What the HEC? Security Implications of HDMI Ethernet Channel and Other Related Protocols
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

HB-T-HDMI and HB-R-HDMI HDMI to Hdbaset Mini Converter Installation & Operation Guide Version 1.0R1 Published: October 1, 2015
HB-T-HDMI and HB-R-HDMI HDMI to HDBaseT Mini Converter Installation & Operation Guide Version 1.0r1 Published: October 1, 2015 Table of Contents Notices . 4 Trademarks . 4 Copyright . 4 Contacting Support . 4 Chapter 1: Introduction . 5 Overview. 5 Features . 5 Block Diagram. 6 Audio . 6 I/O Connections . 6 Installation . 7 Pairing HDMI and SDI HDBaseT Converters. 8 Appendix A: Specifications . 9 HB-T-HDMI & HB-R-HDMI Formats . 9 Video Displays . 9 VESA Displays . 9 Video Input . 10 HB-T-HDMI input . 10 HB-R-HDMI input . 10 Video Output . 10 HB-T-HDMI output . 10 HB-R-HDMI output. 10 HDCP . 10 Audio Input. 10 Control Data Ports. 10 RS-232 Extension. 10 RS-232 Cable Option . 10 DB9 Pinout . 10 IR Extension Input & Output Ports . 11 IR/RS-232 Cable Kit Option . 11 Physical . 11 Power . 11 Size. 11 Environment. 11 Appendix B: Safety and Compliance . .12 Federal Communications Commission (FCC) Compliance Notices . 12 Class A Interference Statement . 12 FCC Caution . 12 Canadian ICES Statement . 12 European Union and European Free Trade Association (EFTA) Regulatory Compliance. 13 Declaration of Conformity . 13 Recycling Notice . 14 Korean KCC Compliance Statement . 14 Taiwan Compliance Statement . 14 Japanese Compliance Statement . 15 Translated Warning and Caution Messages. 15 HB-T-HDMI & HB-R-HDMI v1.0r12 www.aja.com Before Operation Please Read These Instructions . 15 Warranty Information . .21 Limited Warranty. 21 HB-T-HDMI & HB-R-HDMI v1.0r13 www.aja.com Notices Trademarks AJA®, lo®, Ki Pro®, KONA®, KUMO®,T-TAP®, Because it matters.® and ROI® are registered trademarks of AJA Video Systems, Inc. -

120L10E Spec Release V08102020
4K Ultra HD Smart Laser TV with HDR and 120" Wide Color Gamut , screen included 4K class Model 120L10E Lose yourself in an immersive 120-inch display This 120-inch ‘panel-less’ 4K Ultra HD Smart Laser TV is a masterful combination of movie-theater technology, elegant aesthetics, and a simple table-top setup. Enjoy watching your favorite shows, movies or sports on a 120” screen in your living room, family room or home theater. The Hisense 4K Ultra HD Smart Laser TV features Hisense’s proprietary technology to produce luminance, incredible color and unmatched motion rate. In addition, the TV comes with built- in Harman Kardon® speakers with a wireless subwoofer. The Laser TV delivers 3000 lumens, HDR, Wide Color Gamut, a UHD Upscaler to bring your content to near 4K quality, Wi-Fi, popular music and movie apps (such as Netflix) and many more features to enjoy for an incredible and premium viewing experience. 4K UHD RESOLUTION* 120-INCH AMBIENT LIGHT REJECTION (ALR) SCREEN Enjoy four times (8.3 million) the amount of pixels of standard The 120-inch Hisense display screen makes converting your living full high definition TVs for a crystal-clear picture that will or workspace into the perfect setting for your viewing needs. With change your viewing experience. cutting-edge ALR screen technology that rejects ambient daylight and allows you to experience a great picture in either dark or illuminated settings. UHD UPSCALER HARMAN KARDON SPEAKERS Convert any input and all resolutions (SD/HD/FHD) 2x10W (left) and 2x10W (right) audio and a 60W subwoofer. -

