Organizational Culture and Structure at Freebsd Nothing to Learn from Business Schools ;)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Institutionalizing Freebsd Isolated and Virtualized Hosts Using Bsdinstall(8), Zfs(8) and Nfsd(8)
Institutionalizing FreeBSD Isolated and Virtualized Hosts Using bsdinstall(8), zfs(8) and nfsd(8) [email protected] @MichaelDexter BSDCan 2018 Jails and bhyve… FreeBSD’s had Isolation since 2000 and Virtualization since 2014 Why are they still strangers? Institutionalizing FreeBSD Isolated and Virtualized Hosts Using bsdinstall(8), zfs(8) and nfsd(8) Integrating as first-class features Institutionalizing FreeBSD Isolated and Virtualized Hosts Using bsdinstall(8), zfs(8) and nfsd(8) This example but this is not FreeBSD-exclusive Institutionalizing FreeBSD Isolated and Virtualized Hosts Using bsdinstall(8), zfs(8) and nfsd(8) jail(8) and bhyve(8) “guests” Application Binary Interface vs. Instructions Set Architecture Institutionalizing FreeBSD Isolated and Virtualized Hosts Using bsdinstall(8), zfs(8) and nfsd(8) The FreeBSD installer The best file system/volume manager available The Network File System Broad Motivations Virtualization! Containers! Docker! Zones! Droplets! More more more! My Motivations 2003: Jails to mitigate “RPM Hell” 2011: “bhyve sounds interesting...” 2017: Mitigating Regression Hell 2018: OpenZFS EVERYWHERE A Tale of Two Regressions Listen up. Regression One FreeBSD Commit r324161 “MFV r323796: fix memory leak in [ZFS] g_bio zone introduced in r320452” Bug: r320452: June 28th, 2017 Fix: r324162: October 1st, 2017 3,710 Commits and 3 Months Later June 28th through October 1st BUT July 27th, FreeNAS MFC Slips into FreeNAS 11.1 Released December 13th Fixed in FreeNAS January 18th 3 Months in FreeBSD HEAD 36 Days -

Thread Scheduling in Multi-Core Operating Systems Redha Gouicem
Thread Scheduling in Multi-core Operating Systems Redha Gouicem To cite this version: Redha Gouicem. Thread Scheduling in Multi-core Operating Systems. Computer Science [cs]. Sor- bonne Université, 2020. English. tel-02977242 HAL Id: tel-02977242 https://hal.archives-ouvertes.fr/tel-02977242 Submitted on 24 Oct 2020 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Ph.D thesis in Computer Science Thread Scheduling in Multi-core Operating Systems How to Understand, Improve and Fix your Scheduler Redha GOUICEM Sorbonne Université Laboratoire d’Informatique de Paris 6 Inria Whisper Team PH.D.DEFENSE: 23 October 2020, Paris, France JURYMEMBERS: Mr. Pascal Felber, Full Professor, Université de Neuchâtel Reviewer Mr. Vivien Quéma, Full Professor, Grenoble INP (ENSIMAG) Reviewer Mr. Rachid Guerraoui, Full Professor, École Polytechnique Fédérale de Lausanne Examiner Ms. Karine Heydemann, Associate Professor, Sorbonne Université Examiner Mr. Etienne Rivière, Full Professor, University of Louvain Examiner Mr. Gilles Muller, Senior Research Scientist, Inria Advisor Mr. Julien Sopena, Associate Professor, Sorbonne Université Advisor ABSTRACT In this thesis, we address the problem of schedulers for multi-core architectures from several perspectives: design (simplicity and correct- ness), performance improvement and the development of application- specific schedulers. -
Full Disk Encryption
Full Disk Encryption David Klaftenegger Department of Information Technology Uppsala University, Sweden 22. March 2019 Caveat Auditor Background Software LUKS this talk contains opinions Questions my opinions not the university’s nor do I claim to be an expert ... so expect some imprecision and errors 22 Mar 2019 Full Disk Encryption - Cryptoparty - 2 - David K My choices loss / theft broken device selling device singular access by evil maid important to you (that I can’t see it) protect in case of • device loss? • theft? • police? • nation state attackers? What’s the problem? Why encrypt data? Background Software LUKS Questions 22 Mar 2019 Full Disk Encryption - Cryptoparty - 3 - David K My choices loss / theft broken device selling device singular access by evil maid (that I can’t see it) protect in case of • device loss? • theft? • police? • nation state attackers? What’s the problem? Why encrypt data? Background important to you Software LUKS Questions 22 Mar 2019 Full Disk Encryption - Cryptoparty - 3 - David K My choices loss / theft broken device selling device singular access by evil maid protect in case of • device loss? • theft? • police? • nation state attackers? What’s the problem? Why encrypt data? Background important to you (that I can’t see it) Software LUKS Questions 22 Mar 2019 Full Disk Encryption - Cryptoparty - 3 - David K My choices loss / theft broken device selling device singular access by evil maid What’s the problem? Why encrypt data? Background important to you (that I can’t see it) Software protect in case -
