The Potential Harms of the Tor Anonymity Network Cluster Disproportionately in Free Countries
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Know Before You Go
Know Before You Go NORWAY A Guide to Keep You Safe Abroad provided by: Pathways to Safety International Updated May 2019 KNOW BEFORE YOU GO: NORWAY 2 Let’s be perfectly clear, the number one way to prevent sexual assault is to not rape. While the responsibility of ending sexual gender based violence is on the perpetrators, this guide will offer general safety tips, country-specific information, and resources to help prevent and prepare travelers for the possibility of sexual assault abroad. GENERAL SAFETY TIPS: 1. Use the buddy system and travel with friends. 7 out of 10 2. Be aware of social and cultural norms. For example, looking at someone in rapes are the eyes when you speak to them is perfectly normal in the U.S., but in committed another country that could signify you’re interested in the person. by someone known to the 3. Recognize controlling behavior when entering a relationship. Most rape 1 survivors recall feeling “uncomfortable” about some of their partner’s behaviors victim such as degrading jokes/language or refusal to accept “no” as an answer, whether in a sexual context or otherwise.2 4. Avoid secluded places where you could be more vulnerable. Meet new people in public spaces and let a trusted friend know where you’ll be beforehand. Always have a backup plan in mind. 5. Trust your gut. Many victims have a “bad feeling” right before an assault takes place. It’s okay to leave a situation that is making you feel uncomfortable. Stay alert and aware in new social settings and places. -
![Arxiv:1907.07120V1 [Cs.CY] 16 Jul 2019 1 Introduction That China Hindered Access to I2P by Poisoning DNS Resolu- Tions of the I2P Homepage and Three Reseed Servers](https://docslib.b-cdn.net/cover/9451/arxiv-1907-07120v1-cs-cy-16-jul-2019-1-introduction-that-china-hindered-access-to-i2p-by-poisoning-dns-resolu-tions-of-the-i2p-homepage-and-three-reseed-servers-59451.webp)
Arxiv:1907.07120V1 [Cs.CY] 16 Jul 2019 1 Introduction That China Hindered Access to I2P by Poisoning DNS Resolu- Tions of the I2P Homepage and Three Reseed Servers
Measuring I2P Censorship at a Global Scale Nguyen Phong Hoang Sadie Doreen Michalis Polychronakis Stony Brook University The Invisible Internet Project Stony Brook University Abstract required flexibility for conducting fine-grained measurements on demand. We demonstrate these benefits by conducting an The prevalence of Internet censorship has prompted the in-depth investigation of the extent to which the I2P (invis- creation of several measurement platforms for monitoring ible Internet project) anonymity network is blocked across filtering activities. An important challenge faced by these different countries. platforms revolves around the trade-off between depth of mea- Due to the prevalence of Internet censorship and online surement and breadth of coverage. In this paper, we present surveillance in recent years [7, 34, 62], many pro-privacy and an opportunistic censorship measurement infrastructure built censorship circumvention tools, such as proxy servers, virtual on top of a network of distributed VPN servers run by vol- private networks (VPN), and anonymity networks have been unteers, which we used to measure the extent to which the developed. Among these tools, Tor [23] (based on onion rout- I2P anonymity network is blocked around the world. This ing [39,71]) and I2P [85] (based on garlic routing [24,25,33]) infrastructure provides us with not only numerous and ge- are widely used by privacy-conscious and censored users, as ographically diverse vantage points, but also the ability to they provide a higher level of privacy and anonymity [42]. conduct in-depth measurements across all levels of the net- In response, censors often hinder access to these services work stack. -

A Generic Data Exchange System for F2F Networks
