Symmetric Key Cryptography Rachel Greenstadt April 28, 2015 Reminders
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
25 Years of Linear Cryptanalysis -Early History and Path Search Algorithm
25 Years of Linear Cryptanalysis -Early History and Path Search Algorithm- Asiacrypt 2018, December 3 2018 Mitsuru Matsui © Mitsubishi Electric Corporation Back to 1990… 2 © Mitsubishi Electric Corporation FEAL (Fast data Encipherment ALgorithm) • Designed by Miyaguchi and Shimizu (NTT). • 64-bit block cipher family with the Feistel structure. • 4 rounds (1987) • 8 rounds (1988) • N rounds(1990) N=32 recommended • Key size is 64 bits (later extended to 128 bits). • Optimized for 8-bit microprocessors (no lookup tables). • First commercially successful cipher in Japan. • Inspired many new ideas, including linear cryptanalysis. 3 © Mitsubishi Electric Corporation FEAL-NX Algorithm [Miyaguchi 90] subkey 4 © Mitsubishi Electric Corporation The Round Function of FEAL 2-byte subkey Linear Relations 푌 2 = 푋1 0 ⊕ 푋2 0 푌 2 = 푋1 0 ⊕ 푋2 0 ⊕ 1 (푁표푡푎푡푖표푛: 푌 푖 = 푖-푡ℎ 푏푖푡 표푓 푌) 5 © Mitsubishi Electric Corporation Linear Relations of the Round Function Linear Relations 푂 16,26 ⊕ 퐼 24 = 퐾 24 K 푂 18 ⊕ 퐼 0,8,16,24 = 퐾 8,16 ⊕ 1 푂 10,16 ⊕ 퐼 0,8 = 퐾 8 S 0 푂 2,8 ⊕ 퐼 0 = 퐾 0 ⊕ 1 (푁표푡푎푡푖표푛: 퐴 푖, 푗, 푘 = 퐴 푖 ⊕ 퐴 푗 ⊕ 퐴 푘 ) S1 O I f S0 f 3-round linear relations with p=1 S1 f modified round function f at least 3 subkey (with whitening key) f bytes affect output6 6 © Mitsubishi Electric Corporation History of Cryptanalysis of FEAL • 4-round version – 100-10000 chosen plaintexts [Boer 88] – 20 chosen plaintexts [Murphy 90] – 8 chosen plaintexts [Biham, Shamir 91] differential – 200 known plaintexts [Tardy-Corfdir, Gilbert 91] – 5 known plaintexts [Matsui, Yamagishi -
The Data Encryption Standard (DES) – History
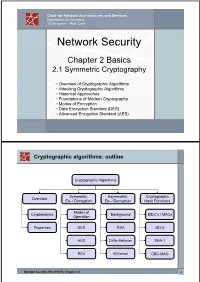
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -
Seed Maturity in White Fir and Red Fir. Pacific Southwest Forest and Range Exp
PACIFIC SOUTHWEST Forest and Range FOREST SERVICE U. S. DEPARTMENT OF AGRICULTURE P.O. BOX 245, BERKELEY, CALIFORNIA 94701 Experiment Station USDA FOREST SERVICE RESEARCH PAPER PSW-99 /1974 CONTENTS Page Summary ................................................... 1 Introduction ................................................. 3 Methods .................................................... 3 Testing Fresh Seeds ....................................... 3 Testing Stratified Seeds .................................... 3 Seedling Vigor Tests ...................................... 4 Artificial Ripening Trial ................................... 4 Other Observations ........................................ 4 Results and Discussion ....................................... 5 Cone Specific Gravity ..................................... 5 Seed Germination, byCollection Date ....................... 5 Seed GerminationandCone Specific Gravity ................ 7 Red Fir Seedling Vigor .................................... 9 ArtificialRipening of White Fir Seeds ....................... 9 OtherMaturity Indices ..................................... 9 Application ................................................. 10 Literature Cited.............................................. 12 THE AUTHOR WILLIAM W. OLIVER is doing silvicultural research on Sierra Nevada conifer types with headquarters at Redding, California. He earned a B.S. degree (1956) in forestry from the University of New Hampshire, and an M.F. degree (1960) from the University of Michigan. A native of -

Block Ciphers and the Data Encryption Standard
Lecture 3: Block Ciphers and the Data Encryption Standard Lecture Notes on “Computer and Network Security” by Avi Kak ([email protected]) January 26, 2021 3:43pm ©2021 Avinash Kak, Purdue University Goals: To introduce the notion of a block cipher in the modern context. To talk about the infeasibility of ideal block ciphers To introduce the notion of the Feistel Cipher Structure To go over DES, the Data Encryption Standard To illustrate important DES steps with Python and Perl code CONTENTS Section Title Page 3.1 Ideal Block Cipher 3 3.1.1 Size of the Encryption Key for the Ideal Block Cipher 6 3.2 The Feistel Structure for Block Ciphers 7 3.2.1 Mathematical Description of Each Round in the 10 Feistel Structure 3.2.2 Decryption in Ciphers Based on the Feistel Structure 12 3.3 DES: The Data Encryption Standard 16 3.3.1 One Round of Processing in DES 18 3.3.2 The S-Box for the Substitution Step in Each Round 22 3.3.3 The Substitution Tables 26 3.3.4 The P-Box Permutation in the Feistel Function 33 3.3.5 The DES Key Schedule: Generating the Round Keys 35 3.3.6 Initial Permutation of the Encryption Key 38 3.3.7 Contraction-Permutation that Generates the 48-Bit 42 Round Key from the 56-Bit Key 3.4 What Makes DES a Strong Cipher (to the 46 Extent It is a Strong Cipher) 3.5 Homework Problems 48 2 Computer and Network Security by Avi Kak Lecture 3 Back to TOC 3.1 IDEAL BLOCK CIPHER In a modern block cipher (but still using a classical encryption method), we replace a block of N bits from the plaintext with a block of N bits from the ciphertext. -

Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, Newdes, RC2, and TEA
Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, NewDES, RC2, and TEA John Kelsey Bruce Schneier David Wagner Counterpane Systems U.C. Berkeley kelsey,schneier @counterpane.com [email protected] f g Abstract. We present new related-key attacks on the block ciphers 3- WAY, Biham-DES, CAST, DES-X, NewDES, RC2, and TEA. Differen- tial related-key attacks allow both keys and plaintexts to be chosen with specific differences [KSW96]. Our attacks build on the original work, showing how to adapt the general attack to deal with the difficulties of the individual algorithms. We also give specific design principles to protect against these attacks. 1 Introduction Related-key cryptanalysis assumes that the attacker learns the encryption of certain plaintexts not only under the original (unknown) key K, but also under some derived keys K0 = f(K). In a chosen-related-key attack, the attacker specifies how the key is to be changed; known-related-key attacks are those where the key difference is known, but cannot be chosen by the attacker. We emphasize that the attacker knows or chooses the relationship between keys, not the actual key values. These techniques have been developed in [Knu93b, Bih94, KSW96]. Related-key cryptanalysis is a practical attack on key-exchange protocols that do not guarantee key-integrity|an attacker may be able to flip bits in the key without knowing the key|and key-update protocols that update keys using a known function: e.g., K, K + 1, K + 2, etc. Related-key attacks were also used against rotor machines: operators sometimes set rotors incorrectly. -

Camellia: a 128-Bit Block Cipher Suitable for Multiple Platforms
Copyright NTT and Mitsubishi Electric Corporation 2000 Camellia: A 128-Bit Block Cipher Suitable for Multiple Platforms † ‡ † Kazumaro Aoki Tetsuya Ichikawa Masayuki Kanda ‡ † ‡ ‡ Mitsuru Matsui Shiho Moriai Junko Nakajima Toshio Tokita † Nippon Telegraph and Telephone Corporation 1-1 Hikarinooka, Yokosuka, Kanagawa, 239-0847 Japan {maro,kanda,shiho}@isl.ntt.co.jp ‡ Mitsubishi Electric Corporation 5-1-1 Ofuna, Kamakura, Kanagawa, 247-8501 Japan {ichikawa,matsui,june15,tokita}@iss.isl.melco.co.jp September 26, 2000 Abstract. We present a new 128-bit block cipher called Camellia. Camellia sup- ports 128-bit block size and 128-, 192-, and 256-bit key lengths, i.e. the same interface specifications as the Advanced Encryption Standard (AES). Camellia was carefully designed to withstand all known cryptanalytic attacks and even to have a sufficiently large security leeway for use of the next 10-20 years. There are no hidden weakness inserted by the designers. It was also designed to have suitability for both software and hardware implementations and to cover all possible encryption applications that range from low-cost smart cards to high-speed network systems. Compared to the AES finalists, Camellia offers at least comparable encryption speed in software and hardware. An optimized implementation of Camellia in assembly language can en- crypt on a PentiumIII (800MHz) at the rate of more than 276 Mbits per second, which is much faster than the speed of an optimized DES implementation. In ad- dition, a distinguishing feature is its small hardware design. The hardware design, which includes key schedule, encryption and decryption, occupies approximately 11K gates, which is the smallest among all existing 128-bit block ciphers as far as we know. -

Report on the AES Candidates
Rep ort on the AES Candidates 1 2 1 3 Olivier Baudron , Henri Gilb ert , Louis Granb oulan , Helena Handschuh , 4 1 5 1 Antoine Joux , Phong Nguyen ,Fabrice Noilhan ,David Pointcheval , 1 1 1 1 Thomas Pornin , Guillaume Poupard , Jacques Stern , and Serge Vaudenay 1 Ecole Normale Sup erieure { CNRS 2 France Telecom 3 Gemplus { ENST 4 SCSSI 5 Universit e d'Orsay { LRI Contact e-mail: [email protected] Abstract This do cument rep orts the activities of the AES working group organized at the Ecole Normale Sup erieure. Several candidates are evaluated. In particular we outline some weaknesses in the designs of some candidates. We mainly discuss selection criteria b etween the can- didates, and make case-by-case comments. We nally recommend the selection of Mars, RC6, Serp ent, ... and DFC. As the rep ort is b eing nalized, we also added some new preliminary cryptanalysis on RC6 and Crypton in the App endix which are not considered in the main b o dy of the rep ort. Designing the encryption standard of the rst twentyyears of the twenty rst century is a challenging task: we need to predict p ossible future technologies, and wehavetotake unknown future attacks in account. Following the AES pro cess initiated by NIST, we organized an op en working group at the Ecole Normale Sup erieure. This group met two hours a week to review the AES candidates. The present do cument rep orts its results. Another task of this group was to up date the DFC candidate submitted by CNRS [16, 17] and to answer questions which had b een omitted in previous 1 rep orts on DFC. -