Building a Virtualisation Appliance with Freebsd/Bhyve/Openzfs Jason Tubnor ICT Senior Security Lead Introduction
Building a virtualisation appliance with FreeBSD/bhyve/OpenZFS Jason Tubnor ICT Senior Security Lead Introduction Building an virtualisation appliance for use within a NGO/NFP Australian Health Sector About Me Latrobe Community Health Service (LCHS) Background Problem Concept Production Reiteration About Me 26 years of IT experience Introduced to Open Source in the mid 90’s Discovered OpenBSD in 2000 A user and advocate of OpenBSD and FreeBSD Life outside of computers: Ultra endurance gravel cycling Latrobe Community Health Service (LCHS) Originally a Gippsland based NFP/NGO health service ICT manages 900+ users Servicing 51 sites across Victoria, Australia Covering ~230,000km2 Roughly the size of Laos in Aisa or Minnesota in USA “Better health, Better lifestyles, Stronger communities” Background First half of 2016 awarded contract to provide NDIS services Mid 2016 – deployment of initial infrastructure MPLS connection L3 switch gear ESXi host running a Windows Server 2016 for printing services Background – cont. Staff number grew We hit capacity constraints on the managed MPLS network An offloading guest was added to the ESXi host VPN traffic could be offloaded from the main network Using cheaply available ISP internet connection Problem Taking stock of the lessons learned in the first phase We needed to come up with a reproducible device Device required to be durable in harsh conditions Budget constraints/cost savings Licensing model Phase 2 was already being negotiated so a solution was required quickly Concept bhyve [FreeBSD] was working extremely well in testing Excellent hardware support Liberally licensed OpenZFS Simplistic Small footprint for a type 2 hypervisor Hardware discovery phase FreeBSD Required virtualisation components in CPU Concept – cont. -

Bhyve - Improvements to Virtual Machine State Save and Restore
bhyve - Improvements to Virtual Machine State Save and Restore Darius Mihai Mihai Carabas, University POLITEHNICA of Bucharest University POLITEHNICA of Bucharest Splaiul Independent, ei 313, Bucharest, Romania, 060042 Splaiul Independent, ei 313, Bucharest, Romania, 060042 Email: [email protected] Email: [email protected] Abstract—As more complex tasks are delegated to distributed Regardless of their exact function, a periodic task is a routine servers, virtual machine hypervisors need to adapt and provide that will have to be called at (or as close as possible) a set features that allow redundancy and load balancing. One such interval. mechanism is the virtual machine save and restore through sys- sleep tem snapshots. A snapshot should allow the complete restoration For example, the basic Unix command can be used of the state that the virtual machine was in when the snapshot to perform an operation every N seconds if sleep $N is was created. Since the snapshot should encapsulate the entire called in a script loop. Since it is safe to assume that all state of the virtualized system, the guest system should not be modern processors have hardware timekeeping components able to differentiate between the moment a snapshot was created implemented, sleep will request from the operating system and the moment when the system was restored, regardless of how much real time has passed between the two events. This that a software timer (i.e., one that is implemented by the paper will present how the time management and block devices operating system as an abstraction [1]) to be set for N are saved and restored for bhyve, FreeBSD’s virtual machine seconds in the future and will yield the processor, without hypervisor. -

