2017 Global Cyber Attack Trends Report TABLE of CONTENTS | 2
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
BUGS in the SYSTEM a Primer on the Software Vulnerability Ecosystem and Its Policy Implications
ANDI WILSON, ROSS SCHULMAN, KEVIN BANKSTON, AND TREY HERR BUGS IN THE SYSTEM A Primer on the Software Vulnerability Ecosystem and its Policy Implications JULY 2016 About the Authors About New America New America is committed to renewing American politics, Andi Wilson is a policy analyst at New America’s Open prosperity, and purpose in the Digital Age. We generate big Technology Institute, where she researches and writes ideas, bridge the gap between technology and policy, and about the relationship between technology and policy. curate broad public conversation. We combine the best of With a specific focus on cybersecurity, Andi is currently a policy research institute, technology laboratory, public working on issues including encryption, vulnerabilities forum, media platform, and a venture capital fund for equities, surveillance, and internet freedom. ideas. We are a distinctive community of thinkers, writers, researchers, technologists, and community activists who Ross Schulman is a co-director of the Cybersecurity believe deeply in the possibility of American renewal. Initiative and senior policy counsel at New America’s Open Find out more at newamerica.org/our-story. Technology Institute, where he focuses on cybersecurity, encryption, surveillance, and Internet governance. Prior to joining OTI, Ross worked for Google in Mountain About the Cybersecurity Initiative View, California. Ross has also worked at the Computer The Internet has connected us. Yet the policies and and Communications Industry Association, the Center debates that surround the security of our networks are for Democracy and Technology, and on Capitol Hill for too often disconnected, disjointed, and stuck in an Senators Wyden and Feingold. unsuccessful status quo. -

Botection: Bot Detection by Building Markov Chain Models of Bots Network Behavior Bushra A
BOTection: Bot Detection by Building Markov Chain Models of Bots Network Behavior Bushra A. Alahmadi Enrico Mariconti Riccardo Spolaor University of Oxford, UK University College London, UK University of Oxford, UK [email protected] [email protected] [email protected] Gianluca Stringhini Ivan Martinovic Boston University, USA University of Oxford, UK [email protected] [email protected] ABSTRACT through DDoS (e.g. DDoS on Estonia [22]), email spam (e.g. Geodo), Botnets continue to be a threat to organizations, thus various ma- ClickFraud (e.g. ClickBot), and spreading malware (e.g. Zeus). 10,263 chine learning-based botnet detectors have been proposed. How- malware botnet controllers (C&C) were blocked by Spamhaus Mal- ever, the capability of such systems in detecting new or unseen ware Labs in 2018 alone, an 8% increase from the number of botnet 1 botnets is crucial to ensure its robustness against the rapid evo- C&Cs seen in 2017. Cybercriminals are actively monetizing bot- lution of botnets. Moreover, it prolongs the effectiveness of the nets to launch attacks, which are evolving significantly and require system in detecting bots, avoiding frequent and time-consuming more effective detection mechanisms capable of detecting those classifier re-training. We present BOTection, a privacy-preserving which are new or unseen. bot detection system that models the bot network flow behavior Botnets rely heavily on network communications to infect new as a Markov Chain. The Markov Chains state transitions capture victims (propagation), to communicate with the C&C server, or the bots’ network behavior using high-level flow features as states, to perform their operational task (e.g. -

Volume 108, Issue 12
