Windows Full Disk Encryption (PDF)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Bitlocker Encryption for USB Drives Bitlocker Is a Security Feature. the Purpose of Bitlocker Is to Encrypt Your Data
BitLocker Encryption for USB Drives BitLocker is a security feature. The purpose of BitLocker is to encrypt your data. This is extremely necessary for any data that is not to be shared with other persons. This will prevent anyone from being able to access your files. In order to have access to your files, you will need to provide a secure password. This password should be unique only to you. More information is provided below on how to make a unique password in step 2. During this process, step 3 offers the option to save a recovery key. The recovery key is 48 characters long and consist of numbers and letters. This key will be saved to Active Directory and allow the IS Department to access your USB/External drive should you forget your password. To get started I would recommend encrypting the USB/External drive BEFORE adding any files. Once the drive is encrypted and you enter your password it will function as any other USB/External drive. So you may add, edit, or delete your files as you normally would. If you have any trouble following this guide or have any questions please do not hesitate to contact the IS department. You will need a USB or External drive in order to successfully complete this process. Multiple ways to navigate to BitLocker: 1. Control Panel System & Security BitLocker Drive Encryption 2. Search bar type in “BitLocker” Manage BitLocker Steps to encrypt your USB drive: Step 1: Click “Turn on BitLocker” Step 2: Check the “Use a password to unlock the drive” and enter your password. -

Operating System Boot from Fully Encrypted Device
Masaryk University Faculty of Informatics Operating system boot from fully encrypted device Bachelor’s Thesis Daniel Chromik Brno, Fall 2016 Replace this page with a copy of the official signed thesis assignment and the copy of the Statement of an Author. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out by my own. All sources, references and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Daniel Chromik Advisor: ing. Milan Brož i Acknowledgement I would like to thank my advisor, Ing. Milan Brož, for his guidance and his patience of a saint. Another round of thanks I would like to send towards my family and friends for their support. ii Abstract The goal of this work is description of existing solutions for boot- ing Linux and Windows from fully encrypted devices with Secure Boot. Before that, though, early boot process and bootloaders are de- scribed. A simple Linux distribution is then set up to boot from a fully encrypted device. And lastly, existing Windows encryption solutions are described. iii Keywords boot process, Linux, Windows, disk encryption, GRUB 2, LUKS iv Contents 1 Introduction ............................1 1.1 Thesis goals ..........................1 1.2 Thesis structure ........................2 2 Boot Process Description ....................3 2.1 Early Boot Process ......................3 2.2 Firmware interfaces ......................4 2.2.1 BIOS – Basic Input/Output System . .4 2.2.2 UEFI – Unified Extended Firmware Interface .5 2.3 Partitioning tables ......................5 2.3.1 MBR – Master Boot Record . -

Turning on Bitlocker Drive Encryption on Windows Computers Before You
Turning on BitLocker drive encryption on Windows computers Before you start a couple of VERY important notes... a) Make sure you have backups before you start just in case anything goes wrong (as it’s much harder, usually impossible, to recover data from an encrypted drive - as you would hope and expect). b) Make sure you keep a safe copy of the encryption key And please provide a copy for the IT Office to store for use in the event of a problem or, if you choose to let Microsoft keep it, make sure you know your login details for Microsoft. If you forget the passwords and can not recover a copy of your key you will loose all your files (which is another reason to keep backups). If you reset BitLocker and a new encryption key is set - please remember to provide a copy to the IT Office Windows 7, 8 and 10 have BitLocker Built in, this can be used to encrypt the hard drive. It just needs to be activated following the steps shown below. 1) Enable BitLocker for a Drive The easiest way to enable BitLocker for a drive is to right-click the drive in a File Explorer window, and then choose the “Turn on BitLocker” command. If you don’t see this option on your context menu. Then click on the windows icon and where it says “Type here to search” type in “encryption” and click on “Manage BitLocker” from the list of options that appears. It’s just that simple. The wizard that pops up walks you through selecting several options, which we’ve broken down into the sections that follow. -