In PDF Format
Arranging Your Virtual Network on FreeBSD Michael Gmelin ([email protected]) January 2020 1 CONTENTS CONTENTS Contents Introduction 3 Document Conventions . .3 License . .3 Plain Jails 4 Plain Jails Using Inherited IP Configuration . .4 Plain Jails Using a Dedicated IP Address . .5 Plain Jails Using a VLAN IP Address . .6 Plain Jails Using a Loopback IP Address . .7 Adding Outbound NAT for Public Traffic . .7 Running a Service and Redirecting Traffic to It . .9 VNET Jails and bhyve VMs 10 VNET Jails Using sysutils/pot ............................. 10 VNET Jails Using sysutils/iocage ............................ 13 Managing Bridges . 13 Adding bhyve VMs and DHCP to the Mix . 16 Preventing Traffic Between VNET Jails/VMs . 17 Firewalling Inside VNET Jails/VMs . 20 VXLAN 22 VXLAN Example Overview . 22 Gateway Configuration . 24 Jailhost-a . 25 Network Configuration (jailhost-a) . 25 VM Configuration (jailhost-a) . 26 Jail Configuration (jailhost-a) . 27 Jailhost-b . 27 Network Configuration (jailhost-b) . 27 Plain Jail Configuration (jailhost-b) . 28 Network Switch Setup (jailhost-b) . 29 VNET Jail Configuration (jailhost-b) . 30 VM Configuration (jailhost-b) . 30 VXLAN Multicast Troubleshooting . 31 Conclusion and Further Reading 33 2020-01-08 (final) 2 CC BY 4.0 INTRODUCTION Introduction Modern FreeBSD offers a range of virtualization options, from the traditional jail environment sharing the network stack with the host operating system, over vnet jails, which allow each jail to have its own network stack, to bhyve virtual machines running their own kernels/operating systems. Depending on individual requirements, there are different ways to configure the virtual network. Jail and VM management tools can ease the process by abstracting away (at least some of) the underlying complexities. -

Freebsd Enterprise Storage Polish BSD User Group Welcome 2020/02/11 Freebsd Enterprise Storage
FreeBSD Enterprise Storage Polish BSD User Group Welcome 2020/02/11 FreeBSD Enterprise Storage Sławomir Wojciech Wojtczak [email protected] vermaden.wordpress.com twitter.com/vermaden bsd.network/@vermaden https://is.gd/bsdstg FreeBSD Enterprise Storage Polish BSD User Group What is !nterprise" 2020/02/11 What is Enterprise Storage? The wikipedia.org/wiki/enterprise_storage page tells nothing about enterprise. Actually just redirects to wikipedia.org/wiki/data_storage page. The other wikipedia.org/wiki/computer_data_storage page also does the same. The wikipedia.org/wiki/enterprise is just meta page with lin s. FreeBSD Enterprise Storage Polish BSD User Group What is !nterprise" 2020/02/11 Common Charasteristics o Enterprise Storage ● Category that includes ser$ices/products designed &or !arge organizations. ● Can handle !arge "o!umes o data and !arge num%ers o sim#!tano#s users. ● 'n$olves centra!ized storage repositories such as SA( or NAS de$ices. ● )equires more time and experience%expertise to set up and operate. ● Generally costs more than consumer or small business storage de$ices. ● Generally o&&ers higher re!ia%i!it'%a"aila%i!it'%sca!a%i!it'. FreeBSD Enterprise Storage Polish BSD User Group What is !nterprise" 2020/02/11 EnterpriCe or EnterpriSe? DuckDuckGo does not pro$ide search results count +, Goog!e search &or enterprice word gi$es ~ 1 )00 000 results. Goog!e search &or enterprise word gi$es ~ 1 000 000 000 results ,1000 times more). ● /ost dictionaries &or enterprice word sends you to enterprise term. ● Given the *+,CE o& many enterprise solutions it could be enterPRICE 0 ● 0 or enterpri$e as well +. -
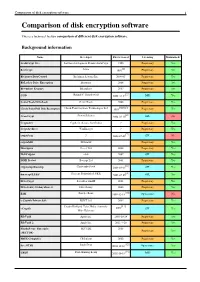
Comparison of Disk Encryption Software 1 Comparison of Disk Encryption Software
