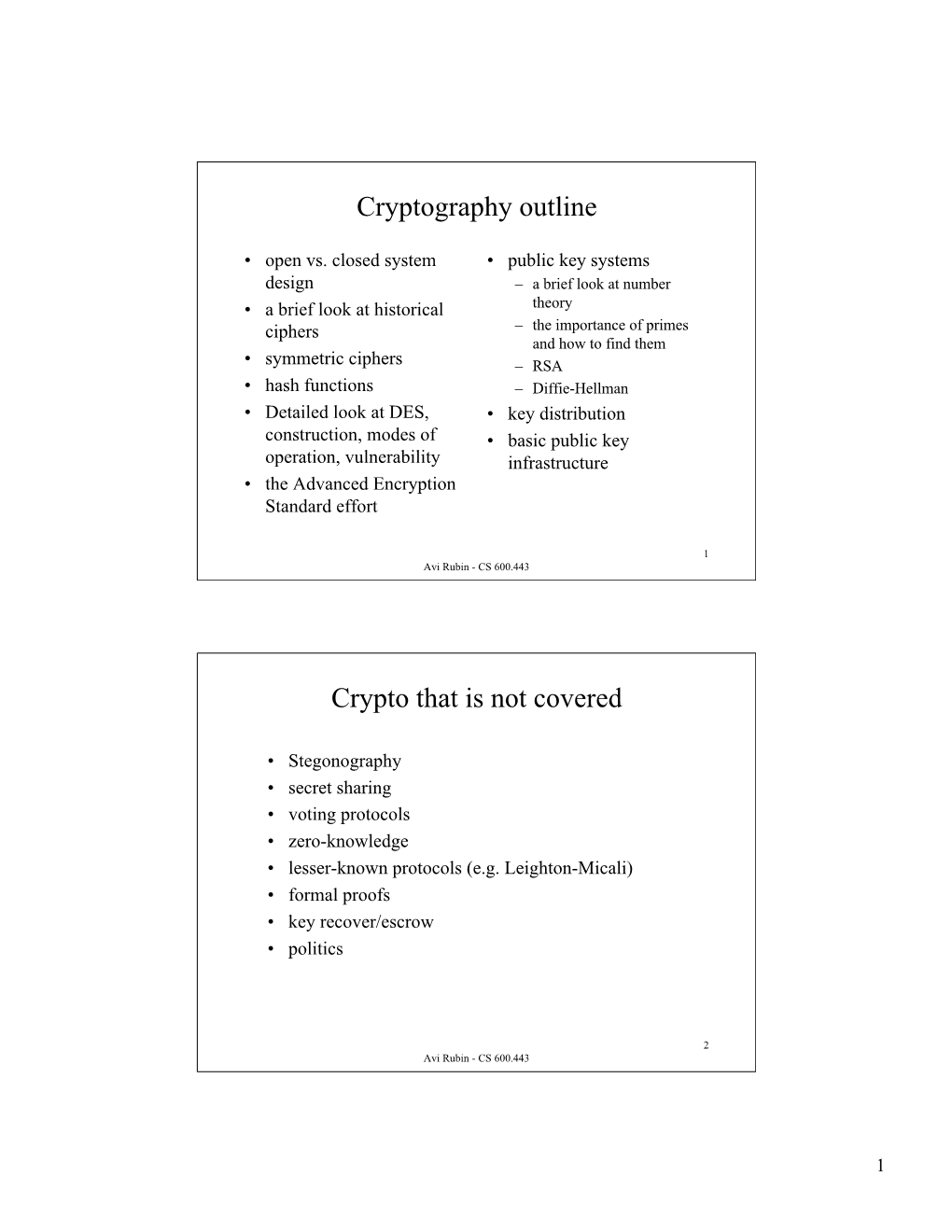
Cryptography Outline Crypto That Is Not Covered
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Design of Rijndael: AES - the Advanced Encryption Standard/Joan Daemen, Vincent Rijmen
Joan Daernen · Vincent Rijrnen Theof Design Rijndael AES - The Advanced Encryption Standard With 48 Figures and 17 Tables Springer Berlin Heidelberg New York Barcelona Hong Kong London Milan Paris Springer TnL-1Jn Joan Daemen Foreword Proton World International (PWI) Zweefvliegtuigstraat 10 1130 Brussels, Belgium Vincent Rijmen Cryptomathic NV Lei Sa 3000 Leuven, Belgium Rijndael was the surprise winner of the contest for the new Advanced En cryption Standard (AES) for the United States. This contest was organized and run by the National Institute for Standards and Technology (NIST) be ginning in January 1997; Rij ndael was announced as the winner in October 2000. It was the "surprise winner" because many observers (and even some participants) expressed scepticism that the U.S. government would adopt as Library of Congress Cataloging-in-Publication Data an encryption standard any algorithm that was not designed by U.S. citizens. Daemen, Joan, 1965- Yet NIST ran an open, international, selection process that should serve The design of Rijndael: AES - The Advanced Encryption Standard/Joan Daemen, Vincent Rijmen. as model for other standards organizations. For example, NIST held their p.cm. Includes bibliographical references and index. 1999 AES meeting in Rome, Italy. The five finalist algorithms were designed ISBN 3540425802 (alk. paper) . .. by teams from all over the world. 1. Computer security - Passwords. 2. Data encryption (Computer sCIence) I. RIJmen, In the end, the elegance, efficiency, security, and principled design of Vincent, 1970- II. Title Rijndael won the day for its two Belgian designers, Joan Daemen and Vincent QA76.9.A25 D32 2001 Rijmen, over the competing finalist designs from RSA, IBl\!I, Counterpane 2001049851 005.8-dc21 Systems, and an English/Israeli/Danish team. -

A Quantitative Study of Advanced Encryption Standard Performance
United States Military Academy USMA Digital Commons West Point ETD 12-2018 A Quantitative Study of Advanced Encryption Standard Performance as it Relates to Cryptographic Attack Feasibility Daniel Hawthorne United States Military Academy, [email protected] Follow this and additional works at: https://digitalcommons.usmalibrary.org/faculty_etd Part of the Information Security Commons Recommended Citation Hawthorne, Daniel, "A Quantitative Study of Advanced Encryption Standard Performance as it Relates to Cryptographic Attack Feasibility" (2018). West Point ETD. 9. https://digitalcommons.usmalibrary.org/faculty_etd/9 This Doctoral Dissertation is brought to you for free and open access by USMA Digital Commons. It has been accepted for inclusion in West Point ETD by an authorized administrator of USMA Digital Commons. For more information, please contact [email protected]. A QUANTITATIVE STUDY OF ADVANCED ENCRYPTION STANDARD PERFORMANCE AS IT RELATES TO CRYPTOGRAPHIC ATTACK FEASIBILITY A Dissertation Presented in Partial Fulfillment of the Requirements for the Degree of Doctor of Computer Science By Daniel Stephen Hawthorne Colorado Technical University December, 2018 Committee Dr. Richard Livingood, Ph.D., Chair Dr. Kelly Hughes, DCS, Committee Member Dr. James O. Webb, Ph.D., Committee Member December 17, 2018 © Daniel Stephen Hawthorne, 2018 1 Abstract The advanced encryption standard (AES) is the premier symmetric key cryptosystem in use today. Given its prevalence, the security provided by AES is of utmost importance. Technology is advancing at an incredible rate, in both capability and popularity, much faster than its rate of advancement in the late 1990s when AES was selected as the replacement standard for DES. Although the literature surrounding AES is robust, most studies fall into either theoretical or practical yet infeasible. -