The Retroshare project The GXS system Decentralize your app! A Generic Data Exchange System for F2F Networks Cyril Soler C.Soler The GXS System 03 Feb. 2018 1 / 19 The Retroshare project The GXS system Decentralize your app! Outline I Overview of Retroshare I The GXS system I Decentralize your app! C.Soler The GXS System 03 Feb. 2018 2 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows, (+ Android). C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. C.Soler The GXS System 03 Feb. 2018 3 / 19 The Retroshare project The GXS system Decentralize your app! The Retroshare Project I Mesh computers using signed TLS over TCP/UDP/Tor/I2P; I anonymous end-to-end encrypted FT with swarming; I mail, IRC chat, forums, channels; I available on Mac OS, Linux, Windows. -
Hacking the Web
Hacking the Web (C) 2009-2020 Arun Viswanathan Ellis Horowitz Marco Papa 1 Table of Contents } General Introduction } Authentication Attacks } Client-Side Attacks } Injection Attacks } Recent Attacks } Privacy Tools 2 (C) 2009-2020 Arun Viswanathan Ellis Horowitz Marco Papa Why secure the Web? } The Web has evolved into an ubiquitous entity providing a rich and common platform for connecting people and doing business. } BUT, the Web also offers a cheap, effective, convenient and anonymous platform for crime. } To get an idea, the Web has been used for the following types of criminal activities (source: The Web Hacking Incidents Database (WHID) http://projects.webappsec.org/w/page/13246995/Web-Hacking-Incident-Database) } Chaos (Attack on Russian nuclear power websites amid accident rumors (5Jan09) } Deceit (SAMY XSS Worm – Nov 2005) } Extortion (David Aireys domain hijacked due to a CSRF (cross site request forgery) flaw in Gmail – 30Dec2007) } Identity Theft (XSS on Yahoo! Hot jobs – Oct 2008) } Information Warfare (Israeli Gaza War - Jan 2009 / Balkan Wars – Apr 2008 ) } Monetary Loss (eBay fraud using XSS) } Physical Pain (Hackers post on epilepsy forum causes migraines and seizures – May 2008) } Political Defacements (Hacker changes news release on Sheriffs website – Jul 2008) (Obama, Oreilly and Britneys Twitter accounts hacked and malicious comments posted – Jan 09) } Chinese Gaming sites hacked (Dec. 2011) 3 Copyright(C) 2009 (c) -20092020- 2019Arun Arun Viswanathan Viswanathan Ellis HorowitzEllis Horowitz Marco Marco Papa Papa -
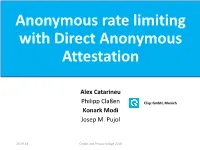
Anonymous Rate Limiting with Direct Anonymous Attestation
Anonymous rate limiting with Direct Anonymous Attestation Alex Catarineu Philipp Claßen Cliqz GmbH, Munich Konark Modi Josep M. Pujol 25.09.18 Crypto and Privacy Village 2018 Data is essential to build services 25.09.18 Crypto and Privacy Village 2018 Problems with Data Collection IP UA Timestamp Message Payload Cookie Type 195.202.XX.XX FF.. 2018-07-09 QueryLog [face, facebook.com] Cookie=966347bfd 14:01 1e550 195.202.XX.XX Chrome.. 2018-07-09 Page https://analytics.twitter.com/user/konark Cookie=966347bfd 14:06 modi 1e55040434abe… 195.202.XX.XX Chrome.. 2018-07-09 QueryLog [face, facebook.com] Cookie=966347bfd 14:10 1e55040434abe… 195.202.XX.XX Chrome.. 2018-07-09 Page https://booking.com/hotels/barcelona Cookie=966347bfd 16:15 1e55040434abe… 195.202.XX.XX Chrome.. 2018-07-09 QueryLog [face, facebook.com] Cookie=966347bfd 14:10 1e55040434abe… 195.202.XX.XX FF.. 2018-07-09 Page https://shop.flixbus.de/user/resetting/res Cookie=966347bfd 18:40 et/hi7KTb1Pxa4lXqKMcwLXC0XzN- 1e55040434abe… 47Tt0Q 25.09.18 Crypto and Privacy Village 2018 Anonymous data collection Timestamp Message Type Payload 2018-07-09 14 Querylog [face, facebook.com] 2018-07-09 14 Querylog [boo, booking.com] 2018-07-09 14 Page https://booking.com/hotels/barcelona 2018-07-09 14 Telemetry [‘engagement’: 0 page loads last week, 5023 page loads last month] More details: https://gist.github.com/solso/423a1104a9e3c1e3b8d7c9ca14e885e5 http://josepmpujol.net/public/papers/big_green_tracker.pdf 25.09.18 Crypto and Privacy Village 2018 Motivation: Preventing attacks on anonymous data collection Timestamp Message Type Payload 2018-07-09 14 querylog [book, booking.com] 2018-07-09 14 querylog [fac, facebook.com] … …. -

