8 a Virtualized Separation Kernel for Mixed-Criticality Systems
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Software Model Checking of ARINC-653 Flight Code with MCP Sarah J
Software Model Checking of ARINC-653 Flight Code with MCP Sarah J. Thompson Guillaume Brat SGT Inc., NASA Ames Research Center CMU, NASA Ames Research Center MS269-1, Moffett Field, California MS-269-1, Moffett Field, California [email protected] [email protected] Arnaud Venet SGT Inc., NASA Ames Research Center MS269-1, Moffett Field, California [email protected] Abstract The ARINC-653 standard defines a common interface for Integrated Modular Avionics (IMA) code. In particular, ARINC-653 Part 1 specifies a process- and partition-management API that is analogous to POSIX threads, but with certain extensions and restrictions intended to support the implementation of high reliability flight code. MCP is a software model checker, developed at NASA Ames, that provides capabilities for model checking C and C++ source code. In this paper, we present recent work aimed at implementing extensions to MCP that support ARINC-653, and we discuss the challenges and opportunities that consequentially arise. Providing support for ARINC-653’s time and space partitioning is nontrivial, though there are implicit benefits for partial order reduction possible as a consequence of the API’s strict interprocess communication policy. 1 Introduction NASA missions are becoming increasingly complex, and, more and more of this complexity is imple- mented in software. In 1977, the flight software for the Voyager mission amounted to only 3000 lines. Twenty years later, the software for Cassini had grown by a factor of ten, and more strikingly, the soft- ware for the Mars Path Finder mission amounted to 160 KLOCs (thousands of lines of code). -

Communications for Integrated Modular Avionics
Communications for Integrated Modular Avionics Richard L. Alena [email protected] John P. Ossenfort IV, SAIC Kenneth I. Laws, QSS Andre Goforth NASA Ames Research Center Moffett Field, CA 94035 Fernando Figueroa, NASA Stennis Space Center TABLE OF CONTENTS Abstract—The aerospace industry has been adopting avionics architectures to take advantage of advances in computer engineering. Integrated Modular Avionics (IMA), 1. INTRODUCTION ..................................................... 1 as described in ARINC 653, distributes functional modules 2. INTEGRATED MODULAR AVIONICS...................... 2 into a robust configuration interconnected with a “virtual 3. NETWORKS FOR AEROSPACE ............................... 4 backplane” data communications network. Each avionics 4. MISSION COMPUTER DESIGN............................... 8 module’s function is defined in software compliant with the 5. LAB EVALUATION............................................... 12 APEX Application Program Interface. The Avionics Full- 6. CONCLUSIONS..................................................... 16 Duplex Ethernet (AFDX) network replaces the point-to- REFERENCES........................................................... 17 point connections used in previous distributed systems with BIOGRAPHY ............................................................ 18 “virtual links”. This network creates a command and data path between avionics modules with the software and 1. INTRODUCTION network defining the active virtual links over an integrated physical network. -
Formal Modelling of Separation Kernels
The University of York Department of Computer Science Submitted in part fulfilment for the degree of MSc in Software Engineering. Formal Modelling of Separation Kernels Andrius Velykis 18th September 20091 Supervised by Dr Leo Freitas Number of words = 45327, as counted by detex <report.tex> j wc -w. This report consists of 98 pages in total. This includes the body of the report (without blank pages) and Appendix A, but not Appendices B, C, D, E and F. 1Updated transactional operation proofs, 21st September 2009. Abstract A separation kernel is an architecture for secure applications, which benefits from inherent security of distributed systems. Due to its small size and usage in high-integrity environments, it makes a good target for formal modelling and verification. This project presents results from mechanisation and modelling of separation kernel components: a process table, a process queue and a scheduler. The results have been developed as a part of the pilot project within the international Grand Challenge in Verified Software. This thesis covers full development life-cycle from project initiation through design and evaluation to successful completion. Important findings about kernel properties, formal modelling and design decisions are discussed. The developed formal specification is fully verified and contributes to the pilot project aim of creating a formal kernel model and refining it down to implementation code. Other reusable artefacts, such as general lemmas and a new technique of ensuring transactional properties of operations are defined. The results will be curated within the Verified Software Repository. i Robertai. Aˇci¯u. Acknowledgements I would like to thank Dr Leo Freitas for his supervision, encouragement and getting me hooked on formal methods. -

