A Survey on Consensus Mechanisms and Mining Strategy Management
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
YEUNG-DOCUMENT-2019.Pdf (478.1Kb)
Useful Computation on the Block Chain The Harvard community has made this article openly available. Please share how this access benefits you. Your story matters Citation Yeung, Fuk. 2019. Useful Computation on the Block Chain. Master's thesis, Harvard Extension School. Citable link https://nrs.harvard.edu/URN-3:HUL.INSTREPOS:37364565 Terms of Use This article was downloaded from Harvard University’s DASH repository, and is made available under the terms and conditions applicable to Other Posted Material, as set forth at http:// nrs.harvard.edu/urn-3:HUL.InstRepos:dash.current.terms-of- use#LAA 111 Useful Computation on the Block Chain Fuk Yeung A Thesis in the Field of Information Technology for the Degree of Master of Liberal Arts in Extension Studies Harvard University November 2019 Copyright 2019 [Fuk Yeung] Abstract The recent growth of blockchain technology and its usage has increased the size of cryptocurrency networks. However, this increase has come at the cost of high energy consumption due to the processing power needed to maintain large cryptocurrency networks. In the largest networks, this processing power is attributed to wasted computations centered around solving a Proof of Work algorithm. There have been several attempts to address this problem and it is an area of continuing improvement. We will present a summary of proposed solutions as well as an in-depth look at a promising alternative algorithm known as Proof of Useful Work. This solution will redirect wasted computation towards useful work. We will show that this is a viable alternative to Proof of Work. Dedication Thank you to everyone who has supported me throughout the process of writing this piece. -

Chia Proof of Space Construction
Chia Proof of Space Construction Introduction In order to create a secure blockchain consensus algorithm using disk space, a Proof of Space is scheme is necessary. This document describes a practical contruction of Proofs of Space, based on Beyond Hellman’s Time- Memory Trade-Offs with Applications to Proofs of Space [1]. We use the techniques laid out in that paper, extend it from 2 to 7 tables, and tweak it to make it efficient and secure, for use in the Chia Blockchain. The document is divided into three main sections: What (mathematical definition of a proof of space), How (how to implement proof of space), and Why (motivation and explanation of the construction) sections. The Beyond Hellman paper can be read first for more mathematical background. Chia Proof of Space Construction Introduction What is Proof of Space? Definitions Proof format Proof Quality String Definition of parameters, and M, f, A, C functions: Parameters: f functions: Matching function M: A′ function: At function: Collation function C: How do we implement Proof of Space? Plotting Plotting Tables (Concepts) Tables Table Positions Compressing Entry Data Delta Format ANS Encoding of Delta Formatted Points Stub and Small Deltas Parks Checkpoint Tables Plotting Algorithm Final Disk Format Full algorithm Phase 1: Forward Propagation Phase 2: Backpropagation Phase 3: Compression Phase 4: Checkpoints Sort on Disk Plotting Performance Space Required Proving Proof ordering vs Plot ordering Proof Retrieval Quality String Retrieval Proving Performance Verification Construction -

