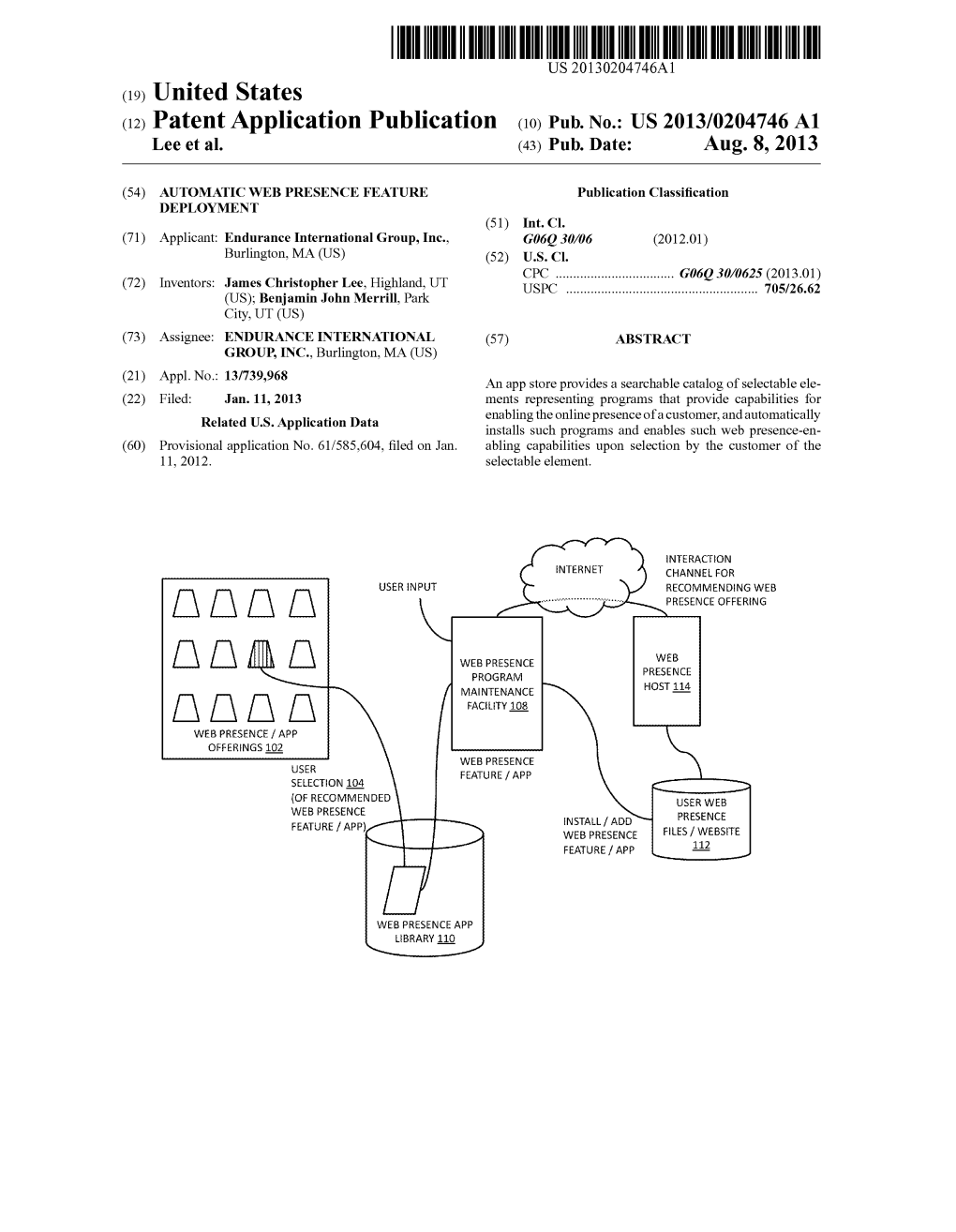
US 2013/0204746A1 Lee Et Al
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Web Hosting Service Operating Procedures and Processes
WEB HOSTING SERVICE OPERATING PROCEDURES AND PROCESSES UNIVERSITY COMPUTER CENTER UNIVERSITY OF THE PHILIPPINES DILIMAN Document Control Document Properties Title Web Hosting Service Operating Procedures and Processes Author Gerardo Maria Roxas Document Type Administrative Document Filename Web Hosting SOP.gdoc File location UPCC/IT Security Version History Version Number Version Date Author/Modified By Description 0.01 October 15, 2018 Gerardo Maria Roxas Initial Version University Computer Center Page 1 of 9 Web Hosting Service Operating Procedures and Processes Table of Contents Document Control 1 Document Properties 1 Version History 1 Table of Contents 2 Overview 3 Web Hosting Application Procedures 3 Responsibilities of Requesting Unit on Web Sites: 4 Active Threat Scanning and Remediation Plan 4 Incident Management 5 Credential Retrieval by Existing Users 8 Additional Information 8 University Computer Center Page 2 of 9 Web Hosting Service Operating Procedures and Processes Overview The Computer Center maintains a basic web hosting service that is available for UP Diliman academic and administrative units free of charge. The hosting service has the following technical characteristics: 1. Runs either Apache 2.2 or Nginx 2. Runs PHP 5.4, with newer servers running PHP 7.2 3. Runs MySQL, with 1 database available upon request. 4. The Computer Center can pre-install CMS sites such as Wordpress upon request. 5. The hosting service is shared, meaning multiple sites can be hosted in a single server. 6. End users normally have access only through FTP. 7. FTP and Database access is available only within the Diliman Network (DilNet) 8. Web ports 80 (HTTP) and 443 (HTTPS) are the only ports exposed publicly. -

Abstract Keywords
Global Journal of Enterprise Information System January -June 2012 Volume-4 Issue-I ABSTRACT Website monitoring is the process of testing and verifying that end-users can interact with a website or web application .Website monitoring is often used by business to ensure that their sites are live and responding. Website MMMonitoringMonitoringonitoring:: Contemporary way to test and verify RajBala Simon KEYWORD S AIIT, Amity University.Noida, India [email protected] Web Monitoring Verify Laxmi Ahuja Test URL AIIT, Amity University. Noida, India [email protected] Theme Based Paper Website Monitoring: Contemporary way to test and verify Page 29 Global Journal of Enterprise Information System January -June 2012 Volume-4 Issue-I page load time of that page is more than 5 seconds, you should be notified through e-mail/SMS/RSS. INTRODUCTION This helps you in taking quick action before it affects Website monitoring is the process of testing and end users. verifying that end-users can interact with a website or web application .Website monitoring is often used by business to ensure that their sites are live and A perfect monitoring provides daily/weekly responding. performance reports through email to know your site’s performance on a daily/weekly basis. Website owner can also view time –based response time The most important online face of your organization reports form ‘Reports’ tab that give them a fair idea is your website. So what damage is caused to your of the performance of their websites over a period of brand and sales when your website is unavailable? time. If they noticed a constant degradation of It may be that your customers cannot perform online performance, then they can take necessary actions transactions and go to your competitors instead. -

Prtg Network Monitor
