U|Xahbeigy03102ozxv+:'
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Elastic Storage for Linux on System Z IBM Research & Development Germany
Peter Münch T/L Test and Development – Elastic Storage for Linux on System z IBM Research & Development Germany Elastic Storage for Linux on IBM System z © Copyright IBM Corporation 2014 9.0 Elastic Storage for Linux on System z Session objectives • This presentation introduces the Elastic Storage, based on General Parallel File System technology that will be available for Linux on IBM System z. Understand the concepts of Elastic Storage and which functions will be available for Linux on System z. Learn how you can integrate and benefit from the Elastic Storage in a Linux on System z environment. Finally, get your first impression in a live demo of Elastic Storage. 2 © Copyright IBM Corporation 2014 Elastic Storage for Linux on System z Trademarks The following are trademarks of the International Business Machines Corporation in the United States and/or other countries. AIX* FlashSystem Storwize* Tivoli* DB2* IBM* System p* WebSphere* DS8000* IBM (logo)* System x* XIV* ECKD MQSeries* System z* z/VM* * Registered trademarks of IBM Corporation The following are trademarks or registered trademarks of other companies. Adobe, the Adobe logo, PostScript, and the PostScript logo are either registered trademarks or trademarks of Adobe Systems Incorporated in the United States, and/or other countries. Cell Broadband Engine is a trademark of Sony Computer Entertainment, Inc. in the United States, other countries, or both and is used under license therefrom. Intel, Intel logo, Intel Inside, Intel Inside logo, Intel Centrino, Intel Centrino logo, Celeron, Intel Xeon, Intel SpeedStep, Itanium, and Pentium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. -

Integrity Checking of Operating Systems with Respect to Kernel Level Malware”
To Bianca, for being who you are. Abstract Kernel-mode rootkits have gained a considerable momentum within the blackhat com- munity. They represent a considerable threat to any computer system, as they pro- vide an intruder with the ability to hide the presence of his malicious activity. These rootkits make changes to the operating system’s kernel, thereby providing particularly stealthy hiding techniques. Considering the kernel rootkit threat and other threats, the collection of reliable information from a compromised system becomes a central problem within the domain of computer security. This thesis addresses this problem. It looks at the possibility of using virtualization as a means to facilitate kernel-mode rootkit detection through integrity checking. The thesis describes several areas within the Linux kernel, which are commonly subverted by kernel-mode rootkits. It introduces the reader to the concept of virtual- ization and describes several technologies employing virtualization. The kernel-mode rootkit threat is then addressed through a description of their hiding methodologies. Some of the existing methods for malware detection are also addressed and analysed. A number of general requirements, which need to be satisfied by a general model enabling kernel-mode rootkit detection, are identified. A model addressing these requirements is suggested, and a framework implementing the model is set-up. The detection capabilities of the framework are tested on a couple of rootkits. iii Preface This report presents the results of my master thesis “Integrity checking of operating systems with respect to kernel level malware”. It is written as part of the Master de- gree (Sivilingeniør) in Computer Science at the Norwegian University of Science and Technology (NTNU), during Spring 2005. -

