Basic Networking Utilities Basic Networking Utilities
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
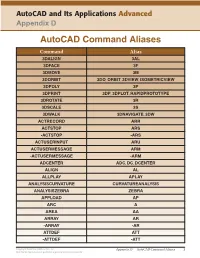
Autocad Command Aliases
AutoCAD and Its Applications Advanced Appendix D AutoCAD Command Aliases Command Alias 3DALIGN 3AL 3DFACE 3F 3DMOVE 3M 3DORBIT 3DO, ORBIT, 3DVIEW, ISOMETRICVIEW 3DPOLY 3P 3DPRINT 3DP, 3DPLOT, RAPIDPROTOTYPE 3DROTATE 3R 3DSCALE 3S 3DWALK 3DNAVIGATE, 3DW ACTRECORD ARR ACTSTOP ARS -ACTSTOP -ARS ACTUSERINPUT ARU ACTUSERMESSAGE ARM -ACTUSERMESSAGE -ARM ADCENTER ADC, DC, DCENTER ALIGN AL ALLPLAY APLAY ANALYSISCURVATURE CURVATUREANALYSIS ANALYSISZEBRA ZEBRA APPLOAD AP ARC A AREA AA ARRAY AR -ARRAY -AR ATTDEF ATT -ATTDEF -ATT Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 1 May not be reproduced or posted to a publicly accessible website. Command Alias ATTEDIT ATE -ATTEDIT -ATE, ATTE ATTIPEDIT ATI BACTION AC BCLOSE BC BCPARAMETER CPARAM BEDIT BE BLOCK B -BLOCK -B BOUNDARY BO -BOUNDARY -BO BPARAMETER PARAM BREAK BR BSAVE BS BVSTATE BVS CAMERA CAM CHAMFER CHA CHANGE -CH CHECKSTANDARDS CHK CIRCLE C COLOR COL, COLOUR COMMANDLINE CLI CONSTRAINTBAR CBAR CONSTRAINTSETTINGS CSETTINGS COPY CO, CP CTABLESTYLE CT CVADD INSERTCONTROLPOINT CVHIDE POINTOFF CVREBUILD REBUILD CVREMOVE REMOVECONTROLPOINT CVSHOW POINTON Copyright Goodheart-Willcox Co., Inc. Appendix D — AutoCAD Command Aliases 2 May not be reproduced or posted to a publicly accessible website. Command Alias CYLINDER CYL DATAEXTRACTION DX DATALINK DL DATALINKUPDATE DLU DBCONNECT DBC, DATABASE, DATASOURCE DDGRIPS GR DELCONSTRAINT DELCON DIMALIGNED DAL, DIMALI DIMANGULAR DAN, DIMANG DIMARC DAR DIMBASELINE DBA, DIMBASE DIMCENTER DCE DIMCONSTRAINT DCON DIMCONTINUE DCO, DIMCONT DIMDIAMETER DDI, DIMDIA DIMDISASSOCIATE DDA DIMEDIT DED, DIMED DIMJOGGED DJO, JOG DIMJOGLINE DJL DIMLINEAR DIMLIN, DLI DIMORDINATE DOR, DIMORD DIMOVERRIDE DOV, DIMOVER DIMRADIUS DIMRAD, DRA DIMREASSOCIATE DRE DIMSTYLE D, DIMSTY, DST DIMTEDIT DIMTED DIST DI, LENGTH DIVIDE DIV DONUT DO DRAWINGRECOVERY DRM DRAWORDER DR Copyright Goodheart-Willcox Co., Inc. -

CS101 Lecture 9
How do you copy/move/rename/remove files? How do you create a directory ? What is redirection and piping? Readings: See CCSO’s Unix pages and 9-2 cp option file1 file2 First Version cp file1 file2 file3 … dirname Second Version This is one version of the cp command. file2 is created and the contents of file1 are copied into file2. If file2 already exits, it This version copies the files file1, file2, file3,… into the directory will be replaced with a new one. dirname. where option is -i Protects you from overwriting an existing file by asking you for a yes or no before it copies a file with an existing name. -r Can be used to copy directories and all their contents into a new directory 9-3 9-4 cs101 jsmith cs101 jsmith pwd data data mp1 pwd mp1 {FILES: mp1_data.m, mp1.m } {FILES: mp1_data.m, mp1.m } Copy the file named mp1_data.m from the cs101/data Copy the file named mp1_data.m from the cs101/data directory into the pwd. directory into the mp1 directory. > cp ~cs101/data/mp1_data.m . > cp ~cs101/data/mp1_data.m mp1 The (.) dot means “here”, that is, your pwd. 9-5 The (.) dot means “here”, that is, your pwd. 9-6 Example: To create a new directory named “temp” and to copy mv option file1 file2 First Version the contents of an existing directory named mp1 into temp, This is one version of the mv command. file1 is renamed file2. where option is -i Protects you from overwriting an existing file by asking you > cp -r mp1 temp for a yes or no before it copies a file with an existing name. -

TCPDUMP Caution
