Software© 2015
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Schon Mal Dran Gedacht,Linux Auszuprobieren? Von G. Schmidt
Schon mal dran gedacht, Linux auszuprobieren? Eine Einführung in das Betriebssystem Linux und seine Distributionen von Günther Schmidt-Falck Das Magazin AUSWEGE wird nun schon seit 2010 mit Hilfe des Computer-Betriebs- system Linux erstellt: Texte layouten, Grafiken und Fotos bearbeiten, Webseiten ge- stalten, Audio schneiden - alles mit freier, unabhängiger Software einer weltweiten Entwicklergemeinde. Aufgrund der guten eigenen Erfahrungen möchte der folgende Aufsatz ins Betriebssystem Linux einführen - mit einem Schwerpunkt auf der Distri- bution LinuxMint. Was ist Linux? „... ein hochstabiles, besonders schnelles und vor allem funktionsfähiges Betriebssystem, das dem Unix-System ähnelt, … . Eine Gemeinschaft Tausender programmierte es und verteilt es nun unter der GNU General Public Li- cense. Somit ist es frei zugänglich für jeden und kos- tenlos! Mehrere Millionen Leute, viele Organisatio- nen und besonders Firmen nutzen es weltweit. Die meisten nutzen es aus folgenden Gründen: • besonders schnell, stabil und leistungs- stark • gratis Support aus vielen Internet- Newsgruppen Tux, der Pinguin, ist das Linux-Maskottchen • übersichtliche Mailing-Listen • massenweise www-Seiten • direkter Mailkontakt mit dem Programmierer sind möglich • Bildung von Gruppen • kommerzieller Support“1 Linux ist heute weit verbreitet im Serverbereich: „Im Oktober 2012 wurden mindes- tens 32% aller Webseiten auf einem Linux-Server gehostet. Da nicht alle Linux-Ser- ver sich auch als solche zu erkennen geben, könnte der tatsächliche Anteil um bis zu 24% höher liegen. Damit wäre ein tatsächlicher Marktanteil von bis zu 55% nicht 1 http://www.linuxnetworx.com/linux-richtig-nutzen magazin-auswege.de – 2.11.2015 Schon mal dran gedacht, Linux auszuprobieren? 1 auszuschliessen. (…) Linux gilt innerhalb von Netzwerken als ausgesprochen sicher und an die jeweiligen Gegebenheiten anpassbar. -

Forescout Counteract® Endpoint Support Compatibility Matrix Updated: October 2018
ForeScout CounterACT® Endpoint Support Compatibility Matrix Updated: October 2018 ForeScout CounterACT Endpoint Support Compatibility Matrix 2 Table of Contents About Endpoint Support Compatibility ......................................................... 3 Operating Systems ....................................................................................... 3 Microsoft Windows (32 & 64 BIT Versions) ...................................................... 3 MAC OS X / MACOS ...................................................................................... 5 Linux .......................................................................................................... 6 Web Browsers .............................................................................................. 8 Microsoft Windows Applications ...................................................................... 9 Antivirus ................................................................................................. 9 Peer-to-Peer .......................................................................................... 25 Instant Messaging .................................................................................. 31 Anti-Spyware ......................................................................................... 34 Personal Firewall .................................................................................... 36 Hard Drive Encryption ............................................................................. 38 Cloud Sync ........................................................................................... -

Development of Cloud-Based Media Player Using Microsoft Azure Services
eISSN:2600-7920 INTI JOURNAL Vol.1, 2018 (24) Development of Cloud-Based Media Player using Microsoft Azure Services Chong Fong Kim1, Chan Yong Kai 2 and Deshinta Arrova Dewi3 1,2,3 Faculty of Information Technology and Science, INTI International University, Nilai, Negeri Sembilan, Malaysia. Corresponding Author: [email protected] Abstract Playing songs offline consumes internal storage capacity of a device. Besides, playing songs, most of the time is an individual acting as a hobby and many song listeners do not have a common platform to share their hobby with others. By putting it on the cloud, the internal storage capacity can be reduced and the chance to share the common hobby with others is available. This paper aims to present the development of a Cloud-Based Media Player (CBMP) to ease the users in managing their song files and sharing with others. The CBMP utilizes a website as the main controller and connects to the Microsoft Azure Services to host the music database. Two separate sections are created for the user to upload and download their songs as private and share sections. Accordingly, users can choose the favored section they want to access. Not only features to upload and download songs are provided, but the CMBP also provides a search function that enables users to search songs in both different to make a search process faster. Due to latency in the cloud services, the suggested song format for CMBP is.MP3 files. The .MP3 files promote better compression rate than .MP4. Besides, .MP4 has higher latency that makes users waiting longer for processing the songs. -