Avionics Applications on a Time-Predictable Chip-Multiprocessor
Avionics Applications on a Time-predictable Chip-Multiprocessor Andre´ Rocha and Claudio´ Silva Rasmus Bo Sørensen, Jens Sparsø, and Martin Schoeberl GMV Department of Applied Mathematics and Computer Science Lisbon, Portugal Technical University of Denmark Email: [andre.rocha, claudio.silva]@gmv.com Email: [rboso, jspa, masca]@dtu.dk Abstract—Avionics applications need to be certified for The demonstrators were ported to the T-CREST platform the highest criticality standard. This certification includes using its compiler tool-chain and analysis tools. The demon- schedulability analysis and worst-case execution time (WCET) strators validate the T-CREST platform. Part of the exercise, analysis. WCET analysis is only possible when the software is written to be WCET analyzable and when the platform is however, is to evaluate the added value of the platform. The time-predictable. In this paper we present prototype avionics platform shall enable application developers to determine the applications that have been ported to the time-predictable WCET of their applications more precisely or more easily. T-CREST platform. The applications are WCET analyzable, Therefore, we compare the T-CREST platform with a well- and T-CREST is supported by the aiT WCET analyzer. This established platform in the avionics domain. combination allows us to provide WCET bounds of avionic tasks, even when executing on a multicore processor. The T-CREST platform was evaluated with the aid of the following three real-world avionic applications: (1) an Airlines Operational Centre (AOC), (2) a Crew Alerting I. INTRODUCTION System (CAS), and (3) an I/O Partition (IOP). We chose The mission of the T-CREST project [1], [2] is to develop T-CREST as platform for avionics applications as this is and build a multicore processor that is time-predictable and currently the only multicore processor where static WCET easy to analyze for the worst-case execution time (WCET). -

Lynuxworks Lynxsecure Embedded Hypervisor and Separation
Operating systems: RTOS and tools Software LynuxWorks, Inc. 855 Embedded Way • San Jose, CA 95138 800-255-5969 www.lynuxworks.com LynxSecure Embedded Hypervisor and Separation Kernel With the introduction of the new LynxSecure separation kernel and embedded hypervisor, LynuxWorks once again raises the bar when it comes to superior embedded software security and safety. LynxSecure has been built from the ground up as a real-time separa- tion kernel able to run different operating systems and applications in their own secure partitions. The LynxSecure separation kernel is a virtual machine monitor that is certifi able to (a) Common Criteria EAL 7 (Evaluated Assurance Level 7) security certifi cation, a level of certifi cation unattained by any known operating system to date; and (b) DO-178B Level A, the highest level of FAA certifi cation for safety-critical avionics applications. LynxSecure conforms to the Multiple Independent Levels of Security/ Safety (MILS) architecture. The embedded hypervisor component of LynxSecure allows multiple “guest” operating systems to run in their own secure partitions. These can be run in either paravirtual- ized or fully virtualized modes, helping preserve legacy applications and operating systems in systems that now have a security require- FEATURES ment. Guest operating systems include the LynxOS family, Linux and › Optimal security and safety – the only operating system designed to Windows. support CC EAL 7 and DO-178B Level A › Real time – time-space partitioned RTOS for superior determinism and performance -

