The Weakness of CTC Qubits and the Power of Approximate Counting
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Complexity Theory Lecture 9 Co-NP Co-NP-Complete
Complexity Theory 1 Complexity Theory 2 co-NP Complexity Theory Lecture 9 As co-NP is the collection of complements of languages in NP, and P is closed under complementation, co-NP can also be characterised as the collection of languages of the form: ′ L = x y y <p( x ) R (x, y) { |∀ | | | | → } Anuj Dawar University of Cambridge Computer Laboratory NP – the collection of languages with succinct certificates of Easter Term 2010 membership. co-NP – the collection of languages with succinct certificates of http://www.cl.cam.ac.uk/teaching/0910/Complexity/ disqualification. Anuj Dawar May 14, 2010 Anuj Dawar May 14, 2010 Complexity Theory 3 Complexity Theory 4 NP co-NP co-NP-complete P VAL – the collection of Boolean expressions that are valid is co-NP-complete. Any language L that is the complement of an NP-complete language is co-NP-complete. Any of the situations is consistent with our present state of ¯ knowledge: Any reduction of a language L1 to L2 is also a reduction of L1–the complement of L1–to L¯2–the complement of L2. P = NP = co-NP • There is an easy reduction from the complement of SAT to VAL, P = NP co-NP = NP = co-NP • ∩ namely the map that takes an expression to its negation. P = NP co-NP = NP = co-NP • ∩ VAL P P = NP = co-NP ∈ ⇒ P = NP co-NP = NP = co-NP • ∩ VAL NP NP = co-NP ∈ ⇒ Anuj Dawar May 14, 2010 Anuj Dawar May 14, 2010 Complexity Theory 5 Complexity Theory 6 Prime Numbers Primality Consider the decision problem PRIME: Another way of putting this is that Composite is in NP. -

EXPSPACE-Hardness of Behavioural Equivalences of Succinct One
EXPSPACE-hardness of behavioural equivalences of succinct one-counter nets Petr Janˇcar1 Petr Osiˇcka1 Zdenˇek Sawa2 1Dept of Comp. Sci., Faculty of Science, Palack´yUniv. Olomouc, Czech Rep. [email protected], [email protected] 2Dept of Comp. Sci., FEI, Techn. Univ. Ostrava, Czech Rep. [email protected] Abstract We note that the remarkable EXPSPACE-hardness result in [G¨oller, Haase, Ouaknine, Worrell, ICALP 2010] ([GHOW10] for short) allows us to answer an open complexity ques- tion for simulation preorder of succinct one counter nets (i.e., one counter automata with no zero tests where counter increments and decrements are integers written in binary). This problem, as well as bisimulation equivalence, turn out to be EXPSPACE-complete. The technique of [GHOW10] was referred to by Hunter [RP 2015] for deriving EXPSPACE-hardness of reachability games on succinct one-counter nets. We first give a direct self-contained EXPSPACE-hardness proof for such reachability games (by adjust- ing a known PSPACE-hardness proof for emptiness of alternating finite automata with one-letter alphabet); then we reduce reachability games to (bi)simulation games by using a standard “defender-choice” technique. 1 Introduction arXiv:1801.01073v1 [cs.LO] 3 Jan 2018 We concentrate on our contribution, without giving a broader overview of the area here. A remarkable result by G¨oller, Haase, Ouaknine, Worrell [2] shows that model checking a fixed CTL formula on succinct one-counter automata (where counter increments and decre- ments are integers written in binary) is EXPSPACE-hard. Their proof is interesting and nontrivial, and uses two involved results from complexity theory. -

Dspace 6.X Documentation
DSpace 6.x Documentation DSpace 6.x Documentation Author: The DSpace Developer Team Date: 27 June 2018 URL: https://wiki.duraspace.org/display/DSDOC6x Page 1 of 924 DSpace 6.x Documentation Table of Contents 1 Introduction ___________________________________________________________________________ 7 1.1 Release Notes ____________________________________________________________________ 8 1.1.1 6.3 Release Notes ___________________________________________________________ 8 1.1.2 6.2 Release Notes __________________________________________________________ 11 1.1.3 6.1 Release Notes _________________________________________________________ 12 1.1.4 6.0 Release Notes __________________________________________________________ 14 1.2 Functional Overview _______________________________________________________________ 22 1.2.1 Online access to your digital assets ____________________________________________ 23 1.2.2 Metadata Management ______________________________________________________ 25 1.2.3 Licensing _________________________________________________________________ 27 1.2.4 Persistent URLs and Identifiers _______________________________________________ 28 1.2.5 Getting content into DSpace __________________________________________________ 30 1.2.6 Getting content out of DSpace ________________________________________________ 33 1.2.7 User Management __________________________________________________________ 35 1.2.8 Access Control ____________________________________________________________ 36 1.2.9 Usage Metrics _____________________________________________________________ -

