Communication in Open Source Innovation
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Learning Apache Mahout Classification Table of Contents
Learning Apache Mahout Classification Table of Contents Learning Apache Mahout Classification Credits About the Author About the Reviewers www.PacktPub.com Support files, eBooks, discount offers, and more Why subscribe? Free access for Packt account holders Preface What this book covers What you need for this book Who this book is for Conventions Reader feedback Customer support Downloading the example code Downloading the color images of this book Errata Piracy Questions 1. Classification in Data Analysis Introducing the classification Application of the classification system Working of the classification system Classification algorithms Model evaluation techniques The confusion matrix The Receiver Operating Characteristics (ROC) graph Area under the ROC curve The entropy matrix Summary 2. Apache Mahout Introducing Apache Mahout Algorithms supported in Mahout Reasons for Mahout being a good choice for classification Installing Mahout Building Mahout from source using Maven Installing Maven Building Mahout code Setting up a development environment using Eclipse Setting up Mahout for a Windows user Summary 3. Learning Logistic Regression / SGD Using Mahout Introducing regression Understanding linear regression Cost function Gradient descent Logistic regression Stochastic Gradient Descent Using Mahout for logistic regression Summary 4. Learning the Naïve Bayes Classification Using Mahout Introducing conditional probability and the Bayes rule Understanding the Naïve Bayes algorithm Understanding the terms used in text classification Using the Naïve Bayes algorithm in Apache Mahout Summary 5. Learning the Hidden Markov Model Using Mahout Deterministic and nondeterministic patterns The Markov process Introducing the Hidden Markov Model Using Mahout for the Hidden Markov Model Summary 6. Learning Random Forest Using Mahout Decision tree Random forest Using Mahout for Random forest Steps to use the Random forest algorithm in Mahout Summary 7. -
Linux VDS Release Notes
Linux VDS Release Notes Linux VDS Release Notes Introduction Important: This document is based on the most recent available information regarding the release of Linux VDS. Future revisions of this document will include updates not only to the status of features, but also an overview of updates to customer documentation. The Linux VDS platform provides a set of features designed and implemented to suit the value-added reseller (VAR), small hosting service provider (HSP), application service provider (ASP), independent software vendor (ISV), and any small- and medium-sized business (SMB). This document provides administrators who possess minimal to moderate technical skills with a guide to the latest documentation and other sources of information available at the time of the release. This document also includes any cautions and warnings specific to this release. For more information, refer to the following documents: • Linux VDS User’s Guide • Linux VDS Getting Started Guide In addition, you can also refer to the following Web content: • Frequently-asked questions (FAQ) Status of Features Linux VDS introduces new features and enhancements. What’s New? The following table describes the status of features included with this release: Feature Status Accrisoft This release introduces support for Accrisoft e-commerce software (http://www.accrisoft.com/ ). You can use the software to build and manage profitable Web sites. Accrisoft is a fee-based, optional application. This release also provides an installation script to assure the software operates fully and correctly on your account. An uninstall script assures that you can remove the software completely and effectively if you need to do so. -
A Rule Based Approach for Spam Detection
