Guide to Industrial Control Systems (ICS) Security
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Systems Security Engineering Considerations for a Multidisciplinary Approach in the Engineering of Trustworthy Secure Systems
NIST Special Publication 800-160 VOLUME 1 Systems Security Engineering Considerations for a Multidisciplinary Approach in the Engineering of Trustworthy Secure Systems RON ROSS MICHAEL McEVILLEY JANET CARRIER OREN This publication contains systems security engineering considerations for ISO/IEC/IEEE 15288:2015, Systems and software engineering — System life cycle processes. It provides security-related implementation guidance for the standard and should be used in conjunction with and as a complement to the standard. This publication is available free of charge from: https://doi.org/10.6028/NIST.SP.800-160v1 NIST Special Publication 800-160 VOLUME 1 Systems Security Engineering Considerations for a Multidisciplinary Approach in the Engineering of Trustworthy Secure Systems RON ROSS Computer Security Division National Institute of Standards and Technology MICHAEL McEVILLEY The MITRE Corporation JANET CARRIER OREN Legg Mason This publication is available free of charge from: https://doi.org/10.6028/NIST.SP.800-160v1 November 2016 INCLUDES UPDATES AS OF 03-21-2018: PAGE XIII U.S. Department of Commerce Penny Pritzker, Secretary National Institute of Standards and Technology Willie May, Under Secretary of Commerce for Standards and Technology and Director SPECIAL PUBLICATION 800-160, VOLUME 1 SYSTEMS SECURITY ENGINEERING A Multidisciplinary Approach in the Engineering of Trustworthy Secure Systems ________________________________________________________________________________________________ Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act (FISMA) of 2014, 44 U.S.C. § 3551 et seq., Public Law (P.L.) 113-283. NIST is responsible for developing information security standards and guidelines, including minimum requirements for federal information systems, but such standards and guidelines shall not apply to national security systems without the express approval of appropriate federal officials exercising policy authority over such systems. -

Practicing a Science of Security a Philosophy of Science Perspective
Practicing a Science of Security A Philosophy of Science Perspective Jonathan M. Spring Tyler Moore David Pym University College London The University of Tulsa University College London Gower Street 800 South Tucker Drive London WC1E 6BT London WC1E 6BT Tulsa, OK 74104-9700 Alan Turing Institute [email protected] [email protected] [email protected] ABSTRACT Experiments Structured observations of the empirical are untenable world Our goal is to refocus the question about cybersecurity re- Reproducibility Evaluate by repetition, replication, varia- search from ‘is this process scientific’ to ‘why is this scientific is impossible tion, reproduction, and/or corroboration process producing unsatisfactory results’. We focus on five No laws of common complaints that claim cybersecurity is not or can- Mechanistic explanation of phenomena nature not be scientific. Many of these complaints presume views to make nature intelligible No single associated with the philosophical school known as Logical Em- Specialization necessitates translation ontology piricism that more recent scholarship has largely modified or rejected. Modern philosophy of science, supported by mathe- ‘Just’ Both science and engineering are neces- matical modeling methods, provides constructive resources engineering sary to mitigate all purported challenges to a science of security. Table 1: Five common complaints raised by the science of cy- Therefore, we argue the community currently practices a bersecurity community and positive reframing from the phi- science of cybersecurity. A philosophy of science perspective losophy of science literature. suggests the following form of practice: structured observa- tion to seek intelligible explanations of phenomena, evaluating explanations in many ways, with specialized fields (including engineering and forensics) constraining explanations within Its proponents claim a science of security is needed for ongo- their own expertise, inter-translating where necessary. -

A Cybersecurity Testbed for Industrial Control Systems
A Cybersecurity Testbed for Industrial Control Systems R. Candell, D.M. Anand, and K. Stouffer National Institute of Standards and Technology, Gaithersburg MD, U.S.A [rick.candell, dhananjay.anand, keith.stouffer]@nist.gov Abstract — The National Institute of Standards and Technology (NIST) is developing a cybersecurity testbed for industrial control systems (ICS). The goal of this testbed is to measure the performance of an ICS when instrumented with cybersecurity protections in accordance with practices prescribed by prevailing standards and guidelines. This paper outlines the testbed design and lists research goals, use cases, and performance metrics currently being considered. The paper is also intended to initiate discussion between control and security practitioners – two groups that have had little interaction in the past. Research outcomes from the testbed will highlight specific cases where security technologies impact control performance, as well as motivate methods by which control engineers can leverage security engineering to design control algorithms that extend safety and fault tolerance to include advanced persistent threats. Keywords — industrial control systems, robotics, chemical process control, cybersecurity, industrial security, process resilience, penetration testing, process performance, measurement science, testbed, robotics, robot control, safety, supervisory control and data acquisition (SCADA) I. Introduction Given the increasing interest in security of industrial control systems (ICS) and the evolving nature of advanced persistent threats against critical industrial infrastructure [1], the National Institute of Standards and Technology (NIST) has been actively involved in developing standards for cyber and control systems security via several standards bodies. Examples of such standards and guidelines include [2] and [3]. A research testbed, currently in development at NIST, will provide a platform on which to apply cybersecurity strategies to use cases that are practically relevant to industry. -
