Chapter 3: Block Ciphers and the Data Encryption Standard
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Data Encryption Standard (DES) – History
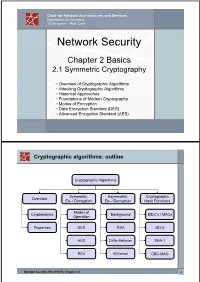
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Chapter 3 –Block Ciphers and the Data Cryptography and Network Encryption Standard Security All the afternoon Mungo had been working on Stern's Chapter 3 code, principally with the aid of the latest messages which he had copied down at the Nevin Square drop. Stern was very confident. He must be well aware London Central knew about that drop. It was obvious Fifth Edition that they didn't care how often Mungo read their messages, so confident were they in the by William Stallings impenetrability of the code. —Talking to Strange Men, Ruth Rendell Lecture slides by Lawrie Brown Modern Block Ciphers Block vs Stream Ciphers now look at modern block ciphers • block ciphers process messages in blocks, each one of the most widely used types of of which is then en/decrypted cryptographic algorithms • like a substitution on very big characters provide secrecy /hii/authentication services – 64‐bits or more focus on DES (Data Encryption Standard) • stream ciphers process messages a bit or byte at a time when en/decrypting to illustrate block cipher design principles • many current ciphers are block ciphers – better analysed – broader range of applications Block vs Stream Ciphers Block Cipher Principles • most symmetric block ciphers are based on a Feistel Cipher Structure • needed since must be able to decrypt ciphertext to recover messages efficiently • bloc k cihiphers lklook like an extremely large substitution • would need table of 264 entries for a 64‐bit block • instead create from smaller building blocks • using idea of a product cipher 1 Claude -

Feistel Like Construction of Involutory Binary Matrices with High Branch Number
Feistel Like Construction of Involutory Binary Matrices With High Branch Number Adnan Baysal1,2, Mustafa C¸oban3, and Mehmet Ozen¨ 3 1TUB¨ ITAK_ - BILGEM,_ PK 74, 41470, Gebze, Kocaeli, Turkey, [email protected] 2Kocaeli University, Department of Computer Engineering, Faculty of Engineering, Institute of Science, 41380, Umuttepe, Kocaeli, Turkey 3Sakarya University, Faculty of Arts and Sciences, Department of Mathematics, Sakarya, Turkey, [email protected], [email protected] August 4, 2016 Abstract In this paper, we propose a generic method to construct involutory binary matrices from a three round Feistel scheme with a linear round function. We prove bounds on the maximum achievable branch number (BN) and the number of fixed points of our construction. We also define two families of efficiently implementable round functions to be used in our method. The usage of these families in the proposed method produces matrices achieving the proven bounds on branch numbers and fixed points. Moreover, we show that BN of the transpose matrix is the same with the original matrix for the function families we defined. Some of the generated matrices are Maximum Distance Binary Linear (MDBL), i.e. matrices with the highest achievable BN. The number of fixed points of the generated matrices are close to the expected value for a random involution. Generated matrices are especially suitable for utilising in bitslice block ciphers and hash functions. They can be implemented efficiently in many platforms, from low cost CPUs to dedicated hardware. Keywords: Diffusion layer, bitslice cipher, hash function, involution, MDBL matrices, Fixed points. 1 Introduction Modern block ciphers and hash functions use two basic layers iteratively to provide security: confusion and diffusion. -

Block Ciphers and the Data Encryption Standard
Lecture 3: Block Ciphers and the Data Encryption Standard Lecture Notes on “Computer and Network Security” by Avi Kak ([email protected]) January 26, 2021 3:43pm ©2021 Avinash Kak, Purdue University Goals: To introduce the notion of a block cipher in the modern context. To talk about the infeasibility of ideal block ciphers To introduce the notion of the Feistel Cipher Structure To go over DES, the Data Encryption Standard To illustrate important DES steps with Python and Perl code CONTENTS Section Title Page 3.1 Ideal Block Cipher 3 3.1.1 Size of the Encryption Key for the Ideal Block Cipher 6 3.2 The Feistel Structure for Block Ciphers 7 3.2.1 Mathematical Description of Each Round in the 10 Feistel Structure 3.2.2 Decryption in Ciphers Based on the Feistel Structure 12 3.3 DES: The Data Encryption Standard 16 3.3.1 One Round of Processing in DES 18 3.3.2 The S-Box for the Substitution Step in Each Round 22 3.3.3 The Substitution Tables 26 3.3.4 The P-Box Permutation in the Feistel Function 33 3.3.5 The DES Key Schedule: Generating the Round Keys 35 3.3.6 Initial Permutation of the Encryption Key 38 3.3.7 Contraction-Permutation that Generates the 48-Bit 42 Round Key from the 56-Bit Key 3.4 What Makes DES a Strong Cipher (to the 46 Extent It is a Strong Cipher) 3.5 Homework Problems 48 2 Computer and Network Security by Avi Kak Lecture 3 Back to TOC 3.1 IDEAL BLOCK CIPHER In a modern block cipher (but still using a classical encryption method), we replace a block of N bits from the plaintext with a block of N bits from the ciphertext. -