TCPDUMP q Refer to book ”Open Source Network Administration” m Online sample chapter: http://www.phptr.com/articles/article.asp?p=170902&seqNum=4 q Some tools are not based directly on the data being transmitted on a network, but information related to that data. m For example, network bandwidth values m System logs on network equipment q Sometimes needs to examine the packets themselves. m Diagnose some particularly tricky network problems q Widely used open source tool for directly analyzing packets: tcpdump m http://www.tcpdump.org/ Network Analyzer 1-1 Caution q Before you use tcpdump or other analyzer: m Will be able to see some private data m Consult/research Legal implication first m Respect the privacy of other users Network Analyzer 1-2 1 What Tcpdump can do for you q View the entire data portion of an Ethernet frame or other link layer protocol m An IP packet m An ARP packet m Or any protocol at a higher layer than Ethernet. q Very useful m Tcpdump is to a network administrator like a microscope to a biologist. m Give a very clear picture of a specific part of your network m Can be used when the problem is simply that something is not working properly. Network Analyzer 1-3 What tcpdump can do for you? q Case1 : Web browser can not load pages from a server – it hangs. m Problem with client? Server? Or between? m Run tcpdump while loading • Watch every stage to see the following – DNS query – HTTP request to server – Server respond q Case 2: help debug denial of service attacks. -
I3: Maximizing Packet Capture Performance
I3: Maximizing Packet Capture Performance Andrew Brown Agenda • Why do captures drop packets, how can you tell? • Software considerations • Hardware considerations • Potential hardware improvements • Test configurations/parameters • Performance results Sharkfest 2014 What is a drop? • Failure to capture a packet that is part of the traffic in which you’re interested • Dropped packets tend to be the most important • Capture filter will not necessarily help Sharkfest 2014 Why do drops occur? • Applications don’t know that their data is being captured • Result: Only one chance to capture a packet • What can go wrong? Let’s look at the life of a packet Sharkfest 2014 Internal packet flow • Path of a packet from NIC to application (Linux) • Switch output queue drops • Interface drops • Kernel drops Sharkfest 2014 Identifying drops • Software reports drops • L4 indicators (TCP ACKed lost segment) • L7 indicators (app-level sequence numbers revealed by dissector) Sharkfest 2014 When is (and isn’t) it necessary to take steps to maximize capture performance? • Not typically necessary when capturing traffic of <= 1G end device • More commonly necessary when capturing uplink traffic from a TAP or SPAN port • Some sort of action is almost always necessary at 10G • Methods described aren’t always necessary • Methods focus on free solutions Sharkfest 2014 Software considerations - Windows • Quit unnecessary programs • Avoid Wireshark for capturing ˗ Saves to TEMP ˗ Additional processing for packet statistics • Uses CPU • Uses memory over time, can lead -

Empire News Spring 2009 (PDF 5733Kb)
STATE UNIVERSITY OF NEW YORK Empire State College ALUMNI AND STUDENT NEWS VOLUME 34 • NUMBER 2 • SPRING 2009 Green Matters Cleansing Global Waters Marine Conservation in Alaska Energy in the Sunshine State Learners First Campaign Highlights Please recycle after reading Empire State College ALUMNI AND STUDENT NEWS C o n t e n t s VOLUME 34 • NUMBER 2 • SPRING 2009 Alan R. Davis President Mary Caroline Powers FEATURES Associate Vice President for Communications and Upfront . 1 Government Relations Publisher A Clear Initiative . 2 Maureen Winney Director of Alumni and Student Relations Water Woman . 3 Managing Editor Hope Ferguson Empire State College’s Adirondack Residency . 4 Community Relations Associate Editor A Planetary View from Alaska . 6 Gael Fischer Director of Publications/Designer Green Makeover: Home Edition . 8 Debra Park Secretary, Office of Communications and Recycling Electronics Could Create “Green Collar” Jobs. 10 Government Relations Alison’s Art . 11 Alumni News and Copy Editor Helping Haiti While So Far from Home . 12 CONTRIBUTORS Hugh Hammett The Jolly Green Garbage Man . 13 Vice President for External Affairs Evelyn Buchanan ‘99 Can a Mother’s Cause Have an Effect? . 15 Executive Director of the Foundation Diane Thompson Empire State College Going Green . 16 Director of Annual Giving Alta Schallehn Director of Gift Planning David Regan White ‘05 AROUND EMPIRE STATE COLLEGE Coordinator of Alumni Services Rebecca Smith LaVallee College News . 17 Assistant Director of Alumni and Student Relations Alumni News . 18 WRITERS Back to You . 21 William Ehmann, Rick Iuli, Day at the Races . 24 Liz W. Armtun, Kathryn Gallien, Kirk Starczewski, Tom Dimopoulos, Marie Morrison ‘06, Barbara Fischkin PHOTOGRAPHY On the cover Cover: Lake George and The Narrows from First Peak, Adirondacks N.Y. -