Extensible Distributed Operating System for Reliable Control Systems
194 Extensible Distributed Operating System for Reliable Control Systems Katsumi Maruyama, Kazuya Kodama, Soichiro Hidaka, Hiromichi Hashizume National Institute of Informatics, 2-1-2 Hitotsubashi, Chiyoda-ku, Tokyo, Japan Email:{maruyama,kazuya,hidaka,has}@nii.ac.jp Abstract small monitor-like OSs are used. However, these monitor- like OSs lack program protection mechanisms, and program Since most control systems software is hardware-related, development is difficult. real-time-oriented and complex, adaptable OSs which help Therefore, an extensible/adaptable OS for control sys- program productivity and maintainability improvement are tems is required . We are developing a new OS character- in strong demand. ized by: We are developing an adaptable and extensible OS based on micro-kernel and multi-server scheme: each server runs • Use of an efficient and flexible micro-kernel (L4-ka). • Multi-server based modular OS. (Each OS service is in a protected mode interacting only via messages, and implemented as individual user-level process.) could be added/extended/deleted easily. Since this OS is • Robustness. Only the micro-kernel runs in kernel highly modularized, inter-process messaging overhead is a mode and in kernel space. Other modules run in a pro- concern. Our implementation proved good efficiency and tected user space and mode. maintainability. • Hardware driver programs in user-level process. • Flexible distributed processing by global message passing. 1. Introduction This OS structure proved to enhance OS modularity and ease of programming. However, inter-process messaging Most systems, from large scale public telephone switch- overhead should be considered . We measured the overhead, ing systems to home electronics, are controlled by software, and the overhead was proved to be small enough. -
Cloud Computing Bible Is a Wide-Ranging and Complete Reference
A thorough, down-to-earth look Barrie Sosinsky Cloud Computing Barrie Sosinsky is a veteran computer book writer at cloud computing specializing in network systems, databases, design, development, The chance to lower IT costs makes cloud computing a and testing. Among his 35 technical books have been Wiley’s Networking hot topic, and it’s getting hotter all the time. If you want Bible and many others on operating a terra firma take on everything you should know about systems, Web topics, storage, and the cloud, this book is it. Starting with a clear definition of application software. He has written nearly 500 articles for computer what cloud computing is, why it is, and its pros and cons, magazines and Web sites. Cloud Cloud Computing Bible is a wide-ranging and complete reference. You’ll get thoroughly up to speed on cloud platforms, infrastructure, services and applications, security, and much more. Computing • Learn what cloud computing is and what it is not • Assess the value of cloud computing, including licensing models, ROI, and more • Understand abstraction, partitioning, virtualization, capacity planning, and various programming solutions • See how to use Google®, Amazon®, and Microsoft® Web services effectively ® ™ • Explore cloud communication methods — IM, Twitter , Google Buzz , Explore the cloud with Facebook®, and others • Discover how cloud services are changing mobile phones — and vice versa this complete guide Understand all platforms and technologies www.wiley.com/compbooks Shelving Category: Use Google, Amazon, or -

MILS Architectural Approach Supporting Trustworthiness of the Iiot Solutions
MILS Architectural Approach Supporting Trustworthiness of the IIoT Solutions An Industrial Internet Consortium Whitepaper Rance J. DeLong (The Open Group); Ekaterina Rudina (Kaspersky) MILS Architectural Approach Context and Overview 1 Context and Overview ...................................................................................................... 4 1.1 Need for Trustworthy System Operation ............................................................................. 5 1.2 What is MILS today .............................................................................................................. 6 1.3 How MILS Addresses Safety ................................................................................................. 7 1.4 How MILS Addresses Security .............................................................................................. 8 1.5 How MILS Supports Reliability, Resilience, and Privacy ........................................................ 9 2 MILS Concepts .................................................................................................................. 9 2.1 Centralized vs Distributed Security Architecture .................................................................. 9 2.1.1 Domain Isolation .................................................................................................................................. 10 2.1.2 Isolation and Information Flow Control ............................................................................................... 11 2.1.3 Separation -
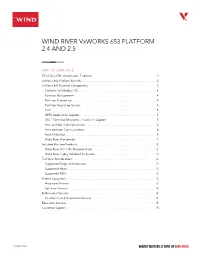
WIND RIVER Vxworks 653 PLATFORM 2.4 and 2.5
WIND RIVER VxWORKS 653 PLATFORM 2.4 AND 2.5 TABLE OF CONTENTS RTCA DO-178C Certification Evidence .......................................... 2 VxWorks 653 Platform Benefits ................................................. 2 VxWorks 653 Runtime Components ............................................ 3 VxWorks 653 Module OS ................................................... 4 Partition Management ..................................................... 4 Partition Scheduling ....................................................... 4 Partition Operating System ................................................. 4 COIL .................................................................... 5 APEX Application Support .................................................. 5 FACE Technical Reference 2.0 and 2.1 Support ................................ 5 Inter-partition Communication ............................................... 6 Intra-partition Communication ............................................... 6 Health Monitor ........................................................... 6 Wind River Workbench ..................................................... 7 Included Runtime Products .................................................. 12 Wind River DO-178C Network Stack ......................................... 12 Wind River Highly Reliable File System ....................................... 12 Technical Specifications ..................................................... 12 Supported Target Architectures ........................................... -