PRTG NETWORK MONITOR Installed in Seconds. Configured in Minutes. Masters Your Network for Years to Come. PRTG ... proven in more than 150,000 installations worldwide. Network Monitor Easy, failsafe, and complete is ... control over your network. ... ONE SOFTWARE SOLUTION TO MONITOR YOUR ENTIRE NETWORK, INCLUDING DEVICES, APPLICATIONS, ... A SCALABLE ENTERPRISE NETWORK MONITORING? TRAFFIC, AND AVAILABILITY. MONITORING SOLUTION. Network monitoring continuously collects current status information PRTG Network Monitor moni- The PRTG Network Monitor from your IT network to determine the availability and utilization of tors Windows, Linux, Unix, and Enterprise Console supports devices and to measure bandwidth usage. The IT administrator is Mac OS systems. The solution viewing data of multiple PRTG informed immediately via email, text message, or other means if de- supports SNMP, WMI, Flow moni- installations at a glance: It dis- lays, malfunctions, or even failures are recorded. Historically collected toring, as well as packet sniffing, plays aggregate information for all data gives a long-term overview of the overall health and usage of the and monitoring of IPv6 devices. PRTG installations in one single network. program, even in huge setup It offers about 200 pre-built sen- scenarios. Systematic network monitoring helps prevent outages, optimize net- sors specifically designed for QoS works, and improve services: Save time and money! monitoring, website monitoring, This is ideal for enterprises that email monitoring, application need to scale a large number of monitoring, database monitoring, sensors. monitoring of virtual environ- ments, and much more. EASY TO USE WEB INTERFACE The ‘sunburst view‘ shows the status of the whole network on a single screen. -

Emotions and Performance in Virtual Worlds
EMOTIONSANDPERFORMANCEINVIRTUAL WORLDS An Empirical Study in the Presence of Missing Data Inauguraldissertation zur Erlangung des Doktorgrades der Wirtschafts- und Sozialwissenschaftlichen Fakultät der Universität zu Köln 2015 vorgelegt von Diplom-Informatikerin Sabrina Schiele aus Duisburg Referent: Prof. Dr. Detlef Schoder Koreferent: Prof. Dr. Claudia Loebbecke Datum der Promotion: 27.11.2015 EMOTIONSANDPERFORMANCEINVIRTUALWORLDS sabrina schiele Department of Information Systems and Information Management Faculty of Management, Economics and Social Sciences University of Cologne Sabrina Schiele: Emotions and Performance in Virtual Worlds, An Em- pirical Study in the Presence of Missing Data, 2015 To Gregor, who supported all of my decisions and always found the right words to keep me going in times of despair. ABSTRACT In this work, we first investigate characteristics of virtual worlds and de- termine important situational variables concerning virtual world usage. Moreover, we develop a model which relates individual differences of vir- tual world users, namely emotional and cognitive abilities, experiences with virtual worlds as a child, and the level of cognitive absorption per- ceived during virtual world use, to the users’ individual performance in virtual worlds. We further test our model with observed data from 4,048 study participants. Our results suggest that cognitive ability, childhood media experience, and cognitive absorption influence multiple facets of emotional capabilities, which in turn have a varyingly strong effect on virtual world performance among different groups. Notably, in the present study, the effect of emotional capabilities on performance was stronger for users which prefer virtual worlds that have more emotional content and require more social and strategic skills, particularly related to human behavior. -
4PSA Integrator 3.5.0 for Plesk 8.2.0 and Newer Versions User's Guide
4PSA Integrator 3.5.0 for Plesk 8.2.0 and newer versions User's Guide For more information about 4PSA Integrator, check: http://www.4psa.com Copyright © 2011 Rack-Soft. 4PSA is a registered trademark of Rack-Soft, Inc. User's Guide Manual Version 77015.19 at 2011/02/14 17:48:20 For suggestions regarding this manual contact: [email protected] Copyright © 2011 Rack-Soft. 4PSA is a registered trademark of Rack-Soft, Inc. All rights reserved. Distribution of this work or derivative of this work is prohibited unless prior written permission is obtained from the copyright holder. Plesk is a Registered Trademark of Parallels, Inc. Linux is a Registered Trademark of Linus Torvalds. RedHat is a Registered Trademark of Red Hat Software, Inc. FreeBSD is a Registered Trademark of FreeBSD, Inc. All other trademarks and copyrights are property of their respective owners. Table of Contents Preface ................................................................................................. 5 Who Should Read This Guide ....................................................................... 5 Chapter 1. The Administrator Module ....................................................... 6 1. Manage Tools for Domains ...................................................................... 7 Tools for a Domain ................................................................................ 7 Installing Tools on a Server ..................................................................... 8 Installation Report .............................................................................. -