A RULE BASED APPROACH FOR SPAM DETECTION Thesis submitted in partial fulfillment of the requirements for the award of degree of Master of Engineering In Computer Science & Engineering By: Ravinder Kamboj (Roll No. 800832030) Under the supervision of: Dr. V.P Singh Mrs. Sanmeet Bhatia Assistant Professor Assistant Professor Computer Science & Engineering Department of SMCA COMPUTER SCIENCE AND ENGINEERING DEPARTMENT THAPAR UNIVERSITY PATIALA – 147004 JULY- 2010 i ii Abstract Spam is defined as a junk Email or unsolicited Email. Spam has increased tremendously in the last few years. Today more than 85% of e-mails that are received by e-mail users are spam. The cost of spam can be measured in lost human time, lost server time and loss of valuable mail. Spammers use various techniques like spam via botnet, localization of spam and image spam. According to the mail delivery process anti-spam measures for Email Spam can be divided in to two parts, based on Emails envelop and Email data. Black listing, grey listing and white listing techniques can be applied on the Email envelop to detect spam. Techniques based on the data part of Email like heuristic techniques and Statistical techniques can be used to combat spam. Bayesian filters as part of statistical technique divides the income message in to words called tokens and checks their probability of occurrence in spam e-mails and ham e-mails. Two types of approaches can be followed for the detection of spam e-mails one is learning approach other is rule based approach. Learning approach required a large dataset of spam e-mails and ham e-mails is required for the training of spam filter; this approach has good time characteristics filter can be retrained quickly for new Spam. -
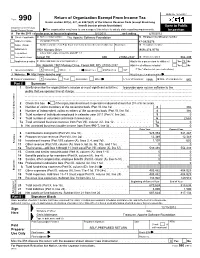
Return of Organization Exempt from Income
OMB No. 1545-0047 Return of Organization Exempt From Income Tax Form 990 Under section 501(c), 527, or 4947(a)(1) of the Internal Revenue Code (except black lung benefit trust or private foundation) Open to Public Department of the Treasury Internal Revenue Service The organization may have to use a copy of this return to satisfy state reporting requirements. Inspection A For the 2011 calendar year, or tax year beginning 5/1/2011 , and ending 4/30/2012 B Check if applicable: C Name of organization The Apache Software Foundation D Employer identification number Address change Doing Business As 47-0825376 Name change Number and street (or P.O. box if mail is not delivered to street address) Room/suite E Telephone number Initial return 1901 Munsey Drive (909) 374-9776 Terminated City or town, state or country, and ZIP + 4 Amended return Forest Hill MD 21050-2747 G Gross receipts $ 554,439 Application pending F Name and address of principal officer: H(a) Is this a group return for affiliates? Yes X No Jim Jagielski 1901 Munsey Drive, Forest Hill, MD 21050-2747 H(b) Are all affiliates included? Yes No I Tax-exempt status: X 501(c)(3) 501(c) ( ) (insert no.) 4947(a)(1) or 527 If "No," attach a list. (see instructions) J Website: http://www.apache.org/ H(c) Group exemption number K Form of organization: X Corporation Trust Association Other L Year of formation: 1999 M State of legal domicile: MD Part I Summary 1 Briefly describe the organization's mission or most significant activities: to provide open source software to the public that we sponsor free of charge 2 Check this box if the organization discontinued its operations or disposed of more than 25% of its net assets. -

Mastering Spam a Multifaceted Approach with the Spamato Spam Filter System
DISS. ETH NO. 16839 Mastering Spam A Multifaceted Approach with the Spamato Spam Filter System A dissertation submitted to the SWISS FEDERAL INSTITUTE OF TECHNOLOGY ZURICH for the degree of Doctor of Sciences presented by KENO ALBRECHT Dipl. Inf. born June 4, 1977 citizen of Germany accepted on the recommendation of Prof. Dr. Roger Wattenhofer, examiner Prof. Dr. Gordon V. Cormack, co-examiner Prof. Dr. Christof Fetzer, co-examiner 2006 Abstract Email is undoubtedly one of the most important applications used to com- municate over the Internet. Unfortunately, the email service lacks a crucial security mechanism: It is possible to send emails to arbitrary people with- out revealing one’s own identity. Additionally, sending millions of emails costs virtually nothing. Hence over the past years, these characteristics have facilitated and even boosted the formation of a new business branch that advertises products and services via unsolicited bulk