Mercy College Student Handbook Each Year and on the College’S Intranet
STUDENT HANDBOOK 2020-2021 w w TABLE OF CONTENTS MERCY COLLEGE Soliciting or Commercial Activity .................................... 22 A Message from the President .......................................... 2 Mercy College Policies .................................................... 22 History ............................................................................... 3 Code of Student Conduct ............................................... 23 Objectives .......................................................................... 3 Code of Conduct for Residential Life Students ............... 25 Accreditations.................................................................... 4 Residential Area Guest Policy ......................................... 27 Disclaimer .......................................................................... 4 Quiet Hours Policy .......................................................... 28 General Standards of Conduct .......................................... 5 Inspections ...................................................................... 28 Notice of Non-Discrimination ............................................ 5 Fire Safety ....................................................................... 28 Sanctions for Code of Conduct Violations ...................... 29 ACADEMIC SUPPORT AND OTHER COLLEGE SERVICES Student Judicial Process ................................................. 31 Academic Advising ............................................................. 6 Division of Student Affairs ................................................ -

DVD Menus with Dvdstyler
Full Circle THE INDEPENDENT MAGAZINE FOR THE UBUNTU LINUX COMMUNITY ISSUE #74 - June 2013 ) ) m m o o c c . r r k k c c i i l l F F ( ( s s a a i i B B a a e e r r A A y y a a B B e e h h T T : : o o t t o o h h P P SSOOFFTTWWAARREE SSHHOOWWDDOOWWNN PDF VIEWERS: EVINCE vs OKULAR full circle magazine #74 1 Full Ciircle Magaziine iis neiither affiiliiated wiith,, nor endorsed by,, Canoniical Ltd.. contents ^ HowTo Full Circle Opinions THE INDEPENDENT MAGAZINE FOR THE UBUNTU LINUX COMMUNITY My Story p.31 Gpodder p.08 Columns LibreOffice p.11 Command & Conquer p.06 Ubuntu News p.04 My Story p.33 Connect To IPV6 p.14 Ask The New Guy p.26 Ubuntu Games p.47 Review p.34 Blender p.18 Linux Labs p.29 Q&A p.42 Software Showdown p.36 Inkscape p.21 Linux Certified p.48 Ubuntu Women p.45 Letters p.39 Graphics The articles contained in this magazine are released under the Creative Commons Attribution-Share Alike 3.0 Unported license. This means you can adapt, copy, distribute and transmit the articles but only under the following conditions: you must attribute the work to the original author in some way (at least a name, email or URL) and to this magazine by name ('Full Circle Magazine') and the URL www.fullcirclemagazine.org (but not attribute the article(s) in any way that suggests that they endorse you or your use of the work). -

Internet Evidence Finder Report
Patrick Leahy Center for Digital Investigation (LCDI) Internet Evidence Finder Report Written and Researched by Nick Murray 175 Lakeside Ave, Room 300A Phone: 802/865-5744 Fax: 802/865-6446 http://www.lcdi.champlin.edu July 2013 IEF Report 6/28/2013 Page 1 of 33 Patrick Leahy Center for Digital Investigation (LCDI) Disclaimer: This document contains information based on research that has been gathered by employee(s) of The Senator Patrick Leahy Center for Digital Investigation (LCDI). The data contained in this project is submitted voluntarily and is unaudited. Every effort has been made by LCDI to assure the accuracy and reliability of the data contained in this report. However, LCDI nor any of our employees make no representation, warranty or guarantee in connection with this report and hereby expressly disclaims any liability or responsibility for loss or damage resulting from use of this data. Information in this report can be downloaded and redistributed by any person or persons. Any redistribution must maintain the LCDI logo and any references from this report must be properly annotated. Contents Introduction ............................................................................................................................................................. 5 Prior Work: .......................................................................................................................................................... 7 Purpose and Scope: ............................................................................................................................................ -