Digital Visual Interface (DVI)
Digital Visual Interface 1 Digital Visual Interface Digital Visual Interface (DVI) A male DVI-D (single link) connector. Type Digital computer video connector Production history Designer Digital Display Working Group Designed April 1999 Produced 1999 to present Superseded by DisplayPort General specifications Hot pluggable Yes External Yes Video signal Digital video stream: (Single) WUXGA (1,920 × 1,200) @ 60 Hz (Dual) Limited by copper bandwidth limitations, DVI source limitations, and DVI sync limitations. Analog RGB video (−3 dB at 400 MHz) Pins 29 Data Data signal RGB data, clock, and display data channel Bitrate (Single link) 3.96 Gbit/s (Dual link) Limited only by copper bandwidth limitations, DVI source limitations, and DVI sync limitations. Max. devices 1 Protocol 3 × transition minimized differential signaling data and clock Pin out A female DVI-I socket from the front Pin 1 TMDS data 2− Digital red− (link 1) Pin 2 TMDS data 2+ Digital red+ (link 1) Digital Visual Interface 2 Pin 3 TMDS data 2/4 shield Pin 4 TMDS data 4− Digital green− (link 2) Pin 5 TMDS data 4+ Digital green+ (link 2) Pin 6 DDC clock Pin 7 DDC data Pin 8 Analog vertical sync Pin 9 TMDS data 1− Digital green− (link 1) Pin 10 TMDS data 1+ Digital green+ (link 1) Pin 11 TMDS data 1/3 shield Pin 12 TMDS data 3- Digital blue− (link 2) Pin 13 TMDS data 3+ Digital blue+ (link 2) Pin 14 +5 V Power for monitor when in standby Pin 15 Ground Return for pin 14 and analog sync Pin 16 Hot plug detect Pin 17 TMDS data 0− Digital blue− (link 1) and digital sync Pin 18 TMDS data 0+ Digital blue+ (link 1) and digital sync Pin 19 TMDS data 0/5 shield Pin 20 TMDS data 5− Digital red− (link 2) Pin 21 TMDS data 5+ Digital red+ (link 2) Pin 22 TMDS clock shield Pin 23 TMDS clock+ Digital clock+ (links 1 and 2) Pin 24 TMDS clock− Digital clock− (links 1 and 2) C1 Analog red C2 Analog green C3 Analog blue C4 Analog horizontal sync C5 Analog ground Return for R, G, and B signals Digital Visual Interface (DVI) is a video display interface developed by the Digital Display Working Group (DDWG). -

Developed by the Consumer Technology Association Video Division
4K Ultra High-Definition TV A display system may be referred to as 4K Ultra High-Definition if it meets the following minimum performance attributes: Display Resolution – Has at least 8 million active pixels, with at least 3840 horizontally and at least 2160 vertically. Physical pixels shall be individually addressable such that the horizontal and vertical resolution above can be demonstrated over the full range of colors provided by the display. Aspect Ratio – The width to height ratio of the display’s native resolution is 16:9 or wider. Upconversion – The display is capable of upscaling HD video and displaying it at 4K Ultra High- Definition display resolution. Digital Input – Has one or more HDMI inputs supporting at least 3840x2160 native content resolution at 24p, 30p, & 60p frames per second. At least one of the 3840x2160 HDMI inputs shall support HDCP v2.2 or equivalent content protection. Colorimetry – Processes 2160p video inputs encoded according to ITU-R BT.709 color space, and may support wider colorimetry standards. Bit Depth – Has a minimum bit depth of 8 bits. Connected 4K Ultra High-Definition TV A display system may be referred to as Connected 4K Ultra High-Definition (or Connected 4K UHD) if it meets the following minimum performance attributes: 4K Ultra High-Definition Capability – Meets all of the requirements of CTA’s 4K Ultra High-Definition Display Characteristics V3. Video Codec – Decodes IP-delivered video of 3840x2160 resolution that has been compressed using HEVC* and may decode video from other standard encoders. Audio Codec – Receives and reproduces, and/or outputs multichannel audio. -

