Notes on Programming Standard ML of New Jersey (Version 110.0.6)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Bit Shifts Bit Operations, Logical Shifts, Arithmetic Shifts, Rotate Shifts
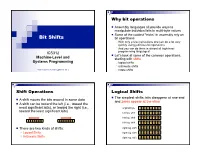
Why bit operations Assembly languages all provide ways to manipulate individual bits in multi-byte values Some of the coolest “tricks” in assembly rely on Bit Shifts bit operations With only a few instructions one can do a lot very quickly using judicious bit operations And you can do them in almost all high-level ICS312 programming languages! Let’s look at some of the common operations, Machine-Level and starting with shifts Systems Programming logical shifts arithmetic shifts Henri Casanova ([email protected]) rotate shifts Shift Operations Logical Shifts The simplest shifts: bits disappear at one end A shift moves the bits around in some data and zeros appear at the other A shift can be toward the left (i.e., toward the most significant bits), or toward the right (i.e., original byte 1 0 1 1 0 1 0 1 toward the least significant bits) left log. shift 0 1 1 0 1 0 1 0 left log. shift 1 1 0 1 0 1 0 0 left log. shift 1 0 1 0 1 0 0 0 There are two kinds of shifts: right log. shift 0 1 0 1 0 1 0 0 Logical Shifts right log. shift 0 0 1 0 1 0 1 0 Arithmetic Shifts right log. shift 0 0 0 1 0 1 0 1 Logical Shift Instructions Shifts and Numbers Two instructions: shl and shr The common use for shifts: quickly multiply and divide by powers of 2 One specifies by how many bits the data is shifted In decimal, for instance: multiplying 0013 by 10 amounts to doing one left shift to obtain 0130 Either by just passing a constant to the instruction multiplying by 100=102 amounts to doing two left shifts to obtain 1300 Or by using whatever -

Scoping Changes with Method Namespaces
Scoping Changes with Method Namespaces Alexandre Bergel ADAM Project, INRIA Futurs Lille, France [email protected] Abstract. Size and complexity of software has reached a point where modular constructs provided by traditional object-oriented programming languages are not expressive enough. A typical situation is how to modify a legacy code without breaking its existing clients. We propose method namespaces as a visibility mechanism for behavioral refine- ments of classes (method addition and redefinition). New methods may be added and existing methods may be redefined in a method namespace. This results in a new version of a class accessible only within the defining method namespace. This mechanism, complementary to inheritance in object-orientation and tradi- tional packages, allows unanticipated changes while minimizing the impact on former code. Method Namespaces have been implemented in the Squeak Smalltalk system and has been successfully used to provide a translated version of a library without ad- versely impacting its original clients. We also provide benchmarks that demon- strate its application in a practical setting. 1 Introduction Managing evolution and changes is a critical part of the life cycle of all software sys- tems [BMZ+05, NDGL06]. In software, changes are modeled as a set of incremental code refinements such as class redefinition, method addition, and method redefinition. Class-based object-oriented programming languages (OOP) models code refinements with subclasses that contain behavioral differences. It appears that subclassing is well adapted when evolution is anticipated. For example, most design patterns and frame- works rely on class inheritance to express future anticipated adaptation and evolution. However, subclassing does not as easily help in expressing unanticipated software evo- lution [FF98a, BDN05b]. -
Managing Projects with GNU Make, Third Edition by Robert Mecklenburg
ManagingProjects with GNU Make Other resources from O’Reilly Related titles Unix in a Nutshell sed and awk Unix Power Tools lex and yacc Essential CVS Learning the bash Shell Version Control with Subversion oreilly.com oreilly.com is more than a complete catalog of O’Reilly books. You’ll also find links to news, events, articles, weblogs, sample chapters, and code examples. oreillynet.com is the essential portal for developers interested in open and emerging technologies, including new platforms, pro- gramming languages, and operating systems. Conferences O’Reilly brings diverse innovators together to nurture the ideas that spark revolutionary industries. We specialize in document- ing the latest tools and systems, translating the innovator’s knowledge into useful skills for those in the trenches. Visit con- ferences.oreilly.com for our upcoming events. Safari Bookshelf (safari.oreilly.com) is the premier online refer- ence library for programmers and IT professionals. Conduct searches across more than 1,000 books. Subscribers can zero in on answers to time-critical questions in a matter of seconds. Read the books on your Bookshelf from cover to cover or sim- ply flip to the page you need. Try it today with a free trial. THIRD EDITION ManagingProjects with GNU Make Robert Mecklenburg Beijing • Cambridge • Farnham • Köln • Sebastopol • Tokyo Managing Projects with GNU Make, Third Edition by Robert Mecklenburg Copyright © 2005, 1991, 1986 O’Reilly Media, Inc. All rights reserved. Printed in the United States of America. Published by O’Reilly Media, Inc., 1005 Gravenstein Highway North, Sebastopol, CA 95472. O’Reilly books may be purchased for educational, business, or sales promotional use. -