Frequently Asked Questions
Copyright & File-Sharing FREQUENTLY ASKED QUESTIONS WHAT IS COPYRIGHT? BUT I BOUGHT IT. WHY CAN’T I SHARE IT? WHAT CAN I DO TO AVOID COPYRIGHT Copyright refers to the legal rights creators have There is a difference between using and distributing INFRINGEMENT? over the use, distribution, and reproduction of copyrighted materials. Purchasing songs, movies, or Download content from legitimate sources and do original work (music, movies, software, etc.). software from legitimate sources does not give you the not share copyrighted materials online. Uninstall Copyright infringement is the unlawful use of any right to share these materials over the Internet or make P2P applications (e.g., Popcorn Time, BitTorrent, material protected under copyright law. Common copies for others. When you purchase a Peer-to-Peer Vuze), which may be sharing your files without violations include downloading ‘pirated’ copies of (P2P) program (e.g., Frostwire, BitTorrent, Vuze), you your knowledge. Do not share your NetID and copyrighted materials or sharing files not intended only buy the software, not any files you download or password with anyone. Keep your computer for you to distribute. share using this software. up-to-date with the latest security patches and anti-virus software. HOW DO I KNOW IT’S COPYRIGHTED? DOES UMASS IT MONITOR MY INTERNET Assume all materials are copyright-protected CONNECTION? HOW CAN I LEGALLY DOWNLOAD CONTENT? unless you created them or you have received the No. We do not monitor the contents of your computer Services like Amazon, iTunes, and eMusic offer author’s explicit permission to distribute them. All or issue copyright complaints. -

Illegal File Sharing Notice Notice Is Sent to All Enrolled Students Via Email
Illegal File Sharing Notice Notice is sent to all enrolled students via email. Sample notification: Do YOU know the risks of illegal file sharing? The Recording Industry Association of America, the Motion Picture Association of America, the TV networks like NBC and ABC and other copyright holders will find you and sue you for illegal file sharing! It has happened to students here on campus, so don’t think that this won’t happen to you! Are YOU ready to pay $3,000 to $5,000 for illegally file sharing music, movies, software, etc.? Copyright law allows a copyright holder to sue someone who violates their rights for up to $150,000 per song, movie or TV episode. Students who have been fined at UWSP settled out of court for between $3,000 and $5,000. No one has that kind of cash just sitting around, so how can you avoid these fines? 1. Do NOT use peer‐to‐peer (P2P) file sharing programs like LimeWire, FrostWire, BitTorrent, Ares or Bearshare. 2. Educate yourself about illegal downloading and file sharing at: http://library.uwsp.edu/guides/Copyright/filesharing.htm 3. Use legal music, video and TV sites listed on this web site: http://www.educause.edu/Resources/Browse/LegalDownloading/33381 Here is what happens if YOU get caught for illegal file sharing on the UWSP campus: If you are a student caught while using our Residential Network, the campus wireless network or the campus wired network such as in a computer lab, you will lose your ability to use the Internet on campus for 7 days for a first offense. -