Displayport to HDMI Converter Cable - 6 Ft (2M) - 4K
DisplayPort to HDMI Converter Cable - 6 ft (2m) - 4K Product ID: DP2HDMM2MB This 6-foot (2M) DisplayPort™ to HDMI® adapter cable lets you connect your DisplayPort equipped Ultrabook™, laptop or desktop computer to an HDMI display or projector with no additional adapters or cables required. The passive adapter supports video resolutions up to Ultra HD 4K. Astonishing picture quality This adapter cable ensures you can maintain an astonishing picture quality, four times the resolution of 1080p, when converting DisplayPort to HDMI. The adapter is also backward compatible with lower resolution displays and video sources. With support for high-definition resolutions of 1080p and 720p, you can future-proof your existing setup for 4K video. www.startech.com 1 800 265 1844 Hassle-free setup For the simplest and most discreet installation, this DP to HDMI adapter connects directly from your DisplayPort video source to the HDMI port on your display. It doesn't need a power source, unlike some converter dongles that require active power and separate bulky video cabling. Clutter-free installation At 6ft (2m) in length, this adapter cable delivers a compact connection that eliminates excess to ensure a tidy, professional installation. For shorter installations, we also offer a 3 ft DP to HDMI cable (DP2HDMM1MB), enabling you to choose the right cable length for your custom installation needs. The DP2HDMM2MB is backed by a 2-year StarTech.com warranty and free lifetime technical support. www.startech.com 1 800 265 1844 Certifications, Reports Applications -

Overview of Digital and Analog Connections Digital Video
Overview of Digital and Analog Connections Digital Video connectors are used to deliver the highest quality video signal. The technology uses TMDS (Transition Minimized Differential Signaling) to transmit large amounts of digital data from the source to the display, resulting in a high-quality image. DVI (Digital Visual Interface) was developed by the industry governing organization DDWG (Data Display Working Group) to send digital information from a computer to a digital display, such as a flat-panel LCD monitor. HDMI took a step forward by integrating audio and video into a more compact interface. DisplayPort is an interface technology that is designed to connect high-graphics capable PCs and displays as well as home theater equipment and displays. DisplayPort is similar to HDMI in that the DisplayPort signal carries both digital audio and video. HDMI HDMI stands for High Definition Multimedia Interface. This technology carries the same video information as DVI but adds the capacity for digital audio and control signals as well. The current version of HDMI carries one TMDS link of digital video. Found on many home-theater/consumer electronics devices, HDMI uses a 19-pin connector that is held in place by friction. This connector is technically described as a Type A HDMI connector. See our Available HDMI Cables HDMI Mini The Type C connector HDMI, the HDMI mini connector has the same number of pins but with its compact size, it is used for portable devices. See our Available HDMI Mini Cables DisplayPort™ DisplayPort™ is an interface technology that is designed to connect high-end graphics capable PCs and displays as well as home theater equipment and displays. -
