University of California, San Diego
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Supplementary Table S4. FGA Co-Expressed Gene List in LUAD
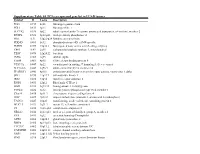
Supplementary Table S4. FGA co-expressed gene list in LUAD tumors Symbol R Locus Description FGG 0.919 4q28 fibrinogen gamma chain FGL1 0.635 8p22 fibrinogen-like 1 SLC7A2 0.536 8p22 solute carrier family 7 (cationic amino acid transporter, y+ system), member 2 DUSP4 0.521 8p12-p11 dual specificity phosphatase 4 HAL 0.51 12q22-q24.1histidine ammonia-lyase PDE4D 0.499 5q12 phosphodiesterase 4D, cAMP-specific FURIN 0.497 15q26.1 furin (paired basic amino acid cleaving enzyme) CPS1 0.49 2q35 carbamoyl-phosphate synthase 1, mitochondrial TESC 0.478 12q24.22 tescalcin INHA 0.465 2q35 inhibin, alpha S100P 0.461 4p16 S100 calcium binding protein P VPS37A 0.447 8p22 vacuolar protein sorting 37 homolog A (S. cerevisiae) SLC16A14 0.447 2q36.3 solute carrier family 16, member 14 PPARGC1A 0.443 4p15.1 peroxisome proliferator-activated receptor gamma, coactivator 1 alpha SIK1 0.435 21q22.3 salt-inducible kinase 1 IRS2 0.434 13q34 insulin receptor substrate 2 RND1 0.433 12q12 Rho family GTPase 1 HGD 0.433 3q13.33 homogentisate 1,2-dioxygenase PTP4A1 0.432 6q12 protein tyrosine phosphatase type IVA, member 1 C8orf4 0.428 8p11.2 chromosome 8 open reading frame 4 DDC 0.427 7p12.2 dopa decarboxylase (aromatic L-amino acid decarboxylase) TACC2 0.427 10q26 transforming, acidic coiled-coil containing protein 2 MUC13 0.422 3q21.2 mucin 13, cell surface associated C5 0.412 9q33-q34 complement component 5 NR4A2 0.412 2q22-q23 nuclear receptor subfamily 4, group A, member 2 EYS 0.411 6q12 eyes shut homolog (Drosophila) GPX2 0.406 14q24.1 glutathione peroxidase -

Estrogen's Impact on the Specialized Transcriptome, Brain, and Vocal
Estrogen’s Impact on the Specialized Transcriptome, Brain, and Vocal Learning Behavior of a Sexually Dimorphic Songbird by Ha Na Choe Department of Molecular Genetics & Microbiology Duke University Date:_____________________ Approved: ___________________________ Erich D. Jarvis, Supervisor ___________________________ Hiroaki Matsunami ___________________________ Debra Silver ___________________________ Dong Yan ___________________________ Gregory Crawford Dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in the Department of Molecular Genetics & Microbiology in the Graduate School of Duke University 2020 ABSTRACT Estrogen’s Impact on the Specialized Transcriptome, Brain, and Vocal Learning Behavior of a Sexually Dimorphic Songbird by Ha Na Choe Department of Molecular Genetics & Microbiology Duke University Date:_________________________ Approved: ___________________________ Erich D. Jarvis, Supervisor ___________________________ Hiroaki Matsunami ___________________________ Debra Silver ___________________________ Dong Yan ___________________________ Gregory Crawford Dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in the Department of Molecular Genetics & Microbiology in the Graduate School of Duke University 2020 Copyright by Ha Na Choe 2020 Abstract The song system of the zebra finch (Taeniopygia guttata) is highly sexually dimorphic, where only males develop the neural structures necessary to learn and produce learned vocalizations -

Examining the Effects of Endogenous Sex Steroids and the Xenoestrogen Contaminant 17-Ethinylestradiol on Previtellogenic Coho Salmon Ovarian Growth and Function
Examining the effects of endogenous sex steroids and the xenoestrogen contaminant 17-ethinylestradiol on previtellogenic coho salmon ovarian growth and function Christopher A. Monson A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy University of Washington 2018 Reading committee: Dr. Graham Young, Chair Dr. Penny Swanson Dr. Steven Roberts Program authorized to offer degree: Aquatic and Fishery Sciences ©Copyright 2018 Christopher A. Monson University of Washington Abstract Examining the effects of endogenous sex steroids and the xenoestrogen contaminant 17α- ethinylestradiol on previtellogenic coho salmon ovarian growth and function. Christopher A. Monson Chair of Supervisory Committee: Professor Graham Young School of Aquatic and Fishery Sciences In teleost fish, as in other oviparous vertebrates, the production of a fertilizable egg is a complex process driven by the specific spatiotemporal coordination of endocrine and paracrine factors in multiple tissues. Across the brain-pituitary-ovary-liver (BPOL) axis, this includes the synthesis and release of pituitary gonadrotopins, the ovarian production and release of sex steroids, and the hepatic synthesis and release of egg yolk protein precursors, as well as numerous factors that mediate these processes. The factors controlling the earliest stages of oogenesis, the loading of yolk proteins (vitellogenesis), and the final maturational stage are fairly well understood, but the control of the intermediate growth stages (primary and early secondary growth) and the developmental point analogous to the onset of mammalian puberty, the transition from primary to secondary growth, are less clear. The research described in this dissertation addresses the regulation of the ovarian transcriptome by sex steroids during the primary and early secondary growth stages in coho salmon (Oncorhynchus kisutch), and the potential disruption of normal ovarian processes during early secondary growth by a potent synthetic steroidal xenoestrogen. -

In-Silico Guided Identification of Ciliogenesis Candidate Genes in a Non-Conventional Animal Model
Iowa State University Capstones, Theses and Graduate Theses and Dissertations Dissertations 2019 In-silico guided identification of ciliogenesis candidate genes in a non-conventional animal model Natalia I. Acevedo Luna Iowa State University Follow this and additional works at: https://lib.dr.iastate.edu/etd Part of the Bioinformatics Commons Recommended Citation Acevedo Luna, Natalia I., "In-silico guided identification of ciliogenesis candidate genes in a non- conventional animal model" (2019). Graduate Theses and Dissertations. 17382. https://lib.dr.iastate.edu/etd/17382 This Dissertation is brought to you for free and open access by the Iowa State University Capstones, Theses and Dissertations at Iowa State University Digital Repository. It has been accepted for inclusion in Graduate Theses and Dissertations by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. In-silico guided identification of ciliogenesis candidate genes in a non-conventional animal model by Natalia Acevedo Luna A dissertation submitted to the graduate faculty in partial fulfillment of the requirements for the degree of DOCTOR OF PHILOSOPHY Major: Bioinformatics and Computational Biology Program of Study Committee: Heike Hofmann, Co-major Professor Geetu Tuteja, Co-major Professor Matthew Hufford Dennis V. Lavrov Mohan Gupta The student author, whose presentation of the scholarship herein was approved by the program of study committee, is solely responsible for the content of this dissertation. The Graduate College will ensure this dissertation is globally accessible and will not permit alterations after a degree is conferred. Iowa State University Ames, Iowa 2019 ii DEDICATION This dissertation would never have been possible without the support and love of the wonderful people I have the honor of calling my family, they are my core and my every- thing.