The XTR Public Key System
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Bilinear Map Cryptography from Progressively Weaker Assumptions
Full version of an extended abstract published in Proceedings of CT-RSA 2013, Springer-Verlag, Feb. 2013. Available from the IACR Cryptology ePrint Archive as Report 2012/687. The k-BDH Assumption Family: Bilinear Map Cryptography from Progressively Weaker Assumptions Karyn Benson, Hovav Shacham ∗ Brent Watersy University of California, San Diego University of Texas at Austin fkbenson, [email protected] [email protected] February 4, 2013 Abstract Over the past decade bilinear maps have been used to build a large variety of cryptosystems. In addition to new functionality, we have concurrently seen the emergence of many strong assump- tions. In this work, we explore how to build bilinear map cryptosystems under progressively weaker assumptions. We propose k-BDH, a new family of progressively weaker assumptions that generalizes the de- cisional bilinear Diffie-Hellman (DBDH) assumption. We give evidence in the generic group model that each assumption in our family is strictly weaker than the assumptions before it. DBDH has been used for proving many schemes secure, notably identity-based and functional encryption schemes; we expect that our k-BDH will lead to generalizations of many such schemes. To illustrate the usefulness of our k-BDH family, we construct a family of selectively secure Identity-Based Encryption (IBE) systems based on it. Our system can be viewed as a generalization of the Boneh-Boyen IBE, however, the construction and proof require new ideas to fit the family. We then extend our methods to produces hierarchical IBEs and CCA security; and give a fully secure variant. In addition, we discuss the opportunities and challenges of building new systems under our weaker assumption family. -
Public-Key Cryptography
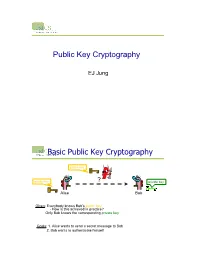
Public Key Cryptography EJ Jung Basic Public Key Cryptography public key public key ? private key Alice Bob Given: Everybody knows Bob’s public key - How is this achieved in practice? Only Bob knows the corresponding private key Goals: 1. Alice wants to send a secret message to Bob 2. Bob wants to authenticate himself Requirements for Public-Key Crypto ! Key generation: computationally easy to generate a pair (public key PK, private key SK) • Computationally infeasible to determine private key PK given only public key PK ! Encryption: given plaintext M and public key PK, easy to compute ciphertext C=EPK(M) ! Decryption: given ciphertext C=EPK(M) and private key SK, easy to compute plaintext M • Infeasible to compute M from C without SK • Decrypt(SK,Encrypt(PK,M))=M Requirements for Public-Key Cryptography 1. Computationally easy for a party B to generate a pair (public key KUb, private key KRb) 2. Easy for sender to generate ciphertext: C = EKUb (M ) 3. Easy for the receiver to decrypt ciphertect using private key: M = DKRb (C) = DKRb[EKUb (M )] Henric Johnson 4 Requirements for Public-Key Cryptography 4. Computationally infeasible to determine private key (KRb) knowing public key (KUb) 5. Computationally infeasible to recover message M, knowing KUb and ciphertext C 6. Either of the two keys can be used for encryption, with the other used for decryption: M = DKRb[EKUb (M )] = DKUb[EKRb (M )] Henric Johnson 5 Public-Key Cryptographic Algorithms ! RSA and Diffie-Hellman ! RSA - Ron Rives, Adi Shamir and Len Adleman at MIT, in 1977. • RSA -