Comparison of disk encryption software 1 Comparison of disk encryption software This is a technical feature comparison of different disk encryption software. Background information Name Developer First released Licensing Maintained? ArchiCrypt Live Softwaredevelopment Remus ArchiCrypt 1998 Proprietary Yes [1] BestCrypt Jetico 1993 Proprietary Yes BitArmor DataControl BitArmor Systems Inc. 2008-05 Proprietary Yes BitLocker Drive Encryption Microsoft 2006 Proprietary Yes Bloombase Keyparc Bloombase 2007 Proprietary Yes [2] CGD Roland C. Dowdeswell 2002-10-04 BSD Yes CenterTools DriveLock CenterTools 2008 Proprietary Yes [3][4][5] Check Point Full Disk Encryption Check Point Software Technologies Ltd 1999 Proprietary Yes [6] CrossCrypt Steven Scherrer 2004-02-10 GPL No Cryptainer Cypherix (Secure-Soft India) ? Proprietary Yes CryptArchiver WinEncrypt ? Proprietary Yes [7] cryptoloop ? 2003-07-02 GPL No cryptoMill SEAhawk Proprietary Yes Discryptor Cosect Ltd. 2008 Proprietary Yes DiskCryptor ntldr 2007 GPL Yes DISK Protect Becrypt Ltd 2001 Proprietary Yes [8] cryptsetup/dmsetup Christophe Saout 2004-03-11 GPL Yes [9] dm-crypt/LUKS Clemens Fruhwirth (LUKS) 2005-02-05 GPL Yes DriveCrypt SecurStar GmbH 2001 Proprietary Yes DriveSentry GoAnywhere 2 DriveSentry 2008 Proprietary Yes [10] E4M Paul Le Roux 1998-12-18 Open source No e-Capsule Private Safe EISST Ltd. 2005 Proprietary Yes Dustin Kirkland, Tyler Hicks, (formerly [11] eCryptfs 2005 GPL Yes Mike Halcrow) FileVault Apple Inc. 2003-10-24 Proprietary Yes FileVault 2 Apple Inc. 2011-7-20 Proprietary -

Curs 8 Virtualizare Nativ˘A
Curs 8 Virtualizare nativ˘a Servicii avansate pentru ISP 24 aprilie 2017 SAISP Curs 8, Virtualizare nativ˘a 1/37 Outline Introducere KVM KVM s, i libvirt Concluzii ^Intreb˘ari SAISP Curs 8, Virtualizare nativ˘a 2/37 Virtualizare I abstractizarea resurselor unui sistem de calcul I memorie virtual˘a I mas, ini virtuale I emulare I virtualizarea stoc˘arii I system virtual machine I process virtual machine SAISP Curs 8, Virtualizare nativ˘a 3/37 I paravirtualizare (paravirtualization) I virtualizare la nivelul sistemului de operare (operating-system level virtualization) I Cu ce difer˘avirtualizarea de emulare? I la virtualizare, cea mai mare parte a instruct, iunilor se execut˘a pe sistemul fizic I se poate emula o arhitectur˘adiferit˘ade arhitectura sistemului fizic I hypervisor I hosted virtualization (type 2 hypervisor) I bare metal virtualization (type 1 hypervisor) Tipuri de virtualizare I virtualizare complet˘a(full-virtualization) I virtualizare asistat˘ahardware (hardware-assisted virtualization) SAISP Curs 8, Virtualizare nativ˘a 4/37 I virtualizare la nivelul sistemului de operare (operating-system level virtualization) I Cu ce difer˘avirtualizarea de emulare? I la virtualizare, cea mai mare parte a instruct, iunilor se execut˘a pe sistemul fizic I se poate emula o arhitectur˘adiferit˘ade arhitectura sistemului fizic I hypervisor I hosted virtualization (type 2 hypervisor) I bare metal virtualization (type 1 hypervisor) Tipuri de virtualizare I virtualizare complet˘a(full-virtualization) I virtualizare asistat˘ahardware (hardware-assisted -
Seven Ways to Increase Security in a New Freebsd Installation by MARIUSZ ZABORSKI
1 of 6 Seven Ways to Increase Security in a New FreeBSD Installation BY MARIUSZ ZABORSKI FreeBSD can be used as a desktop or as a server operating system. When setting up new boxes, it is crucial to choose the most secure configuration. We have a lot of data on our computers, and it all needs to be protected. This article describes seven configuration improvements that everyone should remember when configur- ing a new FreeBSD box. Full Disk Encryption With a fresh installation, it is important to decide about hard drive encryption—par- 1ticularly since it may be challenging to add later. The purpose of disk encryption is to protect data stored on the system. We store a lot of personal and business data on our com- puters, and most of the time, we do not want that to be read by unauthorized people. Our laptop may be stolen, and if so, it should be assumed that a thief might gain access to almost every document, photo, and all pages logged in to through our web browser. Some people may also try to tamper with or read our data when we are far away from our computer. We recommend encrypting all systems—especially servers or personal computers. Encryp- tion of hard disks is relatively inexpensive and the advantages are significant. In FreeBSD, there are three main ways to encrypt storage: • GBDE, • ZFS native encryption, • GELI. Geom Based Disk Encryption (GBDE) is the oldest disk encryption mechanism in FreeBSD. But the GBDE is currently neglected by developers. GDBE supports only AES-CBC with a 128-bit key length and uses a separate key for each write, which may introduce some CPU overhead. -