emails, better known as spam. Nowadays, spam makes up more than 50% of all emails and thus has become a major vexation of the Internet experience. Although this problem has been dealt with for a long time, only little success (measured on a global scale) has been achieved so far. Fighting spam is a cat and mouse game where spammers and anti-spammers regularly beat each other with sophisticated techniques of increasing complexity. While spammers try to bypass existing spam filters, anti-spammers seek to detect and block new spamming tricks as soon as they emerge. In this dissertation, we describe the Spamato spam filter system as a mul- tifaceted approach to help regain a spam-free inbox. -

Suse Linux Enterprise Server 10 Mail Scanning Gateway Build Guide
SuSE Linux Enterprise Server 10 Mail Scanning Gateway Build Guide Written By: Stephen Carter [email protected] Last Modified 9. May. 2007 Page 1 of 96 Table of Contents Due credit.......................................................................................................................................................4 Overview........................................................................................................................................................5 System Requirements.....................................................................................................................................6 SLES10 DVD............................................................................................................................................6 An existing e-mail server..........................................................................................................................6 A Pentium class PC...................................................................................................................................6 Internet Access..........................................................................................................................................6 Internet Firewall Modifications.................................................................................................................7 Installation Summary.....................................................................................................................................8 How -
Curriculum Vitae Von Bastian Nolte (Kurzversion)
Curriculum Vitae von Bastian Nolte Expert IT Business Consultant & Coach Software-Architekt und Full Stack Developer Telefon (CH) +41 44 586 97 10 Mobil (DE) +49 173 20 989 60 E-Mail [email protected] Adresse Grosswilstrasse 2, 6048 Horw / Luzern, Schweiz Web: https://www.bastian-nolte.name Xing https://www.xing.com/profile/Bastian_Nolte Berufserfahrung 22 Jahre Erfahrung im IT-Bereich, davon etwa 9 Jahre als Business Consultant und 4 als Coach. Rollen in (technischer) Projektleitungsfunktion und als Architekt habe ich zirka 11 Jahre lang ausgeübt. Nationalität Deutsch Einsetzbar CH-LI-D-A (Schweiz, Liechtenstein, Deutschland, Österreich) Bevorzugte Schweiz Arbeitsregion (oder remote) Branchenerfahrung Versicherung, Informationstechnologie, Automotive, Dienstleister, IT Dienstleister, Öffentlicher Dienst, Bildungsträger, Telekommunikation, IT Sicherheit Fremdsprachen Englisch Auszeichnungen Innovationspreis Public Private Partnership 2009 (PPP) für den Fachübergreifen- den Einsatz Neuer Medien Freizeit Wandern, Tauchen, Mountain Biking, Kayaking Letzte 2021 Apache Kafka Kurs Confluent Fortbildungen 4929: Confluent Training «Apache Kafka Fundamentals» 2021 Microsoft Azure Zertifizierung Microsoft, AZ-900: Microsoft Certified Azure Fundamentals Pearson VUE. 2020 Kubernetes-Zertifizierung The Linux LFS158x: Introduction to Kubernetes Foundation, e. 2020 DevOps Kubernetes Camp Software & Viertägiges Intensivtraining über Kubernetes und Knative. Support Medi. 2019 Kommunikation & Moderationstechniken in der IT oose Innovative Informa. -

Openstackでnecが実現する 「OSSクラウド」の世界