Cyber Security Engineering, Bs
2016-2017 Volgenau School of Engineering CYBER SECURITY ENGINEERING, B.S. 2016 - 2017 Cyber Security Engineering is concerned with the development of cyber resilient systems which include the protection of the physical as well as computer and network systems. It requires a proactive approach in engineering design of physical systems with cyber security incorporated from the beginning of system development. Cyber security engineering is an important quantitative methodology to be used in all industries to include, but not limited to, transportation, energy, healthcare, infrastructure, finance, government (federal, state, and local), and defense. The program is focused on the cyber security engineering of integrated cyber-physical systems. This degree provides a foundation in cyber security engineering, and is most appropriate for students with a strong mathematics and science background. The program is administered by the Dean's Office, Volgenau School of Engineering. Cyber security engineers are part of integrated design and development teams for physical systems that require embedded cyber security design, working with engineers from other disciplines (e.g. civil, mechanical, electrical, systems engineers as well as computer scientists and software engineers). Cyber security engineers are engineers who know technology, but who also have in-depth exposure to the application/domain area. Not only do they provide technological solutions to cyber security problems of engineering systems posed by others, but by having an understanding of the application/domain, they can formulate potential security threats, propose appropriate solutions, and then provide leadership in the design of a system to resist and survive these threats. Because of their interdisciplinary training, cyber security engineers are expected to play an increasing role in attacking some of the most pressing current cyber security issues in the country. -

BEST PRACTICES for UTILITY CYBERSECURITY Prepared by Doug Morrill, Associate Director and Sam Crawford, Phd, Managing Consultant, Navigant Consulting, Inc
ENERGY BEST PRACTICES FOR UTILITY CYBERSECURITY Prepared by Doug Morrill, Associate Director and Sam Crawford, PhD, Managing Consultant, Navigant Consulting, Inc. May 2017 GENERAL DISCLAIMER: This presentation was prepared by Navigant Consulting, Inc. (Navigant) for informational purposes only. The term “best practices” is used to reference practices which the authors currently believe to be generally accepted and recommended practices, and the views expressed in this paper are those of the authors and do not necessarily represent the views of Navigant. Further, Navigant does not make any express or implied warranty or representation concerning the information contained in this presentation, or as to merchantability or fitness for a particular purpose or function. The intended audience for this guide includes network engineers, cybersecurity professionals, cybersecurity program managers and others that are interested in a general overview and comment on the highlights of cybersecurity for the utility industry. It assumes a reasonable level of general network architecture and administration as well as basic understanding of the major components of electric utility information and operations technology. The guide is not meant to be comprehensive or to be used as the foundation for a robust and complete cybersecurity program.1 1. This paper includes a high-level overview of best practices from various existing standards and includes Navigant’s unique, informed analysis and interpretation of the frameworks in the context of current security threats in the industry and future technologies. These standards include the North American Electrical Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) requirements, the National Institute of Standards and Technology (NIST), the International Organization for Standardization (ISO), the International Electrotechnical Commission (IEC), and others. -

Programmable Logic Controller
Revised 10/07/19 SPECIFICATIONS - DETAILED PROVISIONS Section 17010 - Programmable Logic Controller C O N T E N T S PART 1 - GENERAL ....................................................................................................................... 1 1.01 DESCRIPTION .............................................................................................................. 1 1.02 RELATED SECTIONS ...................................................................................................... 1 1.03 REFERENCE STANDARDS AND CODES ............................................................................ 2 1.04 DEFINITIONS ............................................................................................................... 2 1.05 SUBMITTALS ............................................................................................................... 3 1.06 DESIGN REQUIREMENTS .............................................................................................. 8 1.07 INSTALLED-SPARE REQUIREMENTS ............................................................................. 13 1.08 SPARE PARTS............................................................................................................. 13 1.09 MANUFACTURER SERVICES AND COORDINATION ........................................................ 14 1.10 QUALITY ASSURANCE................................................................................................. 15 PART 2 - PRODUCTS AND MATERIALS......................................................................................... -