Open-Source-Lösungen Zur Wahrung Der Datensicherheit Und
Fachhochschule Hannover Fakult¨at IV - Wirtschaft und Informatik Studiengang Angewandte Informatik MASTERARBEIT Open-Source-L¨osungen zur Wahrung der Datensicherheit und glaubhaften Abstreitbarkeit in typischen Notebook-Szenarien Jussi Salzwedel September 2009 Beteiligte Erstprufer¨ Prof. Dr. rer. nat. Josef von Helden Fachhochschule Hannover Ricklinger Stadtweg 120 30459 Hannover E-Mail: [email protected] Telefon: 05 11 / 92 96 - 15 00 Zweitprufer¨ Prof. Dr. rer. nat. Carsten Kleiner Fachhochschule Hannover Ricklinger Stadtweg 120 30459 Hannover E-Mail: [email protected] Telefon: 05 11 / 92 96 - 18 35 Autor Jussi Salzwedel E-Mail: [email protected] 2 Erkl¨arung Hiermit erkl¨are ich, dass ich die eingereichte Masterarbeit selbst¨andig und ohne fremde Hilfe verfasst, andere als die von mir angegebenen Quellen und Hilfsmittel nicht benutzt und die den benutzten Werken w¨ortlich oder inhaltlich entnommenen Stellen als solche kenntlich gemacht habe. Ort, Datum Unterschrift 3 Inhaltsverzeichnis 1 Einfuhrung¨ 14 1.1 Einleitung................................... 14 1.2 Motivation................................... 15 1.3 Typografische Konventionen......................... 18 1.4 Abgrenzung.................................. 18 2 Anwendungsf¨alle 20 2.1 A1: Notebook kommt abhanden....................... 20 2.2 A2: Notebook kommt abhanden und wird nach Verlust gefunden..... 21 2.3 A3: Benutzen des Notebooks, ohne sensitive Daten preiszugeben..... 22 3 Sicherheitsanforderungen 23 3.1 S0: Open-Source............................... 24 3.2 S1: Gew¨ahrleistung der Vertraulichkeit................... 24 3.3 S2: Uberpr¨ ufbarkeit¨ der Integrit¨at...................... 24 3.4 S3: Glaubhafte Abstreitbarkeit........................ 25 4 Theoretische Grundlagen 26 4.1 Verschlusselungsverfahren¨ .......................... 26 4.1.1 Advanced Encryption Standard................... 27 4.1.2 Blowfish................................ 28 4.1.3 Camellia................................ 28 4.1.4 CAST5............................... -

An Overview of Security in the Freebsd Kernel 131 Dr
AsiaBSDCon 2014 Proceedings March 13-16, 2014 Tokyo, Japan Copyright c 2014 BSD Research. All rights reserved. Unauthorized republication is prohibited. Published in Japan, March 2014 INDEX P1A: Bold, fast optimizing linker for BSD — Luba Tang P1B: Visualizing Unix: Graphing bhyve, ZFS and PF with Graphite 007 Michael Dexter P2A: LLVM in the FreeBSD Toolchain 013 David Chisnall P2B: NPF - progress and perspective 021 Mindaugas Rasiukevicius K1: OpenZFS: a Community of Open Source ZFS Developers 027 Matthew Ahrens K2: Bambi Meets Godzilla: They Elope 033 Eric Allman P3A: Snapshots, Replication, and Boot-Environments—How new ZFS utilities are changing FreeBSD & PC-BSD 045 Kris Moore P3B: Netmap as a core networking technology 055 Luigi Rizzo, Giuseppe Lettieri, and Michio Honda P4A: ZFS for the Masses: Management Tools Provided by the PC-BSD and FreeNAS Projects 065 Dru Lavigne P4B: OpenBGPD turns 10 years - Design, Implementation, Lessons learned 077 Henning Brauer P5A: Introduction to FreeNAS development 083 John Hixson P5B: VXLAN and Cloud-based networking with OpenBSD 091 Reyk Floeter INDEX P6A: Nested Paging in bhyve 097 Neel Natu and Peter Grehan P6B: Developing CPE Routers based on NetBSD: Fifteen Years of SEIL 107 Masanobu SAITOH and Hiroki SUENAGA P7A: Deploying FreeBSD systems with Foreman and mfsBSD 115 Martin Matuška P7B: Implementation and Modification for CPE Routers: Filter Rule Optimization, IPsec Interface and Ethernet Switch 119 Masanobu SAITOH and Hiroki SUENAGA K3: Modifying the FreeBSD kernel Netflix streaming servers — Scott Long K4: An Overview of Security in the FreeBSD Kernel 131 Dr. Marshall Kirk McKusick P8A: Transparent Superpages for FreeBSD on ARM 151 Zbigniew Bodek P8B: Carve your NetBSD 165 Pierre Pronchery and Guillaume Lasmayous P9A: How FreeBSD Boots: a soft-core MIPS perspective 179 Brooks Davis, Robert Norton, Jonathan Woodruff, and Robert N.