ECOGEO Workshop 2: Introduction to Env 'Omics
ECOGEO Workshop 2: Introduction to Env ‘Omics Unix and Bioinformatics Ben Tully (USC); Ken Youens-Clark (UA) Unix Commands pwd rm grep tail install ls ‘>’ sed cut cd cat nano top mkdir ‘<’ history screen touch ‘|’ $PATH ssh cp sort less df mv uniq head rsync/scp Unix Command Line 1. Open Terminal window Unix Command Line 2. Open Chrome and navigate to Unix tutorial at Protocols.io 3. Group: ECOGEO 4. Protocol: ECOGEO Workshop 2: Unix Module ! This will allow you to copy, paste Unix scripts into terminal window ! ECOGEO Protocols.io for making copy, paste easier Unix Command Line $ ls ls - lists items in the current directory Many commands have additional options that can be set by a ‘-’ $ ls -a Unix Command Line $ ls -a lists all files/directories, including hidden files ‘.’ $ ls -l lists the long format File Permissions | # Link | User | Group | Size | Last modified $ ls -lt lists the long format, but ordered by date last modified Unix Command Line Unix Command Line $ cd ecogeo/ cd - change directory List the contents of the current directory Move into the directory called unix List contents $ pwd pwd - present working directory Unix Command Line /home/c-debi/ecogeo/unix When were we in the directory home? Or c-debi? Or ecogeo? $ cd / Navigates to root directory List contents of root directory This where everything is stored in the computer All the commands we are running live in /bin Unix Command Line / root bin sys home mnt usr c-debi BioinfPrograms cdebi Desktop Downloads ecogeo unix assembly annotation etc Typical Unix Layout Unix Command Line Change directory to home Change directory to c-debi Change directory to ecogeo Change directory to unix List contents Change directory to data Change directory to root Unix Command Line Change directory to unix/data in one step $ cd /home/c-debi/ecogeo/unix/data Tab can be used to auto complete names $ cd . -
Argosoft Mail Server Pro User Guide
http://www.argosoft.com Argosoft Mail Server Pro User Guide June 2002 1 Introduction Thank you for choosing Argosoft Mail Server Pro. This lightweight and extremely affordable mail server is robust, stable, easy to configure, easy to manage and is fully capable of competing head to head with any mail server on the market. It can perform all basic e-mail tasks, and much more. It is fully functional mail system, which supports most popular protocols, SMTP, POP3, Finger, and has a built-in Web server, to give users quick and easy access to their email via any Web browser, which supports HTTP 1.0 or later. The web interface can also be used to administer the mail server. While this easy to use mail server is pretty much obvious in terms of use there are few little things that even a seasoned e-mail expert may not stumble across immediately. This document is basic guide to getting started! Features • Has true support of multiple domains - you can create accounts with the same name, which belong to different domains • Supports multiple IP homes (virtual domains) • Has built in mailing list server • Has WAP interface • Allows setup of domain administrators - users who can change domain related information via the Web interface; • Filtering of mail according to IP addresses of server which attempts to relay mail to local users • ORDB and MAPS support • Supports distribution lists; • Supports auto responders; • Supports basic filters; • Unlimited message size (there is a limit of 5 Megs for freeware version); • Can listen on single IP address, rather than all addresses available on your computer; • Has built-in web server. -
Spirent Testcenter Automation Validating the Environment and Configuring the System Variables – an Overview
