IC Technical Specifications for Construction and Management Of
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

On Morals, Fictions, and Genres
On Morals, Fictions, and Genres by Shen-yi Liao A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy (Philosophy) in The University of Michigan 2011 Doctoral Committee: Professor Kendall L. Walton, Chair Professor Daniel Jacobson Associate Professor Sarah Buss Assistant Professor Sekhar Chandra Sripada c Shen-yi Liao 2011 All Rights Reserved ACKNOWLEDGEMENTS To start, I would like to thank the members of my committee, whose incisive feedback and patient guidance made this dissertation possible. Ken Walton sparked my interest in aesthetics and guided this project from the very beginning. The influence of his thoughtful criticisms can be seen on nearly every page. Sarah Buss has been a source of constant encouragement and her attention to detail greatly improved this work. Dan Jacobson consistently provided invaluable comments on this work and equally invaluable advice on navigating academia. Chandra Sripada served as an exemplary model for integrating empirical methods into philosophical inquiry. I also owe much gratitude to all others who have contributed to the finished dissertation and my growth as a philosopher. In particular, although their names do not appear on the cover page, Tamar Gendler, Shaun Nichols, and Andy Egan more than deserve the title of unofficial committee members. Each of them had a tremendous impact on the way I think about the topics covered in this dissertation, and more importantly, the way I think as a philosopher. In addition, Lina Jansson taught me much about scientific explanation and Nina Strohminger taught me much about experimental design and statistical analysis. Other members of the Michigan philosophical community deserve thanks. -

The Low-Status Character in Shakespeare's Comedies Linda St
Western Kentucky University TopSCHOLAR® Masters Theses & Specialist Projects Graduate School 5-1-1973 The Low-Status Character in Shakespeare's Comedies Linda St. Clair Western Kentucky University Follow this and additional works at: http://digitalcommons.wku.edu/theses Part of the English Language and Literature Commons Recommended Citation St. Clair, Linda, "The Low-Status Character in Shakespeare's Comedies" (1973). Masters Theses & Specialist Projects. Paper 1028. http://digitalcommons.wku.edu/theses/1028 This Thesis is brought to you for free and open access by TopSCHOLAR®. It has been accepted for inclusion in Masters Theses & Specialist Projects by an authorized administrator of TopSCHOLAR®. For more information, please contact [email protected]. ARCHIVES THE LOW-STATUS CHARACTER IN SHAKESPEAREf S CCiiEDIES A Thesis Presented to the Faculty of the Department of English Western Kentucky University Bov/ling Green, Kentucky In Partial Fulfillment of the Requirements for the Degree Master of Arts Linda Abbott St. Clair May, 1973 THE LOW-STATUS CHARACTER IN SHAKESPEARE'S COMEDIES APPROVED >///!}<•/ -J?/ /f?3\ (Date) a D TfV OfThesis / A, ^ of the Grafduate School ACKNOWLEDGEMENTS With gratitude I express my appreciation to Dr. Addie Milliard who gave so generously of her time and knowledge to aid me in this study. My thanks also go to Dr. Nancy Davis and Dr. v.'ill Fridy, both of whom painstakingly read my first draft, offering invaluable suggestions for improvement. iii TABLE OF CONTENTS ACKNOWLEDGEMENTS iii INTRODUCTION 1 THE EARLY COMEDIES 8 THE MIDDLE COMEDIES 35 THE LATER COMEDIES 8? CONCLUSION 106 BIBLIOGRAPHY Ill iv INTRODUCTION Just as the audience which viewed Shakespeare's plays was a diverse group made of all social classes, so are the characters which Shakespeare created. -

