Objects of Value
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Design Pattern Interview Questions
DDEESSIIGGNN PPAATTTTEERRNN -- IINNTTEERRVVIIEEWW QQUUEESSTTIIOONNSS http://www.tutorialspoint.com/design_pattern/design_pattern_interview_questions.htm Copyright © tutorialspoint.com Dear readers, these Design Pattern Interview Questions have been designed specially to get you acquainted with the nature of questions you may encounter during your interview for the subject of Design Pattern. As per my experience good interviewers hardly plan to ask any particular question during your interview, normally questions start with some basic concept of the subject and later they continue based on further discussion and what you answer: What are Design Patterns? Design patterns represent the best practices used by experienced object-oriented software developers. Design patterns are solutions to general problems that software developers faced during software development. These solutions were obtained by trial and error by numerous software developers over quite a substantial period of time. What is Gang of Four GOF? In 1994, four authors Erich Gamma, Richard Helm, Ralph Johnson and John Vlissides published a book titled Design Patterns - Elements of Reusable Object-Oriented Software which initiated the concept of Design Pattern in Software development. These authors are collectively known as Gang of Four GOF. Name types of Design Patterns? Design patterns can be classified in three categories: Creational, Structural and Behavioral patterns. Creational Patterns - These design patterns provide a way to create objects while hiding the creation logic, rather than instantiating objects directly using new opreator. This gives program more flexibility in deciding which objects need to be created for a given use case. Structural Patterns - These design patterns concern class and object composition. Concept of inheritance is used to compose interfaces and define ways to compose objects to obtain new functionalities. -

Introductory Programming in C# Release 1.0
Introductory Programming in C# Release 1.0 Andrew N. Harrington and George K. Thiruvathukal May 29, 2012 CONTENTS 1 Context 1 1.1 Introduction to the Notes.........................................1 1.2 Comments on Miles Chapter 1......................................1 2 C# Data and Operations 3 2.1 Development Tools............................................3 2.2 Lab Exercise: Editing, Compiling, and Running............................5 2.3 Comments on Miles Simple Data....................................9 2.4 Division and Remainders.........................................9 2.5 Substitutions in Console.WriteLine................................... 10 2.6 Learning to Solve Problems....................................... 12 2.7 Lab: Division Sentences......................................... 15 2.8 Homework: Grade Calculation...................................... 18 3 Defining Functions of your Own 23 3.1 Syntax Template Typography...................................... 23 3.2 A First Function Definition....................................... 23 3.3 Multiple Function Definitions...................................... 25 3.4 Function Parameters........................................... 26 3.5 Multiple Function Parameters...................................... 29 3.6 Returned Function Values........................................ 30 3.7 Two Roles: Writer and Consumer of Functions............................. 32 3.8 Local Scope............................................... 33 3.9 Static Variables............................................. -