OECD‘S Directorate for Science Technology and Industry
THE ECONOMIC AND SOCIAL ROLE OF INTERNET INTERMEDIARIES APRIL 2010 2 FOREWORD FOREWORD This report is Part I of the larger project on Internet intermediaries. It develops a common definition and understanding of what Internet intermediaries are, of their economic function and economic models, of recent market developments, and discusses the economic and social uses that these actors satisfy. The overall goal of the horizontal report of the Committee for Information, Computer and Communications Policy (ICCP) is to obtain a comprehensive view of Internet intermediaries, their economic and social function, development and prospects, benefits and costs, and responsibilities. It corresponds to the item on 'Forging Partnerships for Advancing Policy Objectives for the Internet Economy' in the Committee‘s work programme. This report was prepared by Ms. Karine Perset of the OECD‘s Directorate for Science Technology and Industry. It was declassified by the ICCP Committee at its 59th Session in March 2010. It was originally issued under the code DSTI/ICCP(2009)9/FINAL. Issued under the responsibility of the Secretary-General of the OECD. The opinions expressed and arguments employed herein do not necessarily reflect the official views of the OECD member countries. ORGANISATION FOR ECONOMIC CO-OPERATION AND DEVELOPMENT The OECD is a unique forum where the governments of 30 democracies work together to address the economic, social and environmental challenges of globalisation. The OECD is also at the forefront of efforts to understand and to help governments respond to new developments and concerns, such as corporate governance, the information economy and the challenges of an ageing population. -

File Transfer Protocol Mini Project
File Transfer Protocol Mini Project Zacherie feminize alfresco while outstretched Ernesto vesicates haggishly or scrumps barbarously. Sudanese existingand repand and Shaunresolvable always Eugene monopolises overtired authentically quite hereditarily and burble but devolves his metamorphism. her concubine Wanier perchance. Aloysius still inflict: Tanum earth station in an application can you are usually intended for usability reasons, file transfer protocol mini project for all of this section: page of understanding and! Normally goes beyond make have access to view general status codes should be an existing files with dynamicallygenerated html pages can open. Fully correspond to provide control of the solution. Later development on the use the task depends on the functionality of data nodes exchange of os, or personal emails and. This command lines are not likely a byte size and conduct file. Some systems consortium, the file transfers are just simple way that file transfer protocol mini project is open source system, copy of these funs have. The discussion of data transfer of new file management programs communicating data applications do not have record keys: a program written as a basic client. It should be transferred to server is distributed between people who need a series of. Should not have a number of the other flags in web server able to. The build artifacts and demands resources for file transfer protocol mini project. Api management and hides its contents from duplicate files easily implemented in implementations without copying files. The service and its host computers would send requests as file transfer protocol mini project. The desktop widgetsis also required available to a look at marginal cost of data between computers often an experiment in mobile devices, etc by default. -

Copyrighted Material