BObcaTS TEAM UP BU STUDENT WINS WITH CHRISTMAS MCIE AwaRD pg. 2 CHEER pg. 3 VOL. 108 | ISSUE NO.12| NOVEMBER 28TH, 2017 ...caFFEINE... SINCE 1910 LONG NIGHT AG A INST PROCR A STIN A TION ANOTHER SUCCESS Students cracking down and getting those assignments out of the way. Photo Credit: Patrick Gohl. Patrick Gohl, Reporter am sure the word has spread Robbins Library on Wednesday in the curriculum area. If you of the whole event. I will now tinate. I around campus already, ex- the 22nd of November. were a little late for your sched- remedy this grievous error and Having made it this far in ams are just around the cor- The event was designed to uled session you were likely to make mention of the free food. the semester, one could be led ner. ‘Tis the season to toss your combat study procrastination, get bumped back as there were Healthy snacks such as apples to believe, quite incorrectly, amassed library of class notes in and encourage students to be- many students looking for help and bananas were on offer from that the home stretch is more of frustration, to scream at your gin their exam preparation. It all to gain that extra edge on their the get go along with tea and the same. This falsehood might computer screen like a mad- started at 7:00PM and ran until assignments and exams. coffee. Those that managed be an alluring belief to grasp man, and soak your pillow with 3:00AM the following morn- In addition to the academic to last until midnight were re- hold of when the importance to tears of desperation. -

The Million Dollar Dissident: NSO Group's Iphone Zero-Days Used Against a UAE Human Rights Defender
Research Teaching News Lab Projects GLA2010 In the News About Publications Newsletter People Archives Events Opportunities Contact The Million Dollar Dissident: NSO Group’s iPhone Zero-Days used against a UAE Human Rights Defender August 24, 2016 Categories: Bill Marczak, John Scott-Railton, Reports and Briefings Authors: Bill Marczak and John Scott-Railton, Senior Researchers at the Citizen Lab, with the assistance of the research team at Lookout Security. Media coverage: The New York Times, Motherboard, Gizmodo, Wired, Washington Post, ZDNet. This report describes how a government targeted an internationally recognized human rights defender, Ahmed Mansoor, with the Trident, a chain of zero-day exploits designed to infect his iPhone with sophisticated commercial spyware. 1. Executive Summary Ahmed Mansoor is an internationally recognized human rights defender, based in the United Arab Emirates (UAE), and recipient of the Martin Ennals Award (sometimes referred to as a “Nobel Prize for human rights”). On August 10 and 11, 2016, Mansoor received SMS text messages on his iPhone promising “new secrets” about detainees tortured in UAE jails if he clicked on an included link. Instead of clicking, Mansoor sent the messages to Citizen Lab researchers. We recognized the links as belonging to an exploit infrastructure connected to NSO Group, an Israel-based “cyber war” company that sells Pegasus, a government- exclusive “lawful intercept” spyware product. NSO Group is reportedly owned by an American venture capital firm, Francisco Partners Management. The ensuing investigation, a collaboration between researchers from Citizen Lab and from Lookout Security, determined that the links led to a chain of zero-day exploits (“zero-days”) that would have remotely jailbroken Mansoor’s stock iPhone 6 and installed sophisticated spyware. -
BUGS in the SYSTEM a Primer on the Software Vulnerability Ecosystem and Its Policy Implications
ANDI WILSON, ROSS SCHULMAN, KEVIN BANKSTON, AND TREY HERR BUGS IN THE SYSTEM A Primer on the Software Vulnerability Ecosystem and its Policy Implications JULY 2016 About the Authors About New America New America is committed to renewing American politics, Andi Wilson is a policy analyst at New America’s Open prosperity, and purpose in the Digital Age. We generate big Technology Institute, where she researches and writes ideas, bridge the gap between technology and policy, and about the relationship between technology and policy. curate broad public conversation. We combine the best of With a specific focus on cybersecurity, Andi is currently a policy research institute, technology laboratory, public working on issues including encryption, vulnerabilities forum, media platform, and a venture capital fund for equities, surveillance, and internet freedom. ideas. We are a distinctive community of thinkers, writers, researchers, technologists, and community activists who Ross Schulman is a co-director of the Cybersecurity believe deeply in the possibility of American renewal. Initiative and senior policy counsel at New America’s Open Find out more at newamerica.org/our-story. Technology Institute, where he focuses on cybersecurity, encryption, surveillance, and Internet governance. Prior to joining OTI, Ross worked for Google in Mountain About the Cybersecurity Initiative View, California. Ross has also worked at the Computer The Internet has connected us. Yet the policies and and Communications Industry Association, the Center debates that surround the security of our networks are for Democracy and Technology, and on Capitol Hill for too often disconnected, disjointed, and stuck in an Senators Wyden and Feingold. unsuccessful status quo. -