Investigating Profiled Side-Channel Attacks Against the DES Key
IACR Transactions on Cryptographic Hardware and Embedded Systems ISSN 2569-2925, Vol. 2020, No. 3, pp. 22–72. DOI:10.13154/tches.v2020.i3.22-72 Investigating Profiled Side-Channel Attacks Against the DES Key Schedule Johann Heyszl1[0000−0002−8425−3114], Katja Miller1, Florian Unterstein1[0000−0002−8384−2021], Marc Schink1, Alexander Wagner1, Horst Gieser2, Sven Freud3, Tobias Damm3[0000−0003−3221−7207], Dominik Klein3[0000−0001−8174−7445] and Dennis Kügler3 1 Fraunhofer Institute for Applied and Integrated Security (AISEC), Germany, [email protected] 2 Fraunhofer Research Institution for Microsystems and Solid State Technologies (EMFT), Germany, [email protected] 3 Bundesamt für Sicherheit in der Informationstechnik (BSI), Germany, [email protected] Abstract. Recent publications describe profiled single trace side-channel attacks (SCAs) against the DES key-schedule of a “commercially available security controller”. They report a significant reduction of the average remaining entropy of cryptographic keys after the attack, with surprisingly large, key-dependent variations of attack results, and individual cases with remaining key entropies as low as a few bits. Unfortunately, they leave important questions unanswered: Are the reported wide distributions of results plausible - can this be explained? Are the results device- specific or more generally applicable to other devices? What is the actual impact on the security of 3-key triple DES? We systematically answer those and several other questions by analyzing two commercial security controllers and a general purpose microcontroller. We observe a significant overall reduction and, importantly, also observe a large key-dependent variation in single DES key security levels, i.e. -

Known and Chosen Key Differential Distinguishers for Block Ciphers
Known and Chosen Key Differential Distinguishers for Block Ciphers Ivica Nikoli´c1?, Josef Pieprzyk2, Przemys law Soko lowski2;3, Ron Steinfeld2 1 University of Luxembourg, Luxembourg 2 Macquarie University, Australia 3 Adam Mickiewicz University, Poland [email protected], [email protected], [email protected], [email protected] Abstract. In this paper we investigate the differential properties of block ciphers in hash function modes of operation. First we show the impact of differential trails for block ciphers on collision attacks for various hash function constructions based on block ciphers. Further, we prove the lower bound for finding a pair that follows some truncated differential in case of a random permutation. Then we present open-key differential distinguishers for some well known round-reduced block ciphers. Keywords: Block cipher, differential attack, open-key distinguisher, Crypton, Hierocrypt, SAFER++, Square. 1 Introduction Block ciphers play an important role in symmetric cryptography providing the basic tool for encryp- tion. They are the oldest and most scrutinized cryptographic tool. Consequently, they are the most trusted cryptographic algorithms that are often used as the underlying tool to construct other cryp- tographic algorithms. One such application of block ciphers is for building compression functions for the hash functions. There are many constructions (also called hash function modes) for turning a block cipher into a compression function. Probably the most popular is the well-known Davies-Meyer mode. Preneel et al. in [27] have considered all possible modes that can be defined for a single application of n-bit block cipher in order to produce an n-bit compression function. -