C Strings and Pointers
Software Design Lecture Notes Prof. Stewart Weiss C Strings and Pointers C Strings and Pointers Motivation The C++ string class makes it easy to create and manipulate string data, and is a good thing to learn when rst starting to program in C++ because it allows you to work with string data without understanding much about why it works or what goes on behind the scenes. You can declare and initialize strings, read data into them, append to them, get their size, and do other kinds of useful things with them. However, it is at least as important to know how to work with another type of string, the C string. The C string has its detractors, some of whom have well-founded criticism of it. But much of the negative image of the maligned C string comes from its abuse by lazy programmers and hackers. Because C strings are found in so much legacy code, you cannot call yourself a C++ programmer unless you understand them. Even more important, C++'s input/output library is harder to use when it comes to input validation, whereas the C input/output library, which works entirely with C strings, is easy to use, robust, and powerful. In addition, the C++ main() function has, in addition to the prototype int main() the more important prototype int main ( int argc, char* argv[] ) and this latter form is in fact, a prototype whose second argument is an array of C strings. If you ever want to write a program that obtains the command line arguments entered by its user, you need to know how to use C strings. -

Scala−−, a Type Inferred Language Project Report
Scala−−, a type inferred language Project Report Da Liu [email protected] Contents 1 Background 2 2 Introduction 2 3 Type Inference 2 4 Language Prototype Features 3 5 Project Design 4 6 Implementation 4 6.1 Benchmarkingresults . 4 7 Discussion 9 7.1 About scalac ....................... 9 8 Lessons learned 10 9 Language Specifications 10 9.1 Introdution ......................... 10 9.2 Lexicalsyntax........................ 10 9.2.1 Identifiers ...................... 10 9.2.2 Keywords ...................... 10 9.2.3 Literals ....................... 11 9.2.4 Punctions ...................... 12 9.2.5 Commentsandwhitespace. 12 9.2.6 Operations ..................... 12 9.3 Syntax............................ 12 9.3.1 Programstructure . 12 9.3.2 Expressions ..................... 14 9.3.3 Statements ..................... 14 9.3.4 Blocksandcontrolflow . 14 9.4 Scopingrules ........................ 16 9.5 Standardlibraryandcollections. 16 9.5.1 println,mapandfilter . 16 9.5.2 Array ........................ 16 9.5.3 List ......................... 17 9.6 Codeexample........................ 17 9.6.1 HelloWorld..................... 17 9.6.2 QuickSort...................... 17 1 of 34 10 Reference 18 10.1Typeinference ....................... 18 10.2 Scalaprogramminglanguage . 18 10.3 Scala programming language development . 18 10.4 CompileScalatoLLVM . 18 10.5Benchmarking. .. .. .. .. .. .. .. .. .. .. 18 11 Source code listing 19 1 Background Scala is becoming drawing attentions in daily production among var- ious industries. Being as a general purpose programming language, it is influenced by many ancestors including, Erlang, Haskell, Java, Lisp, OCaml, Scheme, and Smalltalk. Scala has many attractive features, such as cross-platform taking advantage of JVM; as well as with higher level abstraction agnostic to the developer providing immutability with persistent data structures, pattern matching, type inference, higher or- der functions, lazy evaluation and many other functional programming features. -
Investigating Powershell Attacks
Investigating PowerShell Attacks Black Hat USA 2014 August 7, 2014 PRESENTED BY: Ryan Kazanciyan, Matt Hastings © Mandiant, A FireEye Company. All rights reserved. Background Case Study WinRM, Victim VPN SMB, NetBIOS Attacker Victim workstations, Client servers § Fortune 100 organization § Command-and-control via § Compromised for > 3 years § Scheduled tasks § Active Directory § Local execution of § Authenticated access to PowerShell scripts corporate VPN § PowerShell Remoting © Mandiant, A FireEye Company. All rights reserved. 2 Why PowerShell? It can do almost anything… Execute commands Download files from the internet Reflectively load / inject code Interface with Win32 API Enumerate files Interact with the registry Interact with services Examine processes Retrieve event logs Access .NET framework © Mandiant, A FireEye Company. All rights reserved. 3 PowerShell Attack Tools § PowerSploit § Posh-SecMod § Reconnaissance § Veil-PowerView § Code execution § Metasploit § DLL injection § More to come… § Credential harvesting § Reverse engineering § Nishang © Mandiant, A FireEye Company. All rights reserved. 4 PowerShell Malware in the Wild © Mandiant, A FireEye Company. All rights reserved. 5 Investigation Methodology WinRM PowerShell Remoting evil.ps1 backdoor.ps1 Local PowerShell script Persistent PowerShell Network Registry File System Event Logs Memory Traffic Sources of Evidence © Mandiant, A FireEye Company. All rights reserved. 6 Attacker Assumptions § Has admin (local or domain) on target system § Has network access to needed ports on target system § Can use other remote command execution methods to: § Enable execution of unsigned PS scripts § Enable PS remoting © Mandiant, A FireEye Company. All rights reserved. 7 Version Reference 2.0 3.0 4.0 Requires WMF Requires WMF Default (SP1) 3.0 Update 4.0 Update Requires WMF Requires WMF Default (R2 SP1) 3.0 Update 4.0 Update Requires WMF Default 4.0 Update Default Default Default (R2) © Mandiant, A FireEye Company. -