The Complexity Zoo
The Complexity Zoo Scott Aaronson www.ScottAaronson.com LATEX Translation by Chris Bourke [email protected] 417 classes and counting 1 Contents 1 About This Document 3 2 Introductory Essay 4 2.1 Recommended Further Reading ......................... 4 2.2 Other Theory Compendia ............................ 5 2.3 Errors? ....................................... 5 3 Pronunciation Guide 6 4 Complexity Classes 10 5 Special Zoo Exhibit: Classes of Quantum States and Probability Distribu- tions 110 6 Acknowledgements 116 7 Bibliography 117 2 1 About This Document What is this? Well its a PDF version of the website www.ComplexityZoo.com typeset in LATEX using the complexity package. Well, what’s that? The original Complexity Zoo is a website created by Scott Aaronson which contains a (more or less) comprehensive list of Complexity Classes studied in the area of theoretical computer science known as Computa- tional Complexity. I took on the (mostly painless, thank god for regular expressions) task of translating the Zoo’s HTML code to LATEX for two reasons. First, as a regular Zoo patron, I thought, “what better way to honor such an endeavor than to spruce up the cages a bit and typeset them all in beautiful LATEX.” Second, I thought it would be a perfect project to develop complexity, a LATEX pack- age I’ve created that defines commands to typeset (almost) all of the complexity classes you’ll find here (along with some handy options that allow you to conveniently change the fonts with a single option parameters). To get the package, visit my own home page at http://www.cse.unl.edu/~cbourke/. -

The Polynomial Hierarchy
ij 'I '""T', :J[_ ';(" THE POLYNOMIAL HIERARCHY Although the complexity classes we shall study now are in one sense byproducts of our definition of NP, they have a remarkable life of their own. 17.1 OPTIMIZATION PROBLEMS Optimization problems have not been classified in a satisfactory way within the theory of P and NP; it is these problems that motivate the immediate extensions of this theory beyond NP. Let us take the traveling salesman problem as our working example. In the problem TSP we are given the distance matrix of a set of cities; we want to find the shortest tour of the cities. We have studied the complexity of the TSP within the framework of P and NP only indirectly: We defined the decision version TSP (D), and proved it NP-complete (corollary to Theorem 9.7). For the purpose of understanding better the complexity of the traveling salesman problem, we now introduce two more variants. EXACT TSP: Given a distance matrix and an integer B, is the length of the shortest tour equal to B? Also, TSP COST: Given a distance matrix, compute the length of the shortest tour. The four variants can be ordered in "increasing complexity" as follows: TSP (D); EXACTTSP; TSP COST; TSP. Each problem in this progression can be reduced to the next. For the last three problems this is trivial; for the first two one has to notice that the reduction in 411 j ;1 17.1 Optimization Problems 413 I 412 Chapter 17: THE POLYNOMIALHIERARCHY the corollary to Theorem 9.7 proving that TSP (D) is NP-complete can be used with DP. -

Quantum Supremacy
Quantum Supremacy Practical QS: perform some computational task on a well-controlled quantum device, which cannot be simulated in a reasonable time by the best-known classical algorithms and hardware. Theoretical QS: perform a computational task efficiently on a quantum device, and prove that task cannot be efficiently classically simulated. Since proving seems to be beyond the capabilities of our current civilization, we lower the standards for theoretical QS. One seeks to provide formal evidence that classical simulation is unlikely. For example: 3-SAT is NP-complete, so it cannot be efficiently classical solved unless P = NP. Theoretical QS: perform a computational task efficiently on a quantum device, and prove that task cannot be efficiently classically simulated unless “the polynomial Heierarchy collapses to the 3nd level.” Quantum Supremacy A common feature of QS arguments is that they consider sampling problems, rather than decision problems. They allow us to characterize the complexity of sampling measurements of quantum states. Which is more difficult: Task A: deciding if a circuit outputs 1 with probability at least 2/3s, or at most 1/3s Task B: sampling from the output of an n-qubit circuit in the computational basis Sampling from distributions is generically more difficult than approximating observables, since we can use samples to estimate observables, but not the other way around. One can imagine quantum systems whose local observables are easy to classically compute, but for which sampling the full state is computationally complex. By moving from decision problems to sampling problems, we make the task of classical simulation much more difficult. -

