Using the JIT Vulnerability to Pwning Microsoft Edge
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
AAS Worldwide Telescope: Seamless, Cross-Platform Data Visualization Engine for Astronomy Research, Education, and Democratizing Data
AAS WorldWide Telescope: Seamless, Cross-Platform Data Visualization Engine for Astronomy Research, Education, and Democratizing Data The Harvard community has made this article openly available. Please share how this access benefits you. Your story matters Citation Rosenfield, Philip, Jonathan Fay, Ronald K Gilchrist, Chenzhou Cui, A. David Weigel, Thomas Robitaille, Oderah Justin Otor, and Alyssa Goodman. 2018. AAS WorldWide Telescope: Seamless, Cross-Platform Data Visualization Engine for Astronomy Research, Education, and Democratizing Data. The Astrophysical Journal: Supplement Series 236, no. 1. Published Version https://iopscience-iop-org.ezp-prod1.hul.harvard.edu/ article/10.3847/1538-4365/aab776 Citable link http://nrs.harvard.edu/urn-3:HUL.InstRepos:41504669 Terms of Use This article was downloaded from Harvard University’s DASH repository, and is made available under the terms and conditions applicable to Open Access Policy Articles, as set forth at http:// nrs.harvard.edu/urn-3:HUL.InstRepos:dash.current.terms-of- use#OAP Draft version January 30, 2018 Typeset using LATEX twocolumn style in AASTeX62 AAS WorldWide Telescope: Seamless, Cross-Platform Data Visualization Engine for Astronomy Research, Education, and Democratizing Data Philip Rosenfield,1 Jonathan Fay,1 Ronald K Gilchrist,1 Chenzhou Cui,2 A. David Weigel,3 Thomas Robitaille,4 Oderah Justin Otor,1 and Alyssa Goodman5 1American Astronomical Society 1667 K St NW Suite 800 Washington, DC 20006, USA 2National Astronomical Observatories, Chinese Academy of Sciences 20A Datun Road, Chaoyang District Beijing, 100012, China 3Christenberry Planetarium, Samford University 800 Lakeshore Drive Birmingham, AL 35229, USA 4Aperio Software Ltd. Headingley Enterprise and Arts Centre, Bennett Road Leeds, LS6 3HN, United Kingdom 5Harvard Smithsonian Center for Astrophysics 60 Garden St. -
XAMARIN.FORMS for BEGINNERS ABOUT ME Tom Soderling Sr
XAMARIN.FORMS FOR BEGINNERS ABOUT ME Tom Soderling Sr. Mobile Apps Developer @ Polaris Industries; Ride Command Xamarin.Forms enthusiast DevOps hobbyist & machine learning beginner 4 year XCMD Blog: https://tomsoderling.github.io GitHub: https://github.com/TomSoderling Twitter: @tomsoderling How Deep Pickster Spaniel Is It? THE PLAN • Introduction: Why, What, and When • Overview of Xamarin.Forms Building Blocks • Building a Xamarin.Forms UI in XAML • Data Binding • View Customization • Next Steps & Resources • Please ask any questions that come up! THE PLAN • Introduction: Why, What, and When • Overview of Xamarin.Forms Building Blocks • Building a Xamarin.Forms UI in XAML • Data Binding • View Customization • Next Steps & Resources INTRODUCTION : WHY • WET: the soggy state of mobile app development • Write Everything Twice INTRODUCTION : WHY • WET: the soggy state of mobile app development • Write Everything Twice INTRODUCTION : WHAT • What is Xamarin.Forms? • Cross-platform UI framework • Platforms: • Mobile: iOS 8 and up, Android 4.0.3 (API 15) • Desktop: Windows 10 UWP, MacOS, WFP • Samsung Smart Devices: Tizen INTRODUCTION : WHAT • Brief History: • May 2011, Xamarin founded • MonoTouch and Mono for Android using MonoDevelop IDE • February 2013, release of Xamarin 2.0 • Xamarin Studio IDE & integration with Visual Studio • Renamed to Xamarin.Android and Xamarin.iOS • May 2014, Xamarin.Forms released as part of Xamarin 3 • February 24 2016, Xamarin acquired by Microsoft • Owned, actively developed on, and supported by Microsoft • Free -

Licensing Information User Manual Release 9.1 F13415-01
Oracle® Hospitality Cruise Fleet Management Licensing Information User Manual Release 9.1 F13415-01 August 2019 LICENSING INFORMATION USER MANUAL Oracle® Hospitality Fleet Management Licensing Information User Manual Version 9.1 Copyright © 2004, 2019, Oracle and/or its affiliates. All rights reserved. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error- free. If you find any errors, please report them to us in writing. If this software or related documentation is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and adaptation of the programs, including any operating system, integrated software, any programs installed on the hardware, and/or documentation, shall be subject to license terms and license restrictions applicable to the programs. -
Internet Explorer 9 Features
