Web Hacking 101 How to Make Money Hacking Ethically
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
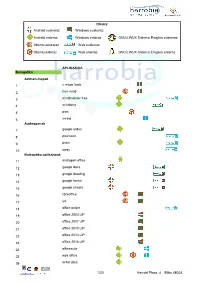
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -
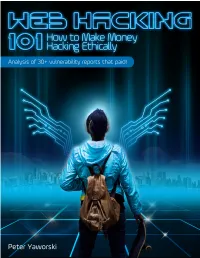
Web Hacking 101 How to Make Money Hacking Ethically
Web Hacking 101 How to Make Money Hacking Ethically Peter Yaworski © 2015 - 2016 Peter Yaworski Tweet This Book! Please help Peter Yaworski by spreading the word about this book on Twitter! The suggested tweet for this book is: Can’t wait to read Web Hacking 101: How to Make Money Hacking Ethically by @yaworsk #bugbounty The suggested hashtag for this book is #bugbounty. Find out what other people are saying about the book by clicking on this link to search for this hashtag on Twitter: https://twitter.com/search?q=#bugbounty For Andrea and Ellie. Thanks for supporting my constant roller coaster of motivation and confidence. This book wouldn’t be what it is if it were not for the HackerOne Team, thank you for all the support, feedback and work that you contributed to make this book more than just an analysis of 30 disclosures. Contents 1. Foreword ....................................... 1 2. Attention Hackers! .................................. 3 3. Introduction ..................................... 4 How It All Started ................................. 4 Just 30 Examples and My First Sale ........................ 5 Who This Book Is Written For ........................... 7 Chapter Overview ................................. 8 Word of Warning and a Favour .......................... 10 4. Background ...................................... 11 5. HTML Injection .................................... 14 Description ....................................... 14 Examples ........................................ 14 1. Coinbase Comments ............................. -

Volunteered Geographic Information System Design: Project and Participation Guidelines
International Journal of Geo-Information Article Volunteered Geographic Information System Design: Project and Participation Guidelines José-Pablo Gómez-Barrón *, Miguel-Ángel Manso-Callejo, Ramón Alcarria and Teresa Iturrioz MERCATOR Research Group: Geo-Information Technologies, Technical High School of Topography, Geodesy and Cartography Engineering, Technical University of Madrid (UPM), Campus Sur, 28031 Madrid, Spain; [email protected] (M.-A.M.-C.); [email protected] (R.A.); [email protected] (T.I.) * Correspondence: [email protected]; Tel.: +34-913-366-487 Academic Editors: Linda See, Vyron Antoniou, David Jonietz and Wolfgang Kainz Received: 14 March 2016; Accepted: 20 June 2016; Published: 5 July 2016 Abstract: This article sets forth the early phases of a methodological proposal for designing and developing Volunteered Geographic Information (VGI) initiatives based on a system perspective analysis in which the components depend and interact dynamically among each other. First, it focuses on those characteristics of VGI projects that present different goals and modes of organization, while using a crowdsourcing strategy to manage participants and contributions. Next, a tool is developed in order to design the central crowdsourced processing unit that is best suited for a specific project definition, associating it with a trend towards crowd-based or community-driven approaches. The design is structured around the characterization of different ways of participating, and the task cognitive demand of working on geo-information management, spatial problem solving and ideation, or knowledge acquisition. Then, the crowdsourcing process design helps to identify what kind of participants are needed and outline subsequent engagement strategies. This is based on an analysis of differences among volunteers’ participatory behaviors and the associated set of factors motivating them to contribute, whether on a crowd or community-sourced basis. -
Manual Oruxmaps V.7.0.0
Manual OruxMaps v.7.0.0 ¡COLABRORATE WITH ORUXMAPS! You can help the project: Donate using Paypal Download OruxMaps Donate WORKING WITH THE MANUALS It is an easy task if we do it between all. Español English ***NEEDS A LOT OF HELP*** 1 INDEX NEWS 7.0. VERSION ............................................................................................ 3 NEWS 6.5.0 VERSION .......................................................................................... 6 QUICK START ................................................................................................... 13 Widget ..............................................................................................................................14 MAPS ............................................................................................................... 15 Online Maps ....................................................................................................................16 WMS (Web Map Service) ......................................................................................18 Composite maps .......................................................................................................22 Maps Off-Line ................................................................................................................24 Index map .......................................................................................................................29 Nigth mode .....................................................................................................................29 -

