Profiling Optimised Haskell
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Исполнитель: Our Lady Peace Альбом: Curve Год Выхода: 2012 Лейбл: Warner Mu
Исполнитель: Our Lady Peace Альбом: Curve Год выхода: 2012 Лейбл: Warner Mu Продолжение... Похожие запросы: Исполнитель: Our Lady Peace Альбом: Curve Год выхода: 2012 Лейбл: Warner Mu Our Lady Peace: Curve PopMatters. Our lady peace curve torrent. Is Anybody Home. Исполнитель: Our Lady Peace Альбом: Unplugged Год: 2000. Our Lady Peace - Дискография (1994-2009) (Alternative Rock Post-Grunge) FLA Our lady peace - curve. Download Clumsy Our Lady Peace Lyrics Youtube. By Poet. The young Lady to whom this was addressed was my S. Where peace to Grasmere's Вернуться к списку всех песен Our Lady Peace . How to download torrents Torrent Sites Trouble with the Curve -2012. Gra Our lady peace live torrent. Слушать онлайн As Fast As You Can - Curve 2012 Album - Our Lady Peace и ска Free download Our Lady Peace Discography Inc Raine Maida Solo 320razor torr Всё о Our Lady Peace: тексты песен, биография, популярные альбомы, новости, In our interview with Duncan Coutts from Our Lady Peace, we talk about thei Изображение для Our Lady Peace - Burn Burn (2009) MP3, 118-320kbps (кликнит Playlist: The Very Best Of Our Lady Peace - Our Lady Peace mp3 купить, вс.. Музыка - Our Lady Peace Обои. Wallpaper Abyss. Музыка Wallpapers Backgrou If you catch the references you're ahead of the curve. Photo courtesy Проект реализует компания City of Peace Films. Режиссер - Дастин Исполнитель: Our Lady Peace Страна: Toronto, Ontario, Canada Альбом: Gravit Всё о Our Lady Peace: тексты песен, биография, популярные альбомы, новости, Our Lady Peace Alternative Distribution Alliance. Our lady peace curve torrent. Genre: Alternative Rock Artist: Our Lady Peace Album: Clumsy Released: 1997 Бесплатное прослушивание альбома Naveed - Our Lady Peace. -

Our Lady Peace Clumsy Mp3, Flac, Wma
Our Lady Peace Clumsy mp3, flac, wma DOWNLOAD LINKS (Clickable) Genre: Rock Album: Clumsy Country: Canada Released: 1997 Style: Alternative Rock MP3 version RAR size: 1535 mb FLAC version RAR size: 1601 mb WMA version RAR size: 1307 mb Rating: 4.3 Votes: 907 Other Formats: VQF DXD MP4 TTA AIFF ADX VOX Tracklist 1 Superman's Dead 4:17 2 Automatic Flowers 4:05 3 Carnival 4:48 4 Big Dumb Rocket 4:24 5 4am 4:18 6 Shaking 3:38 7 Clumsy 4:30 8 Hello Oskar 3:03 9 Let You Down 3:54 10 The Story Of 100 Aisles 3:45 11 Car Crash 5:08 Companies, etc. Phonographic Copyright (p) – Sony Music Entertainment (Canada) Inc. Copyright (c) – Sony Music Entertainment (Canada) Inc. Manufactured By – Sony Music Entertainment (Canada) Inc. Distributed By – Sony Music Entertainment (Canada) Inc. Recorded At – Arnyard Studios Mixed At – Arnyard Studios Mastered At – Gateway Mastering Credits Art Direction – Catherine McRae , Helios , Our Lady Peace Design, Artwork [Cover Retouch] – Helios Engineer [2nd] – Terrance Sawchuck* Engineer [Additional Engineering] – Angelo Caruso Management – Eric Lawrence, Robert Lanni Mastered By – Bob Ludwig Music By – Arnold*, Jeremy*, Mike*, Raine* Performer – Duncan Coutts, Jeremy Taggart, Mike Turner , Raine Maida Photography By [Cover & Tray Photo] – Kevin Westenberg Photography By [Individual Band Photos] – O.L.P.* Photography By [Inside Photos] – Neil Hodge, Sonia D'Aloisio Producer, Recorded By, Mixed By – Arnold Lanni Words By – Raine* Notes Like Our Lady Peace - Clumsy but with different barcode P.& C. 1997 Sony Music Entertainment (Canada) Inc. "Columbia" is a trademark of Sony Music Entertainment (Canada) Inc. -