m National Institute of Information Technologies NIIT White Paper On “What is New in Internet Explorer 9” Submitted by: Md. Yusuf Hasan Student ID: S093022200027 Year: 1st Quarter: 2nd Program: M.M.S Date - 08 June 2010 Dhaka - Bangladesh Internet Explorer History Abstract: In the early 90s—the dawn of history as far as the World Wide Web is concerned—relatively few users were communicating across this Internet Explorer 9 (abbreviated as IE9) is the upcoming global network. They used an assortment of shareware and other version of the Internet Explorer web browser from software for Microsoft Windows operating system. In 1995, Microsoft Microsoft. It is currently in development, but developer hosted an Internet Strategy Day and announced its commitment to adding Internet capabilities to all its products. In fulfillment of that previews have been released. announcement, Microsoft Internet Explorer arrived as both a graphical Web browser and the name for a set of technologies. IE9 will have complete or nearly complete support for all 1995: Internet Explorer 1.0: In July 1995, Microsoft released the CSS 3 selectors, border-radius CSS 3 property, faster Windows 95 operating system, which included built-in support for JavaScript and embedded ICC v2 or v4 color profiles dial-up networking and TCP/IP (Transmission Control support via Windows Color System. IE9 will feature Protocol/Internet Protocol), key technologies for connecting to the hardware accelerated graphics rendering using Direct2D, Internet. In response to the growing public interest in the Internet, Microsoft created an add-on to the operating system called Internet hardware accelerated text rendering using Direct Write, Explorer 1.0. -
Seeing the Sky Visualization & Astronomers
Seeing the Sky Visualization & Astronomers Alyssa A. Goodman Harvard Smithsonian Center for Astrophysics & Radcliffe Institute for Advanced Study @aagie WorldWide Telescope Gm1m2 F= gluemultidimensional data exploration R2 Cognition “Paper of the Future” Language* Data Pictures Communication *“Language” includes words & math Why Galileo is my Hero Explore-Explain-Explore Notes for & re-productions of Siderius Nuncius 1610 WorldWide Telescope Galileo’s New Order, A WorldWide Telescope Tour by Goodman, Wong & Udomprasert 2010 WWT Software Wong (inventor, MS Research), Fay (architect, MS Reseearch), et al., now open source, hosted by AAS, Phil Rosenfield, Director see wwtambassadors.org for more on WWT Outreach WorldWide Telescope Galileo’s New Order, A WorldWide Telescope Tour by Goodman, Wong & Udomprasert 2010 WWT Software Wong (inventor, MS Research), Fay (architect, MS Reseearch), et al., now open source, hosted by AAS, Phil Rosenfield, Director see wwtambassadors.org for more on WWT Outreach Cognition “Paper of the Future” Language* Data Pictures Communication *“Language” includes words & math enabled by d3.js (javascript) outputs d3po Cognition Communication [demo] [video] Many thanks to Alberto Pepe, Josh Peek, Chris Beaumont, Tom Robitaille, Adrian Price-Whelan, Elizabeth Newton, Michelle Borkin & Matteo Cantiello for making this posible. 1610 4 Centuries from Galileo to Galileo 1665 1895 2009 2015 WorldWide Telescope Gm1m2 F= gluemultidimensional data exploration R2 WorldWide Telescope gluemultidimensional data exploration WorldWide Telescope gluemultidimensional data exploration Data, Dimensions, Display 1D: Columns = “Spectra”, “SEDs” or “Time Series” 2D: Faces or Slices = “Images” 3D: Volumes = “3D Renderings”, “2D Movies” 4D:4D Time Series of Volumes = “3D Movies” Data, Dimensions, Display Spectral Line Observations Loss of 1 dimension Mountain Range No loss of information Data, Dimensions, Display mm peak (Enoch et al. -

Software License Agreement (EULA)
Third-party Computer Software AutoVu™ ALPR cameras • angular-animate (https://docs.angularjs.org/api/ngAnimate) licensed under the terms of the MIT License (https://github.com/angular/angular.js/blob/master/LICENSE). © 2010-2016 Google, Inc. http://angularjs.org • angular-base64 (https://github.com/ninjatronic/angular-base64) licensed under the terms of the MIT License (https://github.com/ninjatronic/angular-base64/blob/master/LICENSE). © 2010 Nick Galbreath © 2013 Pete Martin • angular-translate (https://github.com/angular-translate/angular-translate) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • angular-translate-handler-log (https://github.com/angular-translate/bower-angular-translate-handler-log) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • angular-translate-loader-static-files (https://github.com/angular-translate/bower-angular-translate-loader-static-files) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • Angular Google Maps (http://angular-ui.github.io/angular-google-maps/#!/) licensed under the terms of the MIT License (https://opensource.org/licenses/MIT). © 2013-2016 angular-google-maps • AngularJS (http://angularjs.org/) licensed under the terms of the MIT License (https://github.com/angular/angular.js/blob/master/LICENSE). © 2010-2016 Google, Inc. http://angularjs.org • AngularUI Bootstrap (http://angular-ui.github.io/bootstrap/) licensed under the terms of the MIT License (https://github.com/angular- ui/bootstrap/blob/master/LICENSE). -

How Github Secures Open Source Software