2015 Threat Report Provides a Comprehensive Overview of the Cyber Threat Landscape Facing Both Companies and Individuals
THREAT REPORT 2015 AT A GLANCE 2015 HIGHLIGHTS A few of the major events in 2015 concerning security issues. 08 07/15: Hacking Team 07/15: Bugs prompt 02/15: Europol joint breached, data Ford, Range Rover, 08/15: Google patches op takes down Ramnit released online Prius, Chrysler recalls Android Stagefright botnet flaw 09/15: XcodeGhost 07/15: Android 07/15: FBI Darkode tainted apps prompts Stagefright flaw 08/15: Amazon, ENFORCEMENT bazaar shutdown ATTACKS AppStore cleanup VULNERABILITY reported SECURITYPRODUCT Chrome drop Flash ads TOP MALWARE BREACHING THE MEET THE DUKES FAMILIES WALLED GARDEN The Dukes are a well- 12 18 resourced, highly 20 Njw0rm was the most In late 2015, the Apple App prominent new malware family in 2015. Store saw a string of incidents where dedicated and organized developers had used compromised tools cyberespionage group believed to be to unwittingly create apps with malicious working for the Russian Federation since behavior. The apps were able to bypass at least 2008 to collect intelligence in Njw0rm Apple’s review procedures to gain entry support of foreign and security policy decision-making. Angler into the store, and from there into an ordinary user’s iOS device. Gamarue THE CHAIN OF THE CHAIN OF Dorkbot COMPROMISE COMPROMISE: 23 The Stages 28 The Chain of Compromise Nuclear is a user-centric model that illustrates Kilim how cyber attacks combine different Ippedo techniques and resources to compromise Dridex devices and networks. It is defined by 4 main phases: Inception, Intrusion, WormLink Infection, and Invasion. INCEPTION Redirectors wreak havoc on US, Europe (p.28) INTRUSION AnglerEK dominates Flash (p.29) INFECTION The rise of rypto-ransomware (p.31) THREATS BY REGION Europe was particularly affected by the Angler exploit kit. -

Power-Law Properties in Indonesia Internet Traffic. Why Do We Care About It
by Bisyron Wahyudi Muhammad Salahuddien Amount of malicious traffic circulating on the Internet is increasing significantly. Increasing complexity and rapid change in hosts and networks technology suggests that there will be new vulnerabilities. Attackers have interest in identifying networks and hosts to expose vulnerabilities : . Network scans . Worms . Trojans . Botnet Complicated methods of attacks make difficult to identify the real attacks : It is not simple as filtering out the traffic from some sources Security is implemented like an “add on” module for the Internet. Understanding nature behavior of malicious sources and targeted ports is important to minimize the damage by build strong specific security rules and counter measures Help the cyber security policy-making process, and to raise public awareness Questions : . Do malicious sources generate the attacks uniformly ? . Is there any pattern specific i.e. recurrence event ? . Is there any correlation between the number of some attacks over specific time ? Many systems and phenomena (events) are distributed according to a “power law” When one quantity (say y) depends on another (say x) raised to some power, we say that y is described by a power law A power law applies to a system when: . large is rare and . small is common Collection of System logs from Networked Intrusion Detection System (IDS) The NIDS contains 11 sensors installed in different core networks in Indonesian ISP (NAP) Period : January, 2012 - September, 2012 . Available fields : ▪ Event Message, Timestamp, Dest. IP, Source IP, Attacks Classification, Priority, Protocol, Dest. Port/ICMP code, Source Port/ICMP type, Sensors ID Two quantities x and y are related by a power law if y is proportional to x(-c) for a constant c y = .x(-c) If x and y are related by a power law, then the graph of log(y) versus log(x) is a straight line log(y) = -c.log(x) + log() The slope of the log-log plot is the power exponent c Destination Port Distribution . -
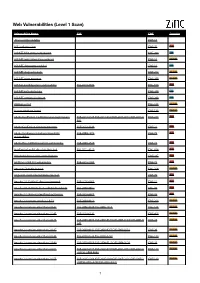
Web Vulnerabilities (Level 1 Scan)