Linux Journal | August 2014 | Issue
™ SPONSORED BY Since 1994: The Original Magazine of the Linux Community AUGUST 2014 | ISSUE 244 | www.linuxjournal.com PROGRAMMING HOW-TO: + OpenGL Build, Develop Programming and Validate Creation of RPMs USE VAGRANT Sysadmin Cloud for an Easier Troubleshooting Development with dhclient Workflow Tips for PROMISE Becoming a THEORY Web Developer An In-Depth A Rundown Look of Linux for Recreation V WATCH: ISSUE OVERVIEW LJ244-Aug2014.indd 1 7/23/14 6:56 PM Get the automation platform that makes it easy to: Build Infrastructure Deploy Applications Manage In your data center or in the cloud. getchef.com LJ244-Aug2014.indd 2 7/23/14 11:41 AM Are you tiredtiered of of dealing dealing with with proprietary proprietary storage? storage? ® 9%2Ä4MHÆDCÄ2SNQ@FD ZFS Unified Storage zStax StorCore from Silicon - From modest data storage needs to a multi-tiered production storage environment, zStax StorCore zStax StorCore 64 zStax StorCore 104 The zStax StorCore 64 utilizes the latest in The zStax StorCore 104 is the flagship of the dual-processor Intel® Xeon® platforms and fast zStax product line. With its highly available SAS SSDs for caching. The zStax StorCore 64 configurations and scalable architecture, the platform is perfect for: zStax StorCore 104 platform is ideal for: VPDOOPHGLXPRIILFHILOHVHUYHUV EDFNHQGVWRUDJHIRUYLUWXDOL]HGHQYLURQPHQWV VWUHDPLQJYLGHRKRVWV PLVVLRQFULWLFDOGDWDEDVHDSSOLFDWLRQV VPDOOGDWDDUFKLYHV DOZD\VDYDLODEOHDFWLYHDUFKLYHV TalkTalk with with an anexpert expert today: today: 866-352-1173 866-352-1173 - http://www.siliconmechanics.com/zstax LJ244-Aug2014.indd 3 7/23/14 11:41 AM AUGUST 2014 CONTENTS ISSUE 244 PROGRAMMING FEATURES 64 Vagrant 74 An Introduction to How to use Vagrant to create a OpenGL Programming much easier development workflow. -
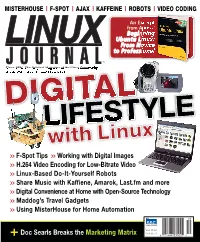
Withlinux Linux
LINUX JOURNAL MISTERHOUSE | F-SPOT | AJAX | KAFFEINE | ROBOTS | VIDEO CODING An Excerpt from Apress’ Beginning DIGITAL LIFESTYLE DIGITAL Ubuntu Linux: From Novice to Professional ™ Since 1994: The Original Magazine of the Linux Community OCTOBER 2006 | ISSUE 150 | www.linuxjournal.com MisterHouse | AL F-Spot DIGIT | Ajax | Kaffeine LIFESTYLE | ux Robots with LinuxLin | Video Coding Video >> F-Spot Tips >> Working with Digital Images >> H.264 Video Encoding for Low-Bitrate Video | Ubuntu >> Linux-Based Do-It-Yourself Robots >> Share Music with Kaffiene, Amarok, Last.fm and more >> Digital Convenience at Home with Open-Source Technology O >> Maddog’s Travel Gadgets C T O B E >> Using MisterHouse for Home Automation R 2006 AN I S S PUBLICATION U E USA $5.00 150 + Doc Searls Breaks the Marketing Matrix CAN $6.50 U|xaHBEIGy03102ozXv,:! Today, Carlo restored a failed router in Miami, rebooted a Linux server in Tokyo, and remembered someone’s very special day. With Avocent centralized management solutions, the world can finally revolve around you. Avocent puts secure access and control right at your fingertips – from multi-platform servers to network routers, your local data center to branch offices. Our “agentless” out-of-band solution manages your physical and virtual connections (KVM, serial, integrated power, embedded service processors, IPMI and SoL) from a single console. You have guaranteed access to your critical hardware even when in-band methods fail. Let others roll crash carts to troubleshoot – with Avocent, trouble becomes a thing of the past, so you can focus on the present. Visit www.avocent.com/special to download Data Center Control: Guidelines to Achieve Centralized Management white paper. -

BESIII Physical Analysis on Hadoop Platform
20th International Conference on Computing in High Energy and Nuclear Physics (CHEP2013) IOP Publishing Journal of Physics: Conference Series 513 (2014) 032044 doi:10.1088/1742-6596/513/3/032044 BESIII Physical Analysis on Hadoop Platform Jing HUO12, Dongsong ZANG12, Xiaofeng LEI12, Qiang LI12, Gongxing SUN1 1Institute of High Energy Physics, Beijing, China 2University of Chinese Academy of Sciences, Beijing, China E-mail: [email protected] Abstract. In the past 20 years, computing cluster has been widely used for High Energy Physics data processing. The jobs running on the traditional cluster with a Data-to-Computing structure, have to read large volumes of data via the network to the computing nodes for analysis, thereby making the I/O latency become a bottleneck of the whole system. The new distributed computing technology based on the MapReduce programming model has many advantages, such as high concurrency, high scalability and high fault tolerance, and it can benefit us in dealing with Big Data. This paper brings the idea of using MapReduce model to do BESIII physical analysis, and presents a new data analysis system structure based on Hadoop platform, which not only greatly improve the efficiency of data analysis, but also reduces the cost of system building. Moreover, this paper establishes an event pre-selection system based on the event level metadata(TAGs) database to optimize the data analyzing procedure. 1. Introduction 1.1 The current BESIII computing architecture High Energy Physics experiment is a typical data-intensive application. The BESIII computing system now consist of 3PB+ data, 6500 CPU cores, and it is estimated that there will be more than 10PB data produced in the future 5 years. -