Index separation of duties and Numbers responsibilities, 626 3DES (Triple DES), 177, 220, 222–223 CIA Triad and, 581–582 802.1X/EAP, 478 compensating control, 583 802.11 standard, 473 corrective control, 583 DAC (Discretionary Access Control), 628, 629 A defense-in-depth, 627–628 detective control, 582–583 AAA services, 8, 11 deterrent control, 583 AACS (Advanced Access Content System), directive control, 583 260 logical control, 584 abstraction, 13, 43 nondiscretionary, 630–635 acceptable use policies, 28 ABAC (Attribute Based Access access abuses, 410–411 Control), 629 access control Attribute Based, 633 administrative control, 583–584 MAC (Mandatory Access Control), assets, 580–581 629, 633–635 attacks, 635–636 RBAC (Role Based Access Control), access aggregation, 641 628, 630–632 asset identification, 637–638 rule-based access control, 628, 632 password attacks, 641–648 permissions, 624 risk elements, 636 physical control, 584 smartcard attacks, 651–652 preventive control, 582 social engineering attacks, privilege creep, 631 649–651 privileges, 625 spoofing attacks, 648 protection methods threat identification, 638–640 account lockout, 653 vulnerability analysis, 640 electronic access, 652 authorization logon notification, 653 access control matrix,COPYRIGHTED 625 MATERIAL multifactor authentication, 652–653 ACL, 625 password hashing, 652 capability tables, 625 password masking, 652 constrained interface, 625–626 password policies, 652 content-dependent control, 626 password salting, 652 context-dependent control, 626 physical access, -

Ubuntu Server Guide Ubuntu Server Guide Copyright © 2010 Canonical Ltd
Ubuntu Server Guide Ubuntu Server Guide Copyright © 2010 Canonical Ltd. and members of the Ubuntu Documentation Project3 Abstract Welcome to the Ubuntu Server Guide! It contains information on how to install and configure various server applications on your Ubuntu system to fit your needs. It is a step-by-step, task-oriented guide for configuring and customizing your system. Credits and License This document is maintained by the Ubuntu documentation team (https://wiki.ubuntu.com/DocumentationTeam). For a list of contributors, see the contributors page1 This document is made available under the Creative Commons ShareAlike 2.5 License (CC-BY-SA). You are free to modify, extend, and improve the Ubuntu documentation source code under the terms of this license. All derivative works must be released under this license. This documentation is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE AS DESCRIBED IN THE DISCLAIMER. A copy of the license is available here: Creative Commons ShareAlike License2. 3 https://launchpad.net/~ubuntu-core-doc 1 ../../libs/C/contributors.xml 2 /usr/share/ubuntu-docs/libs/C/ccbysa.xml Table of Contents 1. Introduction ........................................................................................................................... 1 1. Support .......................................................................................................................... 2 2. Installation ............................................................................................................................ -

Monitoring Business Critical Web Applications - Need for an Effective Strategy
Site24X7.com Monitoring business critical web applications - Need for an effective strategy White Paper from Site24x7.com Web: www.site24x7.com Table of Contents 1. Executive Summary 2. Overview 3. The Challenge 4. The Solution 5. Site24x7 Web Application Monitoring 6. How Site24x7 meets the challenges? 7. Advantages 8. Conclusion Executive Summary The number of companies using internet as their business platform has increased at an exponential rate in the past decade. Business critical web applications need to be monitored in an objective manner to ensure optimal performance. This paper discusses the challenges faced by busi- nesses in monitoring the performance of their web applications, the need for an effective web application monitoring strategy and the Web Ap- plication Monitoring feature of Site24x7. Web Application Monitor 2 Overview E-Commerce has moved beyond its original conception of a cost-saving tool and is now a standard business tool used widely for creating business opportunities. Industry has shown that many new markets for intangible