Ultra High Definition 4K Television User's Guide
Ultra High Definition 4K Television User’s Guide: 65L9400U 58L8400U If you need assistance: Toshiba's Support Web site support.toshiba.com For more information, see “Troubleshooting” on page 173 in this guide. Owner's Record The model number and serial number are on the back and side of your television. Print out this page and write these numbers in the spaces below. Refer to these numbers whenever you communicate with your Toshiba dealer about this Television. Model name: Serial number: Register your Toshiba Television at register.toshiba.com Note: To display a High Definition picture, the TV must be receiving a High Definition signal (such as an over- the-air High Definition TV broadcast, a High Definition digital cable program, or a High Definition digital satellite program). For details, contact your TV antenna installer, cable provider, or GMA300039012 satellite provider. 12/14 2 CHILD SAFETY: PROPER TELEVISION PLACEMENT MATTERS TOSHIBA CARES • Manufacturers, retailers and the rest of the consumer electronics industry are committed to making home entertainment safe and enjoyable. • As you enjoy your television, please note that all televisions – new and old – must be supported on proper stands or installed according to the manufacturer’s recommendations. Televisions that are inappropriately situated on dressers, bookcases, shelves, desks, speakers, chests, carts, etc., may fall over, resulting in injury. TUNE IN TO SAFETY • ALWAYS follow the manufacturer’s recommendations for the safe installation of your television. • ALWAYS read and follow all instructions for proper use of your television. • NEVER allow children to climb on or play on the television or the furniture on which the television is placed. -

HDMI to Mini-Displayport Scaler/Converter AT-DP300
HDMI to Mini-DisplayPort Scaler/converter AT-DP300 User Manual Toll free: 1-877-536-3976 Local: 1-408-962-0515 www.atlona.com TABLE OF CONTENTS 1. Introduction 2 2. Applications 2 3. Package Contents 3 4. Features 3 5. Specifications 3 6. Panel Descriptions 4 6.1. Left Panel 4 6.2. Right Panel 4 6.3. Top Panel 4 7. Connection Diagram 5 8. Safety Information 6 9. Warranty 7 10. Atlona Product Registration 8 Toll free: 1-877-536-3976 Local: 1-408-962-0515 1 www.atlona.com INTRODUCTION The Atlona AT-DP300 is HDMI to Mini DisplayPort Scaler/converter, designed to convert any HDMI sources such as BluRay Player, Cable Box, Video Game Console, Apple TV to Mini DisplayPort which is commonly used by Apple 24” LED, Apple 27” LED and iMac 27”. The AT-DP300 is able to accept high resolution audio/video signals up to 1080p and scale them to either 1920x1200 or 720p Apple 24” users: • Video IN: AT-DP300 can take all standard VESA resolutions though HDMI input: 640~480 to 1920x1200 and 480p~1080p • Video OUT: AT-DP300 supports native resolution output 1920x1200 • Audio: Apple 24” LED only support Audio though USB cable (not though Mini DisplayPort, therefore please use 3.5mm audio out on the DP300 or digital audio on the hdmi source to go to separate set of speakers or home the- ater). If you decide to use Stereo Audio output on the DP300, please select audio output in the source settings to be 2channel PCM. Apple 27” LED and iMac 27” users: • Video IN: AT-DP300 can take all standard VESA resolutions though HDMI input: 640~480 to 1920x1200 and 480p~1080p • Video OUT: AT-DP300 is only capable of supporting one output resolution 1280x720 (720p). -