Security + Encryption Standards
Security + Encryption Standards Author: Joseph Lee Email: joseph@ ripplesoftware.ca Mobile: 778-725-3206 General Concepts Forward secrecy / perfect forward secrecy • Using a key exchange to provide a new key for each session provides improved forward secrecy because if keys are found out by an attacker, past data cannot be compromised with the keys Confusion • Cipher-text is significantly different than the original plaintext data • The property of confusion hides the relationship between the cipher-text and the key Diffusion • Is the principle that small changes in message plaintext results in large changes in the cipher-text • The idea of diffusion is to hide the relationship between the cipher-text and the plaintext Secret-algorithm • A proprietary algorithm that is not publicly disclosed • This is discouraged because it cannot be reviewed Weak / depreciated algorithms • An algorithm that can be easily "cracked" or defeated by an attacker High-resiliency • Refers to the strength of the encryption key if an attacker discovers part of the key Data-in-transit • Data sent over a network Data-at-rest • Data stored on a medium Data-in-use • Data being used by an application / computer system Out-of-band KEX • Using a medium / channel for key-exchange other than the medium the data transfer is taking place (phone, email, snail mail) In-band KEX • Using the same medium / channel for key-exchange that the data transfer is taking place Integrity • Ability to determine the message has not been altered • Hashing algorithms manage Authenticity -
Miss in the Middle
Miss in the middle By: Gal Leonard Keret Miss in the Middle Attacks on IDEA, Khufu and Khafre • Written by: – Prof. Eli Biham. – Prof. Alex Biryukov. – Prof. Adi Shamir. Introduction • So far we used traditional differential which predict and detect statistical events of highest possible probability. Introduction • A new approach is to search for events with probability one, whose condition cannot be met together (events that never happen). Impossible Differential • Random permutation: 휎 푀0 = 푎푛푦 퐶 표푓 푠푖푧푒 푀0. • Cipher (not perfect): 퐸 푀0 = 푠표푚푒 퐶 표푓 푠푖푧푒 푀0. • Events (푚 ↛ 푐) that never happen distinguish a cipher from a random permutation. Impossible Differential • Impossible events (푚 ↛ 푐) can help performing key elimination. • All the keys that lead to impossibility are obviously wrong. • This way we can filter wrong key guesses and leaving the correct key. Enigma – for example • Some of the attacks on Enigma were based on the observation that letters can not be encrypted to themselves. 퐸푛푖푔푚푎(푀0) ≠ 푀0 In General • (푀0, 퐶1) is a pair. If 푀0 푀0 → 퐶1. • 푀 ↛ 퐶 . 0 0 Some rounds For any key • ∀ 푘푒푦| 퐶1 → 퐶0 ↛ is an impossible key. Cannot lead to 퐶0. Some rounds Find each keys Decrypt 퐶1back to 퐶0. IDEA • International Data Encryption Algorithm. • First described in 1991. • Block cipher. • Symmetric. • Key sizes: 128 bits. • Block sizes: 64 bits. ⊕ - XOR. ⊞ - Addition modulo 216 ⊙ - Multiplication modulo 216+1 Encryption security • Combination of different mathematical groups. • Creation of "incompatibility“: ∗ • 푍216+1 → 푍216 ∗ • 푍216 → 푍216+1 ∗ ∗ Remark: 푍216+1 doesn’t contain 0 like 푍216 , so in 푍216+1 0 will be converted to 216 since 0 ≡ 216(푚표푑 216). -