Ex. 8 Complexity 1. by Savich Theorem NL ⊆ DSPACE (Log2n)
Ex. 8 Complexity 1. By Savich theorem NL ⊆ DSP ACE(log2n) ⊆ DSP ASE(n). we saw in one of the previous ex. that DSP ACE(n2f(n)) 6= DSP ACE(f(n)) we also saw NL ½ P SP ASE so we conclude NL ½ DSP ACE(n) ½ DSP ACE(n3) ½ P SP ACE but DSP ACE(n) 6= DSP ACE(n3) as needed. 2. (a) We emulate the running of the s ¡ t ¡ conn algorithm in parallel for two paths (that is, we maintain two pointers, both starts at s and guess separately the next step for each of them). We raise a flag as soon as the two pointers di®er. We stop updating each of the two pointers as soon as it gets to t. If both got to t and the flag is raised, we return true. (b) As A 2 NL by Immerman-Szelepsc¶enyi Theorem (NL = vo ¡ NL) we know that A 2 NL. As C = A \ s ¡ t ¡ conn and s ¡ t ¡ conn 2 NL we get that A 2 NL. 3. If L 2 NICE, then taking \quit" as reject we get an NP machine (when x2 = L we always reject) for L, and by taking \quit" as accept we get coNP machine for L (if x 2 L we always reject), and so NICE ⊆ NP \ coNP . For the other direction, if L is in NP \coNP , then there is one NP machine M1(x; y) solving L, and another NP machine M2(x; z) solving coL. We can therefore de¯ne a new machine that guesses the guess y for M1, and the guess z for M2. -

Glossary of Complexity Classes
App endix A Glossary of Complexity Classes Summary This glossary includes selfcontained denitions of most complexity classes mentioned in the b o ok Needless to say the glossary oers a very minimal discussion of these classes and the reader is re ferred to the main text for further discussion The items are organized by topics rather than by alphab etic order Sp ecically the glossary is partitioned into two parts dealing separately with complexity classes that are dened in terms of algorithms and their resources ie time and space complexity of Turing machines and complexity classes de ned in terms of nonuniform circuits and referring to their size and depth The algorithmic classes include timecomplexity based classes such as P NP coNP BPP RP coRP PH E EXP and NEXP and the space complexity classes L NL RL and P S P AC E The non k uniform classes include the circuit classes P p oly as well as NC and k AC Denitions and basic results regarding many other complexity classes are available at the constantly evolving Complexity Zoo A Preliminaries Complexity classes are sets of computational problems where each class contains problems that can b e solved with sp ecic computational resources To dene a complexity class one sp ecies a mo del of computation a complexity measure like time or space which is always measured as a function of the input length and a b ound on the complexity of problems in the class We follow the tradition of fo cusing on decision problems but refer to these problems using the terminology of promise problems -
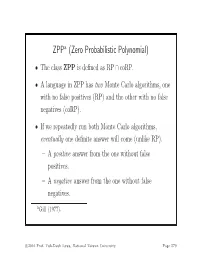
ZPP (Zero Probabilistic Polynomial)
ZPPa (Zero Probabilistic Polynomial) • The class ZPP is defined as RP ∩ coRP. • A language in ZPP has two Monte Carlo algorithms, one with no false positives (RP) and the other with no false negatives (coRP). • If we repeatedly run both Monte Carlo algorithms, eventually one definite answer will come (unlike RP). – A positive answer from the one without false positives. – A negative answer from the one without false negatives. aGill (1977). c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 579 The ZPP Algorithm (Las Vegas) 1: {Suppose L ∈ ZPP.} 2: {N1 has no false positives, and N2 has no false negatives.} 3: while true do 4: if N1(x)=“yes”then 5: return “yes”; 6: end if 7: if N2(x) = “no” then 8: return “no”; 9: end if 10: end while c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 580 ZPP (concluded) • The expected running time for the correct answer to emerge is polynomial. – The probability that a run of the 2 algorithms does not generate a definite answer is 0.5 (why?). – Let p(n) be the running time of each run of the while-loop. – The expected running time for a definite answer is ∞ 0.5iip(n)=2p(n). i=1 • Essentially, ZPP is the class of problems that can be solved, without errors, in expected polynomial time. c 2016 Prof. Yuh-Dauh Lyuu, National Taiwan University Page 581 Large Deviations • Suppose you have a biased coin. • One side has probability 0.5+ to appear and the other 0.5 − ,forsome0<<0.5. -

