Kernel Module Packages Manual for CODE 11 August 13, 2009
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Chrooting All Services in Linux
LinuxFocus article number 225 http://linuxfocus.org Chrooting All Services in Linux by Mark Nielsen (homepage) About the author: Abstract: Mark works as an independent consultant Chrooted system services improve security by limiting damage that donating time to causes like someone who broke into the system can possibly do. GNUJobs.com, writing _________________ _________________ _________________ articles, writing free software, and working as a volunteer at eastmont.net. Introduction What is chroot? Chroot basically redefines the universe for a program. More accurately, it redefines the "ROOT" directory or "/" for a program or login session. Basically, everything outside of the directory you use chroot on doesn't exist as far a program or shell is concerned. Why is this useful? If someone breaks into your computer, they won't be able to see all the files on your system. Not being able to see your files limits the commands they can do and also doesn't give them the ability to exploit other files that are insecure. The only drawback is, I believe it doesn't stop them from looking at network connections and other stuff. Thus, you want to do a few more things which we won't get into in this article too much: Secure your networking ports. Have all services run as a service under a non-root account. In addition, have all services chrooted. Forward syslogs to another computer. Analyze logs files Analyze people trying to detect random ports on your computer Limit cpu and memory resources for a service. Activate account quotas. The reason why I consider chroot (with a non-root service) to be a line of defense is, if someone breaks in under a non-root account, and there are no files which they can use to break into root, then they can only limit damage to the area they break in. -

The Linux Kernel Module Programming Guide
The Linux Kernel Module Programming Guide Peter Jay Salzman Michael Burian Ori Pomerantz Copyright © 2001 Peter Jay Salzman 2007−05−18 ver 2.6.4 The Linux Kernel Module Programming Guide is a free book; you may reproduce and/or modify it under the terms of the Open Software License, version 1.1. You can obtain a copy of this license at http://opensource.org/licenses/osl.php. This book is distributed in the hope it will be useful, but without any warranty, without even the implied warranty of merchantability or fitness for a particular purpose. The author encourages wide distribution of this book for personal or commercial use, provided the above copyright notice remains intact and the method adheres to the provisions of the Open Software License. In summary, you may copy and distribute this book free of charge or for a profit. No explicit permission is required from the author for reproduction of this book in any medium, physical or electronic. Derivative works and translations of this document must be placed under the Open Software License, and the original copyright notice must remain intact. If you have contributed new material to this book, you must make the material and source code available for your revisions. Please make revisions and updates available directly to the document maintainer, Peter Jay Salzman <[email protected]>. This will allow for the merging of updates and provide consistent revisions to the Linux community. If you publish or distribute this book commercially, donations, royalties, and/or printed copies are greatly appreciated by the author and the Linux Documentation Project (LDP). -
LM1881 Video Sync Separator Datasheet
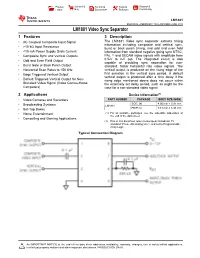
Product Sample & Technical Tools & Support & Folder Buy Documents Software Community LM1881 SNLS384G –FEBRUARY 1995–REVISED JUNE 2015 LM1881 Video Sync Separator 1 Features 3 Description The LM1881 Video sync separator extracts timing 1• AC Coupled Composite Input Signal information including composite and vertical sync, • >10-kΩ Input Resistance burst or back porch timing, and odd and even field • <10-mA Power Supply Drain Current information from standard negative going sync NTSC, • Composite Sync and Vertical Outputs PAL (1) and SECAM video signals with amplitude from • Odd and Even Field Output 0.5-V to 2-V p-p. The integrated circuit is also capable of providing sync separation for non- • Burst Gate or Back Porch Output standard, faster horizontal rate video signals. The • Horizontal Scan Rates to 150 kHz vertical output is produced on the rising edge of the • Edge Triggered Vertical Output first serration in the vertical sync period. A default vertical output is produced after a time delay if the • Default Triggered Vertical Output for Non- rising edge mentioned above does not occur within Standard Video Signal (Video Games-Home the externally set delay period, such as might be the Computers) case for a non-standard video signal. 2 Applications Device Information(1) • Video Cameras and Recorders PART NUMBER PACKAGE BODY SIZE (NOM) SOIC (8) 4.90 mm × 3.91 mm • Broadcasting Systems LM1881 • Set-Top Boxes PDIP (8) 9.81 mm × 6.35 mm • Home Entertainment (1) For all available packages, see the orderable addendum at the end of the data sheet. • Computing and Gaming Applications (1) PAL in this datasheet refers to European broadcast TV standard “Phase Alternating Line”, and not to Programmable Array Logic. -