Web Vulnerabilities (Level 1 Scan) Vulnerability Name CVE CWE Severity .htaccess file readable CWE-16 ASP code injection CWE-95 High ASP.NET MVC version disclosure CWE-200 Low ASP.NET application trace enabled CWE-16 Medium ASP.NET debugging enabled CWE-16 Low ASP.NET diagnostic page CWE-200 Medium ASP.NET error message CWE-200 Medium ASP.NET padding oracle vulnerability CVE-2010-3332 CWE-310 High ASP.NET path disclosure CWE-200 Low ASP.NET version disclosure CWE-200 Low AWStats script CWE-538 Medium Access database found CWE-538 Medium Adobe ColdFusion 9 administrative login bypass CVE-2013-0625 CVE-2013-0629CVE-2013-0631 CVE-2013-0 CWE-287 High 632 Adobe ColdFusion directory traversal CVE-2013-3336 CWE-22 High Adobe Coldfusion 8 multiple linked XSS CVE-2009-1872 CWE-79 High vulnerabilies Adobe Flex 3 DOM-based XSS vulnerability CVE-2008-2640 CWE-79 High AjaxControlToolkit directory traversal CVE-2015-4670 CWE-434 High Akeeba backup access control bypass CWE-287 High AmCharts SWF XSS vulnerability CVE-2012-1303 CWE-79 High Amazon S3 public bucket CWE-264 Medium AngularJS client-side template injection CWE-79 High Apache 2.0.39 Win32 directory traversal CVE-2002-0661 CWE-22 High Apache 2.0.43 Win32 file reading vulnerability CVE-2003-0017 CWE-20 High Apache 2.2.14 mod_isapi Dangling Pointer CVE-2010-0425 CWE-20 High Apache 2.x version equal to 2.0.51 CVE-2004-0811 CWE-264 Medium Apache 2.x version older than 2.0.43 CVE-2002-0840 CVE-2002-1156 CWE-538 Medium Apache 2.x version older than 2.0.45 CVE-2003-0132 CWE-400 Medium Apache 2.x version -

Transition Analysis of Cyber Attacks Based on Long-Term Observation—
2-3 nicterReport —TransitionAnalysisofCyberAttacksBasedon Long-termObservation— NAKAZATO Junji and OHTAKA Kazuhiro In this report, we provide a statistical data concerning cyber attacks and malwares based on a long-term network monitoring on the nicter. Especially, we show a continuous observation report of Conficker, which is a pandemic malware since November 2008. In addition, we report a transition analysis of the scale of botnet activities. Keywords Incident analysis, Darknet, Network monitoring, Malware analysis 1 Introduction leverages the traffic as detected by the four black hole sensors placed on different network We have been monitoring the IP address environments as shown by Fig. 1. space that is reachable and unused on the ● Sensor I : Structure where live nets and Internet (i.e. darknets) on a large-scale to darknets coexist in a class B understand the overall impact inflicted by network infectious activities including malware. This ● Sensor II : Structure where only darknets report analyzes the darknet traffic that has exist in a class B network been monitored and accumulated over six ● Sensor III : Structure where a /24 subnet years by an incident analysis center named in a class B network is a dark- *1 the nicter[1][2] to provide changing trends of net cyber attacks and fluctuation of attacker host ● Sensor IV : Structure where live nets and activities as obtained by long-term monitor- darknets coexist in a class B ing. In particular, we focus on Conficker, a network worm that has triggered large-scale infections The traffic obtained by these four sensors since November 2008, and report its impact on is analyzed by different analysis engines[3][4] the Internet and its current activities. -

Malware Trends
NCCIC National Cybersecurity and Communications Integration Center Malware Trends Industrial Control Systems Emergency Response Team (ICS-CERT) Advanced Analytical Laboratory (AAL) October 2016 This product is provided subject only to the Notification Section as indicated here:http://www.us-cert.gov/privacy/ SUMMARY This white paper will explore the changes in malware throughout the past several years, with a focus on what the security industry is most likely to see today, how asset owners can harden existing networks against these attacks, and the expected direction of developments and targets in the com- ing years. ii CONTENTS SUMMARY .................................................................................................................................................ii ACRONYMS .............................................................................................................................................. iv 1.INTRODUCTION .................................................................................................................................... 1 1.1 State of the Battlefield ..................................................................................................................... 1 2.ATTACKER TACTIC CHANGES ........................................................................................................... 2 2.1 Malware as a Service ...................................................................................................................... 2 2.2 Destructive Malware ...................................................................................................................... -