Users' Guide for Hand-Held and Walk-Through Metal Detectors
U.S. Department of Justice Office of Justice Programs National Institute of Justice National Institute of Justice Users’ Guide for Hand-Held and Walk-Through Metal Detectors NIJ Guide 600–00 ABOUT THE LAW ENFORCEMENT AND CORRECTIONS STANDARDS AND TESTING PROGRAM The Law Enforcement and Corrections Standards and Testing Program is sponsored by the Office of Science and Technology of the National Institute of Justice (NIJ), U.S. Department of Justice. The program responds to the mandate of the Justice System Improvement Act of 1979, which directed NIJ to encourage research and development to improve the criminal justice system and to disseminate the results to Federal, State, and local agencies. The Law Enforcement and Corrections Standards and Testing Program is an applied research effort that determines the technological needs of justice system agencies, sets minimum performance standards for specific devices, tests commercially available equipment against those standards, and disseminates the standards and the test results to criminal justice agencies nationally and internationally. The program operates through: The Law Enforcement and Corrections Technology Advisory Council (LECTAC), consisting of nationally recognized criminal justice practitioners from Federal, State, and local agencies, which assesses technological needs and sets priorities for research programs and items to be evaluated and tested. The Office of Law Enforcement Standards (OLES) at the National Institute of Standards and Technology, which develops voluntary national performance standards for compliance testing to ensure that individual items of equipment are suitable for use by criminal justice agencies. The standards are based upon laboratory testing and evaluation of representative samples of each item of equipment to determine the key attributes, develop test methods, and establish minimum performance requirements for each essential attribute. -
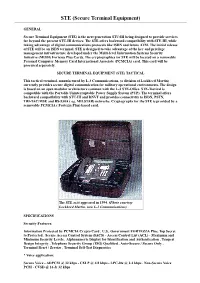
Secure Terminal Equipment)
STE (Secure Terminal Equipment) GENERAL Secure Terminal Equipment (STE) is the next generation STU-III being designed to provide services far beyond the present STU-III devices. The STE offers backward compatibility with STU-III, while taking advantage of digital communications protocols like ISDN and future ATM. The initial release of STE will be an ISDN terminal. STE is designed to take advantage of the key and privilege management infrastructure developed under the Multi-level Information Systems Security Initiative (MISSI) Fortezza Plus Cards. The cryptographics for STE will be located on a removable Personal Computer Memory Card International Associate (PCMCIA) card. This card will be procured separately. SECURE TERMINAL EQUIPMENT (STE) TACTICAL This tactical terminal, manufactured by L-3 Communications, (a division of Lockheed Martin) currently provides secure digital communication for military operational environments. The design is based on an open modular architecture common with the L-3 STE-Office. STE-Tactical is compatible with the Portable Uninterruptable Power Supply System (PUP). The terminal offers backward compatibility with STU-III and DNVT and provides connectivity to ISDN, PSTN, TRI-TAC/MSE and RS-530A ( eg. MILSTAR) networks. Cryptography for the STE is provided by a removable PCMCIA ( Fortezza Plus) based card. The STE as it appeared in 1994. (Photo courtesy Lockheed Martin, now L-3 Communications) SPECIFICATIONS Security Features: Information Protected by PCMCIA Crypto Card . U.S.. Government FORTEZZA Plus, Top Secret to Protected . Secure Access Control System (SACS) - Access Control List (ACL) - Maximum and Minimum Security Levels . Alphanumeric Display for Identification and Authentication . Tempest Design Integrity . Telephone Security Group (TSG) Qualified . -