Block Ciphers
Block Ciphers Chester Rebeiro IIT Madras CR STINSON : chapters 3 Block Cipher KE KD untrusted communication link Alice E D Bob #%AR3Xf34^$ “Attack at Dawn!!” message encryption (ciphertext) decryption “Attack at Dawn!!” Encryption key is the same as the decryption key (KE = K D) CR 2 Block Cipher : Encryption Key Length Secret Key Plaintext Ciphertext Block Cipher (Encryption) Block Length • A block cipher encryption algorithm encrypts n bits of plaintext at a time • May need to pad the plaintext if necessary • y = ek(x) CR 3 Block Cipher : Decryption Key Length Secret Key Ciphertext Plaintext Block Cipher (Decryption) Block Length • A block cipher decryption algorithm recovers the plaintext from the ciphertext. • x = dk(y) CR 4 Inside the Block Cipher PlaintextBlock (an iterative cipher) Key Whitening Round 1 key1 Round 2 key2 Round 3 key3 Round n keyn Ciphertext Block • Each round has the same endomorphic cryptosystem, which takes a key and produces an intermediate ouput • Size of the key is huge… much larger than the block size. CR 5 Inside the Block Cipher (the key schedule) PlaintextBlock Secret Key Key Whitening Round 1 Round Key 1 Round 2 Round Key 2 Round 3 Round Key 3 Key Expansion Expansion Key Key Round n Round Key n Ciphertext Block • A single secret key of fixed size used to generate ‘round keys’ for each round CR 6 Inside the Round Function Round Input • Add Round key : Add Round Key Mixing operation between the round input and the round key. typically, an ex-or operation Confusion Layer • Confusion layer : Makes the relationship between round Diffusion Layer input and output complex. -

KLEIN: a New Family of Lightweight Block Ciphers
KLEIN: A New Family of Lightweight Block Ciphers Zheng Gong1, Svetla Nikova1;2 and Yee Wei Law3 1Faculty of EWI, University of Twente, The Netherlands fz.gong, [email protected] 2 Dept. ESAT/SCD-COSIC, Katholieke Universiteit Leuven, Belgium 3 Department of EEE, The University of Melbourne, Australia [email protected] Abstract Resource-efficient cryptographic primitives become fundamental for realizing both security and efficiency in embedded systems like RFID tags and sensor nodes. Among those primitives, lightweight block cipher plays a major role as a building block for security protocols. In this paper, we describe a new family of lightweight block ciphers named KLEIN, which is designed for resource-constrained devices such as wireless sensors and RFID tags. Compared to the related proposals, KLEIN has ad- vantage in the software performance on legacy sensor platforms, while its hardware implementation can be compact as well. Key words. Block cipher, Wireless sensor network, Low-resource implementation. 1 Introduction With the development of wireless communication and embedded systems, we become increasingly de- pendent on the so called pervasive computing; examples are smart cards, RFID tags, and sensor nodes that are used for public transport, pay TV systems, smart electricity meters, anti-counterfeiting, etc. Among those applications, wireless sensor networks (WSNs) have attracted more and more attention since their promising applications, such as environment monitoring, military scouting and healthcare. On resource-limited devices the choice of security algorithms should be very careful by consideration of the implementation costs. Symmetric-key algorithms, especially block ciphers, still play an important role for the security of the embedded systems. -