Globalfs: a Strongly Consistent Multi-Site File System
GlobalFS: A Strongly Consistent Multi-Site File System Leandro Pacheco Raluca Halalai Valerio Schiavoni University of Lugano University of Neuchatelˆ University of Neuchatelˆ Fernando Pedone Etienne Riviere` Pascal Felber University of Lugano University of Neuchatelˆ University of Neuchatelˆ Abstract consistency, availability, and tolerance to partitions. Our goal is to ensure strongly consistent file system operations This paper introduces GlobalFS, a POSIX-compliant despite node failures, at the price of possibly reduced geographically distributed file system. GlobalFS builds availability in the event of a network partition. Weak on two fundamental building blocks, an atomic multicast consistency is suitable for domain-specific applications group communication abstraction and multiple instances of where programmers can anticipate and provide resolution a single-site data store. We define four execution modes and methods for conflicts, or work with last-writer-wins show how all file system operations can be implemented resolution methods. Our rationale is that for general-purpose with these modes while ensuring strong consistency and services such as a file system, strong consistency is more tolerating failures. We describe the GlobalFS prototype in appropriate as it is both more intuitive for the users and detail and report on an extensive performance assessment. does not require human intervention in case of conflicts. We have deployed GlobalFS across all EC2 regions and Strong consistency requires ordering commands across show that the system scales geographically, providing replicas, which needs coordination among nodes at performance comparable to other state-of-the-art distributed geographically distributed sites (i.e., regions). Designing file systems for local commands and allowing for strongly strongly consistent distributed systems that provide good consistent operations over the whole system. -

A Study of Cryptographic File Systems in Userspace
Turkish Journal of Computer and Mathematics Education Vol.12 No.10 (2021), 4507-4513 Research Article A study of cryptographic file systems in userspace a b c d e f Sahil Naphade , Ajinkya Kulkarni Yash Kulkarni , Yash Patil , Kaushik Lathiya , Sachin Pande a Department of Information Technology PICT, Pune, India [email protected] b Department of Information Technology PICT, Pune, India [email protected] c Department of Information Technology PICT, Pune, India [email protected] d Department of Information Technology PICT, Pune, India [email protected] e Veritas Technologies Pune, India, [email protected] f Department of Information Technology PICT, Pune, India [email protected] Article History: Received: 10 January 2021; Revised: 12 February 2021; Accepted: 27 March 2021; Published online: 28 April 2021 Abstract: With the advancements in technology and digitization, the data storage needs are expanding; along with the data breaches which can expose sensitive data to the world. Thus, the security of the stored data is extremely important. Conventionally, there are two methods of storage of the data, the first being hiding the data and the second being encryption of the data. However, finding out hidden data is simple, and thus, is very unreliable. The second method, which is encryption, allows for accessing the data by only the person who encrypted the data using his passkey, thus allowing for higher security. Typically, a file system is implemented in the kernel of the operating systems. However, with an increase in the complexity of the traditional file systems like ext3 and ext4, the ones that are based in the userspace of the OS are now allowing for additional features on top of them, such as encryption-decryption and compression. -