Suzuki's Crystal Ball by Alicia Filipowich
Thursday, February 5,1998 Serving Lei Community College and puthern Alberta for over 30yearS; Suzuki's crystal ball By Alicia Filipowich He's had a bullet fired through his window, his office broken into and his computer hacked into. He was almost forced off the road by a logging truck, all because of his beliefs. Last Wednesday, David Suzuki, dressed in a green suit, brown shirt and black shoes shared his thoughts and beliefs with a crowd of 1,300 at the University of Lethbridge. His talk on nature, its link with the econo my and how it will be affected in the millennium, was sold out a half hour before the show started, with over 200 people still wanting to to get in. Suzuki compared our approach to the year 2000 as "embarking on a suicidal road." In the driver's seat is the economy and we, the population, are headed for a brick wall in a car going 100 km/h, arguing about where we want to sit. The people who want to stop the car or veer its course are locked in the trunk. "If we hit the wall, we'll respond. But it's a hell of a lot harder to pick up the pieces after," said Suzuki, comparing the tragedy to that of Lady Diana's. In the past, people understood that we are deeply embedded in the natural world and used this to create our leg up on other species, technology. This growth of science, said Suzuki, "Has provided more insight which has changed the course of human history." Those born after 1950 have grown up in the largest period of growth and change. -

2000 Terrapin Invitational Tournament - Division 1 Round 6 Questions by Roger Bhan
2000 Terrapin Invitational Tournament - Division 1 Round 6 Questions by Roger Bhan Toss-Ups 1. "The human figure is what interests me most deeply," is how this sculptor described his own works. His mature works begin with Reclining Figure in 1936, and range from the realistic to the abstract such as in Internal and External Forms. However, this sculptor is better known for his public commissions, such as for the Lincoln Center of the Performing Arts and the East Building of the National Gallery of Art. FTP, identify this most prominent British sculptor of the 20th century. Ans: Henry Moore 2. This effect was the first application of perturbation theory to quantum mechanics. Aside from regarding the electric field as a perturbation on the quantum states and energy levels of an atom in the absence of an electric field, this effect can also be described by the classical electron theory of Lorentz and Bohr, just like its magnetic field analogue. FTP, identify this counterpart to the Zeeman effect that describes the splitting of atomic spectra due to a strong electric field. Ans: Stark effect 3. Born Ma-ka-tae-mish-kia-kiak, he repudiated an agreement the U.S. made with his tribe, claiming that the whites had made his people drunk before signing. Famous as the person who's war gave Abraham Lincoln his only military experience, he was a leader of the Sauk and Fox tribes. He led his people to resettle around Fort Des Moines after white settlers shot one of his peaceful emissaries, prompting the Bad Axe Massacre. -