Type-Safe Multi-Tier Programming with Standard ML Modules
Experience Report: Type-Safe Multi-Tier Programming with Standard ML Modules Martin Elsman Philip Munksgaard Ken Friis Larsen Department of Computer Science, iAlpha AG, Switzerland Department of Computer Science, University of Copenhagen, Denmark [email protected] University of Copenhagen, Denmark [email protected] kfl[email protected] Abstract shared module, it is now possible, on the server, to implement a We describe our experience with using Standard ML modules and module that for each function responds to a request by first deseri- Standard ML’s core language typing features for ensuring type- alising the argument into a value, calls the particular function and safety across physically separated tiers in an extensive web applica- replies to the client with a serialised version of the result value. tion built around a database-backed server platform and advanced Dually, on the client side, for each function, the client code can client code that accesses the server through asynchronous server serialise the argument and send the request asynchronously to the requests. server. When the server responds, the client will deserialise the re- sult value and apply the handler function to the value. Both for the server part and for the client part, the code can be implemented in 1. Introduction a type-safe fashion. In particular, if an interface type changes, the The iAlpha Platform is an advanced asset management system programmer will be notified about all type-inconsistencies at com- featuring a number of analytics modules for combining trading pile -

The Common HOL Platform
The Common HOL Platform Mark Adams Proof Technologies Ltd, UK Radboud University, Nijmegen, The Netherlands The Common HOL project aims to facilitate porting source code and proofs between members of the HOL family of theorem provers. At the heart of the project is the Common HOL Platform, which defines a standard HOL theory and API that aims to be compatible with all HOL systems. So far, HOL Light and hol90 have been adapted for conformance, and HOL Zero was originally developed to conform. In this paper we provide motivation for a platform, give an overview of the Common HOL Platform’s theory and API components, and show how to adapt legacy systems. We also report on the platform’s successful application in the hand-translation of a few thousand lines of source code from HOL Light to HOL Zero. 1 Introduction The HOL family of theorem provers started in the 1980s with HOL88 [5], and has since grown to include many systems, most prominently HOL4 [16], HOL Light [8], ProofPower HOL [3] and Is- abelle/HOL [12]. These four main systems have developed their own advanced proof facilities and extensive theory libraries, and have been successfully employed in major projects in the verification of critical hardware and software [1, 11] and the formalisation of mathematics [7]. It would clearly be of benefit if these systems could “talk” to each other, specifically if theory, proofs and source code could be exchanged in a relatively seamless manner. This would reduce the considerable duplication of effort otherwise required for one system to benefit from the major projects and advanced capabilities developed on another. -

The Scala Experience Safe Programming Can Be Fun!
The Scala Programming Language Mooly Sagiv Slides taken from Martin Odersky (EPFL) Donna Malayeri (CMU) Hila Peleg (Technion) Modern Functional Programming • Higher order • Modules • Pattern matching • Statically typed with type inference • Two viable alternatives • Haskel • Pure lazy evaluation and higher order programming leads to Concise programming • Support for domain specific languages • I/O Monads • Type classes • ML/Ocaml/F# • Eager call by value evaluation • Encapsulated side-effects via references • [Object orientation] Then Why aren’t FP adapted? • Education • Lack of OO support • Subtyping increases the complexity of type inference • Programmers seeks control on the exact implementation • Imperative programming is natural in certain situations Why Scala? (Coming from OCaml) • Runs on the JVM/.NET • Can use any Java code in Scala • Combines functional and imperative programming in a smooth way • Effective libraries • Inheritance • General modularity mechanisms The Java Programming Language • Designed by Sun 1991-95 • Statically typed and type safe • Clean and Powerful libraries • Clean references and arrays • Object Oriented with single inheritance • Interfaces with multiple inheritance • Portable with JVM • Effective JIT compilers • Support for concurrency • Useful for Internet Java Critique • Downcasting reduces the effectiveness of static type checking • Many of the interesting errors caught at runtime • Still better than C, C++ • Huge code blowouts • Hard to define domain specific knowledge • A lot of boilerplate code • -

