in AI in the Early and Mid-1960s Chapter 6. CMU: From the General Problem Solver to the Physical Symbol System and Production Systems Chapter 7. Stanford University and SRI Part III. The Challenges of 1970 Chapter 8. The Mansfield Amendment, “The Heilmeier Era”, and the Crisis in Research Funding Chapter 9. The AI Culture Wars: the War Inside AI and Academia Chapter 10. The AI Culture Wars: Popular Culture Part IV. Big Ideas and Hardware Improvements in the 1970s invert these and put the hardware chapter first Chapter 11. AI at MIT in the 1970s: The Semantic Fallout of NLR and Vision Chapter 12. Hardware, Software, and Applications in the 1970s Chapter 13. -
1. with Examples of Different Programming Languages Show How Programming Languages Are Organized Along the Given Rubrics: I
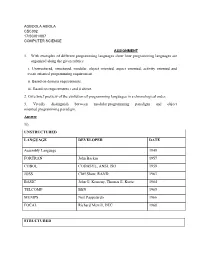
AGBOOLA ABIOLA CSC302 17/SCI01/007 COMPUTER SCIENCE ASSIGNMENT 1. With examples of different programming languages show how programming languages are organized along the given rubrics: i. Unstructured, structured, modular, object oriented, aspect oriented, activity oriented and event oriented programming requirement. ii. Based on domain requirements. iii. Based on requirements i and ii above. 2. Give brief preview of the evolution of programming languages in a chronological order. 3. Vividly distinguish between modular programming paradigm and object oriented programming paradigm. Answer 1i). UNSTRUCTURED LANGUAGE DEVELOPER DATE Assembly Language 1949 FORTRAN John Backus 1957 COBOL CODASYL, ANSI, ISO 1959 JOSS Cliff Shaw, RAND 1963 BASIC John G. Kemeny, Thomas E. Kurtz 1964 TELCOMP BBN 1965 MUMPS Neil Pappalardo 1966 FOCAL Richard Merrill, DEC 1968 STRUCTURED LANGUAGE DEVELOPER DATE ALGOL 58 Friedrich L. Bauer, and co. 1958 ALGOL 60 Backus, Bauer and co. 1960 ABC CWI 1980 Ada United States Department of Defence 1980 Accent R NIS 1980 Action! Optimized Systems Software 1983 Alef Phil Winterbottom 1992 DASL Sun Micro-systems Laboratories 1999-2003 MODULAR LANGUAGE DEVELOPER DATE ALGOL W Niklaus Wirth, Tony Hoare 1966 APL Larry Breed, Dick Lathwell and co. 1966 ALGOL 68 A. Van Wijngaarden and co. 1968 AMOS BASIC FranÇois Lionet anConstantin Stiropoulos 1990 Alice ML Saarland University 2000 Agda Ulf Norell;Catarina coquand(1.0) 2007 Arc Paul Graham, Robert Morris and co. 2008 Bosque Mark Marron 2019 OBJECT-ORIENTED LANGUAGE DEVELOPER DATE C* Thinking Machine 1987 Actor Charles Duff 1988 Aldor Thomas J. Watson Research Center 1990 Amiga E Wouter van Oortmerssen 1993 Action Script Macromedia 1998 BeanShell JCP 1999 AngelScript Andreas Jönsson 2003 Boo Rodrigo B. -

Oral History of Brian Kernighan
Oral History of Brian Kernighan Interviewed by: John R. Mashey Recorded April 24, 2017 Princeton, NJ CHM Reference number: X8185.2017 © 2017 Computer History Museum Oral History of Brian Kernighan Mashey: Well, hello, Brian. It’s great to see you again. Been a long time. So we’re here at Princeton, with Brian Kernighan, and we want to go do a whole oral history with him. So why don’t we start at the beginning. As I recall, you’re Canadian. Kernighan: That is right. I was born in Toronto long ago, and spent my early years in the city of Toronto. Moved west to a small town, what was then a small town, when I was in the middle of high school, and then went to the University of Toronto for my undergraduate degree, and then came here to Princeton for graduate school. Mashey: And what was your undergraduate work in? Kernighan: It was in one of these catch-all courses called Engineering Physics. It was for people who were kind of interested in engineering and math and science and didn’t have a clue what they wanted to actually do. Mashey: <laughs> So how did you come to be down here? Kernighan: I think it was kind of an accident. It was relatively unusual for people from Canada to wind up in the United States for graduate school at that point, but I thought I would try something different and so I applied to six or seven different schools in the United States, got accepted at some of them, and then it was a question of balancing things like, “Well, they promised that they would get you out in a certain number of years and they promised that they would give you money,” but the question is whether, either that was true or not and I don’t know. -

Turing Award • John Von Neumann Medal • NAE, NAS, AAAS Fellow
15-712: Advanced Operating Systems & Distributed Systems A Few Classics Prof. Phillip Gibbons Spring 2021, Lecture 2 Today’s Reminders / Announcements • Summaries are to be submitted via Canvas by class time • Announcements and Q&A are via Piazza (please enroll) • Office Hours: – Prof. Phil Gibbons: Fri 1-2 pm & by appointment – TA Jack Kosaian: Mon 1-2 pm – Zoom links: See canvas/Zoom 2 CS is a Fast Moving Field: Why Read/Discuss Old Papers? “Those who cannot remember the past are condemned to repeat it.” - George Santayana, The Life of Reason, Volume 1, 1905 See what breakthrough research ideas look like when first presented 3 The Rise of Worse is Better Richard Gabriel 1991 • MIT/Stanford style of design: “the right thing” – Simplicity in interface 1st, implementation 2nd – Correctness in all observable aspects required – Consistency – Completeness: cover as many important situations as is practical • Unix/C style: “worse is better” – Simplicity in implementation 1st, interface 2nd – Correctness, but simplicity trumps correctness – Consistency is nice to have – Completeness is lowest priority 4 Worse-is-better is Better for SW • Worse-is-better has better survival characteristics than the-right-thing • Unix and C are the ultimate computer viruses – Simple structures, easy to port, required few machine resources to run, provide 50-80% of what you want – Programmer conditioned to sacrifice some safety, convenience, and hassle to get good performance and modest resource use – First gain acceptance, condition users to expect less, later