The Importance of Being Earnest Noah | Meliha Grbic’ | Mia Klopfenstein | Geneve Lau the Meeting of Cecily & Gwendolen
The Importance of Being Earnest Noah | Meliha Grbic’ | Mia Klopfenstein | Geneve Lau The Meeting of Cecily & Gwendolen Click ↯ https://www.youtube.com/wat ch?v=1Yvb25Ypvhw&t=137s Let’s Talk! stock conflict? satire? characters? dramatic irony? foreshadowing? Convention 1 : Foil Algernon and Jack ★ Older/younger sibling ★ Jack: more responsible, compassionate ○ “For Heaven’s sake, don’t try to be cynical. It’s perfectly easy to be cynical.” ○ “My dear Algy, I don’t know whether you will be able to understand my real motives. You are hardly serious enough.” ★ Algernon: frivolous, less responsible, aesthetically concerned ○ “If I am occasionally over-dressed, I make up for it by being immensely over-educated” (1292-1293) ○ Cucumber sandwich situation Convention 1 : Foil Gwendolen and Cecily ★ Urban/Country life ★ Similarities: both love Ernest, diary, ★ Gwendolen: sophisticated, polished ○ “Gwendolen: [Satirically.] I am glad to say that I have never seen a spade. It is obvious that our social spheres have been widely different.” (II. 297-229) ★ Cecily: simple, witty and charming ○ “Gwendolen: Five counties! I don’t think I should like that; I hate crowds. ○ Cecily: [Sweetly] I suppose that is why you live in town? [Gwendolen bites her lip, and beats her foot nervously with her parasol.] Convention 2 : Denouement ★ Bunburying conflict climaxes in the garden, Resolution occurs in the house ★ Cecily and Gwendolen swear to remain distant to Jack and Algernon ○ However, Gwendolen makes the first move: “Mr. Worthing, I have something very particular to ask you” (1891-1892). ○ Characterization of Gwendolen and Cecily lends itself to a fast resolution ★ Gwendolen and Cecily are immediately content with the bunburying explanations ○ “Gwendolen: ...Their explanations appear to be quite satisfactory.../ Cecily: I am more than content…” (1913-1915) ★ Jack reveals Algernon’s deception to Lady Bracknell → She doesn’t care ○ Condones the marriage of Algernon and Cecily. -
Non-Proprietary FIPS 140-2 Security Policy: KMF/Wave/Traffic Cryptr
Non-Proprietary FIPS 140-2 Security Policy: KMF/Wave/Traffic CryptR Document Version: 1.5 Date: January 9, 2020 Copyright Motorola Solutions, Inc. 2020 Version 1.5 Page 1 of 30 Motorola Solutions Public Material – May be reproduced only in its original entirety (without revision). Table of Contents KMF/Wave/Traffic CryptR ...................................................................................................... 1 1 Introduction .................................................................................................................... 4 1.1 Module Description and Cryptographic Boundary ......................................................................6 2 Modes of Operation ........................................................................................................ 8 2.1 Approved Mode Configuration ....................................................................................................8 3 Cryptographic Functionality ............................................................................................. 9 3.1 Critical Security Parameters ...................................................................................................... 11 3.2 Public Keys ................................................................................................................................. 15 4 Roles, Authentication and Services ................................................................................ 16 4.1 Assumption of Roles ................................................................................................................. -

Green Acres School Reading Suggestions for 5Th Or 6Th Graders Updated June 2019
Green Acres School Reading Suggestions for 5th or 6th Graders Updated June 2019 (The books recommended below are part of the Green Acres Library collection. Reading levels and interests vary greatly, so you may want to look also at Reading Suggestions for 4th Graders and Reading Suggestions for 7th/8th Graders.) This list includes: • Fiction • Poetry and Short Stories • Biography and Memoir • Other Nonfiction Graphic books are denoted with the symbol. Fiction Alice, Alex; transl. by Castle In the Stars: The Space Race of 1869 Anne Smith and Owen Smith. "In … this lavishly illustrated graphic novel, Alex Alice delivers a historical fantasy adventure set in a world where man journeyed into space in 1869, not 1969.” Graphic steampunk/Historical fantasy. (Publisher) Appelt, Kathi and Alison McGhee. Maybe a Fox “A fox kit born with a deep spiritual connection to a rural Vermont legend has a special bond with 11-year-old Jules.” Fantasy. (Kirkus Reviews) Avi. The Unexpected Life of Oliver Cromwell Pitts “A 12-year-old boy is left to fend for himself in 18th-century England following a terrible storm and the disappearance of his father… Impossible to put down.” Historical fiction. (Kirkus Reviews) Bauer, Joan. Soar "Sports, friendship, tragedy, and a love connection are all wrapped up in one heartwarming, page-turning story. …This coming-of-age tale features a boy who is courageous and witty; readers—baseball fans or otherwise—will cheer on Jeremiah and this team. The latest middle grade novel from this award-winning author is triumphant and moving." Fiction. (School Library Journal) Beckhorn, Susan. -