Control Theory
Control theory S. Simrock DESY, Hamburg, Germany Abstract In engineering and mathematics, control theory deals with the behaviour of dynamical systems. The desired output of a system is called the reference. When one or more output variables of a system need to follow a certain ref- erence over time, a controller manipulates the inputs to a system to obtain the desired effect on the output of the system. Rapid advances in digital system technology have radically altered the control design options. It has become routinely practicable to design very complicated digital controllers and to carry out the extensive calculations required for their design. These advances in im- plementation and design capability can be obtained at low cost because of the widespread availability of inexpensive and powerful digital processing plat- forms and high-speed analog IO devices. 1 Introduction The emphasis of this tutorial on control theory is on the design of digital controls to achieve good dy- namic response and small errors while using signals that are sampled in time and quantized in amplitude. Both transform (classical control) and state-space (modern control) methods are described and applied to illustrative examples. The transform methods emphasized are the root-locus method of Evans and fre- quency response. The state-space methods developed are the technique of pole assignment augmented by an estimator (observer) and optimal quadratic-loss control. The optimal control problems use the steady-state constant gain solution. Other topics covered are system identification and non-linear control. System identification is a general term to describe mathematical tools and algorithms that build dynamical models from measured data. -

Overview of Distributed Control Systems Formalisms 253
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by DSpace at VSB Technical University of Ostrava Overview of distributed control systems formalisms 253 OVERVIEW OF DISTRIBUTED CONTROL SYSTEMS FORMALISMS P. Holeko Department of Control and Information Systems, Faculty of Electrical Engineering, University of Žilina Univerzitná 8216/1, SK 010 26, Žilina, Slovak republic, tel.: +421 41 513 3343, e-mail: [email protected] Summary This paper discusses a chosen set of mainly object-oriented formal and semiformal methods, methodics, environments and tools for specification, analysis, modeling, simulation, verification, development and synthesis of distributed control systems (DCS). 1. INTRODUCTION interconnected by a network for the purpose of communication and monitoring. Increasing demands on technical parameters, In the next section the problem of formalizing reliability, effectivity, safety and other the processes of DCS’s life-cycle will be discussed. characteristics of industrial control systems initiate distribution of its control components across the 3. FORMAL METHODS plant. The complexity requires involving of formal The main motivations of using formal concepts methods in the process of specification, analysis, are [9]: modeling, simulation, verification, development, and ° In the process of formalizing informal in the optimal case in synthesis of such systems. requirements, ambiguities, omissions and contradictions will often be discovered; 2. DISTRIBUTED CONTROL SYSTEM ° The formal model -
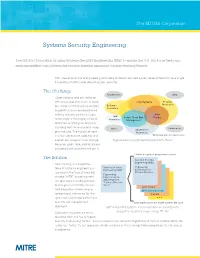
Systems Security Engineering Fact Sheet
The MITRE Corporation Systems Security Engineering The MITRE Corporation is using Systems Security Engineering (SSE) to ensure the U.S. Air Force fields and sustains resilient capabilities that provide mission assurance against evolving threats. SSE uses scientific and engineering principles to deliver assured system-level protection via a single, full-system/full life cycle view of system security. The Challenge Requirements DMS* Cyber attacks, and our ability to effectively deal with them, impact Cryptography Program our nation’s infrastructure, military Software Protection Assurance capabilities, and commercial and military industry partners. Cyber Anti- HW Supply Chain Risk Tamper technology is thoroughly embed- Assurance Management ded into everything we engineer, including both business and weap- Sustainment Other Information ons systems. The historical ways Assurance in which we acquire, operate, and *Diminishing Manufacturing Sources sustain our systems must change Typical security engineering approach: “As Is” because, given time, sophisticated and persistent attackers will get in. Holistic, integrated, program protection The Solution Systems Security Engineering (SSE) New thinking in the applica- tions of systems engineering is Systems Security Engineering Engineering (SSE) Instructions for required in the face of evolving CPI Identification Engineering threats. MITRE is working with Instructions for SSE Integrated our sponsors to address these Technical Process challenges in a holistic manner (SITP) Anti-Tamper that allows the -