IPFS and Friends: a Qualitative Comparison of Next Generation Peer-To-Peer Data Networks Erik Daniel and Florian Tschorsch
1 IPFS and Friends: A Qualitative Comparison of Next Generation Peer-to-Peer Data Networks Erik Daniel and Florian Tschorsch Abstract—Decentralized, distributed storage offers a way to types of files [1]. Napster and Gnutella marked the beginning reduce the impact of data silos as often fostered by centralized and were followed by many other P2P networks focusing on cloud storage. While the intentions of this trend are not new, the specialized application areas or novel network structures. For topic gained traction due to technological advancements, most notably blockchain networks. As a consequence, we observe that example, Freenet [2] realizes anonymous storage and retrieval. a new generation of peer-to-peer data networks emerges. In this Chord [3], CAN [4], and Pastry [5] provide protocols to survey paper, we therefore provide a technical overview of the maintain a structured overlay network topology. In particular, next generation data networks. We use select data networks to BitTorrent [6] received a lot of attention from both users and introduce general concepts and to emphasize new developments. the research community. BitTorrent introduced an incentive Specifically, we provide a deeper outline of the Interplanetary File System and a general overview of Swarm, the Hypercore Pro- mechanism to achieve Pareto efficiency, trying to improve tocol, SAFE, Storj, and Arweave. We identify common building network utilization achieving a higher level of robustness. We blocks and provide a qualitative comparison. From the overview, consider networks such as Napster, Gnutella, Freenet, BitTor- we derive future challenges and research goals concerning data rent, and many more as first generation P2P data networks, networks. -
Privacy Enhancing Technologies 2003 an Analysis of Gnunet And
Privacy Enhancing Technologies 2003 An Analysis of GNUnet and the Implications for Anonymous, Censorship-Resistant Networks Dennis Kügler Federal Office for Information Security, Germany [email protected] 1 Anonymous, Censorship-Resistant Networks • Anonymous Peer-to-Peer Networks – Gnutella • Searching is relatively anonymous • Downloading is not anonymous • Censorship-Resistant Networks – Eternity Service • Distributed storage medium • Attack resistant • Anonymous, Censorship-Resistant Networks – Freenet – GNUnet 2 GNUnet: Obfuscated, Distributed Filesystem Content Hash Key: [H(B),H(E (B))] • H(B) – Content encryption: H(B) – Unambiguous filename: H(E (B)) H(B) • Content replication – Caching while delivering – Based on unambiguous filename • Searchability – Keywords 3 GNUnet: Peer-to-Peer MIX Network • Initiating node – Downloads content • Supplying nodes – Store content unencrypted • Intermediary nodes – Forward and cache encrypted content – Plausible deniability due to encryption • Economic model – Based on credit Query A Priority=20 B – Charge for queries c =c -20 B B - – Pay for responses 4 GNUnet Encoding • DBlocks DBlock DBlock ... DBlock – 1KB of the content – Content hash encrypted • IBlocks IBlock ... IBlock – CHKs of 25 DBlocks – Organized as tree – Content hash encrypted IBlock • RBlock – Description of the content – CHK of the root IBlock RBlock – Keyword encrypted 5 The Attacker Model • Attacker – Controls malicious nodes that behave correctly – Prepares dictionary of interesting keywords – Observes queries and -

Wikileaks and the Institutional Framework for National Security Disclosures