Characterizing Ethereum's Mining Power Decentralization at a Deeper
Characterizing Ethereum’s Mining Power Decentralization at a Deeper Level Liyi Zeng∗§, Yang Chen†§, Shuo Chen†, Xian Zhang†, Zhongxin Guo†, Wei Xu∗, Thomas Moscibroda‡ ∗Institute for Interdisciplinary Information Sciences, Tsinghua University †Microsoft Research ‡Microsoft Azure §Contacts: [email protected], [email protected] Abstract—For proof-of-work blockchains such as Ethereum, than 50% of the total power has grown from several the mining power decentralization is an important discussion hundred to several thousand. Overall, the power is more point in the community. Previous studies mostly focus on the decentralized at the participant level than 4 years ago. aggregated power of the mining pools, neglecting the pool participants who are the source of the pools’ power. In this paper, However, we also find that this number varied signif- we present the first large-scale study of the pool participants icantly over time, which means it requires continuous in Ethereum’s mining pools. Pool participants are not directly tracking. Additionally, as our current data and method- observable because they communicate with their pools via private ology cannot de-anonymize the participants, it’s possible channels. However, they leave “footprints” on chain as they that some participants split themselves into many smaller use Ethereum accounts to anonymously receive rewards from mining pools. For this study, we combine several data sources ones for various reasons, which could make our estima- to identify 62,358,646 pool reward transactions sent by 47 tion inaccurate if not completely off the target. Further pools to their participants over Ethereum’s entire near 5-year study to improve the estimation accuracy is important. -
Blockchain in an Internet-Of-Things Network Based on User Participation
Blockchain in an Internet-of-Things Network Based on User Participation Robert Ljungblad Computer Science and Engineering, bachelor's level 2019 Luleå University of Technology Department of Computer Science, Electrical and Space Engineering ABSTRACT The internet-of-things is the relatively new and rapidly growing concept of connecting everyday devices to the internet. Every day more and more devices are added to the internet-of-things and it is not showing any signs of slowing down. In addition, advancements in new technologies such as blockchains, artificial intelligence, virtual reality and machine learning are made practically every day. However, there are still much to learn about these technologies. This thesis explores the possibilities of blockchain technology by applying it to an internet-of-things network based on user participation. More specifically, it is applied to a use case derived from Luleå Kommun’s wishes to easier keep track of how full the city’s trash cans are. The goal of the thesis is to learn more about how blockchains can help an internet-of-things network as well as what issues can arise. The method takes an exploratory approach to the problem by partaking in a workshop with Luleå Kommun and by performing a literature study. It also takes a qualitative approach by creating a proof-of-concept solution to experience the technology firsthand. The final proof-of-concept as well as issues that arose during the project are analysed with the help of information gathered and experience gained throughout the project. It is concluded that blockchain technology can help communication in an internet-of-things network based on user participation. -

Crypto Research Report ‒ April 2019 Edition
April 2019 Edition VI. “When the Tide Goes Out…” Investments: Gold and Bitcoin, Stronger Together Technical Analysis: Spring Awakening? Cryptocurrency Mining in Theory and Practice Demelza Kelso Hays Mark J. Valek We would like to express our profound gratitude to our premium partners for supporting the Crypto Research Report: www.cryptofunds.li Contents Editorial ............................................................................................................................................... 4 In Case You Were Sleeping: When the Tide Goes Out…............................................................... 5 Back to the Roots ............................................................................................................................................. 6 How Long Will This Bear Market Last .............................................................................................................. 7 A Tragic Story Traverses the World ................................................................................................................. 9 When the tide goes out… ............................................................................................................................... 10 A State Cryptocurrency? ................................................................................................................................ 12 Support is Increasing ..................................................................................................................................... 14 -

IPFS and Friends: a Qualitative Comparison of Next Generation Peer-To-Peer Data Networks Erik Daniel and Florian Tschorsch
1 IPFS and Friends: A Qualitative Comparison of Next Generation Peer-to-Peer Data Networks Erik Daniel and Florian Tschorsch Abstract—Decentralized, distributed storage offers a way to types of files [1]. Napster and Gnutella marked the beginning reduce the impact of data silos as often fostered by centralized and were followed by many other P2P networks focusing on cloud storage. While the intentions of this trend are not new, the specialized application areas or novel network structures. For topic gained traction due to technological advancements, most notably blockchain networks. As a consequence, we observe that example, Freenet [2] realizes anonymous storage and retrieval. a new generation of peer-to-peer data networks emerges. In this Chord [3], CAN [4], and Pastry [5] provide protocols to survey paper, we therefore provide a technical overview of the maintain a structured overlay network topology. In particular, next generation data networks. We use select data networks to BitTorrent [6] received a lot of attention from both users and introduce general concepts and to emphasize new developments. the research community. BitTorrent introduced an incentive Specifically, we provide a deeper outline of the Interplanetary File System and a general overview of Swarm, the Hypercore Pro- mechanism to achieve Pareto efficiency, trying to improve tocol, SAFE, Storj, and Arweave. We identify common building network utilization achieving a higher level of robustness. We blocks and provide a qualitative comparison. From the overview, consider networks such as Napster, Gnutella, Freenet, BitTor- we derive future challenges and research goals concerning data rent, and many more as first generation P2P data networks, networks. -