Ein Wilder Ritt Distributionen
09/2016 Besichtigungstour zu den skurrilsten Linux-Distributionen Titelthema Ein wilder Ritt Distributionen 28 Seit den frühen 90ern schießen die Linux-Distributionen wie Pilze aus dem Boden. Das Linux-Magazin blickt zurück auf ein paar besonders erstaunliche oder schräge Exemplare. Kristian Kißling www.linux-magazin.de © Antonio Oquias, 123RF Oquias, © Antonio Auch wenn die Syntax anderes vermu- samer Linux-Distributionen aufzustellen, Basis für Evil Entity denkt (Grün!), liegt ten lässt, steht der Name des klassischen denn in den zweieinhalb Jahrzehnten falsch. Tatsächlich basierte Evil Entity auf Linux-Tools »awk« nicht für Awkward kreuzte eine Menge von ihnen unseren Slackware und setzte auf einen eher düs- (zu Deutsch etwa „tolpatschig“), sondern Weg. Während einige davon noch putz- ter anmutenden Enlightenment-Desktop für die Namen seiner Autoren, nämlich munter in die Zukunft blicken, ist bei an- (Abbildung 3). Alfred Aho, Peter Weinberger und Brian deren nicht recht klar, welche Zielgruppe Als näher am Leben erwies sich der Fo- Kernighan. Kryptische Namen zu geben sie anpeilen oder ob sie überhaupt noch kus der Distribution, der auf dem Ab- sei eine lange etablierte Unix-Tradition, am Leben sind. spielen von Multimedia-Dateien lag – sie heißt es auf einer Seite des Debian-Wiki wollten doch nur Filme schauen. [1], die sich mit den Namen traditioneller Linux für Zombies Linux-Tools beschäftigt. Je kaputter, desto besser Denn, steht dort weiter, häufig halten Apropos untot: Die passende Linux- Entwickler die Namen ihrer Tools für Distribution für Zombies ließ sich recht Auch Void Linux [4], der Name steht selbsterklärend oder sie glauben, dass einfach ermitteln. Sie heißt Undead Linux je nach Übersetzung für „gleichgültig“ sie die User ohnehin nicht interessieren. -

A Brief Study and Comparison Of, Open Source Intrusion Detection System Tools
International Journal of Advanced Computational Engineering and Networking, ISSN: 2320-2106, Volume-1, Issue-10, Dec-2013 A BRIEF STUDY AND COMPARISON OF, OPEN SOURCE INTRUSION DETECTION SYSTEM TOOLS 1SURYA BHAGAVAN AMBATI, 2DEEPTI VIDYARTHI 1,2Defence Institute of Advanced Technology (DU) Pune –411025 Email: [email protected], [email protected] Abstract - As the world becomes more connected to the cyber world, attackers and hackers are becoming increasingly sophisticated to penetrate computer systems and networks. Intrusion Detection System (IDS) plays a vital role in defending a network against intrusion. Many commercial IDSs are available in marketplace but with high cost. At the same time open source IDSs are also available with continuous support and upgradation from large user community. Each of these IDSs adopts a different approaches thus may target different applications. This paper provides a quick review of six Open Source IDS tools so that one can choose the appropriate Open Source IDS tool as per their organization requirements. Keywords - Intrusion Detection, Open Source IDS, Network Securit, HIDS, NIDS. I. INTRODUCTION concentrate on the activities in a host without considering the activities in the computer networks. Every day, intruders are invading countless homes On the other hand, NIDS put its focus on computer and organisations across the country via virus, networks without examining the hosts’ activities. worms, Trojans, DoS/DDoS attacks by inserting bits Intrusion Detection methodologies can be classified of malicious code. Intrusion detection system tools as Signature based detection, Anomaly based helps in protecting computer and network from a detection and Stateful Protocol analysis based numerous threats and attacks. -

Ten Strategies of a World-Class Cybersecurity Operations Center Conveys MITRE’S Expertise on Accumulated Expertise on Enterprise-Grade Computer Network Defense
Bleed rule--remove from file Bleed rule--remove from file MITRE’s accumulated Ten Strategies of a World-Class Cybersecurity Operations Center conveys MITRE’s expertise on accumulated expertise on enterprise-grade computer network defense. It covers ten key qualities enterprise- grade of leading Cybersecurity Operations Centers (CSOCs), ranging from their structure and organization, computer MITRE network to processes that best enable effective and efficient operations, to approaches that extract maximum defense Ten Strategies of a World-Class value from CSOC technology investments. This book offers perspective and context for key decision Cybersecurity Operations Center points in structuring a CSOC and shows how to: • Find the right size and structure for the CSOC team Cybersecurity Operations Center a World-Class of Strategies Ten The MITRE Corporation is • Achieve effective placement within a larger organization that a not-for-profit organization enables CSOC operations that operates federally funded • Attract, retain, and grow the right staff and skills research and development • Prepare the CSOC team, technologies, and processes for agile, centers (FFRDCs). FFRDCs threat-based response are unique organizations that • Architect for large-scale data collection and analysis with a assist the U.S. government with limited budget scientific research and analysis, • Prioritize sensor placement and data feed choices across development and acquisition, enteprise systems, enclaves, networks, and perimeters and systems engineering and integration. We’re proud to have If you manage, work in, or are standing up a CSOC, this book is for you. served the public interest for It is also available on MITRE’s website, www.mitre.org. more than 50 years. -