OpenStackでNECが実現する 「OSSクラウド」の世界 2013年3月12日 日本電気株式会社 プラットフォームマーケティング戦略本部 OSS推進室 技術主幹 高橋 千恵子 目次 ▐ OSSの動向 ▐ NECのOSS/Linux事業 ▐ OSSプラットフォームへの取り組み 高可用Linuxプラットフォーム OSSミドルウェアの活用 ▐ OSSクラウド OpenStackへの取り組み OSSクラウドソリューション ~沖縄クラウドサービス基盤~ OpenFlow+OpenStack ▐ 最後に ●本資料に掲載された社名、商品名は各社の商標または登録商標です。 Page 1 © NEC Corporation 2013 OSSの動向 Page 2 © NEC Corporation 2013 OSSコミュニティによるプロジェクト ▐ 全般 ・・・・・SaaS型アプリケーションが増加/著名OSSのベンダー配布、有償サポートや買収が進む OSS定点観測は、freecode.com にて実施。 ▐ インフラ系・・・仮想化やクラウド基盤関係のOSSが注目される/システム、ネット管理OSSの伸びがある サイトでの人気度(300以上)で順位付け。 OSSプロジェクトは2012.4時点で32.4万件。 ▐ デプロイメント系・・PostgreSQL、mySQLが高人気 これらのDB管理、DBクラスタリングOSSも伸びている ビジネス用途を中心に表示。 ▐ アプリ系・・・・SaaS型グループウェアOSS、ソフトウェア分類を越えた統合的な著名OSSの伸びがある コンシューマ・プライベート系は除く。 コンテンツアプリケーション •PHProject [GW] エンジニ コラボレーティブ •EGroupware CRM ERM SCM • Dokuwiki [Wiki] • jGnash アリング • WebGUI [CMF] • phpBB [GW] •OBM [GW] • Enterprise CRM and ア • Tiki Tiki CMS Groupware • ProcessMaker • CorneliOS [CMS] • Ariadne Groupware System • Task Juggler [PM] • Blender オペレーション • TinyMCE [DCM] • XODA • Simple Groupware [GW] プ • OpenWebMail[webmail]• Teamwork [GW] • Dolibarr • Achievo [PM] • mxGraph 製造管理 • Drupal [CMS] • mnoGoSerch • LedgerSMB • white_dune • eZpublish [publish FW]• Managing • ZIm [blog] • Plans [GW] • The Apache Open リ • Tine2.0 [CRM&GW] • GnuCash • Jgraph • OTRS • XWiki [Wiki] • Midgard • Zimbra [GW] for Business • Elastix • GroupOffice [GW] • Twiki [KB] • TUTOS[ERP&PM] • graphviz • FUDForum • OpenSearch Project コンシューマ 系 • SquirrelMail [Webmail] • Time Trex • BRL-CAD • Asterisk • Plone CMS Server • Citadel [bbs] • -

Review and Analysis of Networking Challenges in Cloud Computing
Review and Analysis of Networking Challenges in Cloud Computing JOSE MOURA, Instituto Universitário de Lisboa (ISCTE-IUL), Instituto de Telecomunicações, Portugal DAVID HUTCHISON, Lancaster University, Infolab21, UK Cloud Computing offers virtualized computing, storage, and networking resources, over the Internet, to organizations and individual users in a completely dynamic way. These cloud resources are cheaper, easier to manage, and more elastic than sets of local, physical, ones. This encourages customers to outsource their applications and services to the cloud. The migration of both data and applications outside the administrative domain of customers into a shared environment imposes transversal, functional problems across distinct platforms and technologies. This article provides a contemporary discussion of the most relevant functional problems associated with the current evolution of Cloud Computing, mainly from the network perspective. The paper also gives a concise description of Cloud Computing concepts and technologies. It starts with a brief history about cloud computing, tracing its roots. Then, architectural models of cloud services are described, and the most relevant products for Cloud Computing are briefly discussed along with a comprehensive literature review. The paper highlights and analyzes the most pertinent and practical network issues of relevance to the provision of high-assurance cloud services through the Internet, including security. Finally, trends and future research directions are also presented. Categories and Subject Descriptors: C.2.2 [Computer-Communication Networks]: Network Protocols; C.2.3 [Computer-Communication Networks]: Network Operations; C.2.4 [Computer- Communication Networks]: Distributed Systems General Terms: Design, Algorithms, Management, Performance, Security, Reliability Additional Key Words and Phrases: Cloud Architecture, Cloud Solutions, Security Challenges, Cloud DDoS, Performance Challenges, Management of Cloud Services in Future networks 1. -

Vulnerability Summary for the Week of September 17, 2018.Pdf
Vulnerability Summary for the Week of September 17, 2018 The vulnerabilities are based on the CVE vulnerability naming standard and are organized according to severity, determined by the Common Vulnerability Scoring System (CVSS) standard. The division of high, medium, and low severities correspond to the following scores: High - Vulnerabilities will be labeled High severity if they have a CVSS base score of 7.0 - 10.0 Medium - Vulnerabilities will be labeled Medium severity if they have a CVSS base score of 4.0 - 6.9 Low - Vulnerabilities will be labeled Low severity if they have a CVSS base score of 0.0 - 3.9 Entries may include additional information provided by organizations and efforts sponsored by Ug-CERT. This information may include identifying information, values, definitions, and