Creating Rpms Guide
CREATING RPMS (Student version) v1.0 Featuring 36 pages of lecture and a 48 page lab exercise This docu m e n t serves two purpose s: 1. Representative sample to allow evaluation of our courseware manuals 2. Make available high quality RPM documentation to Linux administrators A bout this m aterial : The blue background you see simulates the custom paper that all Guru Labs course w are is printed on. This student version does not contain the instructor notes and teaching tips present in the instructor version. For more information on all the features of our unique layout, see: http://ww w . g urulabs.co m /courseware/course w are_layout.php For more freely available Guru Labs content (and the latest version of this file), see: http://www.gurulabs.co m/goodies/ This sample validated on: Red Hat Enterprise Linux 4 & Fedora Core v3 SUSE Linux Enterprise Server 9 & SUSE Linux Professional 9.2 About Guru Labs: Guru Labs is a Linux training company started in 199 9 by Linux experts to produce the best Linux training and course w are available. For a complete list, visit our website at: http://www.gurulabs.co m/ This work is copyrighted Guru Labs, L.C. 2005 and is licensed under the Creative Common s Attribution- NonCom mer cial- NoDerivs License. To view a copy of this license, visit http://creativecom m o n s.org/licenses/by- nc- nd/2.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 943 0 5, USA. Guru Labs 801 N 500 W Ste 202 Bountiful, UT 84010 Ph: 801-298-5227 WWW.GURULABS.COM Objectives: • Understand -

Suse Linux Enterprise Server 12 - Administration Guide Pdf, Epub, Ebook
SUSE LINUX ENTERPRISE SERVER 12 - ADMINISTRATION GUIDE PDF, EPUB, EBOOK Admin Guide Contributors | 630 pages | 28 Apr 2016 | Samurai Media Limited | 9789888406500 | English | none SUSE Linux Enterprise Server 12 - Administration Guide PDF Book To prevent the conflicts, before starting the migration, execute the following as a super user:. PA, IA In todays service oriented IT zero downtime becomes more and more a most wanted feature. If you want to change actions for single packages, right-click a package in the package view and choose an action. When debugging a problem, you sometimes need to temporarily install a lot of -debuginfo packages which give you more information about running processes. If you are only reading the release notes of the current release, you could miss important changes. However, this can be changed through macro configuration. In this case, the oldest zswap pages are written back to disk-based swap. YaST snapshots are labeled as zypp y2base in the Description column ; Zypper snapshots are labeled zypp zypper. Global variables, or environment variables, can be accessed in all shells. If it is 0 zero the command was successful, everything else marks an error which is specific to the command. The installation medium must be inserted in the HMC. Maintaining netgroup data. This option fetches changes in repositories, but keeps the disabled repositories in the same state—disabled. The rollback snapshots are therefore automatically deleted when the set number of snapshots is reached. The visible physical entity, as it is typically mounted to a motherboard or an equivalent. When using the self-signed certificate, you need to confirm its signature before the first connection. -
26 Disk Space Management
26 Disk Space Management 26.1 INTRODUCTION It has been said that the only thing all UNIX systems have in common is the login message asking users to clean up their files and use less disk space. No matter how much space you have, it isn’t enough; as soon as a disk is added, files magically appear to fill it up. Both users and the system itself are potential sources of disk bloat. Chapter 12, Syslog and Log Files, discusses various sources of logging information and the techniques used to manage them. This chapter focuses on space problems caused by users and the technical and psy- chological weapons you can deploy against them. If you do decide to Even if you have the option of adding more disk storage to your system, add a disk, refer to it’s a good idea to follow this chapter’s suggestions. Disks are cheap, but Chapter 9 for help. administrative effort is not. Disks have to be dumped, maintained, cross-mounted, and monitored; the fewer you need, the better. 26.2 DEALING WITH DISK HOGS In the absence of external pressure, there is essentially no reason for a user to ever delete anything. It takes time and effort to clean up unwanted files, and there’s always the risk that something thrown away might be wanted again in the future. Even when users have good intentions, it often takes a nudge from the system administrator to goad them into action. 618 Chapter 26 Disk Space Management 619 On a PC, disk space eventually runs out and the machine’s primary user must clean up to get the system working again. -
How UNIX Organizes and Accesses Files on Disk Why File Systems
UNIX File Systems How UNIX Organizes and Accesses Files on Disk Why File Systems • File system is a service which supports an abstract representation of the secondary storage to the OS • A file system organizes data logically for random access by the OS. • A virtual file system provides the interface between the data representation by the kernel to the user process and the data presentation to the kernel in memory. The file and directory system cache. • Because of the performance disparity between disk and CPU/memory, file system performance is the paramount issue for any OS Main memory vs. Secondary storage • Small (MB/GB) Large (GB/TB) • Expensive Cheap -2 -3 • Fast (10-6/10-7 sec) Slow (10 /10 sec) • Volatile Persistent Cannot be directly accessed • Directly accessible by CPU by CPU – Interface: (virtual) memory – Data should be first address brought into the main memory Secondary storage (disk) • A number of disks directly attached to the computer • Network attached disks accessible through a fast network - Storage Area Network (SAN) • Simple disks (IDE, SATA) have a described disk geometry. Sector size is the minimum read/write unit of data (usually 512Bytes) – Access: (#surface, #track, #sector) • Smart disks (SCSI, SAN, NAS) hide the internal disk layout using a controller type function – Access: (#sector) • Moving arm assembly (Seek) is expensive – Sequential access is x100 times faster than the random access Internal disk structure • Disk structure User Process Accessing Data • Given the file name. Get to the file’s FCB using the file system catalog (Open, Close, Set_Attribute) • The catalog maps a file name to the FCB – Checks permissions • file_handle=open(file_name): – search the catalog and bring FCB into the memory – UNIX: in-memory FCB: in-core i-node • Use the FCB to get to the desired offset within the file data: (CREATE, DELETE, SEEK, TRUNCATE) • close(file_handle): release FCB from memory Catalog Organization (Directories) • In UNIX, special files (not special device files) called directories contain information about other files. -

