Appendix A: ASCII Character Codes
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Keyboard Shortcuts for Windows Computers
AbilityNet Factsheet – May 2019 Keyboard Shortcuts for Windows computers This factsheet highlights some of the actions you can carry out quickly on your computer by using key combinations rather than using the mouse to navigate menus and options. These key combinations are referred to as shortcuts as they are often a much quicker way of carrying out tasks. They can also be particularly useful for repetitive actions. AbilityNet Factsheet: Keyboard Shortcuts Page 1 of 12 www.abilitynet.org.uk/factsheets May 2019 Contents 1. What are shortcuts ............................................................................................. 3 A note on Apple (Mac) computers ........................................................................... 3 Conventions ............................................................................................................. 3 Navigating Within Windows Using the Keyboard ..................................................... 4 Reference Chart ...................................................................................................... 7 Autocorrect as a shortcut ......................................................................................... 9 2. How can AbilityNet help? ................................................................................. 10 Free advice and home visits .................................................................................. 10 My Computer My Way ........................................................................................... 10 Workplace -
DEC Text Processing Utility Reference Manual
DEC Text Processing Utility Reference Manual Order Number: AA–PWCCD–TE April 2001 This manual describes the elements of the DEC Text Processing Utility (DECTPU). It is intended as a reference manual for experienced programmers. Revision/Update Information: This manual supersedes the DEC Text Processing Utility Reference Manual, Version 3.1 for OpenVMS Version 7.2. Software Version: DEC Text Processing Utility Version 3.1 for OpenVMS Alpha Version 7.3 and OpenVMS VAX Version 7.3 The content of this document has not changed since OpenVMS Version 7.1. Compaq Computer Corporation Houston, Texas © 2001 Compaq Computer Corporation COMPAQ, VAX, VMS, and the Compaq logo Registered in U.S. Patent and Trademark Office. OpenVMS is a trademark of Compaq Information Technologies Group, L.P. Motif is a trademark of The Open Group. PostScript is a registered trademark of Adobe Systems Incorporated. All other product names mentioned herein may be the trademarks or registered trademarks of their respective companies. Confidential computer software. Valid license from Compaq or authorized sublicensor required for possession, use, or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s standard commercial license. Compaq shall not be liable for technical or editorial errors or omissions contained herein. The information in this document is provided "as is" without warranty of any kind and is subject to change without notice. The warranties for Compaq products are set forth in the express limited warranty statements accompanying such products. -

Newline Characters Should Map to a Completely Ignorable Collation Element in the DUCET Marc Lodewijck (Brussels, Belgium) October 28, 2016
Proposal for consideration by UTC Newline characters should map to a completely ignorable collation element in the DUCET Marc Lodewijck (Brussels, Belgium) October 28, 2016 Assume the following records, which compare tertiary-equal: "xy#", "xy", "x#y" With the UCA “Shifted” option for handling variable collation elements, the sorting result is as follows: [3] x#y [1EFF 1F0B | 0020 0020 | 0002 0002 | FFFF 038F FFFF |] [2] xy [1EFF 1F0B | 0020 0020 | 0002 0002 | FFFF FFFF |] [1] xy# [1EFF 1F0B | 0020 0020 | 0002 0002 | FFFF FFFF 038F |] Inserting a variable character makes a string sort before the string without it; and appending a variable character makes a string sort after the string without it. With the “Shift-trimmed” option, this is the outcome: [2] xy [1EFF 1F0B | 0020 0020 | 0002 0002 | |] [3] x#y [1EFF 1F0B | 0020 0020 | 0002 0002 | FFFF 038F |] [1] xy# [1EFF 1F0B | 0020 0020 | 0002 0002 | FFFF FFFF 038F |] Inserting a variable character anywhere makes a string sort after the string without it; and the string having a variable character in the lowest position makes it sort before the other string. The “Shift-trimmed” option is the same as “Shifted”, except that trailing high-quaternary weights (from regular characters) are removed from the sort key. This means that, compared with “Shifted”, the “Shift-trimmed” option sorts strings without variable characters before ones with variable characters added—the string without variable characters has an empty fourth level. Now suppose we wish to sort the following text strings stored in a file: 1/6 It is obvious that we won’t strip off the newline character(s) at the end of each line, before it is processed further. -
