WRT54G2 User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Setting up the Linksys EA9300 Max-Stream AC4000 Tri-Band Wi-Fi Router
Setting up the Linksys EA9300 Max-Stream AC4000 Tri-Band Wi-Fi Router Setting up the Linksys EA9300 Max-Stream AC4000 Tri-Band Wi-Fi Router is made easy using the Smart Setup wizard which is embedded in the router's firmware and is available even if the router does not have an internet connection or the router is on factory default settings. Before you begin: Make sure you have a working internet connection. Power on your modem and connect an ethernet cable from the modem to the internet port of the router. NOTE: If you are replacing an existing router, make sure to disconnect and remove the old one. Connect the power adapter to the router and turn it ON. Wait until the Linksys logo light is solid. Step 1: Connect a wireless computer, tablet or smartphone to the default Wi-Fi network of your router. The wireless credentials are located on a label at the bottom of the device. NOTE: If you need to set up the router using a hardwired computer, connect your computer to one of the ethernet ports at the back of the router. Step 2: Launch a supported web browser and enter “linksyssmartwifi.com” in the Address bar then press [Enter]. NOTE: You can also enter “http://192.168.1.1” or “myrouter.local”. Step 3: Check the box beside I have read and accepted the License Terms for using this software. Then click Next to proceed. NOTE: Open the link to know the license terms and other information. If you prefer to manually set up the router, click on the Manual configuration link. -
Frequently Asked Questions
User Guide E-Series Routers Linksys E-Series Table of Contents Table of Contents Product overview Wireless Security E900/E1200/E1500/E2500/E3200 1 Wireless > Wireless Security 8 Back view 1 Personal options 8 Bottom view 1 Office options 8 E4200 2 Option settings 8 Top view 2 Back view 2 Troubleshooting Setting Up Your E-Series Router How to run Linksys Connect after setup 11 Your router was not successfully set up 12 Where to find more help 3 Get Windows XP Service Pack 3 message 12 How to set up your router 3 Your Internet cable is not plugged in message 13 How to start Linksys Connect 3 Use Linksys Connect to manage your router 3 Cannot access your router message 14 How to manually set up your router 3 Device not found message 15 Advanced Configuration Specifications How to open the browser-based utility 4 Linksys E900 17 Setup > Basic Setup 5 Linksys E1200 18 Language 5 Linksys E1500 19 Internet Setup 5 Linksys E2500 20 Wireless > Basic Wireless Settings 6 Wireless Settings 6 Linksys E3200 21 Linksys E4200 22 i Linksys E-Series Product overview • Power indicator—Stays on steadily while power is connected and Product overview following a successful Wi-Fi Protected Setup connection Flashes slowly during bootup, during firmware upgrades, and during a Wi-Fi Protected Setup connection Flashes quickly when there is a Wi-Fi Protected Setup error • Power—Connect the included AC power adapter to this port E900/E1200/E1500/E2500/E3200 CAUTION Use only the adapter that came with your router Back view • Power button—Press | (on) to turn on the -
Integrity Enhancements for Embedded Linux Devices
Integrity Enhancements for Embedded Linux Devices David Safford [email protected] This material is based on research sponsored by the Department of Homeland Security (DHS) Science and Technology Directorate, Homeland Security Advanced Research Projects Agency, Cyber Security Division (DHS S&T/HSARPA/CSD), BAA 11-02 and Air Force Research Laboratory, Information Directorate under agreement number FA8750-12-2-0243. The U.S. Government is authorized to reproduce and distribute reprints for Governmental purposes notwithstanding any copyright notation thereon. The views and conclusions contained herein are those of the authors and should not be interpreted as necessarily representing the official policies or endorsements, either expressed or implied, of Department of Homeland Security, Air Force Research Laboratory or the U.S. Government. Embedded Linux Integrity ● Server $10K+ PB 4768 Crypto card Trusted and Secure Boot ● PC $1K TB TPM Trusted and Secure Boot (Win8) ● mobile $500 GB Restricted Boot ● embedded $50 MB Nothing ● Sensor $10 KB Nothing Example Embedded Linux Devices ● Pogoplug ● TP-Link MR3020 ● D-Link DIR-505 ● Linksys WRT54G MR-3020 Main Components Three main chips SoC (32 bit MIPS) RAM (32MB) SPI Flash (4MB) Partition Name Size Contents mtd0 “boot” 64KB u-boot mtd1 “kernel” 1024KB Linux Kernel mtd2 “rootfs” 2816KB Linux root filesystem mtd3 “config” 64KB config data mtd4 “ART” 64KB radio config data Recent Embedded Linux Vulnerabilities ● 2012: 4.5 Million home routers compromised in Brazil – https://www.securelist.com/en/blog/208193852/The_tale_of_one_thousand -

WRT310N Wireless-N Gigabit Router