Evaluating Inclusion, Equality, Security, and Privacy in Pseudonym Parties and Other Proofs of Personhood
Identity and Personhood in Digital Democracy: Evaluating Inclusion, Equality, Security, and Privacy in Pseudonym Parties and Other Proofs of Personhood Bryan Ford Swiss Federal Institute of Technology in Lausanne (EPFL) November 5, 2020 Abstract of enforced physical security and privacy can address the coercion and vote-buying risks that plague today’s E- Digital identity seems at first like a prerequisite for digi- voting and postal voting systems alike. We also examine tal democracy: how can we ensure “one person, one vote” other recently-proposed approaches to proof of person- online without identifying voters? But the full gamut of hood, some of which offer conveniencessuch as all-online digital identity solutions – e.g., online ID checking, bio- participation. These alternatives currently fall short of sat- metrics, self-sovereign identity, and social/trust networks isfying all the key digital personhood goals, unfortunately, – all present severe flaws in security, privacy, and trans- but offer valuable insights into the challenges we face. parency, leaving users vulnerable to exclusion, identity loss or theft, and coercion. These flaws may be insur- mountable because digital identity is a cart pulling the Contents horse. We cannot achieve digital identity secure enough to support the weight of digital democracy, until we can 1 Introduction 2 build it on a solid foundation of digital personhood meet- ing key requirements. While identity is about distinguish- 2 Goals for Digital Personhood 4 ing one person from another through attributes or affilia- tions, personhood is about giving all real people inalien- 3 Pseudonym Parties 5 able digital participation rights independent of identity, 3.1 Thebasicidea. -

Asymmetric Proof-Of-Work Based on the Generalized Birthday Problem
Equihash: Asymmetric Proof-of-Work Based on the Generalized Birthday Problem Alex Biryukov Dmitry Khovratovich University of Luxembourg University of Luxembourg [email protected] [email protected] Abstract—The proof-of-work is a central concept in modern Long before the rise of Bitcoin it was realized [20] that cryptocurrencies and denial-of-service protection tools, but the the dedicated hardware can produce a proof-of-work much requirement for fast verification so far made it an easy prey for faster and cheaper than a regular desktop or laptop. Thus the GPU-, ASIC-, and botnet-equipped users. The attempts to rely on users equipped with such hardware have an advantage over memory-intensive computations in order to remedy the disparity others, which eventually led the Bitcoin mining to concentrate between architectures have resulted in slow or broken schemes. in a few hardware farms of enormous size and high electricity In this paper we solve this open problem and show how to consumption. An advantage of the same order of magnitude construct an asymmetric proof-of-work (PoW) based on a compu- is given to “owners” of large botnets, which nowadays often tationally hard problem, which requires a lot of memory to gen- accommodate hundreds of thousands of machines. For prac- erate a proof (called ”memory-hardness” feature) but is instant tical DoS protection, this means that the early TLS puzzle to verify. Our primary proposal Equihash is a PoW based on the schemes [8], [17] are no longer effective against the most generalized birthday problem and enhanced Wagner’s algorithm powerful adversaries. -