Report on the AES Candidates
Rep ort on the AES Candidates 1 2 1 3 Olivier Baudron , Henri Gilb ert , Louis Granb oulan , Helena Handschuh , 4 1 5 1 Antoine Joux , Phong Nguyen ,Fabrice Noilhan ,David Pointcheval , 1 1 1 1 Thomas Pornin , Guillaume Poupard , Jacques Stern , and Serge Vaudenay 1 Ecole Normale Sup erieure { CNRS 2 France Telecom 3 Gemplus { ENST 4 SCSSI 5 Universit e d'Orsay { LRI Contact e-mail: [email protected] Abstract This do cument rep orts the activities of the AES working group organized at the Ecole Normale Sup erieure. Several candidates are evaluated. In particular we outline some weaknesses in the designs of some candidates. We mainly discuss selection criteria b etween the can- didates, and make case-by-case comments. We nally recommend the selection of Mars, RC6, Serp ent, ... and DFC. As the rep ort is b eing nalized, we also added some new preliminary cryptanalysis on RC6 and Crypton in the App endix which are not considered in the main b o dy of the rep ort. Designing the encryption standard of the rst twentyyears of the twenty rst century is a challenging task: we need to predict p ossible future technologies, and wehavetotake unknown future attacks in account. Following the AES pro cess initiated by NIST, we organized an op en working group at the Ecole Normale Sup erieure. This group met two hours a week to review the AES candidates. The present do cument rep orts its results. Another task of this group was to up date the DFC candidate submitted by CNRS [16, 17] and to answer questions which had b een omitted in previous 1 rep orts on DFC. -

State of the Art in Lightweight Symmetric Cryptography
State of the Art in Lightweight Symmetric Cryptography Alex Biryukov1 and Léo Perrin2 1 SnT, CSC, University of Luxembourg, [email protected] 2 SnT, University of Luxembourg, [email protected] Abstract. Lightweight cryptography has been one of the “hot topics” in symmetric cryptography in the recent years. A huge number of lightweight algorithms have been published, standardized and/or used in commercial products. In this paper, we discuss the different implementation constraints that a “lightweight” algorithm is usually designed to satisfy. We also present an extensive survey of all lightweight symmetric primitives we are aware of. It covers designs from the academic community, from government agencies and proprietary algorithms which were reverse-engineered or leaked. Relevant national (nist...) and international (iso/iec...) standards are listed. We then discuss some trends we identified in the design of lightweight algorithms, namely the designers’ preference for arx-based and bitsliced-S-Box-based designs and simple key schedules. Finally, we argue that lightweight cryptography is too large a field and that it should be split into two related but distinct areas: ultra-lightweight and IoT cryptography. The former deals only with the smallest of devices for which a lower security level may be justified by the very harsh design constraints. The latter corresponds to low-power embedded processors for which the Aes and modern hash function are costly but which have to provide a high level security due to their greater connectivity. Keywords: Lightweight cryptography · Ultra-Lightweight · IoT · Internet of Things · SoK · Survey · Standards · Industry 1 Introduction The Internet of Things (IoT) is one of the foremost buzzwords in computer science and information technology at the time of writing. -

Key Schedule Algorithm Using 3-Dimensional Hybrid Cubes for Block Cipher