Mirror Cipher Using Feistel Network
Mirror Cipher using Feistel Network 1 2 3 Ihsan Muhammad Asnadi Ranindya Paramitha Tony 123 Informatics Department, Institut Teknologi Bandung, Bandung 40132, Indonesia 1 2 3 E-mail: 1 [email protected] 1 [email protected] 1 [email protected] Abstract. Mirror cipher is a cipher built by creativity which has a specific feature of mirrored round function. As other ciphers, mirror cipher could be used to secure messages’ confidentiality and integrity. This cipher receives message and key inputs from its user. Then, it runs 9 rounds of feistel networks in ECB modes. Each round would run a round function which consists of 5 functions in mirrored order (9 function calls in total): s-box substitution, row substitution, column substitution, column cumulative xor, and round key addition. This cipher is implemented using Python and has been tested using several message and key combinations. Mirror cipher has applied Shanon’s diffusion and confusion property and proven to be secured from bruteforce and frequency analysis attack. 1. Introduction 1.1. Background In this modern world, data or messages are exchanged anytime and anywhere. To protect confidentiality and integrity of messages, people usually encrypt their messages before sending them, and then decrypt the received messages before reading them. These encryption and decryption practices and techniques are contained under the big concept of cryptography. There are many ciphers (encryption and decryption algorithms) that have been developed since the BC period. Ciphers are then divided into 2 kinds of ciphers, based on how it treats the message: stream cipher and block cipher. -

Development of the Advanced Encryption Standard
Volume 126, Article No. 126024 (2021) https://doi.org/10.6028/jres.126.024 Journal of Research of the National Institute of Standards and Technology Development of the Advanced Encryption Standard Miles E. Smid Formerly: Computer Security Division, National Institute of Standards and Technology, Gaithersburg, MD 20899, USA [email protected] Strong cryptographic algorithms are essential for the protection of stored and transmitted data throughout the world. This publication discusses the development of Federal Information Processing Standards Publication (FIPS) 197, which specifies a cryptographic algorithm known as the Advanced Encryption Standard (AES). The AES was the result of a cooperative multiyear effort involving the U.S. government, industry, and the academic community. Several difficult problems that had to be resolved during the standard’s development are discussed, and the eventual solutions are presented. The author writes from his viewpoint as former leader of the Security Technology Group and later as acting director of the Computer Security Division at the National Institute of Standards and Technology, where he was responsible for the AES development. Key words: Advanced Encryption Standard (AES); consensus process; cryptography; Data Encryption Standard (DES); security requirements, SKIPJACK. Accepted: June 18, 2021 Published: August 16, 2021; Current Version: August 23, 2021 This article was sponsored by James Foti, Computer Security Division, Information Technology Laboratory, National Institute of Standards and Technology (NIST). The views expressed represent those of the author and not necessarily those of NIST. https://doi.org/10.6028/jres.126.024 1. Introduction In the late 1990s, the National Institute of Standards and Technology (NIST) was about to decide if it was going to specify a new cryptographic algorithm standard for the protection of U.S. -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Symmetric Cryptography Chapter 6 Block vs Stream Ciphers • Block ciphers process messages into blocks, each of which is then en/decrypted – Like a substitution on very big characters • 64-bits or more • Stream ciphers process messages a bit or byte at a time when en/decrypting – Many current ciphers are block ciphers • Better analyzed. • Broader range of applications. Block vs Stream Ciphers Block Cipher Principles • Block ciphers look like an extremely large substitution • Would need table of 264 entries for a 64-bit block • Arbitrary reversible substitution cipher for a large block size is not practical – 64-bit general substitution block cipher, key size 264! • Most symmetric block ciphers are based on a Feistel Cipher Structure • Needed since must be able to decrypt ciphertext to recover messages efficiently Ideal Block Cipher Substitution-Permutation Ciphers • in 1949 Shannon introduced idea of substitution- permutation (S-P) networks – modern substitution-transposition product cipher • These form the basis of modern block ciphers • S-P networks are based on the two primitive cryptographic operations we have seen before: – substitution (S-box) – permutation (P-box) (transposition) • Provide confusion and diffusion of message Diffusion and Confusion • Introduced by Claude Shannon to thwart cryptanalysis based on statistical analysis – Assume the attacker has some knowledge of the statistical characteristics of the plaintext • Cipher needs to completely obscure statistical properties of original message • A one-time pad does this Diffusion -