Circuit-Extension Handshakes for Tor Achieving Forward Secrecy in a Quantum World
Proceedings on Privacy Enhancing Technologies ; 2016 (4):219–236 John M. Schanck*, William Whyte, and Zhenfei Zhang Circuit-extension handshakes for Tor achieving forward secrecy in a quantum world Abstract: We propose a circuit extension handshake for 2. Anonymity: Some one-way authenticated key ex- Tor that is forward secure against adversaries who gain change protocols, such as ntor [13], guarantee that quantum computing capabilities after session negotia- the unauthenticated peer does not reveal their iden- tion. In doing so, we refine the notion of an authen- tity just by participating in the protocol. Such pro- ticated and confidential channel establishment (ACCE) tocols are deemed one-way anonymous. protocol and define pre-quantum, transitional, and post- 3. Forward Secrecy: A protocol provides forward quantum ACCE security. These new definitions reflect secrecy if the compromise of a party’s long-term the types of adversaries that a protocol might be de- key material does not affect the secrecy of session signed to resist. We prove that, with some small mod- keys negotiated prior to the compromise. Forward ifications, the currently deployed Tor circuit extension secrecy is typically achieved by mixing long-term handshake, ntor, provides pre-quantum ACCE security. key material with ephemeral keys that are discarded We then prove that our new protocol, when instantiated as soon as the session has been established. with a post-quantum key encapsulation mechanism, Forward secret protocols are a particularly effective tool achieves the stronger notion of transitional ACCE se- for resisting mass surveillance as they resist a broad curity. Finally, we instantiate our protocol with NTRU- class of harvest-then-decrypt attacks. -

Quadratic Reciprocity and Computing Modular Square Roots.Pdf
12 Quadratic reciprocity and computing modular square roots In §2.8, we initiated an investigation of quadratic residues. This chapter continues this investigation. Recall that an integer a is called a quadratic residue modulo a positive integer n if gcd(a, n) = 1 and a ≡ b2 (mod n) for some integer b. First, we derive the famous law of quadratic reciprocity. This law, while his- torically important for reasons of pure mathematical interest, also has important computational applications, including a fast algorithm for testing if an integer is a quadratic residue modulo a prime. Second, we investigate the problem of computing modular square roots: given a quadratic residue a modulo n, compute an integer b such that a ≡ b2 (mod n). As we will see, there are efficient probabilistic algorithms for this problem when n is prime, and more generally, when the factorization of n into primes is known. 12.1 The Legendre symbol For an odd prime p and an integer a with gcd(a, p) = 1, the Legendre symbol (a j p) is defined to be 1 if a is a quadratic residue modulo p, and −1 otherwise. For completeness, one defines (a j p) = 0 if p j a. The following theorem summarizes the essential properties of the Legendre symbol. Theorem 12.1. Let p be an odd prime, and let a, b 2 Z. Then we have: (i) (a j p) ≡ a(p−1)=2 (mod p); in particular, (−1 j p) = (−1)(p−1)=2; (ii) (a j p)(b j p) = (ab j p); (iii) a ≡ b (mod p) implies (a j p) = (b j p); 2 (iv) (2 j p) = (−1)(p −1)=8; p−1 q−1 (v) if q is an odd prime, then (p j q) = (−1) 2 2 (q j p). -

Public Key Cryptography And
PublicPublic KeyKey CryptographyCryptography andand RSARSA Raj Jain Washington University in Saint Louis Saint Louis, MO 63130 [email protected] Audio/Video recordings of this lecture are available at: http://www.cse.wustl.edu/~jain/cse571-11/ Washington University in St. Louis CSE571S ©2011 Raj Jain 9-1 OverviewOverview 1. Public Key Encryption 2. Symmetric vs. Public-Key 3. RSA Public Key Encryption 4. RSA Key Construction 5. Optimizing Private Key Operations 6. RSA Security These slides are based partly on Lawrie Brown’s slides supplied with William Stallings’s book “Cryptography and Network Security: Principles and Practice,” 5th Ed, 2011. Washington University in St. Louis CSE571S ©2011 Raj Jain 9-2 PublicPublic KeyKey EncryptionEncryption Invented in 1975 by Diffie and Hellman at Stanford Encrypted_Message = Encrypt(Key1, Message) Message = Decrypt(Key2, Encrypted_Message) Key1 Key2 Text Ciphertext Text Keys are interchangeable: Key2 Key1 Text Ciphertext Text One key is made public while the other is kept private Sender knows only public key of the receiver Asymmetric Washington University in St. Louis CSE571S ©2011 Raj Jain 9-3 PublicPublic KeyKey EncryptionEncryption ExampleExample Rivest, Shamir, and Adleman at MIT RSA: Encrypted_Message = m3 mod 187 Message = Encrypted_Message107 mod 187 Key1 = <3,187>, Key2 = <107,187> Message = 5 Encrypted Message = 53 = 125 Message = 125107 mod 187 = 5 = 125(64+32+8+2+1) mod 187 = {(12564 mod 187)(12532 mod 187)... (1252 mod 187)(125 mod 187)} mod 187 Washington University in -