Linux Kernel and Driver Development Training Slides
Linux Kernel and Driver Development Training Linux Kernel and Driver Development Training © Copyright 2004-2021, Bootlin. Creative Commons BY-SA 3.0 license. Latest update: October 9, 2021. Document updates and sources: https://bootlin.com/doc/training/linux-kernel Corrections, suggestions, contributions and translations are welcome! embedded Linux and kernel engineering Send them to [email protected] - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 1/470 Rights to copy © Copyright 2004-2021, Bootlin License: Creative Commons Attribution - Share Alike 3.0 https://creativecommons.org/licenses/by-sa/3.0/legalcode You are free: I to copy, distribute, display, and perform the work I to make derivative works I to make commercial use of the work Under the following conditions: I Attribution. You must give the original author credit. I Share Alike. If you alter, transform, or build upon this work, you may distribute the resulting work only under a license identical to this one. I For any reuse or distribution, you must make clear to others the license terms of this work. I Any of these conditions can be waived if you get permission from the copyright holder. Your fair use and other rights are in no way affected by the above. Document sources: https://github.com/bootlin/training-materials/ - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 2/470 Hyperlinks in the document There are many hyperlinks in the document I Regular hyperlinks: https://kernel.org/ I Kernel documentation links: dev-tools/kasan I Links to kernel source files and directories: drivers/input/ include/linux/fb.h I Links to the declarations, definitions and instances of kernel symbols (functions, types, data, structures): platform_get_irq() GFP_KERNEL struct file_operations - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 3/470 Company at a glance I Engineering company created in 2004, named ”Free Electrons” until Feb. -
A U T O M at E D I N S Ta L L At
Proceedings of LISA '99: 13th Systems Administration Conference Seattle, Washington, USA, November 7–12, 1999 A U T O M AT E D I N S TA L L AT I O N O F L I N U X S Y S T E M S U S I N G YA S T Dirk Hohndel and Fabian Herschel THE ADVANCED COMPUTING SYSTEMS ASSOCIATION © 1999 by The USENIX Association All Rights Reserved For more information about the USENIX Association: Phone: 1 510 528 8649 FAX: 1 510 548 5738 Email: [email protected] WWW: http://www.usenix.org Rights to individual papers remain with the author or the author's employer. Permission is granted for noncommercial reproduction of the work for educational or research purposes. This copyright notice must be included in the reproduced paper. USENIX acknowledges all trademarks herein. Automated Installation of Linux Systems Using YaST Dirk Hohndel and Fabian Herschel – SuSE Rhein/Main AG ABSTRACT The paper describes how to allow a customized automated installation of Linux. This is possible via CDRom, network or tape, using a special boot disk that describes the system that should be set up and either standard SuSE Linux CDs, customized install CDs, an appropriately configured installation server, or a tape backup of an existing machine. A control file on the boot disk and additional (optional) control files on the install medium specify which settings should be used and which packages should be installed. This includes settings like language, key table, network setup, hard disk partitioning, packages to install, etc. After giving a quick overview of the syntax and capabilities of this installation method, considerations about how to plan the automated installation at larger sites are presented. -