Designpatternsphp Documentation Release 1.0
DesignPatternsPHP Documentation Release 1.0 Dominik Liebler and contributors Jul 18, 2021 Contents 1 Patterns 3 1.1 Creational................................................3 1.1.1 Abstract Factory........................................3 1.1.2 Builder.............................................8 1.1.3 Factory Method......................................... 13 1.1.4 Pool............................................... 18 1.1.5 Prototype............................................ 21 1.1.6 Simple Factory......................................... 24 1.1.7 Singleton............................................ 26 1.1.8 Static Factory.......................................... 28 1.2 Structural................................................. 30 1.2.1 Adapter / Wrapper....................................... 31 1.2.2 Bridge.............................................. 35 1.2.3 Composite............................................ 39 1.2.4 Data Mapper.......................................... 42 1.2.5 Decorator............................................ 46 1.2.6 Dependency Injection...................................... 50 1.2.7 Facade.............................................. 53 1.2.8 Fluent Interface......................................... 56 1.2.9 Flyweight............................................ 59 1.2.10 Proxy.............................................. 62 1.2.11 Registry............................................. 66 1.3 Behavioral................................................ 69 1.3.1 Chain Of Responsibilities................................... -
Ultimate C#, .Net Interview Q&AE-Book
Register your resume: www.terrafirmajobs.com _________________________________________________ www.terrafirmajobs.com Ultimate C#, .Net Interview Q&AE-book Free E-books available with Terra Firma Java Interview Q&A Terra Firma’s Interview Kit Are you stressed at your Desk Restore the rhythm of your life IT Resume writing tips Heart-Care Tips To get these free e-books, email to: [email protected] with the title of the e-book. Copy Right Note You are permitted to freely distribute/print the unmodified version of this issue/e-book/article. We are not attempting to obtain commercial benefit from the valuable work of the authors and the Editor/Publisher claims the ‘fair use’ of copyrighted material. If you think that by publishing a particular material, your copyright has been violated, please let us know. The Editor/Publisher is not responsible for statements or opinions expressed herein nor do such statements necessarily express the views of Editor/Publisher. 1 More Career Tips: http://www.terrafirmajobs.com/ITpros/IT_resources.asp?id=4 ______________________________________________________________________________ Register your resume: www.terrafirmajobs.com _________________________________________________ Index Chapter Name Page 1) C# interview Questions and Answers. 4 1.1) Advance C# interview Questions 2) General Questions 17 2.1 ) General Questions 2.2 ) Methods and Property 2.3) Assembly Questions 2.4) XML Documentation Question 2.5) Debugging and Testing 3) ADO.net and Database Question 26 4) C#, DOT NET, XML, IIS Interview Questions 28 4.1 ) Framework. 4.2 ) COM 4.3 ) OOPS 4.4 ) C# Language Features 4.5 ) Access Specifier 4.6 ) Constructor / Destructor 4.7 ) ADO.net 4.8 ) ASP.net 4.8.1) Session. -

The Rule of the Big Five
C++11: The Rule of the Big Five Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to (manually) control the allocation of memory for the object, handle the object’s initialisation, then ensure that the object was safely cleaned-up after use and its memory returned to the heap. Because many C programmers weren’t educated in the potential problems (or were just plain lazy or delinquent in their programming) C got a reputation in some quarters for being an unsafe, memory-leaking language. C++ improved matters significantly by introducing an idiom known (snappily) as RAII/RRID – Resource Acquisition Is Initialisation / Resource Release Is Destruction*. The idiom makes use of the fact that every time an object is created a constructor is called; and when that object goes out of scope a destructor is called. The constructor/destructor pair can be used to create an object that automatically allocates and initialises another object (known as the managed object) and cleans up the managed object when it (the manager) goes out of scope. This mechanism is generically referred to as resource management. A resource could be any object that required dynamic creation/deletion – memory, files, sockets, mutexes, etc. Resource management frees the client from having to worry about the lifetime of the managed object, potentially eliminating memory leaks and other problems in C++ code. However, RAII/RRID doesn’t come without cost (to be fair, what does?) Introducing a ‘manager’ object can lead to potential problems – particularly if the ‘manager’ class is passed around the system (it is just another object, after all). -
NET Database Technologies
.NET Database Technologies Entity Framework in Enterprise Applications ORMs in Enterprise Applications l Key issues to consider: l Domain l Granularity of object storage/retrieval l Design of relationships to support storage/ retrieval patterns l Architecture l Isolate presentation/service layers from dependency on data layer l Code re-use l Testability En$ty Framework in Enterprise Applicaons 2 Domain Driven Design l Terminology and concepts of DDD can help with design of domain model with persistence in mind l Model elements correspond to domain classes l Thinking in terms of DDD elements helps clarify how classes should be related and be mapped to storage En$ty Framework in Enterprise Applicaons 3 DDD model elements l Entity l An Entity is defined by having an Identity and continuity l Unique within the system l Value Object l Has no Identity l Represent something by its attributes only l Should probably be immutable - you can create a new one instead of changing another one En$ty Framework in Enterprise Applicaons 4 DDD model elements l Aggregate l Group of things which belong together l Constituent objects make no sense without their parent object l Aggregate Root l Single entity which controls access to an aggregate l Entity which is dealt with by a Repository l Should not have relationships between entities in different aggregates which are not the roots En$ty Framework in Enterprise Applicaons 5 Finding aggregates l Identifying aggregates can help to: l Verify that relationships within the domain model are valid and establish their -