THE YALE LAW JOURNAL PATRICIA L. BELLIA WikiLeaks and the Institutional Framework for National Security Disclosures ABSTRACT. WikiLeaks' successive disclosures of classified U.S. documents throughout 2010 and 2011 invite comparison to publishers' decisions forty years ago to release portions of the Pentagon Papers, the classified analytic history of U.S. policy in Vietnam. The analogy is a powerful weapon for WikiLeaks' defenders. The Supreme Court's decision in the Pentagon Papers case signaled that the task of weighing whether to publicly disclose leaked national security information would fall to publishers, not the executive or the courts, at least in the absence of an exceedingly grave threat of harm. The lessons of the PentagonPapers case for WikiLeaks, however, are more complicated than they may first appear. The Court's per curiam opinion masks areas of substantial disagreement as well as a number of shared assumptions among the Court's members. Specifically, the Pentagon Papers case reflects an institutional framework for downstream disclosure of leaked national security information, under which publishers within the reach of U.S. law would weigh the potential harms and benefits of disclosure against the backdrop of potential criminal penalties and recognized journalistic norms. The WikiLeaks disclosures show the instability of this framework by revealing new challenges for controlling the downstream disclosure of leaked information and the corresponding likelihood of "unintermediated" disclosure by an insider; the risks of non-media intermediaries attempting to curtail such disclosures, in response to government pressure or otherwise; and the pressing need to prevent and respond to leaks at the source. AUTHOR. -
Tor and Circumvention: Lessons Learned
Tor and circumvention: Lessons learned Nick Mathewson The Tor Project https://torproject.org/ 1 What is Tor? Online anonymity 1) open source software, 2) network, 3) protocol Community of researchers, developers, users, and relay operators Funding from US DoD, Electronic Frontier Foundation, Voice of America, Google, NLnet, Human Rights Watch, NSF, US State Dept, SIDA, ... 2 The Tor Project, Inc. 501(c)(3) non-profit organization dedicated to the research and development of tools for online anonymity and privacy Not secretly evil. 3 Estimated ~250,000? daily Tor users 4 Anonymity in what sense? “Attacker can’t learn who is talking to whom.” Bob Alice Alice Anonymity network Bob Alice Bob 5 Threat model: what can the attacker do? Alice Anonymity network Bob watch Alice! watch (or be!) Bob! Control part of the network! 6 Anonymity isn't cryptography: Cryptography just protects contents. “Hi, Bob!” “Hi, Bob!” Alice <gibberish> attacker Bob 7 Anonymity isn't just wishful thinking... “You can't prove it was me!” “Promise you won't look!” “Promise you won't remember!” “Promise you won't tell!” “I didn't write my name on it!” “Isn't the Internet already anonymous?” 8 Anonymity serves different interests for different user groups. Anonymity “It's privacy!” Private citizens 9 Anonymity serves different interests for different user groups. Anonymity Businesses “It's network security!” “It's privacy!” Private citizens 10 Anonymity serves different interests for different user groups. “It's traffic-analysis resistance!” Governments Anonymity Businesses “It's network security!” “It's privacy!” Private citizens 11 Anonymity serves different interests for different user groups. -

DARK WEB INVESTIGATION GUIDE Contents 1
DARK WEB INVESTIGATION GUIDE Contents 1. Introduction 3 2. Setting up Chrome for Dark Web Access 5 3. Setting up Virtual Machines for Dark Web Access 9 4. Starting Points for Tor Investigations 20 5. Technical Clues for De-Anonymizing Hidden Services 22 5.1 Censys.io SSL Certificates 23 5.2 Searching Shodan for Hidden Services 24 5.3 Checking an IP Address for Tor Usage 24 5.4 Additional Resources 25 6. Conclusion 26 2 Dark Web Investigation Guide 1 1. Introduction 3 Introduction 1 There is a lot of confusion about what the dark web is vs. the deep web. The dark web is part of the Internet that is not accessible through traditional means. It requires that you use a technology like Tor (The Onion Router) or I2P (Invisible Internet