Authentication in Key-Exchange: Definitions, Relations and Composition
Authentication in Key-Exchange: Definitions, Relations and Composition Cyprien Delpech de Saint Guilhem1;2, Marc Fischlin3, and Bogdan Warinschi2 1 imec-COSIC, KU Leuven, Belgium 2 Dept Computer Science, University of Bristol, United Kingdom 3 Computer Science, Technische Universit¨atDarmstadt, Germany [email protected], [email protected], [email protected] Abstract. We present a systematic approach to define and study authentication notions in authenti- cated key-exchange protocols. We propose and use a flexible and expressive predicate-based definitional framework. Our definitions capture key and entity authentication, in both implicit and explicit vari- ants, as well as key and entity confirmation, for authenticated key-exchange protocols. In particular, we capture critical notions in the authentication space such as key-compromise impersonation resis- tance and security against unknown key-share attacks. We first discuss these definitions within the Bellare{Rogaway model and then extend them to Canetti{Krawczyk-style models. We then show two useful applications of our framework. First, we look at the authentication guarantees of three representative protocols to draw several useful lessons for protocol design. The core technical contribution of this paper is then to formally establish that composition of secure implicitly authenti- cated key-exchange with subsequent confirmation protocols yields explicit authentication guarantees. Without a formal separation of implicit and explicit authentication from secrecy, a proof of this folklore result could not have been established. 1 Introduction The commonly expected level of security for authenticated key-exchange (AKE) protocols comprises two aspects. Authentication provides guarantees on the identities of the parties involved in the protocol execution. -

RSA: Encryption, Decryption
Data Communications & Networks Session 11 – Main Theme Network Security Dr. Jean-Claude Franchitti New York University Computer Science Department Courant Institute of Mathematical Sciences Adapted from course textbook resources Computer Networking: A Top-Down Approach, 5/E Copyright 1996-2009 J.F. Kurose and K.W. Ross, All Rights Reserved 1 Agenda 1 Session Overview 2 Network Security 3 Summary and Conclusion 2 What is the class about? .Course description and syllabus: »http://www.nyu.edu/classes/jcf/CSCI-GA.2262-001/ »http://www.cs.nyu.edu/courses/spring15/CSCI- GA.2262-001/index.html .Textbooks: » Computer Networking: A Top-Down Approach (5th Edition) James F. Kurose, Keith W. Ross Addison Wesley ISBN-10: 0136079679, ISBN-13: 978-0136079675, 5th Edition (03/09) 3 Course Overview . Computer Networks and the Internet . Application Layer . Fundamental Data Structures: queues, ring buffers, finite state machines . Data Encoding and Transmission . Local Area Networks and Data Link Control . Wireless Communications . Packet Switching . OSI and Internet Protocol Architecture . Congestion Control and Flow Control Methods . Internet Protocols (IP, ARP, UDP, TCP) . Network (packet) Routing Algorithms (OSPF, Distance Vector) . IP Multicast . Sockets 4 Course Approach . Introduction to Basic Networking Concepts (Network Stack) . Origins of Naming, Addressing, and Routing (TCP, IP, DNS) . Physical Communication Layer . MAC Layer (Ethernet, Bridging) . Routing Protocols (Link State, Distance Vector) . Internet Routing (BGP, OSPF, Programmable Routers) . TCP Basics (Reliable/Unreliable) . Congestion Control . QoS, Fair Queuing, and Queuing Theory . Network Services – Multicast and Unicast . Extensions to Internet Architecture (NATs, IPv6, Proxies) . Network Hardware and Software (How to Build Networks, Routers) . Overlay Networks and Services (How to Implement Network Services) . -