JSPP: Morphing C++ Into Javascript Christopher Chedeau, Didier Verna
JSPP: Morphing C++ into JavaScript Christopher Chedeau, Didier Verna To cite this version: Christopher Chedeau, Didier Verna. JSPP: Morphing C++ into JavaScript. [Research Report] LRDE - Laboratoire de Recherche et de Développement de l’EPITA. 2012. hal-01543025 HAL Id: hal-01543025 https://hal.archives-ouvertes.fr/hal-01543025 Submitted on 20 Jun 2017 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. JSPP: Morphing C++ into JavaScript Christopher Chedeau, Didier Verna EPITA Research and Development Laboratory 14–16, rue Voltaire 94276 Le Kremlin-Bicêtre CEDEX, France {christopher.chedeau,didier.verna}@lrde.epita.fr ABSTRACT original JavaScript syntax as much as possible. Ultimately, In a time where the differences between static and dynamic we would like to be able to simply copy and paste JavaScript languages are starting to fade away, this paper brings one code in a C++ source file and compile it as-is. more element to the \convergence" picture by showing that A first prototypical implementation of a syntax-preserving thanks to the novelties from the recent C++0x standard, it JavaScript engine in C++ has been developed. The project is relatively easy to implement a JavaScript layer on top of is called JSPP. -

Static Typing for Object-Oriented Programming 1 Introduction
Science of Computer Programming 23(1):19{53, 1994. Static Typing for Object-Oriented Programming Jens Palsberg Michael I. Schwartzbach [email protected] [email protected] Computer Science Department Aarhus University Ny Munkegade DK-8000 Arh˚ us C, Denmark Abstract We develop a theory of statically typed object-oriented languages. It rep- resents classes as labeled, regular trees, types as finite sets of classes, and subclassing as a partial order on trees. We show that our subclassing or- der strictly generalizes inheritance, and that a novel genericity mechanism arises as an order-theoretic complement. This mechanism, called class substitution, is pragmatically useful and can be implemented efficiently. 1 Introduction Object-oriented programming is becoming widespread. Numerous programming languages supporting object-oriented concepts are in use, and theories about object-oriented design and implementation are being developed and applied [21, 3, 14]. An important issue in object-oriented programming is to obtain reusable software components [30]. This is achieved through the notions of object, class, inheritance, late binding, and the imperative constructs of variables and assignments. Such features are found for example in the Smalltalk language [25] in which a large number of reusable classes have been written. Smalltalk, however, is untyped. Though this is ideal for prototyping and exploratory development, a static type system is required to ensure that programs are readable, reliable, and efficient. This paper studies an idealized subset of Smalltalk, equipped with a novel static type system. Our analysis results in the definition of a new genericity mechanism, called class substitution, which we prove to be the order-theoretic complement of inheritance. -
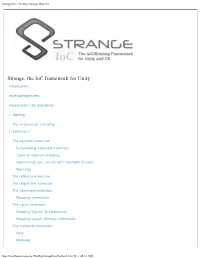
Strangeioc - the Big, Strange How-To
StrangeIoC - The Big, Strange How-To Strange: the IoC framework for Unity Introduction Acknowledgements Introduction: the directories 1. Binding The structure of a binding 2. Extensions The injection extension Instantiating injectable instances Types of injection mapping Some things you can do with Injectable Classes Warnings The reflector extension The dispatcher extension The command extension Mapping commands The signal extension Mapping Signals To Commands Mapping Signals Without Commands The mediation extension View Mediator http://localhost/strangeioc/TheBigStrangeHowTo.html[3/22/15, 1:40:13 AM] StrangeIoC - The Big, Strange How-To The context extension 3. MVCSContext: the big picture Concepts Set up your project A scene is set... A ContextView begins... The Context binds... A Command fires... A View is mediated... Another Command fires... And we’re served... Mapping Across Contexts 4. Conclusion Strange: the IoC framework for Unity Strange attractors create predictable patterns, often in chaotic systems. Introduction Strange is a super-lightweight and highly extensible Inversion-of-Control (IoC) framework, written specifically for C# and Unity. We’ve validated Strange on web, standalone, and iOS and Android. It contains the following features, most of which are optional: A core binding framework that pretty much lets you bind one or more of anything to one or more of anything else. Dependency Injection Map as singleton, value or factory (get a new instance each time you need one) Name injections Perform constructor or setter injection Tag your preferred constructor Tag a method to fire after construction Inject into MonoBehaviours Bind polymorphically (bind any or all of your interfaces to a single concrete class) Reflection binding dramatically reduces overhead of employing reflectivity Two styles of shared event bus. -
Transformation for Class Immutability
Transformation for Class Immutability Fredrik Kjolstad Danny Dig Gabriel Acevedo Marc Snir University of Illinois at Urbana-Champaign {kjolsta1, dig, acevedo7, snir}@illinois.edu ABSTRACT tion [12,14] or flyweight [8]). They also enable compiler opti- It is common for object-oriented programs to have both mu- mizations such as reducing the number of dynamic reads [16]. table and immutable classes. Immutable classes simplify In fact, some argue that we should always use immutable programing because the programmer does not have to rea- classes unless we explicitly need mutability [3]. son about side-effects. Sometimes programmers write im- In addition, immutability makes distributed programming mutable classes from scratch, other times they transform simpler [2]. With current middleware technologies like Java mutable into immutable classes. To transform a mutable RMI, EJB, and Corba, a client can send messages to a dis- class, programmers must find all methods that mutate its tributed object via a local proxy. The proxy implements an transitive state and all objects that can enter or escape update protocol, so if the distributed object is immutable the state of the class. The analyses are non-trivial and the then there is no need for the proxy. rewriting is tedious. Fortunately, this can be automated. Moreover, as parallel programming becomes ubiquitous in the multicore era, immutability makes parallel programming We present an algorithm and a tool, Immutator, that en- ables the programmer to safely transform a mutable class simpler [9,13]. Since threads can not change the state of an into an immutable class. Two case studies and one con- immutable object, they can share it without synchroniza- tion. -