LINUX JOURNAL (ISSN 1075-3583) Is Published Monthly by Belltown Media, Inc., 2121 Sage Road, Ste
EPUB, Kindle,SUBSCRIBERS Android, iPhone & iPad editions SQLAlchemy | ConVirt | Fabric | Azure | RaspberryFREE PiTO ™ Make Your Android Device Play with Your Linux Box A Look at SQLAlchemy’s Since 1994: The Original Magazine of the Linux Community Features SYSTEM FEBRUARY 2013 | ISSUE 226 | www.linuxjournal.com ADMINISTRATION Manage Your HOW TO: Virtual Handling Deployment R Packages with ConVirt Spin up Linux VMs on Azure Use Fabric for Sysadmin Tasks on Remote Machines PLUS: Use a Raspberry Pi as a Colocated Server Cover226-Final-banner.indd 1 1/24/13 11:08 AM LJ226-Feb013-bu.indd 2 1/23/13 1:06 PM visit us at www.siliconmechanics.com or call us toll free at 888-352-1173 RACKMOUNT SERVERS STORAGE SOLUTIONS HIGH-PERFORMANCE COMPUTING ““ Just Just becausebecause it’sit’s badass,badass, doesn’tdoesn’t meanmean it’sit’s aa game.”game.” Pierre, our new Operations Manager, is always looking for the right tools to get more work done in less time. That’s why he respects NVIDIA ® Tesla ® GPUs: he sees customers return again and again for more server products featuring hybrid CPU / GPU computing, like the Silicon Mechanics Hyperform HPCg R2504.v3. When you partner with We start with your choice of two state-of- Silicon Mechanics, you the-art processors, for fast, reliable, energy- get more than stellar efficient processing.T hen we add four NVIDIA ® technology - you get an Tesla® GPUs, to dramatically accelerate parallel Expert like Pierre. processing for applications like ray tracing and finite element analysis. Load it up with DDR3 memory, and you have herculean capabilities and an 80 PLUS Platinum Certified power supply, all in the space of a 4U server. -

Lightweight Virtualization with Gobolinux' Runner
Lightweight virtualization with GoboLinux’ Runner Lucas C. Villa Real [email protected] About GoboLinux ● Alternative distribution born in 2002 ● Explores novel ideas in the Linux distribution ecosystem ● Introduces a rather diferent directory hierarchy How diferent? lucasvr@fedora ~] ls / bin dev home lib64 media opt root sbin sys usr boot etc lib lost+found mnt proc run srv tmp var lucasvr@fedora ~] ls /usr bin games include lib lib64 libexec local sbin share src tmp lucasvr@fedora ~] ls /usr/local bin etc games include lib lib64 libexec sbin share src lucasvr@gobolinux ~] ls / Data Mount Programs System Users GoboLinux File System Hierarchy /Programs Self-contained programs: no need for a package manager ~] ls /Programs AbsTk DifUtils GnuTLS Kerberos LibXML2 ACL Dit GoboHide Kmod LibXSLT Acpid DosFSTools GParted Lame Linux AGNClient E2FSProgs Gperf LCMS Linux-Firmware ALSA-Lib EFIBootMgr GPM Less Linux-PAM ALSA-Utils ELFUtils Grep LibDRM Lsof APR EncFS Grof LibEvdev Lua APR-Util ExFAT GRUB LibExif LuaRocks … /Programs Multiple versions of a given program can coexist ~] ls /Programs/GTK+ 2.24.22 2.24.30 3.10.6 3.21.4 Current Settings ~] ls /Programs/GTK+/2.24.22 bin doc include lib Resources share ~] ls /Programs/GTK+/2.24.22/bin gtk-builder-convert gtk-demo gtk-query-immodules2.0 gtk-update-icon-cache ~] ls /Programs/GTK+/2.24.30/bin gtk-builder-convert gtk-demo gtk-query-immodules2.0 gtk-update-icon-cache /Programs Easy to tell which fles belongs to which packages lucasvr@fedora ~] ls -l /bin/bash -rwxr-xr-x. 1 root root 1072008