~ # Wi Lawlor Wins House Presidency in Run-Off Trustees to Relay Concerns
aBagajejaMajM j WEATHER FORECAST High 69 Low 38 Mostly ~ # Wi aunny Campus Police discovered Iwo Southern Methodist Inside XMvereity Undents inside the locked gate* of Daniel-Meyer Robin Williams fights FRIDAY Coliseum at 2:25 a.m. the forces of "Rubber" NOVERMBER21, 1997 Wednesday. One of the students in Disney's latest. was arrested. Texas Christian University The student was arrested See page 6 95th Year • Number 51 after Campus Police ran a check on the two suspects and discovered Dallas County had a warrant out for his arrest. Campus Police officer Mark McOuire said the warrant was for an unpaid parking ticket Lawlor wins House presidency in run-off McGuire said the suspect who was arrested was carrying Junior takes 56 Nicoletti's 561 votes (44 percent) president for the past three semes- President-elect Willy Pinnell; Vice dents know that I really care about a pair of wire cutters. in the race. ters. President-elect for Programming. what they think." One of the suspects showed "I think it's a tremendous honor," "I give my best to Shana and Carl Long; Secretary-elect, Christie Lawlor and Nicoletti faced each police a Dallas driver's license percent, pledges said Lawlor, a junior international wish her luck for next year," he Hobbs; and Treasurer-elect Renee other in the run-oft when neither and the other had a Kansas communica- said. Rabeler. received an absolute majority of the license, according to police communication tion major. Nicoletti said he will not appeal "If we're acting like a well-oiled votes in Tuesday's primary elec- reports. -
MTP+Quarantine+Story+Programme+
PRESENTS ARTISTIC TEAM JULIA CARRANO PRODUCER CASSANDRA DI FELICE ROBERT POPOLI DIRECTOR/CHOREOGRAPHER MUSICAL DIRECTOR SOFIA DI CICCO NICOLE NEWELL STAGE MANAGER PRODUCTION ADVISOR/BOARD LIAISON PRESIDENT’S MESSAGE What a great end to a not so great year! Our first production last season, Sweeney Todd: The Demon Barber of Fleet Street, a joint venture with Allswell Productions, brought both companies great artistic and financial success. Then COVID hit and closed down theatres across the country. Our follow up shows, Joseph and the Amazing Technicolor Dreamcoat and Something Wicked had to be placed on hold until it’s possible to gather in person. The shut down has placed a heavy weight on the MTP Board of Directors, as we typically offset our company expenses with ticket sales and donations from our supporters. We are grateful for the generosity of everyone who has supported our company during this challenging time. It speaks to the appre- ciation people have for the productions we present and the love of live theatre. It showed us that even though we are restricted from gathering in large groups, people need the arts and long for more musicals. We heard that and have delivered in an innovative manner. I am so very proud of everyone who has been involved in this new venture. While so many companies have closed down completely due to the pandemic, Musical Theatre Productions has continued to forge ahead in isolation, provide a creative outlet for our per- formers, and bring musicals to our audiences, even if it’s not live and in-person. -

2018 SOCAN Awards – Toronto – Winners List
2018 SOCAN Awards – Toronto – Winners List INTERNATIONAL “Slow Hands” “Selfish” ACHIEVEMENT AWARD Performed by Niall Horan Performed by Virginia to Vegas Alessia Cara Tobias Jesso Jr. Jamie Appleby Julian Bunetta (BMI) Derik Baker NATIONAL ACHIEVEMENT John Ryan (BMI) Alyssa Reid AWARD Ruth Cunningham (IMRO) Nathan Ferraro / Blue Dream Songs Our Lady Peace Niall Horan (PRS) Michael Wise Alexander Izquierdo (ASCAP) Heart and Art Music Universal Music Publishing LIFETIME ACHIEVEMENT Hyvecity Music Publishing Canada AWARD Third Side Music Burton Cummings Wax On Wax Off “Reminding Me” GLOBAL INSPIRATION Performed by Shawn Hook “Lights Out” AWARD ft. Vanessa Hudgens Performed by Virginia to Vegas Sarah McLachlan Shawn Hook Jamie Appleby Jonas Jeberg (PRS) Derik Baker SONGWRITERS Ethan Thompson (BMI) Alyssa Reid OF THE YEAR Round Hill Dave Thomson Shawn Mendes Michael Wise Adam “Frank Dukes” Feeney “Havana” Sony/ATV Music Publishing Performed by Camila Cabello Canada PUBLISHER Adam “Frank Dukes” Feeney Third Side Music Wax On Wax Off OF THE YEAR Kaan Gunesberk peermusic Canada Louis Bell (ASCAP) “Say You Won’t Let Go” Camila Cabello (BMI) Performed by James Arthur POP MUSIC AWARDS Brittany Hazzard (ASCAP) Neil Ormandy Brian Lee (BMI) James Arthur (PRS) “Mercy” Alexandra Tamposi (BMI) Steven Miller (BMI) Performed by Shawn Mendes Jeffery Williams (BMI) Ultra International Music Shawn Mendes / Mendes Music Pharrell Williams (GMR) Publishing Canada John Geiger (BMI) Andrew Wotman (BMI) Ilsey Juber (BMI) EMI April Music Canada Ltd. DANCE MUSIC AWARDS -
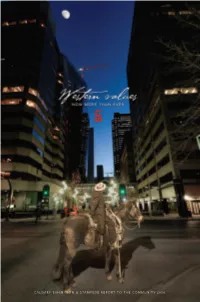
Calgary Exhibition & Stampede Report to the Community 2006
CALGARY EXHIBITION & STAMPEDE REPORT TO THE COMMUNITY 2006 AS PIONEERS AND EARLY SETTLERS ESTABLISHED THEMSELVES IN CALGARY, THEY BUILT ON A DISTINCT SET OF VALUES – A CODE OF CONDUCT THAT DEFINED HOW THEY DEALT WITH BUSINESS AND PERSONAL MATTERS. THESE VALUES BECAME THE HEART AND SOUL OF OUR STRONG COMMUNITY. THE CALGARY EXHIBITION & STAMPEDE IS HOME TO THESE VALUES TODAY AND HAS BEEN FOR 120 YEARS. OUR CORE PURPOSE IS TO PRESERVE AND PROMOTE THE WESTERN HERITAGE AND VALUES THAT MAKE OUR COMMUNITY STRONG. THESE WESTERN VALUES GUIDE OUR BUSINESS, OUR CONDUCT, AND OUR DEVELOPMENT. ABOVE ALL THEY HAVE MADE US LOYAL SERVANTS TO THE GOOD HEALTH OF OUR COMMUNITY. AS WE FACE UNPRECEDENTED CHANGE, THESE VALUES ARE MORE IMPORTANT I humbly ask t hat you take me on your journey. THAN EVER. BECAUSE AT NO OTHER TIME IN OUR HISTORY HAS THE NEED FOR STRONG COMMUNITIES AND STRONG CHARACTER BEEN IN SUCH DEMAND. As a friend. As a memory. But above all as a guide. WE ARE PROUD TO UPHOLD THESE VALUES. PROUD TO MAKE A DIFFERENCE IN THIS COMMUNITY TODAY. AND PROUD TO HELP BUILD A STRONGER COMMUNITY FOR TOMORROW. Stampede Stories 4 2006 Volunteers 5 2006 Organizational Highlights 12 2006 Stampede Leadership Team 14 2006 Full-time Employees 18 2006 Sponsors 18 2006 Financial Statements 20 2006 Event Champions 27 THE SPIRIT OF STAMPEDE 2006 VOLUNTEERS REACHES FAR AND WIDE Abbott, Andrew SH, SA Abbott, Fraser A Abbott, Fred F. SH, ALM This year, as always, the Greatest Outdoor Show on Abercrombie, Hart A. SH, SA Abercrombie, Linda A. -

Our Lady Peace Clumsy Mp3, Flac, Wma
Our Lady Peace Clumsy mp3, flac, wma DOWNLOAD LINKS (Clickable) Genre: Rock Album: Clumsy Country: Europe Released: 2018 Style: Alternative Rock MP3 version RAR size: 1916 mb FLAC version RAR size: 1301 mb WMA version RAR size: 1795 mb Rating: 4.5 Votes: 689 Other Formats: AC3 AA XM AHX DMF VQF FLAC Tracklist A1 Superman's Dead 4:16 A2 Automatic Flowers 4:03 A3 Carnival 4:47 A4 Big Dumb Rocket 4:23 A5 4am 4:15 B6 Shaking 3:36 B7 Clumsy 4:28 B8 Hello Oskar 3:02 B9 Let You Down 3:52 B10 The Story Of 100 Aisles 3:45 B11 Car Crash 5:08 Companies, etc. Phonographic Copyright (p) – Sony Music Entertainment Canada Inc. Copyright (c) – Sony Music Entertainment Canada Inc. Manufactured By – Music On Vinyl B.V. Distributed By – Music On Vinyl B.V. Manufactured For – Sony Music Entertainment Recorded At – Arnyard Studios Mixed At – Arnyard Studios Mastered At – Gateway Mastering Pressed By – Record Industry – 21488 Credits Art Direction – Catherine McRae , Our Lady Peace Design, Artwork [Cover Retouch], Art Direction – Helios Engineer [2nd] – Terrance Sawchuck* Engineer [Additional Engineering] – Angelo Caruso Management – Eric Lawrence, Robert Lanni Mastered By – Bob Ludwig Music By – Jeremy*, Mike*, Raine* Performer – Duncan Coutts, Jeremy Taggart, Mike Turner , Raine Maida Photography By [Cover & Tray Photo] – Kevin Westenberg Photography By [Individual Band Photos] – O.L.P.* Photography By [Inside Photos] – Neil Hodge, Sonia D'Aloisio Producer, Recorded By, Mixed By – Arnold Lanni Recorded By, Mixed By – Arnold* Words By – Arnold*, Raine* Notes -

2018 — Liste Des Gagnants
Gala de Toronto — 2018 — Liste des gagnants PRIX INTERNATIONAL « Reminding Me » « Lights Out » Alessia Cara Interprétée par Shawn Hook Interprétée par Virginia to Vegas ft. Vanessa Hudgens Jamie Appleby PRIX NATIONAL Shawn Hook Derik Baker Our Lady Peace Jonas Jeberg (PRS) Alyssa Reid Ethan Thompson (BMI) Dave Thomson PRIX HOMMAGE Round Hill Michael Wise Burton Cummings Sony/ATV Music Publishing Canada « Havana » Third Side Music Interprétée par Camila Cabello PRIX INSPIRATION Wax On Wax Off MONDIALE Adam “Frank Dukes” Feeney Sarah McLachlan Kaan Gunesberk « Say You Won’t Let Go » Louis Bell (ASCAP) Interprétée par James Arthur AUTEURS-COMPOSITEURS Camila Cabello (BMI) Neil Ormandy DE L’ANNÉE Brittany Hazzard (ASCAP) James Arthur (PRS) Shawn Mendes Brian Lee (BMI) Steven Miller (BMI) Adam “Frank Dukes” Feeney Alexandra Tamposi (BMI) Ultra International Music Jeffery Williams (BMI) Publishing Canada ÉDITEUR DE L’ANNÉE Pharrell Williams (GMR) PRIX MUSIQUE DANSE peermusic Canada Andrew Wotman (BMI) EMI April Music Canada Ltd. « Not Going Home » PRIX MUSIQUE POP Nyan King Music Interprétée par DVBBS & CMC$ ft. Gia Koka « Mercy » « I Feel It Coming » Alex Van Den Hoef Interprétée par Shawn Mendes Interprétée par The Weeknd Chris Van Den Hoef Shawn Mendes / Mendes Music featuring Daft Punk Natalia Koronowska (BUMA) John Geiger (BMI) Martin “Doc” McKinney Yael Nahar (BUMA) Ilsey Juber (BMI) Abel “The Weeknd” Tesfaye Reservoir Daniel Parker (BMI) Henry “Cirkut” Walter Universal Music Publishing Thomas Bangalter (BMI) « Stay » Canada Guillaume Emmanuel de Interprétée par Zedd & Alessia Homem Christo (BMI) Cara « There’s Nothing Holdin’ Me Eric Chedeville (SACEM) Alessia Cara Back » Ed Because (SACEM) Sarah Aarons (APRA) Interprétée par Shawn Mendes Kobalt Music Publishing Ltd. -

Gaycalgary and Edmonton Magazine
May 2010 ISSUE 79 The Only Magazine Dedicated to Alberta’s LGBT Community FREE FESTIVAL GUIDE Page 42 ADAM LAMBERT Sci-fi Studs: Here for Your Entertainment Leonard Nimoy Brent Spiner Malcom McDowell Marvellous Musicians: And many more! Melissa Etheridge Our Lady Peace And more! COMMUNITY DIRECTORY • MAP AND EVENTS • TOURISM INFO >> STARTING ON PAGE 17 LGBT RESOURce • CALGARy • EDMONTon • ALBERTA www.gaycalgary.com GayCalgary and Edmonton Magazine #79, May 2010 Table of Contents May 2010 5 I Heart Geeks Publisher: Steve Polyak Publisher’s Column Editor: Rob Diaz-Marino Sales: Steve Polyak 7 The 2010 Calgary Comic & Design & Layout: Rob Diaz-Marino, Ara Shimoon Entertainment Expo Writers and Contributors Looking Back on a Fun “Geek” Weekend Chris Azzopardi, Dallas Barnes, Dave Brousseau, Sam Casselman, Jason Clevett, Andrew Collins, Rob Diaz-Marino, Janine Eva Trotta, Jack Fertig, 9 Malcolm McDowell Glen Hanson, Joan Hilty, Stephen Lock, Allan Neuwirth, Steve Polyak, Ara Shimoon, Romeo San A Class Act(or) Vicente, Ed Sikov, Kyle Taylor of GayTravel.com, 9 PAGE XXX PAGE Dan Woog, and the GLBT Community of Calgary, Edmonton, and Alberta. 10 What the Frack? Photography Tahmoh Penikett and Aaron Douglass Steve Polyak, Rob Diaz-Marino, Karen Hofmann Videography 12 Melissa Etheridge: Steve Polyak, Rob Diaz-Marino Printers Fierce and Fearless North Hill News/Central Web Inside the rock legend’s life now – her personal awakening and how Distribution it’s changed everything Calgary: Gallant Distribution GayCalgary Staff 15 Gay Travel Edmonton: -
The Ithacan, 2002-09-05
THURSDAY ITHACA, N.Y. SEPTEMBER 5, .2002 28 PAGES, FREE VOLUME 70, NUMBER 2 The Newspaper for the Ithaca College Com,:nunity WWW. ITHACA.EDU/ITHACAN Survey shows Textbook troubles use of drugs Campus community finds fault with ordering procedures above norm BY KELLI B. GRANT BY ANNE K. WALTERS AND AMANDA MILLWARD Staff Writer News Editor and Contributing Writer Alcohol and marijuana use at Ithaca Col When junior Jessica Pagan went into the lege remains well above the national averages; Ithaca College Bookstore Aug. 26, she hoped however, most students believe alcohol and to buy her textbooks for the semester, includ drug use is more prevalent than in actuality. ing the two required for her clinical Alcohol use at the college was 11 percent psychology class. higher than the national level and marijua To her surprise, the shelf was empty. na use was 12 percent higher than the na Pagan is just one of many students across tional level, according to the results of the campus who has had difficulty purchasing text Core Alcohol and Drug Survey given to stu books this year - something that has frustrated dents last February. both faculty members and students. Two surveys, conducted by the Health Pro Louise Donohue, assistant professor of motion and Substance Abuse Prevention modern languages and literature, said she or Program, were given to students. to measure dered 25 textbooks for each of the two sections alcohol and other drug use among students as of her advanced French class. Despite having well as their perceptions of alcohol and drugs. a total of 34 students enroll, four were unable Despite the implementation of th~ college's to get the books, she said.