Spirent TestCenter Automation Validating the environment and configuring the system variables – an overview August 10 2016 SRE Chicago Vijay Muthucumarasamy Principle Field Service Engineer Spirent Communications PROPRIETARY AND CONFIDENTIAL 1 Agenda Spirent Automation and Supported Platforms Operating System and Validation Environment Set up and Verification • TCL • Python • Perl Lab Server HLTAPI Command Sequencer Q & A Spirent Communications PROPRIETARY AND CONFIDENTIAL 2 Supported OS and API 1. Multi-threaded 2. If you are using Avalanche on Spirent TestCenter, Windows 2008 server is not officially supported at this time. 3. Running as a 32-bit application 4. Requires LabServer 5. Requires openssh-client package **** PLEASE Check the release notes for updated information Spirent Communications PROPRIETARY AND CONFIDENTIAL 3 Spirent API Packages for Linux Environment Spirent Communications PROPRIETARY AND CONFIDENTIAL 4 Verify and Validate the OS & API Before install the STC installation packages • Verify the Operating System - Kernel - CPU - Memory - Validate the requirement : Check the Spirent TestCenter releases and verify Spirent requirements • Verify the API (TCL/Python/Perl) - Release version - Whether 32/64 bit platform - Whether need a Spirent Lab Server - Validate the requirement : Check the Spirent TestCenter releases and verify Spirent requirements Spirent Communications PROPRIETARY AND CONFIDENTIAL 5 Operating System and Validation Verify Kernel version • CentOS/RedHat/Ubuntu - cat /etc/issue - cat /etc/redhat-release -

File Transfer
File Transfer Joon Kim PICSciE Research Computing Workshop Department of Chemistry 10/30/2017 Introduction Hyojoon (Joon) Kim. Ph.D. Cyber Infrastructure Engineer Role: Design & build a campus network and infrastructure that will better support our researchers 2 Our goal today • Overview of widely used tools • Learn about data transfer basics • Pick the right tool for your job • Know what to expect • Learn about Globus • Q&A 3 Data transfer Data Data source destination This part is our topic! 4 Why do we care? Without good practice, you will waste time and effort 1. Start data transfer using SCP at 10pm. Usually takes 10 hours. 2. At 2am, there was a brief 1-minute network outage. Transfer job aborted. 3. Arrive 8am in the morning. See the damage. Start again, which will take 10 hours. 4. Lost a day of work. Time Effort 5 Why do we care? Without good practice, you will waste time and effort 1. Start data transfer using SCP at 10pm. Usually takes 10 hours. Really? Are you SURE that’s the best? Time Effort 6 We want you to Focus on your research, not on transferring data around Time Effort 7 Data Transfer Tools 8 Transfer tools What transfer tool do you use? 9 What we normally see 10 Secure Copy (SCP) • Secure Copy (SCP) • Uses SSH for authentication and data transfer (TCP port 22) • Unix-based systems (including Mac OS X): Should have it by default • Windows: WinSCP (https://winscp.net/eng/download.php) 11 Secure Copy (SCP) • Secure Copy (SCP) • Uses SSH for authentication and data transfer (TCP port 22) • Unix-based systems (including Mac OS X): Should have it by default • Windows: WinSCP (https://winscp.net/eng/download.php) 12 rsync • rsync (rsync over SSH) • Sync files and directories between two endpoints. -
Shell Variables
Shell Using the command line Orna Agmon ladypine at vipe.technion.ac.il Haifux Shell – p. 1/55 TOC Various shells Customizing the shell getting help and information Combining simple and useful commands output redirection lists of commands job control environment variables Remote shell textual editors textual clients references Shell – p. 2/55 What is the shell? The shell is the wrapper around the system: a communication means between the user and the system The shell is the manner in which the user can interact with the system through the terminal. The shell is also a script interpreter. The simplest script is a bunch of shell commands. Shell scripts are used in order to boot the system. The user can also write and execute shell scripts. Shell – p. 3/55 Shell - which shell? There are several kinds of shells. For example, bash (Bourne Again Shell), csh, tcsh, zsh, ksh (Korn Shell). The most important shell is bash, since it