Microsoft Windows FIPS 140 Validation Security Policy Document
Secure Kernel Code Integrity Security Policy Document Microsoft Windows FIPS 140 Validation Microsoft Windows 10 (Creators Update, Fall Creators Update, April 2018 Update) Microsoft Windows Server (versions 1703, 1709, and 1803) Non-Proprietary Security Policy Document Version Number 1.4 Updated On April 4, 2019 © 2018 Microsoft. All Rights Reserved Page 1 of 24 This Security Policy is non-proprietary and may be reproduced only in its original entirety (without revision). Secure Kernel Code Integrity Security Policy Document The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, AS TO THE INFORMATION IN THIS DOCUMENT. Complying with all applicable copyright laws is the responsibility of the user. This work is licensed under the Creative Commons Attribution-NoDerivs- NonCommercial License (which allows redistribution of the work). To view a copy of this license, visit http://creativecommons.org/licenses/by-nd-nc/1.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 94305, USA. Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. -

Chapter 2: Windows 7
Chapter 2: Windows 7 When you delete a file, a. A copy of the file will be sent to the desktop b. You send the file to the Recycle Bin. c. The file will not be affected. d. A copy of the file will be stored in your active folder. Which of the following statements is correct about arrange icon on desktop. a. Icons on desktop can be arranged by name. b. Icons on desktop can be arranged by type. c. Icons on desktop can be arranged by size. d. All of the above. Which of the following statements is correct about opening control panel. a. You can open control panel from windows explorer. b. You can open control panel from start menu. c. You can open control panel from my computer. d. All of the above. The documents that is located in start menu store. a. The last 15 files that you have open. b. The last 15 files that you have delete. c. The last 15 files that you have copy. d. None of the above. The desktop is: a. An example of a hardware device. b. A folder. c. A file d. A window. The Shutdown icon on start menu means: a. Close all windows. b. Close the current windows. c. Close your computer. d. None of the above. To open a minimized window, you can click on the:- a. window’s button on the body of the taskbar. b. maximized button on the title bar. c. restore button on the title bar. d. all of the above. -
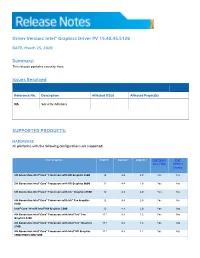
Intel® HD Graphics 5300 12 4.4 2.0 Yes Yes
Driver Version: Intel® Graphics Driver PV 15.40.45.5126 DATE: March 25, 2020 Summary: This release contains security fixes. Issues Resolved Reference No. Description Affected OS(s) Affected Project(s) NA Security Advisory SUPPORTED PRODUCTS: HARDWARE All platforms with the following configurations are supported: Intel® Graphics1 DirectX*2 OpenGL* OpenCL* Intel® Quick Intel® Sync Video Wireless Display 5th Generation Intel® Core™ Processors with HD Graphics 5500 12 4.4 2.0 Yes Yes 5th Generation Intel® Core™ Processors with HD Graphics 6000 12 4.4 2.0 Yes Yes 5th Generation Intel® Core™ Processors with Iris™ Graphics 6100 12 4.4 2.0 Yes Yes 5th Generation Intel® Core™ Processors with Iris™ Pro Graphics 12 4.4 2.0 Yes Yes 6200 Intel® Core™ M with Intel® HD Graphics 5300 12 4.4 2.0 Yes Yes 4th Generation Intel® Core™ Processors with Intel® Iris™ Pro 11.1 4.3 1.2 Yes Yes Graphics 5200 4th Generation Intel® Core™ Processors with Intel® Iris™ Graphics 11.1 4.3 1.2 Yes Yes 5100 4th Generation Intel® Core™ Processors with Intel® HD Graphics 11.1 4.3 1.2 Yes Yes 5000/4600/4400/4200 Intel® Pentium® and Celeron® Processors with Intel® HD Graphics 11.1 4.3 1.2 Yes Yes based on 4th and 5th Generation Intel® Core™ Pentium®, Celeron®, and Atom™ processors based on Braswell and 12 4.3 2.0 Yes Yes CherryTrail. SOFTWARE On 4th Generation Intel Core processors and related Pentium/Celeron: • Microsoft Windows 10® 64-bit, 32-bit* *32-bit support is limited to particular SKU’s. -

Run-Commands-Windows-10.Pdf
Run Commands Windows 10 by Bettertechtips.com Command Action Command Action documents Open Documents Folder devicepairingwizard Device Pairing Wizard videos Open Videos Folder msdt Diagnostics Troubleshooting Wizard downloads Open Downloads Folder tabcal Digitizer Calibration Tool favorites Open Favorites Folder dxdiag DirectX Diagnostic Tool recent Open Recent Folder cleanmgr Disk Cleanup pictures Open Pictures Folder dfrgui Optimie Drive devicepairingwizard Add a new Device diskmgmt.msc Disk Management winver About Windows dialog dpiscaling Display Setting hdwwiz Add Hardware Wizard dccw Display Color Calibration netplwiz User Accounts verifier Driver Verifier Manager azman.msc Authorization Manager utilman Ease of Access Center sdclt Backup and Restore rekeywiz Encryption File System Wizard fsquirt fsquirt eventvwr.msc Event Viewer calc Calculator fxscover Fax Cover Page Editor certmgr.msc Certificates sigverif File Signature Verification systempropertiesperformance Performance Options joy.cpl Game Controllers printui Printer User Interface iexpress IExpress Wizard charmap Character Map iexplore Internet Explorer cttune ClearType text Tuner inetcpl.cpl Internet Properties colorcpl Color Management iscsicpl iSCSI Initiator Configuration Tool cmd Command Prompt lpksetup Language Pack Installer comexp.msc Component Services gpedit.msc Local Group Policy Editor compmgmt.msc Computer Management secpol.msc Local Security Policy: displayswitch Connect to a Projector lusrmgr.msc Local Users and Groups control Control Panel magnify Magnifier -

Self-Encrypting Deception: Weaknesses in the Encryption of Solid State Drives
Self-encrypting deception: weaknesses in the encryption of solid state drives Carlo Meijer Bernard van Gastel Institute for Computing and Information Sciences School of Computer Science Radboud University Nijmegen Open University of the Netherlands [email protected] and Institute for Computing and Information Sciences Radboud University Nijmegen Bernard.vanGastel@{ou.nl,ru.nl} Abstract—We have analyzed the hardware full-disk encryption full-disk encryption. Full-disk encryption software, especially of several solid state drives (SSDs) by reverse engineering their those integrated in modern operating systems, may decide to firmware. These drives were produced by three manufacturers rely solely on hardware encryption in case it detects support between 2014 and 2018, and are both internal models using the SATA and NVMe interfaces (in a M.2 or 2.5" traditional form by the storage device. In case the decision is made to rely on factor) and external models using the USB interface. hardware encryption, typically software encryption is disabled. In theory, the security guarantees offered by hardware encryp- As a primary example, BitLocker, the full-disk encryption tion are similar to or better than software implementations. In software built into Microsoft Windows, switches off software reality, we found that many models using hardware encryption encryption and completely relies on hardware encryption by have critical security weaknesses due to specification, design, and implementation issues. For many models, these security default if the drive advertises support. weaknesses allow for complete recovery of the data without Contribution. This paper evaluates both internal and external knowledge of any secret (such as the password). -

Zenworks 2017 Update 4 Troubleshooting Full Disk Encryption January 2019
ZENworks 2017 Update 4 Troubleshooting Full Disk Encryption January 2019 This document provides troubleshooting guidelines for common problems related to ZENworks Full Disk Encryption. If, after completing the troubleshooting steps, the problem is not resolved, you should contact Technical Support (https://www.novell.com/support/) for additional help. 1 Windows PE Emergency Recovery Disk (ERD) is not working Make sure you have installed the correct WAIK architecture (32-bit vs 64-bit) (Windows 7 only) If you manually created the ERD, use the PowerShell script provided in the Cool Solutions “Windows Powershell script to create a Windows PE emergency recovery disk for ZENworks Full Disk Encryption” article. Try creating the ERD using the ADK for Windows instead of Windows AIK. See “Creating a Windows PE Emergency Recovery Disk” in the ZENworks Full Disk Encryption Emergency Recovery Reference. Try burning the ERD to a DVD rather than a CD. 2 Issues with PBA login or boot sequence After pre-boot authentication occurs, the BIOS or UEFI settings must be correctly set for Windows. With unusual DMI hardware configurations, the standard ZENworks PBA boot method and Linux kernel configuration used to provide the BIOS settings, might not work, resulting in hardware that does not function correctly or is not recognized by Windows. Beginning in ZENworks 2017 Update 2, the Full Disk Encryption Agent includes DMI menu options to repair the boot sequence for issues relating to these DMI configurations. This menu is accessible by using the Ctrl + G keyboard command at a brief point when Full Disk Encryption is shown during a device restart. -
Active@ NTFS Reader for DOS User Guide
Active Data Recovery Software Active@ NTFS Reader for DOS User Guide Version 1.0 Contents PRODUCT OVERVIEW SYSTEM REQUIREMENTS PRODUCT FEATURES OPERATING PROCEDURES 4.1 Bootable Floppy Disk (Startup Disk) Preparation..............................................................................4 4.2 Program Start and Information Display...............................................................................................5 4.3. Scan and Search for Files and Folders..................................................................................................5 4.4. Previewing Files.......................................................................................................................................6 4.5. Copying Files and Folders......................................................................................................................7 4.6. Using Disk Viewer ..................................................................................................................................8 4.7. Localized File Names Display ...............................................................................................................8 4.8. Long File Names Display.......................................................................................................................9 4.9. Command Line Parameters ...................................................................................................................9 1 PRODUCT OVERVIEW Active@ NTFS Reader is a compact and powerful DOS utility that -
Getting Started with Windows Speech Recognition
Getting Started with Windows™ Speech Recognition (WSR) A. OVERVIEW After reading Part One, the first time user will dictate an E-mail or document quickly with high accuracy. The instructions allow you to create, dictate, and send an E-mail without touching the keyboard. The second part discusses steps to attain highest accuracy. The final part has suggestions for increasing productivity when using Windows™ Speech Recognition. II. PART ONE A. WHY USE SPEECH RECOGNITION? Most people will be able to dictate faster and more accurately than they type. My experience with Windows™ Speech Recognition is the ability to dictate over 80 words a minute with accuracy of about 99%. If you truly can type at 80 words a minute with accuracy approaching 99%, you do not need speech recognition. However, even a good keyboarder will benefit from reduced strain on the hands and arms by using Windows™ Speech Recognition. It takes time to become comfortable with dictation into a computer. There will be moments of frustration as you go through the learning curve. If you are impatient or are a perfectionist, DO NOT read on and do not use Windows™ Speech Recognition. If you have reasonable patience, you will learn to dictate accurately and comfortably. The best strategy is to keep things simple for first several days of using Windows™ Speech Recognition. When you are comfortable with the basics, move to part two of this document. B. THE MICROPHONE A good microphone makes dictation into a computer a pleasure instead of a battle. Good microphones reproduce your voice accurately and block out background noise that distorts the audio signal. -
Disk Encryption with 100Gbe Crypto Accelerator
Disk Encryption with 100GbE Crypto Accelerator Chelsio T6 vs. Intel AES-NI vs. Software Enabled Encryption Executive Summary Chelsio Crypto Accelerator is a co-processor designed specifically to perform computationally intensive cryptographic operations more efficiently than general-purpose CPUs. Servers with system load, comprising of cryptographic operations, see great performance improvement by offloading crypto operations on to the Chelsio Unified Wire adapter. Chelsio’s solution uses the standard crypto API framework provided by the operating system and enables the offloading of crypto operations to the adapter. This paper showcases the disk encryption acceleration capabilities of Chelsio T6 adapters by comparing its performance with Intel AES-NI and software encryption. Chelsio solution excels with 100Gbps Crypto rate performance for both encryption and decryption with less than 50% CPU usage. Chelsio’s T6 encryption solution assures complete data protection to datacenters, while providing substantial savings on CPU and memory. Chelsio Disk Encryption Offload The Terminator 6 (T6) ASIC from Chelsio Communications, Inc. is a sixth generation, high performance 1/10/25/40/50/100Gbps unified wire engine which offers crypto offload capability for AES and SHA variants. Chelsio’s disk encryption solution is a special case of data at rest protection where the storage media is a sector-addressable device. Chelsio offloads the AES-XTS mode, which is designed for encrypting data stored on hard disks where there is no additional space for an integrity field. AES-XTS builds on the security of AES by protecting the storage device from many dictionary and copy/paste attacks. Chelsio crypto driver registers with the kernel crypto framework with high priority and ensures that any disk encryption request is offloaded and processed by T6 adapter.