Independence of P Vs. NP in Regards to Oracle Relativizations. · 3 Then
Independence of P vs. NP in regards to oracle relativizations. JERRALD MEEK This is the third article in a series of four articles dealing with the P vs. NP question. The purpose of this work is to demonstrate that the methods used in the first two articles of this series are not affected by oracle relativizations. Furthermore, the solution to the P vs. NP problem is actually independent of oracle relativizations. Categories and Subject Descriptors: F.2.0 [Analysis of Algorithms and Problem Complex- ity]: General General Terms: Algorithms, Theory Additional Key Words and Phrases: P vs NP, Oracle Machine 1. INTRODUCTION. Previously in “P is a proper subset of NP” [Meek Article 1 2008] and “Analysis of the Deterministic Polynomial Time Solvability of the 0-1-Knapsack Problem” [Meek Article 2 2008] the present author has demonstrated that some NP-complete problems are likely to have no deterministic polynomial time solution. In this article the concepts of these previous works will be applied to the relativizations of the P vs. NP problem. It has previously been shown by Hartmanis and Hopcroft [1976], that the P vs. NP problem is independent of Zermelo-Fraenkel set theory. However, this same discovery had been shown by Baker [1979], who also demonstrates that if P = NP then the solution is incompatible with ZFC. The purpose of this article will be to demonstrate that the oracle relativizations of the P vs. NP problem do not preclude any solution to the original problem. This will be accomplished by constructing examples of five out of the six relativizing or- acles from Baker, Gill, and Solovay [1975], it will be demonstrated that inconsistent relativizations do not preclude a proof of P 6= NP or P = NP. -
On Beating the Hybrid Argument∗
THEORY OF COMPUTING, Volume 9 (26), 2013, pp. 809–843 www.theoryofcomputing.org On Beating the Hybrid Argument∗ Bill Fefferman† Ronen Shaltiel‡ Christopher Umans§ Emanuele Viola¶ Received February 23, 2012; Revised July 31, 2013; Published November 14, 2013 Abstract: The hybrid argument allows one to relate the distinguishability of a distribution (from uniform) to the predictability of individual bits given a prefix. The argument incurs a loss of a factor k equal to the bit-length of the distributions: e-distinguishability implies e=k-predictability. This paper studies the consequences of avoiding this loss—what we call “beating the hybrid argument”—and develops new proof techniques that circumvent the loss in certain natural settings. Our main results are: 1. We give an instantiation of the Nisan-Wigderson generator (JCSS 1994) that can be broken by quantum computers, and that is o(1)-unpredictable against AC0. We conjecture that this generator indeed fools AC0. Our conjecture implies the existence of an oracle relative to which BQP is not in the PH, a longstanding open problem. 2. We show that the “INW generator” by Impagliazzo, Nisan, and Wigderson (STOC’94) with seed length O(lognloglogn) produces a distribution that is 1=logn-unpredictable ∗An extended abstract of this paper appeared in the Proceedings of the 3rd Innovations in Theoretical Computer Science (ITCS) 2012. †Supported by IQI. ‡Supported by BSF grant 2010120, ISF grants 686/07,864/11 and ERC starting grant 279559. §Supported by NSF CCF-0846991, CCF-1116111 and BSF grant -

Non-Black-Box Techniques in Cryptography
Non-Black-Box Techniques in Cryptography Thesis for the Ph.D. Degree by Boaz Barak Under the Supervision of Professor Oded Goldreich Department of Computer Science and Applied Mathematics The Weizmann Institute of Science Submitted to the Feinberg Graduate School of the Weizmann Institute of Science Rehovot 76100, Israel January 6, 2004 To my darling Ravit Abstract The American Heritage dictionary defines the term “Black-Box” as “A device or theoretical construct with known or specified performance characteristics but unknown or unspecified constituents and means of operation.” In the context of Computer Science, to use a program as a black-box means to use only its input/output relation by executing the program on chosen inputs, without examining the actual code (i.e., representation as a sequence of symbols) of the program. Since learning properties of a program from its code is a notoriously hard problem, in most cases both in applied and theoretical computer science, only black-box techniques are used. In fact, there are specific cases in which it has been either proved (e.g., the Halting Problem) or is widely conjectured (e.g., the Satisfiability Problem) that there is no advantage for non-black-box techniques over black-box techniques. In this thesis, we consider several settings in cryptography, and ask whether there actually is an advantage in using non-black-box techniques over black-box techniques in these settings. Somewhat surprisingly, our answer is mainly positive. That is, we show that in several contexts in cryptog- raphy, there is a difference between the power of black-box and non-black-box techniques.