DOE Cybersecurity Strategy and Implementation Plan to Improve the Cybersecurity and Resilience of the Department’S Networks and Systems
U.S. Department of Energy CYBERSECURITY STRATEGY 2018-2020 U.S. Department of Energy Cybersecurity Strategy 2018 - 2020 MESSAGE FROM THE DEPUTY SECRETARY Advancing cybersecurity is a core priority for the Department of Energy (DOE). Our Department is approaching the cybersecurity challenge as an enterprise effort, incorporating assets and capabilities from across our programs and National Laboratories. This DOE CybersecurityStrategy will focus attention on our critical cybersecurity mission of protecting our Federal systems and networks. This Strategy, in concert with the recently-published DOE Multiyear Plan for Energy Sector Cybersecurity, is a significant step toward achieving better coordination of key cyber operations across the Department. In my role as chair of the DOE Cyber Council, I have had the privilege of meeting and working with IT and cybersecurity policy and technical leaders across the Department to advance an enterprise-wide approach to cybersecurity. This Strategy and Implementation Plan reflects the outcome of our efforts and identifies the steps we will take to ensure that cyber resources are allocated across DOE as effectively as possible. It is a crucial roadmap for how to translate our cybersecurity priorities into action to protect the Department's most valuable assets. This plan lays out a number of specific things we must do - or continue to do - in order to ensure the enterprise wide success of our collective cybersecurity mission: • Sharing cyber threat data in near-real time, as well as mitigating those threats by expediting and elevating the analysis of that data using U.S. intelligence assets. • Developing common identity services to allow better collaboration and visibility. -
Common Cybersecurity Vulnerabilities in Industrial Control Systems
Common Cybersecurity Vulnerabilities in Industrial Control Systems May 2011 DISCLAIMER This report was prepared as an account of work sponsored by an agency of the U.S. Government. Neither the U.S. Government nor any agency thereof, nor any employee, makes any warranty, expressed or implied, or assumes any legal liability or responsibility for any third party’s use, or the results of such use, or any information, apparatus, product, or process disclosed in this publication, or represents that its use by such third party would not infringe privately owned rights. ACKNOWLEDGMENTS Trent Nelson, Project Manager, Idaho National Laboratory; May Chaffin, Cyber Researcher, Idaho National Laboratory iii iv EXECUTIVE SUMMARY The U.S. Department of Homeland Security (DHS) National Cyber Security Division’s Control Systems Security Program (CSSP) performs cybersecurity vendor assessments, ICS-CERT operations, and asset owner cybersecurity evaluations with the Cyber Security Evaluation Tool (CSET) evaluations for industrial control systems (ICS) to reduce risk and improve the security of ICS and its components used in critical infrastructures throughout the United States. ICS differs from other computer systems because of legacy-inherited cybersecurity weaknesses and the significance of the impact of potential exploitation to the U.S. In 2009,a report titled “Common Cyber Security Vulnerabilities Observed in DHS Industrial Control Systems Assessments” compiled common vulnerabilities identified during 15 security assessments of new ICS products and production ICS installations from 2004 through 2008. Three additional ICS product assessments were performed in 2009 and 2010. This newer, 2010 version is an update to the 2009 version and has been developed to proactively create greater awareness within the ICS community. -
Introduction to Feedback Control
ECE4510/5510: Feedback Control Systems. 1–1 INTRODUCTION TO FEEDBACK CONTROL 1.1: What is feedback control? I Control-system engineers often face this question (or, “What is it that you do, anyway?”) when trying to explain their professional field. I Loosely speaking, control is the process of getting “something” to do what you want it to do (or “not do,” as the case may be). The “something” can be almost anything. Some obvious • examples: aircraft, spacecraft, cars, machines, robots, radars, telescopes, etc. Some less obvious examples: energy systems, the economy, • biological systems, the human body. I Control is a very common concept. e.g.,Human-machineinteraction:Drivingacar. ® Manual control. e.g.,Independentmachine:Roomtemperaturecontrol.Furnacein winter, air conditioner in summer. Both controlled (turned “on”/“off”) by thermostat. (We’ll look at this example more in Topic 1.2.) ® Automatic control (our focus in this course). DEFINITION: Control is the process of causing a system variable to conform to some desired value, called a reference value. (e.g., variable temperature for a climate-control system) = Lecture notes prepared by and copyright c 1998–2013, Gregory L. Plett and M. Scott Trimboli ! ECE4510/ECE5510, INTRODUCTION TO FEEDBACK CONTROL 1–2 tp Mp I Usually defined in terms 1 0.9 of the system’s step re- sponse, as we’ll see in notes Chapter 3. 0.1 t tr ts DEFINITION: Feedback is the process of measuring the controlled variable (e.g.,temperature)andusingthatinformationtoinfluencethe value of the controlled variable. I Feedback is not necessary for control. But, it is necessary to cater for system uncertainty, which is the principal role of feedback.