USER GUIDE Wireless-N Gigabit Router Model: WRT310N About This Guide About This Guide Icon Descriptions While reading through the User Guide you may see various icons that call attention to specific items. Below is a description of these icons: NOTE: This check mark indicates that there is a note of interest and is something that you should pay special attention to while using the product. WARNING: This exclamation point indicates that there is a caution or warning and it is something that could damage your property or product. WEB: This globe icon indicates a noteworthy website address or e-mail address. Online Resources Website addresses in this document are listed without http:// in front of the address because most current web browsers do not require it. If you use an older web browser, you may have to add http:// in front of the web address. Resource Website Linksys www.linksys.com Linksys International www.linksys.com/international Glossary www.linksys.com/glossary Network Security www.linksys.com/security Copyright and Trademarks Linksys is a registered trademark or trademark of Cisco Systems, Inc. and/or its affiliates in the U.S. and certain other countries. Copyright © 2008 Cisco Systems, Inc. All rights reserved. Other brands and product names are trademarks or registered trademarks of their respective holders. Wireless-N Gigabit Router i Table of Contents Chapter 1: Product Overview 4 Front Panel. 4 Back Panel . 4 Placement Positions . 4 Chapter 2: Wireless Security Checklist 6 General Network Security Guidelines . 6 Additional Security Tips . 6 Chapter 3: Advanced Configuration 7 Setup > Basic Setup . -

Network PC Card
Instant WirelessTM Series Network PC Card Use this Guide to install the following: WPC11 V2.5 User Guide COPYRIGHT & TRADEMARKS Copyright © 2001 Linksys, All Rights Reserved. Instant Wireless™ is a registered trade- mark of Linksys. Microsoft, Windows, and the Windows logo are registered trademarks of Microsoft Corporation. All other trademarks and brand names are the property of their respective proprietors. LIMITED WARRANTY Linksys guarantees that every Instant Wireless™ Network PC Card V2.5 is free from phys- ical defects in material and workmanship under normal use for one year from the date of purchase. If these products prove defective during this warranty period, call Linksys Customer Support in order to obtain a Return Authorization Number. BE SURE TO HAVE YOUR PROOF OF PURCHASE AND A BARCODE FROM THE PRODUCT’S PACKAGING ON HAND WHEN CALLING. RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF PURCHASE. When returning a product, mark the Return Authorization Number clearly on the outside of the package and include your original proof of pur- chase. All customers located outside of the United States of America and Canada shall be held responsible for shipping and handling charges. IN NO EVENT SHALL LINKSYS’ LIABILITY EXCEED THE PRICE PAID FOR THE PROD- UCT FROM DIRECT, INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAM- AGES RESULTING FROM THE USE OF THE PRODUCT, ITS ACCOMPANYING SOFT- WARE, OR ITS DOCUMENTATION. LINKSYS DOES NOT OFFER REFUNDS FOR ANY PRODUCT. Linksys makes no warranty or representation, expressed, implied, or statuto- ry, with respect to its products or the contents or use of this documentation and all accompanying software, and specifically disclaims its quality, performance, mer- chantability, or fitness for any particular purpose. -
Hacking Roomba®
Hacking Roomba® Tod E. Kurt Wiley Publishing, Inc. Hacking Roomba® Published by Wiley Publishing, Inc. 10475 Crosspoint Boulevard Indianapolis, IN 46256 www.wiley.com Copyright © 2007 by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada ISBN-13: 978-0-470-07271-4 ISBN-10: 0-470-07271-7 Manufactured in the United States of America 10 9 8 7 6 5 4 3 2 1 No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, or online at http://www.wiley.com/go/permissions. Limit of Liability/Disclaimer of Warranty: The publisher and the author make no representations or warranties with respect to the accuracy or completeness of the contents of this work and specifically disclaim all warranties, including without limitation warranties of fitness for a particular purpose. No warranty may be created or extended by sales or promotional materials. The advice and strategies contained herein may not be suitable for every situation. This work is sold with the understanding that the publisher is not engaged in rendering legal, accounting, or other professional services. -

USER GUIDE R75 Model EA7500/EA7500S Contents