The Twin Diffie-Hellman Problem and Applications
The Twin Diffie-Hellman Problem and Applications David Cash1 Eike Kiltz2 Victor Shoup3 February 10, 2009 Abstract We propose a new computational problem called the twin Diffie-Hellman problem. This problem is closely related to the usual (computational) Diffie-Hellman problem and can be used in many of the same cryptographic constructions that are based on the Diffie-Hellman problem. Moreover, the twin Diffie-Hellman problem is at least as hard as the ordinary Diffie-Hellman problem. However, we are able to show that the twin Diffie-Hellman problem remains hard, even in the presence of a decision oracle that recognizes solutions to the problem — this is a feature not enjoyed by the Diffie-Hellman problem in general. Specifically, we show how to build a certain “trapdoor test” that allows us to effectively answer decision oracle queries for the twin Diffie-Hellman problem without knowing any of the corresponding discrete logarithms. Our new techniques have many applications. As one such application, we present a new variant of ElGamal encryption with very short ciphertexts, and with a very simple and tight security proof, in the random oracle model, under the assumption that the ordinary Diffie-Hellman problem is hard. We present several other applications as well, including: a new variant of Diffie and Hellman’s non-interactive key exchange protocol; a new variant of Cramer-Shoup encryption, with a very simple proof in the standard model; a new variant of Boneh-Franklin identity-based encryption, with very short ciphertexts; a more robust version of a password-authenticated key exchange protocol of Abdalla and Pointcheval. -

Ch 13 Digital Signature
1 CH 13 DIGITAL SIGNATURE Cryptography and Network Security HanJung Mason Yun 2 Index 13.1 Digital Signatures 13.2 Elgamal Digital Signature Scheme 13.3 Schnorr Digital Signature Scheme 13.4 NIST Digital Signature Algorithm 13.6 RSA-PSS Digital Signature Algorithm 3 13.1 Digital Signature - Properties • It must verify the author and the date and time of the signature. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • The digital signature function includes authentication. 4 5 6 Attacks and Forgeries • Key-Only attack • Known message attack • Generic chosen message attack • Directed chosen message attack • Adaptive chosen message attack 7 Attacks and Forgeries • Total break • Universal forgery • Selective forgery • Existential forgery 8 Digital Signature Requirements • It must be a bit pattern that depends on the message. • It must use some information unique to the sender to prevent both forgery and denial. • It must be relatively easy to produce the digital signature. • It must be relatively easy to recognize and verify the digital signature. • It must be computationally infeasible to forge a digital signature, either by constructing a new message for an existing digital signature or by constructing a fraudulent digital signature for a given message. • It must be practical to retain a copy of the digital signature in storage. 9 Direct Digital Signature • Digital signature scheme that involves only the communication parties. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • Thus, the digital signature function includes the authentication function. -