A Novel Feistel Cipher Involving a Bunch of Keys Supplemented with XOR Operation
(IJACSA) International Journal of Advanced Computer Science and Applications, Vol. 3, No. 12, 2012 A Novel Feistel Cipher Involving a Bunch of Keys Supplemented with XOR Operation V.U.K Sastry K. Anup Kumar Dean R&D, Department of Computer Science and Associate Professor, Department of Computer Science Engineering, Sreenidhi Institute of Science & Tech. and Engineering, SNIST, Hyderabad, India Hyderabad, India Abstract—In this investigation, we have developed a novel block In order to satisfy (1.5), we chose ejk as an odd integer, cipher by modifying classical Feistel cipher. In this, we have used which lies in the interval [1-255], and thus we obtain djk also as a key bunched wherein each key has a multiplicative inverse. The an odd integer lying in the interval [1-255]. cryptanalysis carried out in this investigation clearly shows that this cipher cannot be broken by any attack. Here also we adopt an iterative procedure, and make use of the permutation process that consists of the interchange of the Keywords-encryption; decryption; cryptanalysis; avalanche effect; two halves of the plaintext , of course, represented in the form multiplicative inverse. of a pair of matrices. I. INTRODUCTION In the present analysis, our objective is to modify the Feistel cipher by including a bunch of keys. Here our interest is The study of the Feistel cipher [1-2] laid the foundation for to see how the different keys, occurring in the key bunch, the development of cryptography in the seventies of the last would influence the strength of the cipher. century. In the classical Feistel cipher the block size is 64 bits, and it is divided into two halves wherein each half is containing In what follows, we present the plan of the paper. -

Lecture Four
Lecture Four Today’s Topics . Historic Symmetric ciphers . Modern symmetric ciphers . DES, AES . Asymmetric ciphers . RSA . Next class: Protocols Example Ciphers . Shift cipher: each plaintext characters is replaced by a character k to the right. (When k=3, it’s a Caesar cipher). “Watch out for Brutus!” => “Jngpu bhg sbe Oehghf!” . Only 25 choices! Not hard to break by brute force. Substitution Cipher: each character in plaintext is replaced by a corresponding character of ciphertext. E.g., cryptograms in newspapers. plaintext code: a b c d e f g h i f k l m n o p q r s t u v w x y z ciphertext code: m n b v c x z a s d f g h j k l p o i u y t r e w q . 26! Possible pairs. Is is really that hard to break? Substitution ciphers . The Caesar cipher has a small key space, but doesn’t create a statistical independence between the plaintext and the ciphertext. The best ciphers allow no statistical attacks, thereby forcing a brute force, exhaustive search; all the security lies with the key space. As cryptographic algorithms matured, the statistical independence between the plaintext and cipher text increased. Ciphers . The caesar cipher, hill cipher, and playfair cipher all work with a single alphabet for doing substitutions . They are monoalphabetic substitutions. A more complex (and more robust) alternative is to use different substitution mappings on various portions of the plaintext. Polyalphabetic substitutions. More ciphers . Vigenère cipher: each character of plaintext is encrypted with a different a cipher key. -

A Block Cipher Algorithm to Enhance the Avalanche Effect Using Dynamic Key- Dependent S-Box and Genetic Operations 1Balajee Maram and 2J.M
International Journal of Pure and Applied Mathematics Volume 119 No. 10 2018, 399-418 ISSN: 1311-8080 (printed version); ISSN: 1314-3395 (on-line version) url: http://www.ijpam.eu Special Issue ijpam.eu A Block Cipher Algorithm to Enhance the Avalanche Effect Using Dynamic Key- Dependent S-Box and Genetic Operations 1Balajee Maram and 2J.M. Gnanasekar 1Department of CSE, GMRIT, Rajam, India. Research and Development Centre, Bharathiar University, Coimbatore. [email protected] 2Department of Computer Science & Engineering, Sri Venkateswara College of Engineering, Sriperumbudur Tamil Nadu. [email protected] Abstract In digital data security, an encryption technique plays a vital role to convert digital data into intelligible form. In this paper, a light-weight S- box is generated that depends on Pseudo-Random-Number-Generators. According to shared-secret-key, all the Pseudo-Random-Numbers are scrambled and input to the S-box. The complexity of S-box generation is very simple. Here the plain-text is encrypted using Genetic Operations and S-box which is generated based on shared-secret-key. The proposed algorithm is experimentally investigates the complexity, quality and performance using the S-box parameters which includes Hamming Distance, Balanced Output and the characteristic of cryptography is Avalanche Effect. Finally the comparison results motivates that the dynamic key-dependent S-box has good quality and performance than existing algorithms. 399 International Journal of Pure and Applied Mathematics Special Issue Index Terms:S-BOX, data security, random number, cryptography, genetic operations. 400 International Journal of Pure and Applied Mathematics Special Issue 1. Introduction In public network, several types of attacks1 can be avoided by applying Data Encryption/Decryption2.