USER GUIDE R75 Model EA7500/EA7500S Contents Product Overview .........................................................................................................3 Top ....................................................................................................................................................................... 3 Back ..................................................................................................................................................................... 4 Setting Up: Basics ........................................................................................................5 Where to find more help ............................................................................................................................... 5 How to install your router ............................................................................................................................ 6 www.LinksysSmartWiFi.com ....................................................................................9 How to log in to www.LinksysSmartWiFi.com ...................................................................................... 9 Network Map ................................................................................................................................................. 11 Guest Access ................................................................................................................................................ 11 Parental Controls........................................................................................................................................ -

C:\Users\John\Documents\Forums
Network speed between a given system adapter and the network Router is determined by the slowest network device. If the Router is an N Router, then your adapter mode is set for G. The problem is likely your Intel AGN Adapter settings - it's Wireless Mode is likely set to G, B/G, or A/B/G, but the N Mode setting probably isn't Enabled, which overrides the other Wireless Modes. Prior to the procedures below, go to Linksys Support, look up your Router, then download the latest firmware update. If it's the same as what you have, then download that. Linksys Support Standard Procedure for any Linksys Router problem with speed or signal begins with flashing the firmware prior to adjusting any other settings. I've added settings for your Router to match your adapter since I have the same hardware. You can look for your Router's firmware update at Linksys Support Enter your Model # and go from there to get the firmware update. The following assumes you have a Linksys Single Band N Router; though these settings are from my Linksys WRT600N Dual-Band, the Admin Panel is the same, except for the extra 5ghz Band setup on mine. Just in case, I've also added the 5ghz settings. With these settings and the AGN or my Linksys WUSB600N DBN Adapter, I average better than 200mbps+, usually around 240 or 260mbps. The settings for the AGN adapter after these settings are matched for the Router settings. On your Router: Access the Router Admin Panel & Wireless Settings from your Browser - http://192.168.1.1/BasicWirelessSettings.htm 1. -
Wireless-G Broadband Router WIRELESS User Guide
GHz 2,4802.11g Wireless-G Broadband Router WIRELESS User Guide Model No. WRT54G (EU/LA) Wireless-G Broadband Router Copyright and Trademarks Specifications are subject to change without notice. Linksys is a registered trademark or trademark of Cisco Systems, Inc. and/or its affiliates in the U.S. and certain other countries. Copyright © 2006 Cisco Systems, Inc. All rights reserved. Other brands and product names are trademarks or registered trademarks of their respective holders. How to Use This User Guide This User Guide has been designed to make understanding networking with the Wireless-G Broadband Router easier than ever. Look for the following items when reading this User Guide: This checkmark means there is a note of interest and is something you should pay special attention to while using the Wireless-G Broadband Router. This exclamation point means there is a caution or warning and is something that could damage your property or the Wireless-G Broadband Router. This question mark provides you with a reminder about something you might need to do while using the Wireless-G Broadband Router. In addition to these symbols, there are definitions for technical terms that are presented like this: word: definition. Also, each figure (diagram, screenshot, or other image) is provided with a figure number and description, like this: Figure 0-1: Sample Figure Description Figure numbers and descriptions can also be found in the “List of Figures” section in the “Table of Contents”. WRT54GV7-EU-UG-60307 BW Wireless-G Broadband Router Table of -
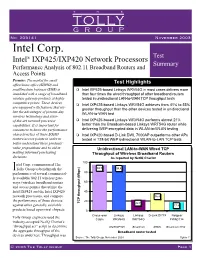
Intel Corp IXP425/IXP420 Network Processors