Installing the Data Broker on a Linux Host : Cloud Sync
Installing the data broker on a Linux host Cloud Sync Ben Cammett April 11, 2021 This PDF was generated from https://docs.netapp.com/us-en/cloudsync/task_installing_linux.html on September 23, 2021. Always check docs.netapp.com for the latest. Table of Contents Installing the data broker on a Linux host. 1 Linux host requirements. 1 Networking requirements . 1 Enabling access to AWS . 1 Enabling access to Google Cloud . 2 Enabling access to Microsoft Azure . 2 Installing the data broker . 2 Installing the data broker on a Linux host When you create a new data broker, choose the On-Prem Data Broker option to install the data broker software on an on-premises Linux host, or on an existing Linux host in the cloud. Cloud Sync guides you through the installation process, but the requirements and steps are repeated on this page to help you prepare for installation. Linux host requirements • Operating system: ◦ CentOS 7.0, 7.7, and 8.0 ◦ Red Hat Enterprise Linux 7.7 and 8.0 ◦ Ubuntu Server 20.04 LTS ◦ SUSE Linux Enterprise Server 15 SP1 The command yum update all must be run on the host before you install the data broker. A Red Hat Enterprise Linux system must be registered with Red Hat Subscription Management. If it is not registered, the system cannot access repositories to update required 3rd party software during installation. • RAM: 16 GB • CPU: 4 cores • Free disk space: 10 GB • SELinux: We recommend that you disable SELinux on the host. SELinux enforces a policy that blocks data broker software updates and can block the data broker from contacting endpoints required for normal operation. -

CIT 470: Advanced Network and System Administration Slide #1 CIT 470: Advanced Network and System Administration Slide #2
Topics 1. The Problem of Software Installation 2. Package Management Systems CIT 470: Advanced Network and 3. Using RPM System Administration 4. Finding RPMs Package Management 5. Building RPMs CIT 470: Advanced Network and System Administration Slide #1 CIT 470: Advanced Network and System Administration Slide #2 Software Installation What’s the problem? 1. Customization What prerequisites does your software have? Select options like language. What prereqs do your prereq packages have? Select file set. How do you handle conflicts? What if two programs install/modify same file? 2. Install new files in appropriate locations. Does your install work on every type of computer? 3. Modify existing configuration files. How do you handle upgrades? 4. Make software available to user. What if user has customized configuration? Shell configuration (PATH, etc.) What if ownerships/permissions have changed? GUI configuration (menu, icons, etc.) What if user needs old and new versions? How do you uninstall software? CIT 470: Advanced Network and System Administration Slide #3 CIT 470: Advanced Network and System Administration Slide #4 Package Manager Features UNIX Package Management Systems • Build management. deb: Debian system uses dpkg and APT. • Dependency tracking. pkgadd: Solaris packaging system. • Querying. portage: Gentoo uses with emerge. • Reversibility. ports: BSD ports system. • Verification. RPM: Redhat packaging system. • Version control. tgz: Tarballs used by Slackware. CIT 470: Advanced Network and System Administration Slide #5 CIT 470: Advanced Network and System Administration Slide #6 1 RPM RPM Package Names RPM Package Manager <name>-<version>-<release>.<arch>.rpm – Originally stood for Red Hat Package Manager – Came with Red Hat Linux 2.0 in 1995. -

Kernel Module Packages Manual for SUSE Linux Enterprise 12 SP2 Or Later and SUSE Linux Enterprise 15
SUSE Best Practices Kernel Module Packages Manual for SUSE Linux Enterprise 12 SP2 or later and SUSE Linux Enterprise 15 SUSE Linux Enterprise 12 SP2+, 15 Document Owner: Ann Davis, Senior Software Engineer, SUSE Kernel Module Packages Manual for SUSE Linux Enterprise 12 SP2 or later and SUSE Linux 1 Enterprise 15 SUSE-based distributions use the RPM Package Manager for software management. As such, any external kernel modules (these are kernel modules not included in SUSE kernel packages) should be packaged in RPM packages. These RPMs should be built in accordance with specic guidelines to ensure that the resulting Kernel Module Packages (KMPs) can be installed and updated appropriately, in synchronization with kernel updates. This document species the requirements for RPM packages that contain kernel modules, and describes the processes surrounding those packages including building, signing, installing and upgrading. A complete example is given and explained. This version of the Kernel Module Packages Manual applies to SUSE Linux Enterprise Server 12 (Service Pack 2 and later), and SUSE Linux Enterprise Server 15, and all products based on these versions. Publication Date: July 31, 2019 Contents 1 Scope 4 2 Background 4 3 Kernel Packages 6 4 Kernel Modules 7 5 Kernel Module Packages 8 6 RPM Provides and Requires 12 7 Building Kernel Module Packages 12 8 Signing 14 9 Deploying Kernel Module Packages 18 10 System Installation and Kernel Module Packages 18 Kernel Module Packages Manual for SUSE Linux Enterprise 12 SP2 or later and SUSE