Development of the Advanced Encryption Standard
Volume 126, Article No. 126024 (2021) https://doi.org/10.6028/jres.126.024 Journal of Research of the National Institute of Standards and Technology Development of the Advanced Encryption Standard Miles E. Smid Formerly: Computer Security Division, National Institute of Standards and Technology, Gaithersburg, MD 20899, USA [email protected] Strong cryptographic algorithms are essential for the protection of stored and transmitted data throughout the world. This publication discusses the development of Federal Information Processing Standards Publication (FIPS) 197, which specifies a cryptographic algorithm known as the Advanced Encryption Standard (AES). The AES was the result of a cooperative multiyear effort involving the U.S. government, industry, and the academic community. Several difficult problems that had to be resolved during the standard’s development are discussed, and the eventual solutions are presented. The author writes from his viewpoint as former leader of the Security Technology Group and later as acting director of the Computer Security Division at the National Institute of Standards and Technology, where he was responsible for the AES development. Key words: Advanced Encryption Standard (AES); consensus process; cryptography; Data Encryption Standard (DES); security requirements, SKIPJACK. Accepted: June 18, 2021 Published: August 16, 2021; Current Version: August 23, 2021 This article was sponsored by James Foti, Computer Security Division, Information Technology Laboratory, National Institute of Standards and Technology (NIST). The views expressed represent those of the author and not necessarily those of NIST. https://doi.org/10.6028/jres.126.024 1. Introduction In the late 1990s, the National Institute of Standards and Technology (NIST) was about to decide if it was going to specify a new cryptographic algorithm standard for the protection of U.S. -
Linear (Hull) and Algebraic Cryptanalysis of the Block Cipher PRESENT
Linear (Hull) and Algebraic Cryptanalysis of the Block Cipher PRESENT Jorge Nakahara Jr1, Pouyan Sepehrdad1, Bingsheng Zhang2, Meiqin Wang3 1EPFL, Lausanne, Switzerland 2Cybernetica AS, Estonia and University of Tartu, Estonia 3Key Laboratory of Cryptologic Technology and Information Security, Ministry of Education, Shandong University, China Estonian Theory Days, 2-4.10.2009 Outline Why cryptanalysis?! Outline Outline Contributions The PRESENT Block Cipher Revisited Algebraic Cryptanalysis of PRESENT Linear Cryptanalysis of PRESENT Linear Hulls of PRESENT Conclusions Acknowledgements Outline Outline Contributions we performed linear analysis of reduced-round PRESENT exploiting fixed-points (and other symmetries) of pLayer exploiting low Hamming Weight bitmasks using iterative linear relations first linear hull analysis of PRESENT: 1st and 2nd best trails known-plaintext and ciphertext-only attack settings revisited algebraic analysis of 5-round PRESENT in less than 3 min best attacks on up to 26-round PRESENT (out of 31 rounds) Outline Outline The PRESENT Block Cipher block cipher designed by Bogdanov et al. at CHES’07 aimed at RFID tags, sensor networks (hardware environments) SPN structure 64-bit block size, 80- or 128-bit key size, 31 rounds one full round: xor with round subkey, S-box layer, bit permutation (pLayer) key schedule: 61-bit left rotation, S-box application, and xor with counter Outline Outline The PRESENT Block Cipher Computational graph of one full round of PRESENT Outline Outline Previous attack complexities on reduced-round -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Symmetric Cryptography Chapter 6 Block vs Stream Ciphers • Block ciphers process messages into blocks, each of which is then en/decrypted – Like a substitution on very big characters • 64-bits or more • Stream ciphers process messages a bit or byte at a time when en/decrypting – Many current ciphers are block ciphers • Better analyzed. • Broader range of applications. Block vs Stream Ciphers Block Cipher Principles • Block ciphers look like an