Zcash Protocol Speci Cation
Zcash Protocol Specication Version 2018.0-beta-14 Daira Hopwood† Sean Bowe† — Taylor Hornby† — Nathan Wilcox† March 11, 2018 Abstract. Zcash is an implementation of the Decentralized Anonymous Payment scheme Zerocash, with security xes and adjustments to terminology, functionality and performance. It bridges the exist- ing transparent payment scheme used by Bitcoin with a shielded payment scheme secured by zero- knowledge succinct non-interactive arguments of knowledge (zk-SNARKs). It attempts to address the problem of mining centralization by use of the Equihash memory-hard proof-of-work algorithm. This specication denes the Zcash consensus protocol and explains its differences from Zerocash and Bitcoin. Keywords: anonymity, applications, cryptographic protocols, electronic commerce and payment, nancial privacy, proof of work, zero knowledge. Contents 1 1 Introduction 5 1.1 Caution . .5 1.2 High-level Overview . .5 2 Notation 7 3 Concepts 8 3.1 Payment Addresses and Keys . .8 3.2 Notes...........................................................9 3.2.1 Note Plaintexts and Memo Fields . .9 3.3 The Block Chain . 10 3.4 Transactions and Treestates . 10 3.5 JoinSplit Transfers and Descriptions . 11 3.6 Note Commitment Trees . 11 3.7 Nullier Sets . 12 3.8 Block Subsidy and Founders’ Reward . 12 3.9 Coinbase Transactions . 12 † Zerocoin Electric Coin Company 1 4 Abstract Protocol 12 4.1 Abstract Cryptographic Schemes . 12 4.1.1 Hash Functions . 12 4.1.2 Pseudo Random Functions . 13 4.1.3 Authenticated One-Time Symmetric Encryption . 13 4.1.4 Key Agreement . 13 4.1.5 Key Derivation . 14 4.1.6 Signature . 15 4.1.6.1 Signature with Re-Randomizable Keys . -
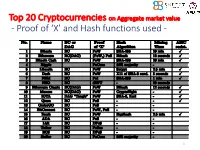
Proof of 'X' and Hash Functions Used
Top 20 Cryptocurrencies on Aggregate market value - Proof of ‘X’ and Hash functions used - 1 ISI Kolkata BlockChain Workshop, Nov 30th, 2017 CRYPTOGRAPHY with BlockChain - Hash Functions, Signatures and Anonymization - Hiroaki ANADA*1, Kouichi SAKURAI*2 *1: University of Nagasaki, *2: Kyushu University Acknowledgements: This work is supported by: Grants-in-Aid for Scientific Research of Japan Society for the Promotion of Science; Research Project Number: JP15H02711 Top 20 Cryptocurrencies on Aggregate market value - Proof of ‘X’ and Hash functions used - 3 Table of Contents 1. Cryptographic Primitives in Blockchains 2. Hash Functions a. Roles b. Various Hash functions used for Proof of ‘X’ 3. Signatures a. Standard Signatures (ECDSA) b. Ring Signatures c. One-Time Signatures (Winternitz) 4. Anonymization Techniques a. Mixing (CoinJoin) b. Zero-Knowledge proofs (zk-SNARK) 5. Conclusion 4 Brief History of Proof of ‘X’ 1992: “Pricing via Processing or Combatting Junk Mail” Dwork, C. and Naor, M., CRYPTO ’92 Pricing Functions 2003: “Moderately Hard Functions: From Complexity to Spam Fighting” Naor, M., Foundations of Soft. Tech. and Theoretical Comp. Sci. 2008: “Bitcoin: A peer-to-peer electronic cash system” Nakamoto, S. Proof of Work 5 Brief History of Proof of ‘X’ 2008: “Bitcoin: A peer-to-peer electronic cash system” Nakamoto, S. Proof of Work 2012: “Peercoin” Proof of Stake (& Proof of Work) ~ : Delegated Proof of Stake, Proof of Storage, Proof of Importance, Proof of Reserves, Proof of Consensus, ... 6 Proofs of ‘X’ 1. Proof of Work 2. Proof of Stake Hash-based Proof of ‘X’ 3. Delegated Proof of Stake 4. Proof of Importance 5. -