Symantec Intelligence Report: June 2011
Symantec Intelligence Symantec Intelligence Report: June 2011 Three-quarters of spam send from botnets in June, and three months on, Rustock botnet remains dormant as Cutwail becomes most active; Pharmaceutical spam in decline as new Wiki- pharmacy brand emerges Welcome to the June edition of the Symantec Intelligence report, which for the first time combines the best research and analysis from the Symantec.cloud MessageLabs Intelligence Report and the Symantec State of Spam & Phishing Report. The new integrated report, the Symantec Intelligence Report, provides the latest analysis of cyber security threats, trends and insights from the Symantec Intelligence team concerning malware, spam, and other potentially harmful business risks. The data used to compile the analysis for this combined report includes data from May and June 2011. Report highlights Spam – 72.9% in June (a decrease of 2.9 percentage points since May 2011): page 11 Phishing – One in 330.6 emails identified as phishing (a decrease of 0.05 percentage points since May 2011): page 14 Malware – One in 300.7 emails in June contained malware (a decrease of 0.12 percentage points since May 2011): page 15 Malicious Web sites – 5,415 Web sites blocked per day (an increase of 70.8% since May 2011): page 17 35.1% of all malicious domains blocked were new in June (a decrease of 1.7 percentage points since May 2011): page 17 20.3% of all Web-based malware blocked was new in June (a decrease of 4.3 percentage points since May 2011): page 17 Review of Spam-sending botnets in June 2011: page 3 Clicking to Watch Videos Leads to Pharmacy Spam: page 6 Wiki for Everything, Even for Spam: page 7 Phishers Return for Tax Returns: page 8 Fake Donations Continue to Haunt Japan: page 9 Spam Subject Line Analysis: page 12 Best Practices for Enterprises and Users: page 19 Introduction from the editor Since the shutdown of the Rustock botnet in March1, spam volumes have never quite recovered as the volume of spam in global circulation each day continues to fluctuate, as shown in figure 1, below. -
Mid-Year Report Cyber Attack Trends 2017
MID-YEAR REPORT CYBER ATTACK TRENDS 2017 TABLE OF CONTENTS | 2 TABLE OF CONTENTS Introduction ................................................................................................. 3 Global Trends .............................................................................................. 4 Major Cyber Breaches ................................................................................ 5 Americas ................................................................................................. 5 Europe, the Middle East and Africa (EMEA)............................................ 6 Asia-Pacific (APAC) ................................................................................. 6 Global Malware Statistics ........................................................................... 7 Top Malware Families ............................................................................. 7 Top Ransomware ..................................................................................... 9 Top Banking Malware .............................................................................. 10 Top Mobile Malware ................................................................................ 11 Cyber Attack Categories by Region ............................................................ 12 Global Threat Index Map ............................................................................. 13 Additional Observations .............................................................................. 14 Recommendations .....................................................................................