extremely large substitution • Would need table of 264 entries for a 64-bit block • Arbitrary reversible substitution cipher for a large block size is not practical – 64-bit general substitution block cipher, key size 264! • Most symmetric block ciphers are based on a Feistel Cipher Structure • Needed since must be able to decrypt ciphertext to recover messages efficiently Ideal Block Cipher Substitution-Permutation Ciphers • in 1949 Shannon introduced idea of substitution- permutation (S-P) networks – modern substitution-transposition product cipher • These form the basis of modern block ciphers • S-P networks are based on the two primitive cryptographic operations we have seen before: – substitution (S-box) – permutation (P-box) (transposition) • Provide confusion and diffusion of message Diffusion and Confusion • Introduced by Claude Shannon to thwart cryptanalysis based on statistical analysis – Assume the attacker has some knowledge of the statistical characteristics of the plaintext • Cipher needs to completely obscure statistical properties of original message • A one-time pad does this Diffusion -
Security Analysis of an Encryption Scheme Based on Nonpositional Polynomial Notations
Open Eng. 2016; 6:250–258 Research Article Open Access Nursulu Kapalova* and Dilmukhanbet Dyusenbayev Security analysis of an encryption scheme based on nonpositional polynomial notations DOI 10.1515/eng-2016-0034 unique providing that bases are pairwise relatively prime. Received May 05, 2016; accepted Jun 28, 2016 As distinct from classical RNSs, irreducible polynomials over GF(2) that is binary polynomials serve as bases in Abstract: The aim of the research was to conduct a cryp- NPNs [1–6]. tographic analysis of an encryption scheme developed Based on NPNs, nonconventional algorithms for en- on the basis of nonpositional polynomial notations to cryption, digital signatures and cryptographic key ex- estimate the algorithm strength. Nonpositional polyno- change have been developed [3, 7–9]. This paper is con- mial notations (NPNs) are residue number systems (RNSs) cerned with an investigation of the strength of a noncon- based on irreducible polynomials over GF(2). To evalu- ventional encryption scheme against cryptanalysis. The ate if the algorithms developed on the basis of NPNs are core of the algorithm under study is as follows. secure, mathematical models of cryptanalysis involving algebraic, linear and differential methods have been de- 1. First of all, an NPN is formed with its working bases signed. The cryptanalysis is as follows. A system of non- consisting of chosen irreducible polynomials linear equations is obtained from a function transforming p x p x ... p x plaintext into ciphertext with a key. Next, a possibility of 1( ), 2( ), , S( ) (1) transition of the nonlinear system to a linear one is consid- over GF(2) of degrees m1, m2, .. -
Symmetric Encryption: AES
Symmetric Encryption: AES Yan Huang Credits: David Evans (UVA) Advanced Encryption Standard ▪ 1997: NIST initiates program to choose Advanced Encryption Standard to replace DES ▪ Why not just use 3DES? 2 AES Process ▪ Open Design • DES: design criteria for S-boxes kept secret ▪ Many good choices • DES: only one acceptable algorithm ▪ Public cryptanalysis efforts before choice • Heavy involvements of academic community, leading public cryptographers ▪ Conservative (but “quick”): 4 year process 3 AES Requirements ▪ Secure for next 50-100 years ▪ Royalty free ▪ Performance: faster than 3DES ▪ Support 128, 192 and 256 bit keys • Brute force search of 2128 keys at 1 Trillion keys/ second would take 1019 years (109 * age of universe) 4 AES Round 1 ▪ 15 submissions accepted ▪ Weak ciphers quickly eliminated • Magenta broken at conference! ▪ 5 finalists selected: • MARS (IBM) • RC6 (Rivest, et. al.) • Rijndael (Belgian cryptographers) • Serpent (Anderson, Biham, Knudsen) • Twofish (Schneier, et. al.) 5 AES Evaluation Criteria 1. Security Most important, but hardest to measure Resistance to cryptanalysis, randomness of output 2. Cost and Implementation Characteristics Licensing, Computational, Memory Flexibility (different key/block sizes), hardware implementation 6 AES Criteria Tradeoffs ▪ Security v. Performance • How do you measure security? ▪ Simplicity v. Complexity • Need complexity for confusion • Need simplicity to be able to analyze and implement efficiently 7 Breaking a Cipher ▪ Intuitive Impression • Attacker can decrypt secret messages • Reasonable amount of work, actual amount of ciphertext ▪ “Academic” Ideology • Attacker can determine something about the message • Given unlimited number of chosen plaintext-ciphertext pairs • Can perform a very large number of computations, up to, but not including, 2n, where n is the key size in bits (i.e.