Interactive Theorem Proving (ITP) Course Web Version
Interactive Theorem Proving (ITP) Course Web Version Thomas Tuerk ([email protected]) Except where otherwise noted, this work is licened under Creative Commons Attribution-ShareAlike 4.0 International License version 3c35cc2 of Mon Nov 11 10:22:43 2019 Contents Part I Preface 3 Part II Introduction 6 Part III HOL 4 History and Architecture 16 Part IV HOL's Logic 24 Part V Basic HOL Usage 38 Part VI Forward Proofs 46 Part VII Backward Proofs 61 Part VIII Basic Tactics 83 Part IX Induction Proofs 110 Part X Basic Definitions 119 Part XI Good Definitions 163 Part XII Deep and Shallow Embeddings 184 Part XIII Rewriting 192 Part XIV Advanced Definition Principles 246 Part XV Maintainable Proofs 267 Part XVI Overview of HOL 4 289 Part XVII Other Interactive Theorem Provers 302 2 / 315 Part I Preface Except where otherwise noted, this work is licened under Creative Commons Attribution-ShareAlike 4.0 International License. Preface these slides originate from a course for advanced master students it was given by the PROSPER group at KTH in Stockholm in 2017 (see https://www.kth.se/social/group/interactive-theorem-) the course focused on how to use HOL 4 students taking the course were expected to I know functional programming, esp. SML I understand predicate logic I have some experience with pen and paper proofs the course consisted of 9 lectures, which each took 90 minutes there were 19 supervised practical sessions, which each took 2 h usually there was 1 lecture and 2 practical sessions each week students were expected to work about 10 h each -
Four Lectures on Standard ML
Mads Tofte March Lab oratory for Foundations of Computer Science Department of Computer Science Edinburgh University Four Lectures on Standard ML The following notes give an overview of Standard ML with emphasis placed on the Mo dules part of the language The notes are to the b est of my knowledge faithful to The Denition of Standard ML Version as regards syntax semantics and terminology They have b een written so as to b e indep endent of any particular implemen tation The exercises in the rst lectures can b e tackled without the use of a machine although having access to an implementation will no doubt b e b enecial The pro ject in Lecture presupp oses access to an implementation of the full language including mo dules At present the Edinburgh compiler do es not fall into this category the author used the New Jersey Standard ML compiler Lecture gives an introduction to ML aimed at the reader who is familiar with some programming language but do es not know ML Both the Core Language and the Mo dules are covered by way of example Lecture discusses the use of ML mo dules in the development of large programs A useful metho dology for programming with functors signatures and structures is presented Lecture gives a fairly detailed account of the static semantics of ML mo dules for those who really want to understand the crucial notions of sharing and signature matching Lecture presents a one day pro ject intended to give the student an opp ortunity of mo difying a nontrivial piece of software using functors signatures and structures -

Functional C
Functional C Pieter Hartel Henk Muller January 3, 1999 i Functional C Pieter Hartel Henk Muller University of Southampton University of Bristol Revision: 6.7 ii To Marijke Pieter To my family and other sources of inspiration Henk Revision: 6.7 c 1995,1996 Pieter Hartel & Henk Muller, all rights reserved. Preface The Computer Science Departments of many universities teach a functional lan- guage as the first programming language. Using a functional language with its high level of abstraction helps to emphasize the principles of programming. Func- tional programming is only one of the paradigms with which a student should be acquainted. Imperative, Concurrent, Object-Oriented, and Logic programming are also important. Depending on the problem to be solved, one of the paradigms will be chosen as the most natural paradigm for that problem. This book is the course material to teach a second paradigm: imperative pro- gramming, using C as the programming language. The book has been written so that it builds on the knowledge that the students have acquired during their first course on functional programming, using SML. The prerequisite of this book is that the principles of programming are already understood; this book does not specifically aim to teach `problem solving' or `programming'. This book aims to: ¡ Familiarise the reader with imperative programming as another way of imple- menting programs. The aim is to preserve the programming style, that is, the programmer thinks functionally while implementing an imperative pro- gram. ¡ Provide understanding of the differences between functional and imperative pro- gramming. Functional programming is a high level activity.