Asus Eee PC for Dummies
Index journal, 101 • Symbols and Numerics • KCalc, 100 > (greater than), redirecting output, 311 KNotes, 105 >> (greater thans), appending to a fi le, 311 Kontact, 100–101 | (vertical bar), directing output to KSnapshot, 102–103 another command, 311–312 PIM (Personal Information Manager), 2G Surf, 14 100–101 4G, 14–15 PIM icon, 99 4G Surf, 14–15 pop-up notes, 101, 105 701SD, 15 Screen Capture icon, 99 900 series, 15–18 to-do list, 101 901 and Beyond icon, 6 Accessories icon, 92, 99 1000 series, 18–19 account name, personalizing, 149 Acrobat Reader, 184. See also PDF readers Acronis True Image, 284 • A • Ad-Aware Free, 231 Adblock Plus, 60 AbiWord, 219–220 add-ons accessories, hardware. See also Firefox, 59–60 personalization Thunderbird, 95–96 Bluetooth, 254–255 Add/Remove Software, 163. See also carrying case, 249–251 installing; uninstalling case graphics, 255–256 Add/Remove Software icon, 147, 163 GPS (Global Positioning System), 259–261 address books, Thunderbird, 96. See also keyboards, 252–253 contact lists mice, 251–252 administrative privileges, 309 modems, 256–257 Advanced Mode, 295–301. See also monitors, 257–259 Easy Mode projectors, 257–259 Advanced Packaging Tool (APT), 204–205 skins (themes), 255–256 advertisements, blocking, 60 USB powered work light, 254 adware, 231 accessories, software. See also AIM, 65 personalization COPYRIGHTEDAll About MATERIAL Eee, 343 accessing, 99 Amarok music player/organizer, 139–140 Calculator, 100 Amazon, 22 Calculator icon, 99 Andreesen, Marc, 58 calendar, 101 Andrew K’s XP Games, 228 capturing -
Stellar Bitraser File Eraser(2 MB, PDF)
BITRASER FILE ERASER Wipe Files Beyond Recovery Secure File Erasure Software For Safeguarding Privacy BitRaser File Eraser DIY software for permanent wiping of sensitive files, web browsing history, app & system traces, & deleted files from laptop, desktops, and external storage media. Wipe sensitive files across devices. Ensure data safety! BitRaser File Eraser is a simple & powerful software for safeguarding data through secure wiping of sensitive files on Windows systems. The tool is ideal for anyone who uses a computer and wants to secure themselves from data breach or leakage threats. Erase files & folders Wipe identity Erase web browsing from Windows PC and documents, tax records, history from Chrome, external storage, etc. photos & videos, etc. Mozilla, Safari, etc. Available for: Know more © Copyright Stellar Information Technology Pvt. Ltd. All Trademarks Acknowledged. www.stellarinfo.com BITRASER FILE ERASER WIPES ALL TYPES OF SENSITIVE FILES ERASES ALL DEVICES & DRIVES Erases photos, videos, tax records, social security Wipes Windows PC, USB flash drives, external number, credit card statement, personal health HDD, SD Card & even files stored on servers. records, official documents and more. CLEARS WEB BROWSING HISTORY REMOVES APPLICATION TRACES TRACES Erases browsing history, cookies, temporary files, Removes activity logs, preferences, etc. generated favorites, etc. Supports Chrome, Mozilla, Safari, IE, with use of News apps, Instant Messengers, Email Microsoft Edge, Opera, & SeaMonkey. apps, Peer to Peer apps, & more. ERASES THE DELETED FILES SCHEDULES THE ERASURE TASKS Wipes the deleted files from system by erasing the Allows to preset & run wiping tasks based on time, day unused space freed up after deletion. Secures & frequency. You can choose specific files for wiping against retrieval of sensitive deleted files. -
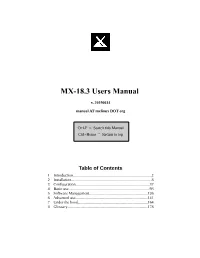
MX-18.3 Users Manual
MX-18.3 Users Manual v. 20190614 manual AT mxlinux DOT org Ctrl-F = Search this Manual Ctrl+Home = Return to top Table of Contents 1 Introduction................................................................................2 2 Installation..................................................................................8 3 Configuration...........................................................................37 4 Basic use..................................................................................93 5 Software Management...........................................................126 6 Advanced use.........................................................................141 7 Under the hood.......................................................................164 8 Glossary.................................................................................178 1 Introduction 1.1 About MX Linux MX Linux is a cooperative venture between the antiX and former MEPIS communities, using the best tools and talents from each distro and including work and ideas originally created by Warren Woodford. It is a midweight OS designed to combine an elegant and efficient desktop with simple configuration, high stability, solid performance and medium-sized footprint. Relying on the excellent upstream work by Linux and the open-source community, we deploy Xfce 4.12 as Desktop Environment on top of a Debian Stable base, drawing from the core antiX system. Ongoing backports and outside additions to our Repos serve to keep components current with developments.