Ready to Watch Some TV?
Dear Sceptre Customer, Congratulations on your new ultra high definition SCEPTRE U Series UHD Display purchase. This display supports 4K resolution. Thank you for your support. To ensure safety and many years of trouble free operation of your display, please read the manual carefully before making any adjustments, and keep them in a safe place for future references. We hope you enjoy your new SCEPTRE UHD Display. For technical assistance, please call 1800-788-2878 and select option 3 or email our tech support group at [email protected]. For all other inquiries, please call 1800-788-2878 and select option 4 or email our customer service group at [email protected]. Web Chat is available during business hours M-F 8:30AM-5:30PM. We recommend you register your SCEPTRE Display at our online website http://www.sceptre.com/registration.html. This 4K UHD Display is MHL® ready using HDMI 1 / MHL. This UHD Display supports 4K resolution at 60 Hz refresh rate under HDMI 1, 2, and 3. - 1 - www.SCEPTRE.com SCEPTRE UMC Series UHD Display User Manual IMPORTANT INFORMATION - 2 - www.SCEPTRE.com SCEPTRE UMC Series UHD Display User Manual SAFETY INSTRUCTIONS Electricity is used to perform many useful functions, but it can also cause personal injuries and property damage if improperly handled. This product has been engineered and manufactured with the highest priority on safety. However, improper use can result in electric shock and / or fire. In order to prevent potential danger, please observe the following instructions when installing, operating and cleaning the product. To ensure your safety and prolong the service life of your Liquid Crystal Television, please read the following precautions carefully before using the product. -
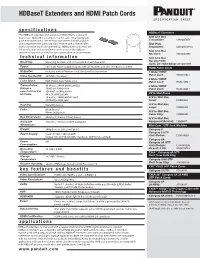
Hdbaset Extenders and HDMI Patch Cords SPECIFICATION SHEET
HDBaseT Extenders and HDMI Patch Cords SPECIFICATION SHEET specifications HDBaseT Extenders The HDBaseT extenders shall extend an HDMI, RS232 signal, and power over 70m/230ft of Category 6 or 6A cable. A two-gang wall Slim Line Box plate transmitter and a slim-line box transmitter shall be available Transmitter: CMHDBTBTX and compatible with both a standard receiver and a receiver with Wall Plate audio extraction (audio de embedding). HDMI patch cords meet the Transmitter: CMHDBTWPTX 2.0 specification and are recommended for use in the HDBaseT Slim Line Box channel in conjunction with Panduit copper cable and connectivity. Receiver: CMHDBTBRX technical information Slim Line Box Receiver with Mounting: Mounting brackets and screws included with box units Audio De-embedding: CMHDBTWRX Power: 24V1A DC Power Supply Included with all Receivers and Slim Line Box transmitter HDMI Patch Cords IR Emitter: Included with all Receivers and Slim Line Box transmitter 1 Meter HDMI Patch Cord: HDMI1MBL^ Video Bandwidth: 297MHz (10.2Gbps) 2 Meter HDMI Color Space: RGB, YCbCr 4:4:4, YCbCr 4:2:2 Patch Cord: HDMI2MBL^ Transmission 40 Meters: 1080P @60Hz@48bit 4 Meter HDMI Distance 1080P @120Hz@24bit Patch Cord: HDMI4MBL^ over Cat 6 or Cat 3D1080P @ 60Hz@36bit AV In-Wall Boxes 6A Cable: 4K x 2K @30Hz@24bi 70 meters: 1080P@60Hz 36bit A/V In-Wall Box, 3D1080P@30Hz 36bit Small: CMBBSWH Housing: Metal Enclosure A/V In-Wall Box, Large: CMBBLWH Color: Black (boxes) White (wall plate) A/V In-Wall Box, Cable Ring: CMBBCMR Box Dimensions: 65mm x 115mm x 17mm (boxes) -