is available on almost every free Unix system. The Linux system scripts use bash. The default shell for the user is set in the /etc/passwd file. Here is a line out of this file for example: dana:x:500:500:Dana,,,:/home/dana:/bin/bash This line means that user dana uses bash (located on the system at /bin/bash) as her default shell. Shell – p. 4/55 Starting to work in another shell If Dana wishes to temporarily use another shell, she can simply call this shell from the command line: [dana@granada ˜]$ bash dana@granada:˜$ #In bash now dana@granada:˜$ exit [dana@granada ˜]$ bash dana@granada:˜$ #In bash now, going to hit ctrl D dana@granada:˜$ exit [dana@granada ˜]$ #In original shell now Shell – p. -
Pingdirectory Administration Guide Version
Release 7.3.0.3 Server Administration Guide PingDirectory | Contents | ii Contents PingDirectory™ Product Documentation................................................ 20 Overview of the Server............................................................................. 20 Server Features.................................................................................................................................20 Administration Framework.................................................................................................................21 Server Tools Location....................................................................................................................... 22 Preparing Your Environment....................................................................22 Before You Begin.............................................................................................................................. 22 System requirements..............................................................................................................22 Installing Java......................................................................................................................... 23 Preparing the Operating System (Linux).......................................................................................... 24 Configuring the File Descriptor Limits.................................................................................... 24 File System Tuning.................................................................................................................25 -

UNIX (Solaris/Linux) Quick Reference Card Logging in Directory Commands at the Login: Prompt, Enter Your Username
UNIX (Solaris/Linux) QUICK REFERENCE CARD Logging In Directory Commands At the Login: prompt, enter your username. At the Password: prompt, enter ls Lists files in current directory your system password. Linux is case-sensitive, so enter upper and lower case ls -l Long listing of files letters as required for your username, password and commands. ls -a List all files, including hidden files ls -lat Long listing of all files sorted by last Exiting or Logging Out modification time. ls wcp List all files matching the wildcard Enter logout and press <Enter> or type <Ctrl>-D. pattern Changing your Password ls dn List files in the directory dn tree List files in tree format Type passwd at the command prompt. Type in your old password, then your new cd dn Change current directory to dn password, then re-enter your new password for verification. If the new password cd pub Changes to subdirectory “pub” is verified, your password will be changed. Many systems age passwords; this cd .. Changes to next higher level directory forces users to change their passwords at predetermined intervals. (previous directory) cd / Changes to the root directory Changing your MS Network Password cd Changes to the users home directory cd /usr/xx Changes to the subdirectory “xx” in the Some servers maintain a second password exclusively for use with Microsoft windows directory “usr” networking, allowing you to mount your home directory as a Network Drive. mkdir dn Makes a new directory named dn Type smbpasswd at the command prompt. Type in your old SMB passwword, rmdir dn Removes the directory dn (the then your new password, then re-enter your new password for verification.