TH E TOLLY GROUP No. 203141 November 2003 Intel Corp. Test Intel® IXP425/IXP420 Network Processors Summary Performance Analysis of 802.11 Broadband Routers and Access Points Premise: The market for small Test Highlights office/home office (SOHO) and small/medium business (SMB) is Intel IXP425-based Linksys WRV54G in most cases delivers more inundated with a range of broadband than four times the wired throughput of other broadband routers wireless gateway products at highly tested in unidirectional LAN-to-WAN TCP throughput tests competitive prices. These devices Intel IXP425-based Linksys WRV54G achieves from 41% to 55% are equipped with features that uti- greater throughput than the other devices tested in unidirectional lize the advantages of present-day WLAN-to-WAN test wireless technology and state- of-the-art network processor Intel IXP425-based Linksys WRV54G performs almost 21% capabilities. It is important for better than the Broadcom-based Linksys WRT54G router while consumers to know the performance delivering WEP-encrypted data in WLAN-to-WLAN testing characteristics of these SOHO Intel IXP420-based D-Link DWL 7000AP outperforms other APs routers/access points in order to tested in 128-bit WEP bidirectional WLAN-to-LAN TCP tests better understand these products’ value propositions and to aid in Unidirectional LAN-to-WAN Wired TCP making informed purchasing Throughput of Wireless Broadband Routers decisions. As reported by NetIQ Chariot 100 ntel Corp. commissioned The ITolly Group to benchmark the 94.7 94.4 performance of several commercial- 80 ly available 802.11 wireless gate- ways (wireless broadband routers 60 and access points) that utilize the Intel IXP425 and the Intel IXP420 40 network processors, and compare 36.4 the performance of those devices 20 TCP throughput (Mbps) 22.7 against other generally available 17.8 products based upon rival chipsets. -
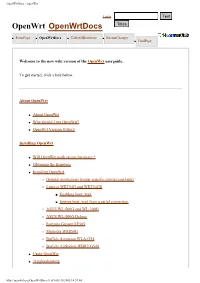
Openwrtdocs - Openwrt
OpenWrtDocs - OpenWrt Login OpenWrt OpenWrtDocs ● FrontPage ● OpenWrtDocs ● TableOfHardware ● RecentChanges ● FindPage Welcome to the new wiki version of the OpenWrt userguide. To get started, click a link below. About OpenWrt ● About OpenWrt ● Why should I run OpenWrt? ● OpenWrt Version History Installing OpenWrt ● Will OpenWrt work on my hardware ? ● Obtaining the firmware ● Installing OpenWrt ❍ General instructions (router specific instructions later) ❍ Linksys WRT54G and WRT54GS ■ Enabling boot_wait ■ Setting boot_wait from a serial connection ❍ ASUS WL-500G and WL-300G ❍ ASUS WL-500G Deluxe ❍ Siemens Gigaset SE505 ❍ Motorola WR850G ❍ Buffalo Airstation WLA-G54 ❍ Buffalo AirStation WBR2-G54S ● Using OpenWrt ● Troubleshooting http://openwrt.org/OpenWrtDocs (1 of 6)18.10.2005 14:57:04 OpenWrtDocs - OpenWrt Using OpenWrt ● Using OpenWrt for the first time ● Firstboot / jffs2 ● Editing Files ● ipkg ● Configuration OpenWrt Configuration ● NVRAM ● Network configuration ❍ Sample network configurations ❍ The ethernet switch ■ Normal Behavior ■ Using Robocfg ● Wireless configuration ❍ Basic settings ❍ WEP encryption ❍ WPA encryption ❍ Wireless Distribution System (WDS) / Repeater / Bridge ❍ OpenWrt as client / wireless bridge ● Software configuration ❍ System ■ dnsmasq ■ nas ■ wl ■ TimeZone and NTP ■ Crontab ■ PPPoE Internet Connection ■ Access to syslog ❍ Applications ■ httpd ■ socks-Proxy http://openwrt.org/OpenWrtDocs (2 of 6)18.10.2005 14:57:04 OpenWrtDocs - OpenWrt ■ uPnP ■ CUPS - Printing system with spooling ● Hardware ❍ LED OpenWrt -

216155 October 2016 Commissioned by Linksys, Inc
#216155 October 2016 Commissioned by Linksys, Inc. Linksys EA7300 Max-Stream AC1750 MU-MIMO Gigabit Router Comparative Wireless LAN Performance EXECUTIVE SUMMARY Busy home networks are now the rule rather than the exception with multiple THE BOTTOM LINE clients demanding multiple high-bandwidth services - like video streaming - Linksys EA7300 Max-Stream AC1750 MU-MIMO simultaneously. Multi-user MIMO (MU-MIMO) technology can deliver Gigabit Router provides: significantly more throughput to multiple users than the prior generation single-user MIMO (SU-MIMO). The Linksys EA7300 Max-Stream AC1750 MU- Up to 3.5X greater aggregate throughput in line-of- MIMO Gigabit Router is a home entertainment Wi-Fi router optimized for online 1 sight tests gaming and streaming. Linksys, Inc. commissioned Tolly to benchmark the throughput of the Linksys Up to 3.5X greater per client average throughput in 2 EA7300 and compare that to the aggregate throughput of several competing line-of-sight tests dual-band, AC1750 wireless LAN (WLAN) solutions. The Linksys solution can deliver up to 3.5X the multi-client, aggregate throughput of competing Up to 4.4X greater individual client average 3 solutions. See Figure 1. ...<continued on next page> throughput in long distance tests Wireless LAN MU-MIMO Multi-Client Downstream Performance Four Clients, Line-of-Sight Aggregate Throughput, (as reported by Ixia IxChariot v7.10 SP3) 600 500 Linksys MU-MIMO delivers up to 3.5X greater aggregate throughput. 400 300 200 Throughput (Mbps) 100 0 Solution Under Test Linksys EA7300 ASUS RT-AC66U NETGEAR R6400 TP-LINK Archer C7 TP-LINK Archer C8 Notes: Dual-band devices provide a 2.4GHz radio and a 5GHz radio.