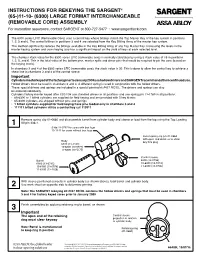
REMOVABLE CORE) ASSEMBLY for Installation Assistance, Contact SARGENT at 800-727-5477 •
INSTRUCTIONS FOR REKEYING THE SARGENT® (65-)11-10- (6300) LARGE FORMAT INTERCHANGEABLE (REMOVABLE CORE) ASSEMBLY For installation assistance, contact SARGENT at 800-727-5477 • www.sargentlock.com The 6300 series LFIC (Removable Core) uses a control key whose bittings match the Top Master Key of the key system in positions 1, 2, 5 and 6. The control bittings in positions 3 and 4 are selected from the Key Bitting Array of the master key system. This method significantly reduces the bittings available in the Key Bitting Array of any Top Master Key. Increasing the levels in the master keying system and cross keying also has a significant impact on the yield of keys at each selected level. The chamber stack value for the 6300 series LFIC (removable core) is normally calculated by using a stack value of 15 in positions 1, 2, 5, and 6. This is the total value of the bottom pins, master splits and driver pins that would be required to pin the core (based on the keying levels). In chambers 3 and 4 of the 6300 series LFIC (removable core), the stack value is 20. This is done to allow the control key to achieve a shear line in chambers 3 and 4 of the control sleeve. Important Cylinders master keyed at the factory prior to January 2009 use hollow drivers and SARGENT recommends their continued use. Hollow drivers must be used in chambers 3 and 4. A different spring is used in conjunction with the hollow drivers. These special drivers and springs are included in a special pinning kit #437 RC/UL. -

Keyboard Shortcuts for Avid Editors
Keyboard Shortcuts for Avid Editors (Media Composer, Newscutter, and Symphony) • Audio • Bin • Capturing • Editing • Effect Mode • Playing & Marking • Timeline • Trim Mode • Tools • Other Note: = Command Key Audio Windows Macintosh Description Alt + click Pan slider Option + click Pan slider Snaps to Mid in Audio Mix tool Snaps to 0 dB in Audio EQ and Audio Alt + click Volume slider Option + click Volume slider tools Alt + click Audio Track Option + click Audio Track Selects track for audio scrub Monitor button Monitor button monitoring Alt + click Track Solo button Option + click Track Solo (Automation Gain tool) button (Automation Gain tool) or or Mutes selected track (1 to 8) Alt + number (1 to 8) at top Option + number (1 to 8) at of keyboard top of keyboard Moves selected audio keyframe Alt + drag keyframe Option + drag keyframe horizontally in Timeline Alt + click digital scrub parameters in Composer Option + click digital scrub monitorOption + click digital parameters in Composer Opens Audio Settings dialog box scrub parameters in monitor Composer monitor Bin Windows Macintosh Description Ctrl + N Creates a new bin + N Selects all items in the active bin or the Project Window, Ctrl + A + A if selected Ctrl + W Closes open windows, bins or dialog boxes + W Prints the selected bin in whatever view you have Ctrl + P + P selected (Text, Frame or Script View) Ctrl + D Duplicates selected clip(s), sequence(s), or title(s) + D Creates a Group Clip from selected Master Clips or Sub Shift + Ctrl + G + Shift + G Clips First, select clips or sequences in the bin, then use this Ctrl + I shortcut to open the Console window, which will display + I useful information Hold down these shortcut keys, then click on the Clip Shift + Ctrl + click Shift + Ctrl + click Menu. -
STAT579: SAS Programming
Note on homework for SAS date formats I'm getting error messages using the format MMDDYY10D. even though this is listed on websites for SAS date formats. Instead, MMDDYY10 and similar (without the D seems to work for both hyphens and slashes. Also note that a date format such as MMDDYYw. means that the w is replaced by a number indicating the width of the string (e.g., 8 or 10). SAS Programming SAS data sets (Chapter 4 of Cody book) SAS creates data sets internally once they are read in from a Data Step. The data sets can be stored in different locations and accessed later on. The default is to store them in WORK, so if you create a data set using data adress; the logfile will say that it created a SAS dataset called WORK.ADDRESS. You can nagivate to the newly created SAS dataset. In SAS Studio, go to the Libraries Tab on the left (Usually appears toward the bottom until you click on it). Then WORK.ADDRESS should appear. SAS Programming SAS data sets SAS Programming SAS data sets SAS Programming Making datasets permanent You can also make SAS datasets permanent. This is done using the libname statement. E.g. SAS Programming Permanent SAS datasets The new dataset should be available to be accessed directly from other SAS programs without reading in original data. This can save a lot of time for large datasets. If the SAS dataset is called mydata, the SAS dataset will be called mydata.sas7bdat, where the 7 refers to the datastructures used in version 7 (and which hasn't changed up to version 9). -

Startup Keyboard Shortcuts Press the Key Or Key Combination Until The