Secure Communications Interoperability Protocols (SCIP)
UNCLASSIFIED/UNLIMITED Secure Communications Interoperability Protocols (SCIP) John S. Collura NATO C3 Agency P.O. Box 174 2501 CD The Hague THE NETHERLANDS [email protected] ABSTRACT The concept of NATO Network Enabled Capabilities, (NNEC) including network-ready communications systems requires a fundamental shift in the paradigms and policies used by NATO and the NATO nations. Enabling these concepts down to the tactical mobile user community will be a challenge. Gone are the days where a single nation brings a combat-ready brigade to a NATO sponsored engagement. Modern brigade-level NATO deployed forces may consist of contributions from many nations. This can be highlighted by the fact that one nation might provide command and control capabilities, another logistics, a third special operations, etc. If communications equipments are purchased from multiple sources in multiple nations, and used in-theatre by the nations contributing to a multinational NATO Response Force formation, (brigade, battalion or corps) there are some inherent issues that require resolution to enable efficient network-ready interoperable communications systems. Adding to these issues are the requirements for secure communications and key management. Which nation or entity will provide the security authority in the deployed segment? Will it be the nation supplying command and control, security, logistics, or some other? Or will it be a NATO entity such as NATO HQ, JFHQ Lisbon, JFC Naples, JFC Brunsum, SHAPE, NAMSA, etc.? Who will be responsible for the in-theatre distribution of cryptographic keying material for the operation? When working with coalitions, how does one define communities of interest such that there is appropriate isolation of operations between different coalitions? Can capabilities be eliminated when a coalition member ceases to be friendly? Efficient net-ready interoperable communications systems are one of the core enabling capabilities for future effective NATO engagements. -

Glossary of Literary Terms
Glossary of Critical Terms for Prose Adapted from “LitWeb,” The Norton Introduction to Literature Study Space http://www.wwnorton.com/college/english/litweb10/glossary/C.aspx Action Any event or series of events depicted in a literary work; an event may be verbal as well as physical, so that speaking or telling a story within the story may be an event. Allusion A brief, often implicit and indirect reference within a literary text to something outside the text, whether another text (e.g. the Bible, a myth, another literary work, a painting, or a piece of music) or any imaginary or historical person, place, or thing. Ambiguity When we are involved in interpretation—figuring out what different elements in a story “mean”—we are responding to a work’s ambiguity. This means that the work is open to several simultaneous interpretations. Language, especially when manipulated artistically, can communicate more than one meaning, encouraging our interpretations. Antagonist A character or a nonhuman force that opposes, or is in conflict with, the protagonist. Anticlimax An event or series of events usually at the end of a narrative that contrast with the tension building up before. Antihero A protagonist who is in one way or another the very opposite of a traditional hero. Instead of being courageous and determined, for instance, an antihero might be timid, hypersensitive, and indecisive to the point of paralysis. Antiheroes are especially common in modern literary works. Archetype A character, ritual, symbol, or plot pattern that recurs in the myth and literature of many cultures; examples include the scapegoat or trickster (character type), the rite of passage (ritual), and the quest or descent into the underworld (plot pattern). -