I DOPC++: EXTENDING C++ with DISTRIBUTED OBJECTS and OBJECT MIGRATION for PGAS MODEL a Thesis Submitted to Kent State University
DOPC++: EXTENDING C++ WITH DISTRIBUTED OBJECTS AND OBJECT MIGRATION FOR PGAS MODEL A thesis submitted to Kent State University in partial fulfillment of the requirements for the degree of Master of Science by Salwa Aljehane December,2015 i Thesis written by Salwa Aljehane B.S., Tibah University, KSA 2007 M.S., Kent State University, USA, 2015 Approved by Dr. Arvind Bansal , Advisor, Master Thesis Committee Dr. Austin Milton , Members, Master Thesis Committee Dr. Angela Guercio , Members, Master Thesis Committee Accepted by Dr. Javed Khan , Chair, Department of Computer Science Dr. James L. Blank , Dean, College of Arts and Sciences ii TABLE OF CONTENTS LIST OF FIGURES ..................................................................................................... VIII! LIST OF TABLES .......................................................................................................... IX! ACKNOWLEDGEMENTS ............................................................................................ X! ABSTRACT ................................................................................................................... XII! CHAPTER 1 INTRODUCTION ..................................................................................... 1! 1.1! Motivation .................................................................................................................. 1! 1.2! Previous Work and Current Limitations .................................................................... 3! 1.4! Objectives of this Research: ...................................................................................... -

IBM Informix Object Interface for C++ Programmer™S Guide
Informix Product Family Informix Client Software Development Kit Version 3.70 IBM Informix Object Interface for C++ Programmer’s Guide SC27-3559-01 Informix Product Family Informix Client Software Development Kit Version 3.70 IBM Informix Object Interface for C++ Programmer’s Guide SC27-3559-01 Note Before using this information and the product it supports, read the information in “Notices” on page E-1. This edition replaces SC27-3559-00. This document contains proprietary information of IBM. It is provided under a license agreement and is protected by copyright law. The information contained in this publication does not include any product warranties, and any statements provided in this publication should not be interpreted as such. When you send information to IBM, you grant IBM a nonexclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. © Copyright IBM Corporation 1996, 2011. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Introduction .................................vii About this publication ...............................vii Types of users .................................vii Software compatibility ..............................vii Naming conventions ...............................vii Example code conventions ..............................vii Additional documentation ..............................viii Compliance with industry standards ..........................viii How