Startup keyboard shortcuts Press the key or key combination until the expected function occurs/appears (for example, hold Option during startup until Startup Manager appears, or Shift until "Safe Boot" appears). Tip: If a startup function doesn't work and you use a third-party keyboard, connect an Apple keyboard and try again. Key or key combination What it does Option Display all bootable volumes (Startup Manager) Shift Perform Safe Boot (start up in Safe Mode) C Start from a bootable disc (DVD, CD) T Start in FireWire target disk mode N Start from NetBoot server X Force Mac OS X startup (if non-Mac OS X startup volumes are present) Command-V Start in Verbose Mode Command-S Start in Single User Mode To use a keyboard shortcut, or key combination, you press a modifier key with a character key. For example, pressing the Command key (the key with a symbol) and the "c" key at the same time copies whatever is currently selected (text, graphics, and so forth) into the Clipboard. This is also known as the Command-C key combination (or keyboard shortcut). A modifier key is a part of many key combinations. A modifier key alters the way other keystrokes or mouse clicks are interpreted by Mac OS X. Modifier keys include: Command, Control, Option, Shift, Caps Lock, and the fn key (if your keyboard has a fn key). Here are the modifier key symbols you can see in Mac OS X menus: (Command key) - On some Apple keyboards, this key also has an Apple logo ( ) (Control key) (Option key) - "Alt" may also appear on this key (Shift key) (Caps Lock) - Toggles Caps Lock on or off fn (Function key) Startup keyboard shortcuts Press the key or key combination until the expected function occurs/appears (for example, hold Option during startup until Startup Manager appears, or Shift until "Safe Boot" appears). -

Key Control Policy
Virginia Polytechnic Institute and State University Access Control: Key Control Policy No. 5620 1.0 Purpose This is a statement of policy regarding access control of buildings and property owned or Policy Effective Date: occupied by Virginia Tech. This policy will serve as the framework by which keys to 6/16/1993 university buildings will be issued, monitored, and maintained. The Key Control Office within the Facilities Department and the Virginia Tech Police Department shall implement Last Revision Date: and oversee the procedures set forth herein. 1/3/2017 The Key Control Office and Virginia Tech Police Department shall work closely with the Policy Owner: campus community to ensure that all university access needs are met. The dual Chris Kiwus responsibility of the two organizations will ensure checks and balances to a critical, high- risk university program. Key issuance and control for Housing and Residence Life is Policy Author: (Contact governed by the Hokie Handbook (www.hokiehandbook.vt.edu). Person) Jon Clark Teglas The issuing of keys, maintenance of physical security devices, and other arrangements concerning security for leased properties other than those at the Virginia Tech Corporate Affected Parties: Research Center are covered by the specific lease agreement for the property in question. Faculty 1.1 Objectives Staff 1. To achieve maximum physical security with minimum logistics. 1.0 Purpose 2. To establish control of the campus keying system including key duplication and 2.0 Policy distribution. 3.0 Procedures 4.0 Definitions 3. To establish a recorded chain of accountability for all keys issued. 5.0 References 4. -

MACBOOK Keyboard Shortcuts
MACBOOK Keyboard Shortcuts Learn about common OS X keyboard shortcuts. A keyboard shortcut is a way to invoke a function in OS X by pressing a combination of keys on your keyboard. To use a keyboard shortcut, or key combination, you press a modifier key with a character key. For example, pressing the Command key (the key that has a symbol) and the "c" key at the same time copies whatever is currently selected (text, graphics, and so forth) into the Clipboard. This is also known as the Command-C key combination (or keyboard shortcut). A modifier key is a part of many key combinations. A modifier key alters the way other keystrokes or mouse/trackpad clicks are interpreted by OS X. Modifier keys include: Command, Shift, Option, Control, Caps Lock, and the Fn key. If your keyboard has an Fn key, you may need to use it in some of the key combinations listed below. For example, if the keyboard shortcut is Control-F2, press Fn-Control-F2. Here are the modifier key symbols you may see in OS X menus: ⌘ Command key ⌃ Control key ⌥ Option key ⇧ Shift Key ⇪ Caps Lock Fn Function Key Startup shortcuts Press the key or key combination until the expected function occurs/appears (for example, hold Option during startup until Startup Manager appears, or Shift until "Safe Boot" appears). Tip: If a startup function doesn't work and you use a third-party keyboard, try again with an Apple keyboard. Key or key combination What it does Display all bootable volumes (Startup Option Manager) Shift Perform a Safe Boot (start up in Safe Mode) Left Shift Prevent -