Towards a Real-Time Component Framework for Software Health Management
Institute for Software Integrated Systems Vanderbilt University Nashville, Tennessee, 37203 Towards a Real-time Component Framework for Software Health Management Abhishek Dubey , Gabor Karsai , Robert Kereskenyi , Nagabhushan Mahadevan TECHNICAL REPORT ISIS-09-111 November, 2009 Towards a Real-time Component Framework for Software Health Management Abhishek Dubey Gabor Karsai Robert Kereskenyi Nagabhushan Mahadevan Institute for Software Integrated Systems, Vanderbilt University, Nashville, TN 37203, USA Abstract— The complexity of software in systems like aerospace industry, that deals with detecting anomalies, di- aerospace vehicles has reached the point where new techniques agnosing failure sources, and prognosticating future failures are needed to ensure system dependability. Such techniques in complex systems, like aerospace vehicles. While System include a novel direction called ‘Software Health Management’ (SHM) that extends classic software fault tolerance with tech- Health Management has been developed for physical (hard- niques borrowed from System Health Management. In this ware) systems, it provides interesting systems engineering paper the initial steps towards building a SHM approach are techniques for other fields like embedded software systems. described that combine component-based software construction The use of System Health Management techniques for with hard real-time operating system platforms. Specifically, embedded software systems points beyond the capabilities the paper discusses how the CORBA Component Model could be combined with the ARINC-653 platform services and the provided by the SFT techniques and can potentially in- lessons learned from this experiment. The results point towards crease a system’s dependability. This new direction is called both extending the CCM as well as revising the ARINC-653. Software Health Management (SHM) [4]. -

(DBATU Iope) Question Bank (MCQ) Cloud Computing Elective II
Diploma in Computer Engineering (DBATU IoPE) Question Bank (MCQ) Cloud Computing Elective II (DCE3204A) Summer 2020 Exam (To be held in October 2020 - Online) Prepared by Prof. S.M. Sabale Head of Computer Engineering Institute of Petrochemical Engineering, Lonere Id 1 Question Following are the features of cloud computing: (CO1) A Reliability B Centralized computing C Location dependency D No need of internet connection Answer Marks 2 Unit I Id 2 Question Which is the property that enables a system to continue operating properly in the event of the failure of some of its components? (CO1) A Availability B Fault-tolerance C Scalability D System Security Answer Marks 2 Unit I Id 3 Question A _____________ is a contract between a network service provider and a customer that specifies, usually in measurable terms (QoS), what services the network service provider will furnish (CO1) A service-level agreement B service-level specifications C document D agreement Answer Marks 2 Unit I Id 4 Question The degree to which a system, subsystem, or equipment is in a specified operable and committable state at the start of a mission, when the mission is called for at an unknown time is called as _________ (CO1) A reliability B Scalability C Availability D system resilience Answer Marks 2 Unit I Id 5 Question Google Apps is an example of (CO1) A IaaS B SaaS C PaaS D Both PaaS and SaaS Answer Marks 2 Unit I Id 6 Question Separation of a personal computer desktop environment from a physical machine through the client server model of computing is known as __________. -

National Information Assurance Partnership
National Information Assurance Partnership ® TM Common Criteria Evaluation and Validation Scheme Validation Report Green Hills Software INTEGRITY-178B Separation Kernel Report Number: CCEVS-VR-10119-2008 Dated: 01 September 2008 Version: 1.0 National Institute of Standards and Technology National Security Agency Information Technology Laboratory Information Assurance Directorate 100 Bureau Drive 9800 Savage Road STE 6757 Gaithersburg, MD 20899 Fort George G. Meade, MD 20755-6757 VALIDATION REPORT Green Hills Software INTEGRITY-178B Separation Kernel ACKNOWLEDGEMENTS Validation Team Shaun Gilmore Santosh Chokhani Ken Elliott Jerry Myers Paul Bicknell Common Criteria Testing Laboratory SAIC, Inc. Columbia, Maryland ii VALIDATION REPORT Green Hills Software INTEGRITY-178B Separation Kernel Table of Contents 1 Executive Summary................................................................1 1.1 Evaluation Details.............................................................2 2 Identification...........................................................................4 3 Threats to Security ..................................................................5 4 Security Policy........................................................................7 5 Assumptions............................................................................8 5.1 Physical Assumptions .......................................................8 5.2 Personnel Assumptions.....................................................8 5.3 Connectivity Assumptions................................................8