(IJACSA) International Journal of Advanced Computer Science and Applications, Vol. 10, No. 8, 2019 Key Schedule Algorithm using 3-Dimensional Hybrid Cubes for Block Cipher Muhammad Faheem Mushtaq1, Sapiee Jamel2, Siti Radhiah B. Megat3, Urooj Akram4, Mustafa Mat Deris5 Faculty of Computer Science and Information Technology Universiti Tun Hussein Onn Malaysia (UTHM), Parit Raja, 86400 Batu Pahat, Johor, Malaysia1, 2, 3, 5 Faculty of Computer Science and Information Technology Khwaja Fareed University of Engineering and Information Technology, 64200 Rahim Yar Khan, Pakistan1, 4 Abstract—A key scheduling algorithm is the mechanism that difficulty for a cryptanalyst to recover the secret key [8]. All generates and schedules all session-keys for the encryption and cryptographic algorithms are recommended to follow 128, 192 decryption process. The key space of conventional key schedule and 256-bits key lengths proposed by Advanced Encryption algorithm using the 2D hybrid cubes is not enough to resist Standard (AES) [9]. attacks and could easily be exploited. In this regard, this research proposed a new Key Schedule Algorithm based on Permutation plays an important role in the development of coordinate geometry of a Hybrid Cube (KSAHC) using cryptographic algorithms and it contains the finite set of Triangular Coordinate Extraction (TCE) technique and 3- numbers or symbols that are used to mix up a readable message Dimensional (3D) rotation of Hybrid Cube surface (HCs) for the into ciphertext as shown in transposition cipher [10]. The logic block cipher to achieve large key space that are more applicable behind any cryptographic algorithm is the number of possible to resist any attack on the secret key. -

ASIC Design of High Speed Kasumi Block Cipher
International Journal of Engineering Research & Technology (IJERT) ISSN: 2278-0181 Vol. 3 Issue 2, February - 2014 ASIC design of High Speed Kasumi Block Cipher Dilip kumar1 Sunil shah2 1M. Tech scholar, Asst. Prof. Gyan ganga institute of technology and science Jabalpur Gyan ganga institute of technology and science Jabalpur M.P. M.P. Abstract - The nature of the information that flows throughout modern cellular communications networks has evolved noticeably since the early years of the first generation systems, when only voice sessions were possible. With today’s networks it is possible to transmit both voice and data, including e-mail, pictures and video. The importance of the security issues is higher in current cellular networks than in previous systems because users are provided with the mechanisms to accomplish very crucial operations like banking transactions and sharing of confidential business information, which require high levels of protection. Weaknesses in security architectures allow successful eavesdropping, message tampering and masquerading attacks to occur, with disastrous consequences for end users, companies and other organizations. The KASUMI block cipher lies at the core of both the f8 data confidentiality algorithm and the f9 data integrity algorithm for Universal Mobile Telecommunications System networks. The design goal is to increase the data conversion rate i.e. the throughput to a substantial value so that the design can be used as a cryptographic coprocessor in high speed network applications. Keywords— Xilinx ISE, Language used: Verilog HDL, Platform Used: family- Vertex4, Device-XC4VLX80 I. INTRODUCTION Symmetric key cryptographic algorithms have a single keyIJERT IJERT for both encryption and decryption. -

SHA-3 and the Hash Function Keccak