Global and Complementary Geospatial Data for Sdgs
Global and Complementary (Non-authoritative) Geospatial Data for SDGs: Role and Utilisation Stephan Arnold, Jun Chen & Olav Eggers A report produced jointly by the Task Team on Global Data and Task Team on Alternative Data Sources established in December 2016 by the Working Group on Geospatial Information of the Inter-agency and Expert Group on Sustainable Development Goal Indicators (IAEG-SDGs) with contributions from Mr. Stephan Arnold, Prof. Jun Chen, Mr. Olav Eggers, Prof. Zhilin Li, Ms. Sandra Liliana Moreno Mayorga, Prof. John Mills, and Prof. John Shi. This report was reviewed by members of the working group before being made available to IAEG-SDGs at its ninth meeting in March 2019. Content 1 PREAMBLE ................................................................................................................................. 3 1.1 Importance of geospatial data to SDGs ............................................................................................... 3 1.2 Scope of this report ............................................................................................................................. 3 2 GLOBAL AND COMPLEMENTARY GEOSPATIAL DATASETS ....................................... 4 2.1 National versus international (global) mapping initiatives .................................................................. 4 2.1.1 Topographic maps and Digital Elevation Models .................................................................................. 4 2.1.2 Satellite Image Data ............................................................................................................................. -

Deriving Incline for Street Networks from Voluntarily Collected GPS Traces
Methods of Geoinformation Science Institute of Geodesy and Geoinformation Science Faculty VI Planning Building Environment MASTER’S THESIS Deriving incline for street networks from voluntarily collected GPS traces Submitted by: Steffen John Matriculation number: 343372 Email: [email protected] Supervisors: Prof. Dr.-Ing. Marc-O. Löwner (TU Berlin) Dr.-Ing. Stefan Hahmann (Universität Heidelberg) Submission date: 24.07.2015 in cooperation with: GIScience Group Institute of Geography Faculty of Chemistry and Earth Sciences Declaration of Authorship I, Steffen John, declare that this thesis titled, 'Deriving incline for street networks from voluntarily collected GPS traces’ and the work presented in it are my own. I confirm that: This work was done wholly or mainly while in candidature for a research degree at this Uni- versity. Where any part of this thesis has previously been submitted for a degree or any other qualifi- cation at this University or any other institution, this has been clearly stated. Where I have consulted the published work of others, this is always clearly attributed. Where I have quoted from the work of others, the source is always given. With the exception of such quotations, this thesis is entirely my own work. I have acknowledged all main sources of help. Where the thesis is based on work done by myself jointly with others, I have made clear exact- ly what was done by others and what I have contributed myself. Signed: Date: ii Abstract The knowledge of incline is useful for many use-cases in navigation for electricity-powered vehicles, cyclists or mobility-restricted people (e.g. -

Quality Assessment of the Contributed Land Use Information from Openstreetmap Versus Authoritative Datasets
Quality Assessment of the Contributed Land Use Information from OpenStreetMap Versus Authoritative Datasets Jamal Jokar Arsanjani, Peter Mooney, Alexander Zipf and Anne Schauss Abstract Land use (LU) maps are an important source of information in academia and for policy-makers describing the usage of land parcels. A large amount of effort and monetary resources are spent on mapping LU features over time and at local, regional, and global scales. Remote sensing images and signal processing tech- niques, as well as land surveying are the prime sources to map LU features. However, both data gathering approaches are financially expensive and time con- suming. But recently, Web 2.0 technologies and the wide dissemination of GPS- enabled devices boosted public participation in collaborative mapping projects (CMPs). In this regard, the OpenStreetMap (OSM) project has been one of the most successful representatives, providing LU features. The main objective of this paper is to comparatively assess the accuracy of the contributed OSM-LU features in four German metropolitan areas versus the pan-European GMESUA dataset as a ref- erence. Kappa index analysis along with per-class user’s and producers’ accuracies are used for accuracy assessment. The empirical findings suggest OSM as an alternative complementary source for extracting LU information whereas exceeding 50 % of the selected cities are mapped by mappers. Moreover, the results identify which land types preserve high/moderate/low accuracy across cities for urban LU mapping. The findings strength the potential of collaboratively collected LU J. Jokar Arsanjani (&) Á A. Zipf Á A. Schauss GIScience Research Group, Institute of Geography, Heidelberg University, 69120 Heidelberg, Germany e-mail: [email protected] A. -