Project) in order to access websites, email or other services. The deep web is slightly different. The deep web is made of all the webpages or entire websites that have not been crawled by a search engine. This could be because they are hidden behind paywalls or require a username and password to access. We are going to be setting up access to the dark web with a focus on the Tor network. We are going to accomplish this in two different ways. The first way is to use the Tor Browser to get Google Chrome connected to the the Tor network. This is the less private and secure option, but it is the easiest to set up and use and is sufficient for accessing material on the dark web. -

The Economic Functioning of Online Drugs Markets
ISSN 2042-2695 CEP Discussion Paper No 1490 Revised August 2017 (Replaced July 2017 version) The Economic Functioning of Online Drugs Markets V. Bhaskar Robin Linacre Stephen Machin Abstract The economic functioning of online drug markets using data scraped from online platforms is studied. Analysis of over 1.5 million online drugs sales shows online drugs markets tend to function without the significant moral hazard problems that, a priori, one might think would plague them. Only a small proportion of online drugs deals receive bad ratings from buyers, and online markets suffer less from problems of adulteration and low quality that are a common feature of street sales of illegal drugs. Furthermore, as with legal online markets, the market penalizes bad ratings, which subsequently lead to significant sales reductions and to market exit. The impact of the well-known seizure by law enforcement of the original Silk Road and the shutdown of Silk Road 2.0 are also studied, together with the exit scam of the market leader at the time, Evolution. There is no evidence that these exits deterred buyers or sellers from online drugs trading, as new platforms rapidly replaced those taken down, with the online market for drugs continuing to grow. Keywords: dark web, drugs JEL codes:K42 This paper was produced as part of the Centre’s Communities Programme. The Centre for Economic Performance is financed by the Economic and Social Research Council. Acknowledgements Robin Linacre contributed to this paper in a personal capacity and in his own time. The research is not linked to any of his work for either the Sentencing Council or the Ministry of Justice. -
CS505: Distributed Systems
Cristina Nita-Rotaru CS505: Distributed Systems Lookup services. Chord. CAN. Pastry. Kademlia. Required Reading } I. Stoica, R. Morris, D. Karger, M. F. Kaashoek, H. Balakrishnan, Chord: A Scalable Peer-to-peer Lookup Service for Internet Applications, SIGCOMM 2001. } A Scalable Content-Addressable Network S.a Ratnasamy, P. Francis, M. Handley, R. Karp, S. Shenker, SIGCOMM 2001 } A. Rowstron and P. Druschel. "Pastry: Scalable, decentralized object location and routing for large-scale peer-to-peer systems". IFIP/ACM International Conference on Distributed Systems Platforms (Middleware), 2001 } Kademlia: A Peer-to-peer Information System Based on the XOR Metric. P. Maymounkov and D. Mazieres, IPTPS '02 2 DHTs 1: Lookup services Peer-to-Peer (P2P) Systems } Applications that take advantage of resources (storage, cycles, content, human presence) available at the edges of the Internet. } Characteristics: } System consists of clients connected through Internet and acting as peers } System is designed to work in the presence of variable connectivity } Nodes at the edges of the network have significant autonomy; no centralized control } Nodes are symmetric in function 4 DHTs Benefits of P2P and Applications } High capacity: all clients provide resources (bandwidth, storage space, and computing power). The capacity of the system increases as more nodes become part of the system. } Increased reliability: achieved by replicating data over multiple peers, and by enabling peers to find the data without relying on a centralized index server. } Applications: