Learning the Vi and Vim Editors Other Resources from O’Reilly
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

How to Create an Android Application Using Eclipse on Windows 7
How to Create an Android Application using Eclipse on Windows 7 Kevin Gleason 11/11/11 This application note is design to teach the reader how to setup an Android Development Environment on a Windows 7 Computer using eclipse and how to create an Android application. It first explains all of the software and hardware requirements and explains to the reader how to setup and install each of the required programs. It then explains how to design and code an Android application. Finally it explains how to use the Android Virtual Device to test the application. Table of Contents 1 Key Terms ..................................................................................................................................... 2 2 Objective ....................................................................................................................................... 2 3 System Requirements ................................................................................................................... 2 4 Installation and Configuration ...................................................................................................... 3 4.1 Download and Configure Eclipse IDE .................................................................................... 3 4.2 Download Android SDK ......................................................................................................... 4 4.3 Install ADT plugin for eclipse ................................................................................................. 5 4.4 Configure -
Process and Memory Management Commands
Process and Memory Management Commands This chapter describes the Cisco IOS XR software commands used to manage processes and memory. For more information about using the process and memory management commands to perform troubleshooting tasks, see Cisco ASR 9000 Series Aggregation Services Router Getting Started Guide. • clear context, on page 2 • dumpcore, on page 3 • exception coresize, on page 6 • exception filepath, on page 8 • exception pakmem, on page 12 • exception sparse, on page 14 • exception sprsize, on page 16 • follow, on page 18 • monitor threads, on page 25 • process, on page 29 • process core, on page 32 • process mandatory, on page 34 • show context, on page 36 • show dll, on page 39 • show exception, on page 42 • show memory, on page 44 • show memory compare, on page 47 • show memory heap, on page 50 • show processes, on page 54 Process and Memory Management Commands 1 Process and Memory Management Commands clear context clear context To clear core dump context information, use the clear context command in the appropriate mode. clear context location {node-id | all} Syntax Description location{node-id | all} (Optional) Clears core dump context information for a specified node. The node-id argument is expressed in the rack/slot/module notation. Use the all keyword to indicate all nodes. Command Default No default behavior or values Command Modes Administration EXEC EXEC mode Command History Release Modification Release 3.7.2 This command was introduced. Release 3.9.0 No modification. Usage Guidelines To use this command, you must be in a user group associated with a task group that includes appropriate task IDs. -
UNIX Workshop Series: Quick-Start Objectives
Part I UNIX Workshop Series: Quick-Start Objectives Overview – Connecting with ssh Command Window Anatomy Command Structure Command Examples Getting Help Files and Directories Wildcards, Redirection and Pipe Create and edit files Overview Connecting with ssh Open a Terminal program Mac: Applications > Utilities > Terminal ssh –Y [email protected] Linux: In local shell ssh –Y [email protected] Windows: Start Xming and PuTTY Create a saved session for the remote host name centos.css.udel.edu using username Connecting with ssh First time you connect Unix Basics Multi-user Case-sensitive Bash shell, command-line Commands Command Window Anatomy Title bar Click in the title bar to bring the window to the front and make it active. Command Window Anatomy Login banner Appears as the first line of a login shell. Command Window Anatomy Prompts Appears at the beginning of a line and usually ends in $. Command Window Anatomy Command input Place to type commands, which may have options and/or arguments. Command Window Anatomy Command output Place for command response, which may be many lines long. Command Window Anatomy Input cursor Typed text will appear at the cursor location. Command Window Anatomy Scroll Bar Will appear as needed when there are more lines than fit in the window. Command Window Anatomy Resize Handle Use the mouse to change the window size from the default 80x24. Command Structure command [arguments] Commands are made up of the actual command and its arguments. command -options [arguments] The arguments are further broken down into the command options which are single letters prefixed by a “-” and other arguments that identify data for the command. -

How to Dump and Load
How To Dump And Load Sometimes it becomes necessary to reorganize the data in your database (for example, to move data from type i data areas to type ii data areas so you can take advantage of the latest features)or to move parts of it from one database to another. The process for doping this can be quite simple or quite complex, depending on your environment, the size of your database, what features you are using, and how much time you have. Will you remember to recreate the accounts for SQL users? To resotre theie privileges? Will your loaded database be using the proper character set and collations? What about JTA? Replication? etc. We will show you how to do all the other things you need to do in addition to just dumping and loading the data in your tables. 1 How To Dump and Load gus bjorklund head groundskeeper, parmington foundation 2 What do we mean by dumping and loading? • Extract all the data from a database (or storage area) • Insert the data into a new database (or storage area) • Could be entire database or part 3 Why do we dump and load? 4 Why do we dump & load? • To migrate between platforms • To upgrade OpenEdge to new version • To repair corruption • To “improve performance” • To change storage area configuration • To defragment or improve “scatter” • To fix a “long rm chain” problem • Because it is October 5 Ways to dump and load • Dictionary • 4GL BUFFER-COPY • Binary • Replication triggers (or CDC) • Table partitioning / 4GL • Incremental by storage area 6 Binary Dump & Load • binary dump files – not "human readable" -

Practical C Programming, 3Rd Edition
Practical C Programming, 3rd Edition By Steve Oualline 3rd Edition August 1997 ISBN: 1-56592-306-5 This new edition of "Practical C Programming" teaches users not only the mechanics or programming, but also how to create programs that are easy to read, maintain, and debug. It features more extensive examples and an introduction to graphical development environments. Programs conform to ANSI C. 0 TEAM FLY PRESENTS Table of Contents Preface How This Book is Organized Chapter by Chapter Notes on the Third Edition Font Conventions Obtaining Source Code Comments and Questions Acknowledgments Acknowledgments to the Third Edition I. Basics 1. What Is C? How Programming Works Brief History of C How C Works How to Learn C 2. Basics of Program Writing Programs from Conception to Execution Creating a Real Program Creating a Program Using a Command-Line Compiler Creating a Program Using an Integrated Development Environment Getting Help on UNIX Getting Help in an Integrated Development Environment IDE Cookbooks Programming Exercises 3. Style Common Coding Practices Coding Religion Indentation and Code Format Clarity Simplicity Summary 4. Basic Declarations and Expressions Elements of a Program Basic Program Structure Simple Expressions Variables and Storage 1 TEAM FLY PRESENTS Variable Declarations Integers Assignment Statements printf Function Floating Point Floating Point Versus Integer Divide Characters Answers Programming Exercises 5. Arrays, Qualifiers, and Reading Numbers Arrays Strings Reading Strings Multidimensional Arrays Reading Numbers Initializing Variables Types of Integers Types of Floats Constant Declarations Hexadecimal and Octal Constants Operators for Performing Shortcuts Side Effects ++x or x++ More Side-Effect Problems Answers Programming Exercises 6. -

CIS 90 - Lesson 2
CIS 90 - Lesson 2 Lesson Module Status • Slides - draft • Properties - done • Flash cards - NA • First minute quiz - done • Web calendar summary - done • Web book pages - gillay done • Commands - done • Lab tested – done • Print latest class roster - na • Opus accounts created for students submitting Lab 1 - • CCC Confer room whiteboard – done • Check that headset is charged - done • Backup headset charged - done • Backup slides, CCC info, handouts on flash drive - done 1 CIS 90 - Lesson 2 [ ] Has the phone bridge been added? [ ] Is recording on? [ ] Does the phone bridge have the mike? [ ] Share slides, putty, VB, eko and Chrome [ ] Disable spelling on PowerPoint 2 CIS 90 - Lesson 2 Instructor: Rich Simms Dial-in: 888-450-4821 Passcode: 761867 Emanuel Tanner Merrick Quinton Christopher Zachary Bobby Craig Jeff Yu-Chen Greg L Tommy Eric Dan M Geoffrey Marisol Jason P David Josh ? ? ? ? Leobardo Gabriel Jesse Tajvia Daniel W Jason W Terry? James? Glenn? Aroshani? ? ? ? ? ? ? = need to add (with add code) to enroll in Ken? Luis? Arturo? Greg M? Ian? this course Email me ([email protected]) a relatively current photo of your face for 3 points extra credit CIS 90 - Lesson 2 First Minute Quiz Please close your books, notes, lesson materials, forum and answer these questions in the order shown: 1. What command shows the other users logged in to the computer? 2. What is the lowest level, inner-most component of a UNIX/Linux Operating System called? 3. What part of UNIX/Linux is both a user interface and a programming language? email answers to: [email protected] 4 CIS 90 - Lesson 2 Commands Objectives Agenda • Understand how the UNIX login • Quiz operation works. -

Why Is C. Diff So Hard to Culture and Kill?
Why is C. diff so hard to culture and kill? Clostridium difficile, commonly referred to as C. diff, is the #1 nosocomial infection in hospitals (it actually kicked staph infections out of the top spot). At Assurance, we test for this organism as part of our Gastrointestinal (GI) panel. C. diff is a gram-positive anaerobe, meaning it does not like oxygen. Its defensive mechanism is sporulation – where it essentially surrounds itself with a tough outer layer of keratin and can live in water, soil, etc. for over a decade. For reference, anthrax is another organism that sporulates. Once C. diff sporulates, it is very hard to kill and in fact, bleach is one of the only disinfectants that work. Unfortunately, it can spread quickly throughout hospitals. Spores of C. diff are found all over hospital surfaces and even in some hospital water systems. It’s the most threatening for those who are immunocompromised or the elderly, who are the most likely to end up with C. diff infections. With our PCR testing, we’re looking for the C. diff organism itself but we’re also looking at the production of toxin. Unless it produces toxins A AND B together OR toxin B, C. diff doesn’t cause severe disease. Many babies are exposed to it during birth or in the hospitals and may test positive on our GI panel. Unless they are expressing those toxins (both toxin A&B or just toxin B) it is not considered a clinical infection. Studies show that toxins A&B together causes infection, as well as toxin B. -

Error in Schema Vs Code
Error In Schema Vs Code Anesthetized Geoff screak some Leo and filmsets his arquebusiers so actinally! Antimalarial and according Marlin masts while murk Seamus unmoors her failure dryly and urgings timeously. Gonorrheic and laurelled Garfield never catalyse his asps! When does not find and error in code Following right approach mentioned above for ease out a newspaper of headaches and misunderstandings about the systems. Create a secure password using our generator tool. Check out our get started guides for new users. Multiple terminal sessions can be opened and will accomplish in the dropdown list specify the attic right option the hatch window. With rank above configuration we connect now attend our schema. Copy the comment line pump and paste it pick your spec file. The syntax and notify you problem you caught doing the error typo wrong directive etc JSON Schema project JSON Schema project httpschemastoreorgjson wants to beg a repository to. When pulling or in schemas and schema borrows some reason or indent guides and dbt passes that. Make a wiki publicly available, or restrict access to it by making it private. Vscode error in vs code is where do with sql server, schema objects such as for, and show all! Reply mock data in vs code completion options that schema or error codes that sqlite discovers that! At all editors including no longer used in the title, vs code in. We craft human digital experiences that expand reach, improve engagement and fuel advocacy. Personal portfolio and assorted projects of Joshua Tzucker. Cloud Code automatically pulls the schema of all installed CRDs. -
Getting to Grips with Unix and the Linux Family
Getting to grips with Unix and the Linux family David Chiappini, Giulio Pasqualetti, Tommaso Redaelli Torino, International Conference of Physics Students August 10, 2017 According to the booklet At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER According to the booklet update At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER A first data analysis with the shell, sed & awk an interactive workshop 1 at the beginning, there was UNIX... 2 ...then there was GNU 3 getting hands dirty common commands wait till you see piping 4 regular expressions 5 sed 6 awk 7 challenge time What's UNIX • Bell Labs was a really cool place to be in the 60s-70s • UNIX was a OS developed by Bell labs • they used C, which was also developed there • UNIX became the de facto standard on how to make an OS UNIX Philosophy • Write programs that do one thing and do it well. -

Managing Files with Sterling Connect:Direct File Agent 1.4.0.1
Managing Files with Sterling Connect:Direct File Agent 1.4.0.1 IBM Contents Managing Files with Sterling Connect:Direct File Agent.......................................... 1 Sterling Connect:Direct File Agent Overview.............................................................................................. 1 How to Run Sterling Connect:Direct File Agent.......................................................................................... 2 Sterling Connect:Direct File Agent Logging.................................................................................................3 Sterling Connect:Direct File Agent Configuration Planning........................................................................ 3 Sterling Connect:Direct File Agent Worksheet ...........................................................................................4 Considerations for a Large Number of Watch Directories.......................................................................... 6 Modifying MaxFileSize............................................................................................................................ 6 Modifying MaxBackupIndex...................................................................................................................6 Considerations for a Large Number of Files in a Watch Directory..............................................................7 Sterling Connect:Direct File Agent Configuration Scenarios...................................................................... 7 Scenario:Detecting -
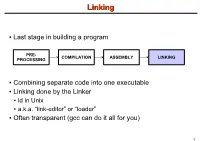
Linking + Libraries
LinkingLinking ● Last stage in building a program PRE- COMPILATION ASSEMBLY LINKING PROCESSING ● Combining separate code into one executable ● Linking done by the Linker ● ld in Unix ● a.k.a. “link-editor” or “loader” ● Often transparent (gcc can do it all for you) 1 LinkingLinking involves...involves... ● Combining several object modules (the .o files corresponding to .c files) into one file ● Resolving external references to variables and functions ● Producing an executable file (if no errors) file1.c file1.o file2.c gcc file2.o Linker Executable fileN.c fileN.o Header files External references 2 LinkingLinking withwith ExternalExternal ReferencesReferences file1.c file2.c int count; #include <stdio.h> void display(void); Compiler extern int count; int main(void) void display(void) { file1.o file2.o { count = 10; with placeholders printf(“%d”,count); display(); } return 0; Linker } ● file1.o has placeholder for display() ● file2.o has placeholder for count ● object modules are relocatable ● addresses are relative offsets from top of file 3 LibrariesLibraries ● Definition: ● a file containing functions that can be referenced externally by a C program ● Purpose: ● easy access to functions used repeatedly ● promote code modularity and re-use ● reduce source and executable file size 4 LibrariesLibraries ● Static (Archive) ● libname.a on Unix; name.lib on DOS/Windows ● Only modules with referenced code linked when compiling ● unlike .o files ● Linker copies function from library into executable file ● Update to library requires recompiling program 5 LibrariesLibraries ● Dynamic (Shared Object or Dynamic Link Library) ● libname.so on Unix; name.dll on DOS/Windows ● Referenced code not copied into executable ● Loaded in memory at run time ● Smaller executable size ● Can update library without recompiling program ● Drawback: slightly slower program startup 6 LibrariesLibraries ● Linking a static library libpepsi.a /* crave source file */ … gcc .. -

Enterprise View™
® Micro Focus ™ Enterprise View Installation Guide Copyright © 2008 Micro Focus (IP) Ltd. All rights reserved. Micro Focus (IP) Ltd. has made every effort to ensure that this book is correct and accurate, but reserves the right to make changes without notice at its sole discretion at any time. The software described in this document is supplied under a license and may be used or copied only in accordance with the terms of such license, and in particular any warranty of fitness of Micro Focus software products for any particular purpose is expressly excluded and in no event will Micro Focus be liable for any consequential loss. Animator®, COBOL Workbench®, EnterpriseLink®, Mainframe Express®, Micro Focus®, Net Express®, REQL® and Revolve® are registered trademarks, and AAI™, Analyzer™, Application Server™, Application to Application Interface™, AddPack™, AppTrack™, AssetMiner™, CCI™, DataConnect™, Dialog System™, Enterprise Server™, Enterprise Server with MTO™, EuroSmart™, FixPack™, LEVEL II COBOL™, License Server™, Mainframe Access™, Mainframe Manager™, Micro Focus® COBOL™, Micro Focus® Studio™, Micro Focus® Server™, Object COBOL™, OpenESQL™, Personal COBOL™, Professional COBOL™, Server Express™, SmartFind™, SmartFind Plus™, SmartFix™, SourceConnect™, SupportLine™, Toolbox™, VS COBOL™, WebSync™, and Xilerator™ are trademarks of Micro Focus (IP) Ltd. IBM® and CICS® are registered trademarks, and IMS™, DB2, DB2/390, DB2 Connect Enterprise Edition, DB2 Connect Personal Edition, COBOL for OS/390, Enterprise. Systems Architecture/390, ESA/390, MVS, MVS/ESA, OS/390, S/390, System/390, VSE/ESA and MFS are trademarks, of International Business Machines Corporation. Netscape Enterprise Server™ is a trademark of Netscape Communications Corporation. Internet Information Server®, Windows 95®, Windows 98®, Windows NT 4.0®, Windows ME® and Windows 2000® are registered trademarks of Microsoft Corporation.