related links. Patch information is provided when available. Please note that some of the information in the bulletins is compiled from external, open source reports and is not a direct result of Ug-CERT analysis. High Vulnerabilities Primary CVSS Source & Vendor -- Product Description Published Score Patch Info There were no high vulnerabilities recorded this week. Back to top Medium Vulnerabilities Primary CVSS Source & Vendor -- Product Description Published Score Patch Info There were no medium vulnerabilities recorded this week. Back to top Low Vulnerabilities Primary CVSS Source & Vendor -- Product Description Published Score Patch Info There were no low vulnerabilities recorded this week. Back to top Severity Not Yet Assigned Source & Primary PublisCVSS Patch Vendor -- Product Description hed Score Info CVE- 2018- not 15546 Accusoft PrizmDoc version 13.3 and earlier yet CONFI accusoft -- prizmdoc contains a Stored Cross-Site Scripting issue 2018- calcul RM through a crafted PDF file. -

Happy 18Th Birthday, Apache Spamassassin™
Happy 18th Birthday, Apache SpamAssassin™ software to stop spam Sidney Markowitz Chair, Apache SpamAssassin PMC [email protected] linkedin.com/in/sidneymarkowitz What is SpamAssassin? A scoring framework An API and a program In Plesk and cPanel and … What is SpamAssassin? A scoring framework An API and a program In Plesk and cPanel and … (You might be using it and not even know it) SpamAssassin timeline, conception to birth 20 Apr 2001 - Justin Mason first commits code to Sourceforge repo 05 Sep 2001 - SpamAssassin 1.0 released 19 Sep 2001 - SpamAssassin 1.1 released 29 Sep 2001 - SpamAssassin 1.2 released 11 Oct 2001 - Genetic Algorithm to score rules (machine learning) 16 Oct 2001 - spamc/spamd client server added 25 Oct 2001 - SpamAssassin 1.3 released 15 Nov 2001 - SpamAssassin 1.4 released 23 Jan 2002 - SpamAssassin 2.0 released SpamAssassin timeline, childhood 23 Jan 2002 - SpamAssassin 2.0 released 20 Feb 2003 - SpamAssassin 2.50 released - Plugin support! 21 Aug 2003 - SpamAssassin 2.60 released 20 Dec 2003 - SpamAssassin becomes an Apache incubator project 23 Jun 2004 - SpamAssassin graduates to full Apache Project status 22 Sep 2004 - Apache SpamAssassin 3.0.0 released SpamAssassin timeline, release, release... 22 Sep 2004 - Apache SpamAssassin 3.0.0 released 14 Sep 2005 SpamAssassin 3.1.0 released Awards! Datamatation’s Product of the Year Anti-Spam Category 2005, 2006 Linux New Media Awards 2006 Best Linux Anti-Spam Solution 02 May 2007 SpamAssassin 3.2.0 released (3.1.x releases continue) 01 Jan 2010 - Y2K10 bug found and -

Table of Contents
Links Table of contents 1 Multimedia................................................................................................................... 2 2 hvanbelle-sites.............................................................................................................. 2 3 Search........................................................................................................................... 2 4 News.............................................................................................................................3 5 Programming................................................................................................................ 3 5.1 General.....................................................................................................................3 5.2 Ruby.........................................................................................................................3 5.3 Perl........................................................................................................................... 3 5.4 Java.......................................................................................................................... 3 5.5 Java Netbeans...........................................................................................................4 5.6 Apache..................................................................................................................... 4 5.7 WebSphere...............................................................................................................4