How GitHub secures open source software Learn how GitHub works to protect you as you use, contribute to, and build on open source. HOW GITHUB SECURES OPEN SOURCE SOFTWARE PAGE — 1 That’s why we’ve built tools and processes that allow GitHub’s role in securing organizations and open source maintainers to code securely throughout the entire software development open source software lifecycle. Taking security and shifting it to the left allows organizations and projects to prevent errors and failures Open source software is everywhere, before a security incident happens. powering the languages, frameworks, and GitHub works hard to secure our community and applications your team uses every day. the open source software you use, build on, and contribute to. Through features, services, and security A study conducted by the Synopsys Center for Open initiatives, we provide the millions of open source Source Research and Innovation found that enterprise projects on GitHub—and the businesses that rely on software is now comprised of more than 90 percent them—with best practices to learn and leverage across open source code—and businesses are taking notice. their workflows. The State of Enterprise Open Source study by Red Hat confirmed that “95 percent of respondents say open source is strategically important” for organizations. Making code widely available has changed how Making open source software is built, with more reuse of code and complex more secure dependencies—but not without introducing security and compliance concerns. Open source projects, like all software, can have vulnerabilities. They can even be GitHub Advisory Database, vulnerable the target of malicious actors who may try to use open dependency alerts, and Dependabot source code to introduce vulnerabilities downstream, attacking the software supply chain. -
Presented by Alyssa Goodman, Center for Astrophysics | Harvard & Smithsonian, Radcliffe Institute for Advanced Study
The Radcliffe Wave presented by Alyssa Goodman, Center for Astrophysics | Harvard & Smithsonian, Radcliffe Institute for Advanced Study Nature paper by: João Alves1,3, Catherine Zucker2, Alyssa Goodman2,3, Joshua Speagle2, Stefan Meingast1, Thomas Robitaille4, Douglas Finkbeiner3, Edward Schlafly5 & Gregory Green6 representing (1) University of Vienna; (2) Harvard University; (3) Radcliffe Insitute; (4) Aperio Software; (5) Lawrence Berkeley National Laboratory; (6) Kavli Insitute for Particle Physics and Cosmology The Radcliffe Wave CARTOON* DATA *drawn by Dr. Robert Hurt, in collaboration with Milky Way experts based on data; as shown in screenshot from AAS WorldWide Telescope The Radcliffe Wave Each red dot marks a star-forming blob of gas whose distance from us has been accurately measured. The Radcliffe Wave is 9000 light years long, and 400 light years wide, with crest and trough reaching 500 light years out of the Galactic Plane. Its gas mass is more than three million times the mass of the Sun. video created by the authors using AAS WorldWide Telescope (includes cartoon Milky Way by Robert Hurt) The Radcliffe Wave ACTUALLY 2 IMPORTANT DEVELOPMENTS DISTANCES!! RADWAVE We can now Surprising wave- measure distances like arrangement to gas clouds in our of star-forming gas own Milky Way is the “Local Arm” galaxy to ~5% of the Milky Way. accuracy. Zucker et al. 2019; 2020 Alves et al. 2020 “Why should I believe all this?” DISTANCES!! We can now requires special measure distances regions on the Sky to gas clouds in our (HII regions own Milky Way with masers) galaxy to ~5% accuracy. can be used anywhere there’s dust & measurable stellar properties Zucker et al. -

Your Chakra Is Not Aligned Hunting Bugs in the Microsoft Edge Script Engine About Me
Your Chakra Is Not Aligned Hunting bugs in the Microsoft Edge Script Engine About Me ● Natalie Silvanovich AKA natashenka ● Project Zero member ● Previously did mobile security on Android and BlackBerry ● ECMAScript enthusiast What are Edge and Chakra ● Edge: Windows 10 browser ● Chakra: Edge’s open-source ECMAScript core ○ Regularly updated ○ Accepts external contributions What is ECMAScript ● ECMAScript == Javascript (mostly) ● Javascript engines implement the ECMAScript standard ● ES7 released in June Why newness matters ● Standards don’t specify implementation ● Design decisions are untested ○ Security and performance advantages (and disadvantages) ● Developers and hackers learn from new bugs ● Attacks mature over time ● High contention space Goals ● Find bugs in Chakra ● Understand and improve weak areas ● Find deep, unusual bugs* Approach ● Code review ○ Finds quality bugs ○ Bugs live longer* ○ Easier to fix an entire class of bugs RTFS ● Reading the standard is important ○ Mozilla docs (MDN) is a great start ● Many features are used infrequently but cause bugs ● Features are deeply intertwined Array.species “But what if I subclass an array and slice it, and I want the thing I get back to be a regular Array and not the subclass?” class MyArray extends Array { static get [Symbol.species]() { return Array;} } ● Easily implemented by inserting a call to script into *every single* Array native call Array Conversion ● Arrays can be complicated but most Arrays are simple ○ Most implementations have simple arrays with more complex fallbacks IntegerArray Add a float FloatArray Add a non-numeric value Configure a value (e.g read-only) ES5Array VarArray Array Conversion ● Integer, Float and ES5 arrays are subclasses of Var Array superclass ● vtable swapping (for real) Array Conversion IntSegment IntArray length vtable size length left head next .. -

Time-Travel Debugging for Javascript/Node.Js
Time-Travel Debugging for JavaScript/Node.js Earl T. Barr Mark Marron Ed Maurer University College London, UK Microsoft Research, USA Microsoft, USA [email protected] [email protected] [email protected] Dan Moseley Gaurav Seth Microsoft, USA Microsoft, USA [email protected] [email protected] ABSTRACT Time-traveling in the execution history of a program during de- bugging enables a developer to precisely track and understand the sequence of statements and program values leading to an error. To provide this functionality to real world developers, we embarked on a two year journey to create a production quality time-traveling de- bugger in Microsoft’s open-source ChakraCore JavaScript engine and the popular Node.js application framework. CCS Concepts •Software and its engineering ! Software testing and debug- Figure 1: Visual Studio Code with extra time-travel functional- ging; ity (Step-Back button in top action bar) at a breakpoint. Keywords • Options for both using time-travel during local debugging Time-Travel Debugging, JavaScript, Node.js and for recording a trace in production for postmortem de- bugging or other analysis (Section 2.1). 1. INTRODUCTION • Reverse-Step Local and Dynamic operations (Section 2.2) Modern integrated development environments (IDEs) provide a that allow the developer to step-back in time to the previously range of tools for setting breakpoints, examining program state, and executed statement in the current function or to step-back in manually logging execution. These features enable developers to time to the previously executed statement in any frame in- quickly track down localized bugs, provided all of the relevant val- cluding exception throws or callee returns. -
Meridium V3.6X Open Source Licenses (PDF Format)
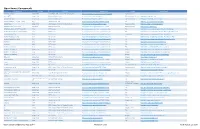
Open Source Components Component Version License License Link Usage Home Page .NET Zip Library Unspecified SharpZipLib GPL License (GPL w/exception) http://www.icsharpcode.net/opensource/sharpziplib/ Dynamic Library http://dotnetziplib.codeplex.com/ 32feet.NET Unspecified Microsoft Public License http://opensource.org/licenses/MS-PL File + Dynamic Library http://32feet.codeplex.com AjaxControlToolkit Unspecified Microsoft Public License http://opensource.org/licenses/MS-PL Dynamic Library http://ajaxcontroltoolkit.codeplex.com/ Android - platform - external - okhttp 4.3_r1 Apache License 2.0 http://www.apache.org/licenses/LICENSE-2.0.html File http://developer.android.com/index.html angleproject Unspecified BSD 3-clause "New" or "Revised" License http://opensource.org/licenses/BSD-3-Clause Dynamic Library http://code.google.com/p/angleproject/ Apache Lucene - Lucene.Net 3.0.3-RC2 Apache License 2.0 http://www.apache.org/licenses/LICENSE-2.0.html Dynamic Library http://lucenenet.apache.org/ AttributeRouting (ASP.NET Web API) 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php File http://www.nuget.org/packages/AttributeRouting.WebApi AttributeRouting (Self-hosted Web API) 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php File http://www.nuget.org/packages/AttributeRouting.WebApi.Hosted AttributeRouting.Core 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php Component http://www.nuget.org/packages/AttributeRouting.Core AttributeRouting.Core.Http 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php -

College Catalog
401 Medical Park Drive Concord, NC 28025 704-403-1555 • Fax: 704-403-2077 Email: [email protected] www.cabarruscollege.edu 2016–2017 CATALOG CONTENTS Greetings from the President .................................................................................................................. 3 Academic Calendars .................................................................................................................................. 4 Accreditation .............................................................................................................................................. 8 Right to Know ........................................................................................................................................... 9 Right to Revise ........................................................................................................................................... 9 History ......................................................................................................................................................... 9 Vision ........................................................................................................................................................ 10 Mission & Goals ...................................................................................................................................... 10 Core Values .............................................................................................................................................