Use of Metal Detectors Tahoe National Forest
Use of Metal Detectors Tahoe National Forest Metal Detector Use Definitions Metal detectors are used by both hobbyists and professionals to look for hidden coins, pipes, and other metallic objects. Due to the need to protect Treasure Trove archaeological sites, we’ve prepared this guide for the Treasure trove includes money, gems, precious metal use of metal detectors on Tahoe National Forest lands. coins, plate, or bullion that has been deliberately hidden If you have questions, contact information is listed on the with the intention of recovering it later. The search for back of this document. buried treasure can involve methods that are damaging to natural and cultural resources, thus a special-use permit from the Forest Service is required. Each permit Help Protect History request is evaluated before such permits are granted. Archaeological sites throughout California provide important insights and knowledge about the past that Archaeological Sites can be gained nowhere else. They are the repositories The use of metal detectors to locate objects of historical for people and cultures not represented in history books. or archaeological value is permitted subject to the Removing artifacts from sites destroys the context of the provisions of the Archaeological Resource Protection Act site, much like tearing pages from a book. Professional of 1979 and the Secretary of Agriculture’s Regulations. archaeologists depend on finding artifacts in their This activity requires a special-use permit. Permits are original location and association to other objects, so they only issued for legitimate research conducted by can accurately understand and interpret the story of that qualified professional archaeologists. -
How to Find GOLD
FIND GOLD TO HOW “Whether you hunt for gold How to Find in the field and stream or in old mines, mine dumps or dredge piles, this book will guide you on your quest to GOLD recover more gold.” Metal Detecting and Panning GARRETT/L Learn effective use of a metal detector and gold pan for: AGAL • Dry panning • Wet panning • Nugget hunting • Field searching Ram Publishing Company A subsidiary of Garrett Metal Detectors ISBN-13: 978-0-915920-98-3 ISBN-10: 0-915920-98-0 $3.95 R 1881 West State Street 50395 Garland, TX 75042 AM PN 1509400 ISBN 0-915920-98-0 9 780915 920983 Charles Garrett / Roy Lagal How to Find GOLD Metal Detecting and Panning Charles Garrett/Roy Lagal HOW TO FIND GOLD © Charles L. Garrett/Roy Lagal 2007 Manufactured in the United States of America. All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording or by any information storage or retrieval system, except in the case of brief quotations embodied in critical articles and reviews. For information, address all inquiries to Editor, Ram Publishing Company. First printing: July 2007 2 www.garrett.com CONTENTS About the Author ...................................................5 Introduction ............................................................9 Basic Tools.............................................................11 Additional Tools ...............................................12 Using a Pan to Find Gold ....................................13 Wet Panning .....................................................14 -

Volume 1 – FOC 2018
1 2 Table of Contents Surveying the Field II The Materiality of Roman Battle: Applying Conflict Archaeology Methods to the Roman World Joanne E. Ball…………………………………………………………………4 Methods in Conflict Archaeology: The Netherlands During the Napoleonic Era (1794-1815). Using Detector Finds to Shed Light on An Under-researched Period. Vincent van der Veen………………………………………………………..19 Musket Balls from the Boston Massacre: Are they Authentic? Dan Sivilich and Joel Bohy………………………………………………….31 Revisiting the US military ‘Levels of War’ Model as a Conceptual Tool in Conflict Archaeology: A Case Study of WW2 Landscapes in Normandy, France. David G Passmore, David Capps-Tunwell, Stephan Harrison………………44 A Decade of Community-Based Projects in the Pacific on WWII Conflict Sites Jennifer F. McKinnon and Toni L. Carrell…………………………………..61 Avocational Detectorists and Battlefield Research: Potential Data Biases Christopher T. Espenshade…………………………………………………..68 Maritime Conflict Archaeology: Battle of the Java Sea: Past and Present Conflicts Robert de Hoop and Martijn Manders……………………………………….75 A Battleship in the Wilderness: The Story of the Chippewa and Lake Ontario’s Forgotten War of 1812 Naval Shipyard* Timothy J. Abel……………………………………………………………...88 3 Surveying the Field II The Materiality of Roman Battle: Applying Conflict Archaeology Methodology to the Roman World. Joanne E. Ball Archaeology, Classics & Egyptology, University of Liverpool, Liverpool L69 7WZ [email protected] ABSTRACT Over the last three decades a growing number of Roman battle sites have been identified across western Europe. Archaeological study of these sites has adapted methodologies developed from the Little Bighorn project onward to the material characteristics of Roman battle, and continue to be refined. Difficulties have been encountered in locating sites within a landscape, due to inadequacies in the historical record.