Usage of VGI for Validation of Land Cover Maps 1,2Cidália C
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by Aston Publications Explorer Usage of VGI for Validation of Land Cover Maps 1,2Cidália C. Fonte, 3Lucy Bastin, 4Linda See, 5Giles Foody, 6Favio Lupia 1 Department of Mathematics, University of Coimbra, Coimbra, Portugal 2 Institute for Systems Engineering and Computers at Coimbra (INESC Coimbra), Coimbra, Portugal 3 School of Engineering and Applied Science, Aston University, Birmingham, B4 7ET, UK 4 Ecosystems Services and Management Program, International Institute for Applied Systems Analysis (IIASA), Laxenburg, Austria 5 School of Geography , University of Nottingham , Nottingham ,NG7 2RD, UK 6 National Institute of Agricultural Economics (INEA), Rome, Italy Corresponding author: Cidália C. Fonte (e-mail: [email protected]) 1 Usage of VGI for Validation of Land Cover Maps Volunteered Geographic Information (VGI) represents a growing source of potentially valuable data for land cover validation. However, the quality and credibility of the data remains a key concern, especially if VGI is to be adopted by more traditional map producers or integrated into authoritative sources in the future. This paper reviews different categories of spatial data quality and the main sources of VGI currently being used in the development and validation of land cover maps. The paper also proposes a framework for addressing different VGI quality assessment methodologies, which is used to identify gaps in approaches that could be used in VGI quality assessment in the future. Keywords: VGI, land cover/land use, quality, validation, crowdsourcing 1. Introduction Land cover maps are fundamental for a wide range of users and for many applications, such as planning, nature and biodiversity protection, environmental monitoring, management of natural resources, climate change and hydrological modelling (Feddema et al. -
Bug Bounty Hunting Essentials
Bug Bounty Hunting Essentials Quick-paced guide to help white-hat hackers get through bug bounty programs Carlos A. Lozano Shahmeer Amir BIRMINGHAM - MUMBAI Bug Bounty Hunting Essentials Copyright © 2018 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews. Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the authors, nor Packt Publishing or its dealers and distributors, will be held liable for any damages caused or alleged to have been caused directly or indirectly by this book. Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information. Commissioning Editor: Gebin George Acquisition Editor: Shrilekha Inani Content Development Editor: Abhishek Jadhav Technical Editor: Mohd Riyan Khan Copy Editor: Safis Editing Project Coordinator: Jagdish Prabhu Proofreader: Safis Editing Indexer: Tejal Daruwale Soni Graphics: Tom Scaria Production Coordinator: Shantanu Zagade First published: November 2018 Production reference: 1301118 Published by Packt Publishing Ltd. Livery Place 35 Livery Street Birmingham B3 2PB, UK. ISBN 978-1-78862-689-7 www.packtpub.com mapt.io Mapt is an online digital library that gives you full access to over 5,000 books and videos, as well as industry leading tools to help you plan your personal development and advance your career. -