Blind Schnorr Signatures in the Algebraic Group Model
An extended abstract of this work appears in EUROCRYPT’20. This is the full version. Blind Schnorr Signatures and Signed ElGamal Encryption in the Algebraic Group Model Georg Fuchsbauer1, Antoine Plouviez2, and Yannick Seurin3 1 TU Wien, Austria 2 Inria, ENS, CNRS, PSL, Paris, France 3 ANSSI, Paris, France first.last@{tuwien.ac.at,ens.fr,m4x.org} January 16, 2021 Abstract. The Schnorr blind signing protocol allows blind issuing of Schnorr signatures, one of the most widely used signatures. Despite its practical relevance, its security analysis is unsatisfactory. The only known security proof is rather informal and in the combination of the generic group model (GGM) and the random oracle model (ROM) assuming that the “ROS problem” is hard. The situation is similar for (Schnorr-)signed ElGamal encryption, a simple CCA2-secure variant of ElGamal. We analyze the security of these schemes in the algebraic group model (AGM), an idealized model closer to the standard model than the GGM. We first prove tight security of Schnorr signatures from the discrete logarithm assumption (DL) in the AGM+ROM. We then give a rigorous proof for blind Schnorr signatures in the AGM+ROM assuming hardness of the one-more discrete logarithm problem and ROS. As ROS can be solved in sub-exponential time using Wagner’s algorithm, we propose a simple modification of the signing protocol, which leaves the signatures unchanged. It is therefore compatible with systems that already use Schnorr signatures, such as blockchain protocols. We show that the security of our modified scheme relies on the hardness of a problem related to ROS that appears much harder. -

CS 255: Intro to Cryptography 1 Introduction 2 End-To-End
Programming Assignment 2 Winter 2021 CS 255: Intro to Cryptography Prof. Dan Boneh Due Monday, March 1st, 11:59pm 1 Introduction In this assignment, you are tasked with implementing a secure and efficient end-to-end encrypted chat client using the Double Ratchet Algorithm, a popular session setup protocol that powers real- world chat systems such as Signal and WhatsApp. As an additional challenge, assume you live in a country with government surveillance. Thereby, all messages sent are required to include the session key encrypted with a fixed public key issued by the government. In your implementation, you will make use of various cryptographic primitives we have discussed in class—notably, key exchange, public key encryption, digital signatures, and authenticated encryption. Because it is ill-advised to implement your own primitives in cryptography, you should use an established library: in this case, the Stanford Javascript Crypto Library (SJCL). We will provide starter code that contains a basic template, which you will be able to fill in to satisfy the functionality and security properties described below. 2 End-to-end Encrypted Chat Client 2.1 Implementation Details Your chat client will use the Double Ratchet Algorithm to provide end-to-end encrypted commu- nications with other clients. To evaluate your messaging client, we will check that two or more instances of your implementation it can communicate with each other properly. We feel that it is best to understand the Double Ratchet Algorithm straight from the source, so we ask that you read Sections 1, 2, and 3 of Signal’s published specification here: https://signal. -

Implementation and Performance Evaluation of XTR Over Wireless Network
Implementation and Performance Evaluation of XTR over Wireless Network By Basem Shihada [email protected] Dept. of Computer Science 200 University Avenue West Waterloo, Ontario, Canada (519) 888-4567 ext. 6238 CS 887 Final Project 19th of April 2002 Implementation and Performance Evaluation of XTR over Wireless Network 1. Abstract Wireless systems require reliable data transmission, large bandwidth and maximum data security. Most current implementations of wireless security algorithms perform lots of operations on the wireless device. This result in a large number of computation overhead, thus reducing the device performance. Furthermore, many current implementations do not provide a fast level of security measures such as client authentication, authorization, data validation and data encryption. XTR is an abbreviation of Efficient and Compact Subgroup Trace Representation (ECSTR). Developed by Arjen Lenstra & Eric Verheul and considered a new public key cryptographic security system that merges high level of security GF(p6) with less number of computation GF(p2). The claim here is that XTR has less communication requirements, and significant computation advantages, which indicate that XTR is suitable for the small computing devices such as, wireless devices, wireless internet, and general wireless applications. The hoping result is a more flexible and powerful secure wireless network that can be easily used for application deployment. This project presents an implementation and performance evaluation to XTR public key cryptographic system over wireless network. The goal of this project is to develop an efficient and portable secure wireless network, which perform a variety of wireless applications in a secure manner. The project literately surveys XTR mathematical and theoretical background as well as system implementation and deployment over wireless network.