Piecework: Generalized Outsourcing Control for Proofs of Work
(Short Paper): PieceWork: Generalized Outsourcing Control for Proofs of Work Philip Daian1, Ittay Eyal1, Ari Juels2, and Emin G¨unSirer1 1 Department of Computer Science, Cornell University, [email protected],[email protected],[email protected] 2 Jacobs Technion-Cornell Institute, Cornell Tech [email protected] Abstract. Most prominent cryptocurrencies utilize proof of work (PoW) to secure their operation, yet PoW suffers from two key undesirable prop- erties. First, the work done is generally wasted, not useful for anything but the gleaned security of the cryptocurrency. Second, PoW is natu- rally outsourceable, leading to inegalitarian concentration of power in the hands of few so-called pools that command large portions of the system's computation power. We introduce a general approach to constructing PoW called PieceWork that tackles both issues. In essence, PieceWork allows for a configurable fraction of PoW computation to be outsourced to workers. Its controlled outsourcing allows for reusing the work towards additional goals such as spam prevention and DoS mitigation, thereby reducing PoW waste. Meanwhile, PieceWork can be tuned to prevent excessive outsourcing. Doing so causes pool operation to be significantly more costly than today. This disincentivizes aggregation of work in mining pools. 1 Introduction Distributed cryptocurrencies such as Bitcoin [18] rely on the equivalence \com- putation = money." To generate a batch of coins, clients in a distributed cryp- tocurrency system perform an operation called mining. Mining requires solving a computationally intensive problem involving repeated cryptographic hashing. Such problem and its solution is called a Proof of Work (PoW) [11]. As currently designed, nearly all PoWs suffer from one of two drawbacks (or both, as in Bitcoin). -

Prospectus, Which Is in the Swedish-Language, and Which Was Approved by the Swedish Financial Supervisory Authority on 17 May 2019
NB: This English-language document is an unofficial translation of XBT Provider AB's base prospectus, which is in the Swedish-language, and which was approved by the Swedish Financial Supervisory Authority on 17 May 2019. In the case of any discrepancies between the base prospectus and this English translation, the Swedish-language base prospectus shall prevail. BASE PROSPECTUS Dated 17 May 2019 for the issuance of BITCOIN TRACKER CERTIFICATES, BITCOIN CASH TRACKER CERTIFICATES, ETHEREUM TRACKER CERTIFICATES, ETHEREUM CLASSIC TRACKER CERTIFICATES, LITECOIN TRACKER CERTIFICATES, XRP TRACKER CERTIFICATES, NEO TRACKER CERTIFICATES & BASKET CERTIFICATES under the Issuance programme of XBT Provider AB (publ) (a limited liability company incorporated under the laws of Sweden) The Certificates are guaranteed by CoinShares (Jersey) Limited ______________________________________ IMPORTANT INFORMATION This base prospectus (the "Base Prospectus") contains information relating to Certificates (as defined below) to be issued under the programme (the "Programme"). Under the Base Prospectus, XBT Provider AB (publ) (the "Issuer" or "XBT Provider") may, from time to time, issue Certificates and apply for such Certificates to be admitted to trading on one or more regulated markets or multilateral trading facilities ("MTF’s") in Finland, Germany, the Netherlands, Norway, Sweden, the United Kingdom or, subject to completion of relevant notification measures, any other Member State within the European Economic Area ("EEA"). The correct performance of the Issuer's payment obligations regarding the Certificates under the Programme are guaranteed by CoinShares (Jersey) Limited (the "Guarantor"). The Certificates are not principal-protected and do not bear interest. Consequently, the value of, and any amounts payable under, the Certificates will be strongly influenced by the performance of the Tracked Digital Currencies (as defined herein) and, unless the certificates are denominated in USD, the USD-SEK exchange rate or, as the case may be, the USD-EUR exchange rate.