Turkey Openstreetmap Dataset
Open Geosci. 2019; 11:140–151 Research Article Open Access Mohammed Zia*, Ziyadin Cakir, and Dursun Zafer Seker Turkey OpenStreetMap Dataset - Spatial Analysis of Development and Growth Proxies https://doi.org/10.1515/geo-2019-0012 Received February 1, 2018; accepted April 16, 2018 1 Introduction Abstract: Number of studies covering major data aspects With the ease of online-data generation and dissemination of OpenStreetMap (OSM) for developed cities and coun- by the advent of Web2.0 technology the narrowly-targeted tries are available in scientific literature. However, this goods and services are getting as economically attractive is not the case for developing ones mainly because of and lucrative as mainstream fare [1, 2]. For example, we low data availability in OSM. This study presents a time- now have Whatsapp, Skype, Viber etc. in Telecommunica- series spatial analysis of Turkey OSM dataset, a devel- tion sector, which was predominantly governed by Tele- oping country, between the year 2007 and 2015 to un- com industries for decades. Wikipedia holds a huge pile derstand how the dataset has developed with time and of online free-content and competes with other propri- space. Five different socio-economic factors of the region etary data sources like Encyclopedia Britannica. Recent are tested to find their relationship, if any, with dataset free publication of classified information by WikiLeaks growth. An east-west spatial trend in data density is ob- and OpenLeaks has challenged governments and other na- served within the country. Population Density and Liter- tional intelligence agencies, who were regulating confi- acy Level of the region are found be the factors control- dential information of citizens so far [3]. -
GPS Tutorial for Hikers How to Efficiently Use Your Mobile As GPS Navigator for Hiking
GPS Tutorial for Hikers How to efficiently use your mobile as GPS navigator for hiking By Marc TORBEY Examples from the Android software OruxMaps V1.0 1 Table of contents • Basics about GPS for hiking slide 3 • Before the hike slide 12 • It’s hiking day! slide 20 • After the hike slide 31 2 Basics about GPS for hiking 3 Abbreviations used • GE Google Earth (free software for computers) • GPS Global Positioning System • OM Orux Maps (GPS application for Android phones) • POI Point Of Interest (on a map) • WP Waypoint 4 GPS Global Positioning System • Several satellite around planet Earth, broadcast GPS “signals”: – GPS devices receive satellite signals… no transmission – Weak signals from remote satellites, so… • perceptible Outdoors only! • 1st “GPS fix” requires user to be still (not moving) • Origin of GPS systems – USA: NAVSTAR – Russia: GLONASS (since 2010) – UE: Galileo (available in 2020). • Goals of GPS systems: – Basic goal: knowing your position on a map – Navigation: sea, land (car) – Orientation: hiking trips 5 GPS maps Typically a digital map is either • A sophisticated software object comprising a drawing of the landscape (with roads, public monuments, …) + a database of POIs + some intelligent software capable of giving you directions to reach your destination POI. – Requires Internet connectivity, to access the latest maps and POIs. – Usually expensive Example Google maps • Or a simple picture, showing the landscape and possibly the roads. – No navigation capabilities but… Ok for hiking! – Can be used off-line by software like OM – Usually available free of charge – Ex: Google Earth/ Hybrid 6 GPS objects - Waypoints • A Waypoint is a point on the map, created in order to locate an important place on the map… – either by the “Create waypoint” function of the OM mobile (marks the user’s current location) – Or by clicking a point on the “Map” – Or by some software • On Google Earth it is called a Placemark. -

Trabajo Fin Alde G Rad O
GRADO DE INGENIERÍA INFORMÁTICA Librería de Python para el trazamiento y la animación de trayectorias de GPS almacenadas en ficheros con formato GPX JUAN JOSÉ MARTÍN MIRALLES Tutor Dr. Isaac Lera Castro Trabajo Final de Grado Escola Politècnica Superior Universitat de les Illes Balears Palma, junio de 2017 GRADO DE INGENIERÍA INFORMÁTICA Librería de Python para el trazamiento y la animación de trayectorias de GPS almacenadas en ficheros con formato GPX JUAN JOSÉ MARTÍN MIRALLES Tutor Dr. Isaac Lera Castro Escola Politècnica Superior Universitat de les Illes Balears Palma, junio de 2017 i A mi familia y, sobre todo, a Espe por darme todo el cariño y las fuerzas para conseguir todo lo que me propongo en mi vida. A Edu, Paula y Sam, por escucharme durante 4 meses hablar únicamente de este proyecto y, aún así, seguir a mi lado. A Carlos y Camila, por una carrera increíble que hubiera sido más difícil sin vosotros. A mi abuelo por ser, simplemente, el mejor abuelo que ha podido existir en este mundo. ÍNDICEGENERAL Índice generalv Índice de figuras vii Índice de cuadros ix Índice de algoritmos xi Acrónimos xiii Abstract xv 1 Introducción1 2 Sistemas de Posicionamiento Global7 2.1 Puntos de interés, trayectorias y rutas de los ficheros con formato GPX8 2.2 Composición de los ficheros GPX....................... 9 2.3 Librerías y aplicaciones compatibles con el formato GPX......... 10 3 Arquitectura de la librería Track Animation 13 3.1 Requerimientos básicos de Track Animation ................ 15 3.2 Librerías de terceros utilizadas ........................ 15 3.3 Módulo tracking.py ............................... 17 3.3.1 Clase ReadTrack ...........................