Christof Paar Jan Pelzl SHA-3 and The Hash Function Keccak An extension chapter for “Understanding Cryptography — A Textbook for Students and Practitioners” www.crypto-textbook.com Springer 2 Table of Contents 1 The Hash Function Keccak and the Upcoming SHA-3 Standard . 1 1.1 Brief History of the SHA Family of Hash Functions. .2 1.2 High-level Description of Keccak . .3 1.3 Input Padding and Generating of Output . .6 1.4 The Function Keccak- f (or the Keccak- f Permutation) . .7 1.4.1 Theta (q)Step.......................................9 1.4.2 Steps Rho (r) and Pi (p).............................. 10 1.4.3 Chi (c)Step ........................................ 10 1.4.4 Iota (i)Step......................................... 11 1.5 Implementation in Software and Hardware . 11 1.6 Discussion and Further Reading . 12 1.7 Lessons Learned . 14 Problems . 15 References ......................................................... 17 v Chapter 1 The Hash Function Keccak and the Upcoming SHA-3 Standard This document1 is a stand-alone description of the Keccak hash function which is the basis of the upcoming SHA-3 standard. The description is consistent with the approach used in our book Understanding Cryptography — A Textbook for Students and Practioners [11]. If you own the book, this document can be considered “Chap- ter 11b”. However, the book is most certainly not necessary for using the SHA-3 description in this document. You may want to check the companion web site of Understanding Cryptography for more information on Keccak: www.crypto-textbook.com. In this chapter you will learn: A brief history of the SHA-3 selection process A high-level description of SHA-3 The internal structure of SHA-3 A discussion of the software and hardware implementation of SHA-3 A problem set and recommended further readings 1 We would like to thank the Keccak designers as well as Pawel Swierczynski and Christian Zenger for their extremely helpful input to this document. -

The Long Road to the Advanced Encryption Standard
The Long Road to the Advanced Encryption Standard Jean-Luc Cooke CertainKey Inc. [email protected], http://www.certainkey.com/˜jlcooke Abstract 1 Introduction This paper will start with a brief background of the Advanced Encryption Standard (AES) process, lessons learned from the Data Encryp- tion Standard (DES), other U.S. government Two decades ago the state-of-the-art in cryptographic publications and the fifteen first the private sector cryptography was—we round candidate algorithms. The focus of the know now—far behind the public sector. presentation will lie in presenting the general Don Coppersmith’s knowledge of the Data design of the five final candidate algorithms, Encryption Standard’s (DES) resilience to and the specifics of the AES and how it dif- the then unknown Differential Cryptanaly- fers from the Rijndael design. A presentation sis (DC), the design principles used in the on the AES modes of operation and Secure Secure Hash Algorithm (SHA) in Digital Hash Algorithm (SHA) family of algorithms Signature Standard (DSS) being case and will follow and will include discussion about point[NISTDSS][NISTDES][DC][NISTSHA1]. how it is directly implicated by AES develop- ments. The selection and design of the DES was shrouded in controversy and suspicion. This very controversy has lead to a fantastic acceler- Intended Audience ation in private sector cryptographic advance- ment. So intrigued by the NSA’s modifica- tions to the Lucifer algorithm, researchers— This paper was written as a supplement to a academic and industry alike—powerful tools presentation at the Ottawa International Linux in assessing block cipher strength were devel- Symposium.