ZS3608 QUICKSTART Mobile Hand-Held Scanners
ZS3608 SCANNER FEATURES ACCESSORIES www.sick.com/ZS36x8_DPM Distributed by 1 Intellistand 3 2 4 1 Scan Window 2 Scan Trigger Mobile Hand-held Scanners 3 LED 4 Beeper QUICKSTART See Product Reference Guide 8025235/en/2020-01-16 for detailed information CABLE ATTACHMENT SET DEFAULTS / ENTER KEY BAR CODES TAB KEY BAR CODE 1. Insert cable fully so that the connector is flush with the scanner surface. ADD A TAB KEY 2. Loosen metal lock plate screws using a PH1 driver. 3. Slide lock plate to fully locked position. To add a Tab key after scanned data, scan the bar code below. 4. Tighten screw using a PH1 driver (torque: 5 in-lb). RETURN TO FACTORY DEFAULTS 1 2 ADD A TAB KEY ADD AN ENTER KEY (Carriage Return/Line Feed) USB CAPS LOCK OVERRIDE BAR CODE To add an Enter key after scanned data, scan the bar code below. 3 4 USB - OVERRIDE CAPS LOCK KEY (ENABLE) ADD AN ENTER KEY (CARRIAGE RETURN/LINE FEED) *USB - DO NOT OVERRIDE CAPS LOCK KEY (DISABLE) STEP 1 - CONNECT HOST INTERFACE STEP 2 - SET UP INTERFACE (Scan Host Bar Codes) USB USB Scan ONE of the bar codes below NOTE: Cables may vary depending on configuration The interface cable automatically detects the host interface type and uses the default setting. If the default (*) does not meet your requirements, scan another host bar code below. *USB KEYBOARD (HID) USB CDC Host USB OPOS HAND- HELD IBM TABLE TOP USB SIMPLE COM PORT EMULATION SNAPI WITHOUT IMAGING SNAPI WITH IMAGING SSI OVER USB CDC IBM HAND-HELD USB RS-232 RS-232 Scan ONE of the bar codes below The interface cable automatically detects the host interface type and uses the default setting. -
V. Console Typewriter
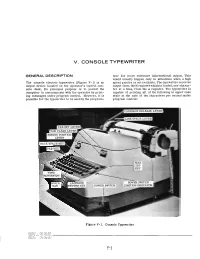
V. CONSOLE TYPEWRITER GENERAL DESCRIPTION mer for more extensive informational output. This would usually happen only in situations when a high The console electric typewriter (Figure V-1) is an speed printer is not available. The typewriter receives output device located on the operator's control con- output from the N register which is loaded, one charac- sole desk. Its principal purpose is to permit the ter at a time, from the A register. The typewriter is computer to communicate with the operator by print- capable of printing all of the following in upper case ing messages under program control. However, it is style at the rate of ten characters per second under possible for the typewriter to beusedby the program- program control: RIAGE ' POW ER SWITC I Figure V-1. Console Typewriter Fled printout SETUP PROCEDURE Black printout Print characters 0-9, A-Z, minus, period, Only two steps in the setup procedure need to be done slash, dollar, and comma regularly at the beginning of each shift. They are: Carriage return Space (by operation of the blank key) 1. Turn typewriter power on by moving the Tabulation power toggle switch to the rear position. The veiwing window above the switch shows Messages are typed out automatically, requiring no white to indicate that power is on. assistance from the operator. However, a typeout should be immediately observed since the message 2. Load paper in the typewriter in the same may c~ntaininstructions requiring a decision and way as in any standardbusiness typewriter. action on the operator's part. All error messages are The paper is continuous strip, so the oper- printed in red. -
Master Key System Design Guide
Master Key System Design Guide Guidance and worksheets for use with ASSA ABLOY Group brands: ADAMS RITE | BARON | CECO | CORBIN RUSSWIN | CURRIES | GRAHAM | HES MARKAR | McKINNEY | NORTON | RIXSON | SARGENT | SECURITRON | YALE Introduction Table of Contents To ensure a facility has the desired level of security, Planning it is necessary to have a properly designed and maintained master key system. ASSA ABLOY Door Convenience vs. Security, Security Solutions offers all of the products and Achieving Proper Balance . 3 services to help you implement a new master key System Structure . 4 system, or expand an existing one. Levels of Keying . 4 2-Level System . 5 Key System Products 3-Level System . 5 Product solutions include: 4-Level System . 5 • Cylinders for various security requirements levels • Cylinders that exceed the stringent standards Key Symbols set forth by industry testing and listing agencies Standard Key Symbols . 6 • Cylinders that work with electrified stand-alone 2-Level System . 6 and networked access control systems 3-Level System . 6 Professional Support Grand Master Pie “A” . 7 4-Level System . 8 Our team of trained and certified Key System Special Keying Requirements, Larger Systems . 8 Specialists will help you design a secure master key system, develop and implement key control policies, select the right cylinder for each doorway, and understand the latest trends in System Expansion physical security. As the leader in security and Define Expansion Parameters. 9 life-safety solutions, ASSA ABLOY has developed Sample Expansion Specification. 9 and implemented the industry’s only Key System Specialist Certification Program. What You Must Know. 9 Theoretical Numbers Reduced .