BDP2110/12 Philips Blu-Ray Disc/ DVD Player
Philips Blu-ray Disc/ DVD player DivX Plus HD USB2.0 Media Link BD-Live BDP2110 Play all your movies from Blu-ray discs and DVDs With the Philips BDP2110 Blu-ray player, movies never looked better. Incredibly sharp images in full HD 1080p are delivered from Blu-ray discs, while DVD upscaling offers near-HD video quality. Engage more • Enjoy all your movies and music from CD and DVD • USB 2.0 plays video/music from USB flash/hard disk drive • EasyLink to control all HDMI CEC devices via a single remote • BD-Live (Profile 2.0) to enjoy online Blu-ray bonus content Hear more • Dolby TrueHD for high fidelity sound • DTS2.0 Digital Out See more • Blu-ray Disc playback for sharp images in full HD 1080p • DivX Plus HD Certified for high definition DivX playback • DVD video upscaling to 1080p via HDMI for near-HD images • Subtitle Shift for widescreen without any missing subtitles Blu-ray Disc/ DVD player BDP2110/12 DivX Plus HD USB2.0 Media Link, BD-Live Highlights Enjoy movies and music technology to let you enjoy HD videos and picture and sound quality, completely free movies from the Internet direct to your Philips from noise. HDTV or PC. DivX Plus HD supports the playback of DivX Plus content (H.264 HD EasyLink video with high-quality AAC audio in an MKV file container) while also supporting previous versions of DivX video up to 1080p. DivX Plus HD for true HD digital video. Dolby TrueHD Enjoy all your movies and music from CD and DVD Blu-ray Disc playback EasyLink lets you control multiple devices like DVD players, Blu-ray players, TV's etc. -
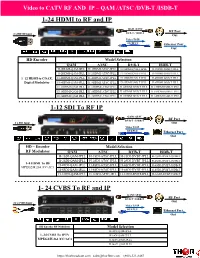
1-24 HDMI to RF and IP 1-12 SDI to RF IP 1- 24 CVBS to RF and IP
Video to CATV RF AND IP – QAM /ATSC /DVB-T /ISDB-T 1-24 HDMI to RF and IP QAM /ATSC RF Port DVB-T / ISDB-T 8 x HDMI Input Out Video TS IP OUTPUT Ethernet Port Out HD Encoder Model Selection QAM ATSC DVB-T ISDB-T H-1HDMI-QAM-IPLL H-1HDMI-ATSC-IPLL H-1HDMI-DVB-T-IPLL H-1HDMI-ISDB-T-IPLL H-2HDMI-QAM-IPLL H-2HDMI-ATSC-IPLL H-2HDMI-DVB-T-IPLL H-2HDMI-ISDB-T-IPLL 1–12 HDMI to COAX, H-4HDMI-QAM-IPLL H-4HDMI-ATSC-IPLL H-4HDMI-DVB-T-IPLL H-4HDMI-ISDB-T-IPLL Digital Modulator H-8HDMI-QAM-IPLL H-8HDMI-ATSC-IPLL H-8HDMI-DVB-T-IPLL H-8HDMI-ISDB-T-IPLL H-12HDMI-QAM-IPLL H-12HDMI-ATSC-IPLL H-12HDMI-DVB-T-IPLL H-12HDMI-ISDB-T-IPLL H-16HDMI-QAM-IPLL H-16HDMI-ATSC-IPLL H-16HDMI-DVB-T-IPLL H-16HDMI-ISDB-T-IPLL H-24HDMI-QAM-IPLL H-24HDMI-ATSC-IPLL H-24HDMI-DVB-T-IPLL H-24HDMI-ISDB-T-IPLL 1-12 SDI To RF IP QAM /ATSC RF Port DVB-T / ISDB-T 8 x SDI Input Out Video TS IP OUTPUT Ethernet Port Out HD – Encoder Model Selection RF Modulator QAM ATSC DVB-T ISDB-T H-1SDI-QAM-IPLL H-1SDI-ATSC-IPLL H-1SDI-DVBT-IPLL H-1SDI-DVBT-ISDB-T H-2SDI-QAM-IPLL H-2SDI-ATSC-IPLL H-2SDI-DVBT-IPLL H-2SDI-DVBT-ISDB-T 1–8 HDMI To RF H-4SDI-QAM-IPLL H-4SDI-ATSC-IPLL H-4SDI-DVBT-IPLL H-4SDI-DVBT-ISDB-T MPEG2/H.264 /CC/AC3 H-8SDI-QAM-IPLL H-8SDI-ATSC-IPLL H-8SDI-DVBT-IPLL H-8SDI-DVBT-ISDB-T H-12SDI-QAM-IPLL H-12SDI-ATSC-IPLL H-12SDI-DVBT-IPLL H-12SDI-DVBT-ISDB-T 1- 24 CVBS To RF and IP QAM /ATSC RF Port DVB-T / ISDB-T 24 x CVBS Input Out Video TS IP OUTPUT Ethernet Port Out HD Encoder RF Modulator Model Selection H-4AV-QAM-IP-LL 1–24 CVBS To IPTV H-8AV-QAM-IP-LL MPEG2/H.264 /CC/AC3 H-16AV-QAM-IP-LL