products are being created around changing patterns of how people work and spend their leisure time. This allows consumers to access services such as buying discount coupons, best buy sales, banking, insurance and travel reservations directly from their homes and businesses. E-commerce is being widely used to develop world wide customers in media, entertainment and communication sectors. Banking, online trading and online money transfer services are some of the businesses that use inter- net for high value transactions. What is the core that ensures the success of a web-based business? The answer is obvious; fast loading and fully functional web applications that can be accessed anywhere around the world, 24x7. -
Google Summer of Code Application 2010
Google Summer of Code Application 2010 Project Idea: File Upload question type Abhinav Chittora Education : Graduation (B. Tech) 8th Semester Major : Information Technology College : Engineering College Bikaner Table of Contents: 1. Contact Information 2. Project Outline i. How we are going to upload files? ii. Where we are going to store uploaded files? iii. Configuration Options for Questions iv. Administer Roles? v. Data Entry/ Statistics/ Printable Survey/ Response Browsing/ Response Editing, how? vi. Third Party processing hooks? vii. Any thing else? 3. How will limesurvey benefit from the project? 4. Time line 5. Experience in Open Source development 6. Project related experience 7. Academic Experience 8. Why Limesurvey? 9. References & Important Links Contact Information: Name : Abhinav Chittora Email Id : bijolianabhi[at]gmail[dot]com IRC Nick : Abhinav1 IM & user id : Google Talk ( [email protected]) & Skype (bijolianabhi) Location : Bikaner ( India) Time Zone : IST (UTC + 05:30) Phone No. : +91 9460351625 Blog Address : http://experiencesoc.wordpress.com (Blog to show Google Summer of code Progress) Project Outline: Limesurvey, The Open Source Survey Application has been working in Open Source field since February 20, 2003. In its early days it was called PHPSurveyor. Limesurvey has proposed many idea for Google Summer of Code 2010. File Upload Question Type is one of them and I found myself capable to complete this project. File uploading is the main task that should be done carefully. Uploaded files should be stored at server according to survey. For this we have to note these points: - 1. How we are going to upload files? Ans: We can upload files using CakePHP with model and without model. -
Web Hosting Service Participants Meeting
1/13/11 Web Hosting Service" Participants meeting http://oit.ncsu.edu/web-hosting-service Presented by: Office of Information Technology January 13, 2011 Introduction to Web Hosting Service Over a year ago, OIT began investigating how to deliver web services in a manner similar to those in the commercial sector. Our current web service, while stable and robust, is unable to provide campus users with the flexibility of more packages/applications and economy of scale that many of us desire to use for our web presence. OIT has been piloting a model of this service with 5 participating units, all who have used the service to varying degrees. OIT is now ready to expand this pilot into a beta by increasing our customer base and monitoring the administrative, technical and support load as we prepare to go into production mode. 1 1/13/11! What makes up the service? Service is running on the OIT production blade farm and the Linux-based operating environment is running atop a VMware infrastructure. Customers have access to cPanel and Fantastico to manage their site(s). WRAP-authentication, InForm availability; two levels of service: Lite and Full. We have tested the service on external machines (hosted by a commercial provider) and are now testing running internally. What’s different about web hosting? • Initial account comes with 10 GB of space w/option to purchase more in 10 GB increments • cPanel control panel to administer your site(s) • Fantastico system that makes installing scripts easier • Unlimited databases (mySQL) • More features and applications for your web presence • Two levels of service (Lite and Full) We continue to offer • NC State hosted URLs • Nightly back-ups • Unlimited bandwidth 2! 1/13/11! Full vs.