Global Threat Assessment 2019 Working Together to End the Sexual Exploitation of Children Online
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

2014 Festival Catalog
welcome For many years, we have worked together to build places for exploring the erotic, for meeting Eros, within ourselves and others. And we have seen the transformation that happens when people are allowed (encouraged) to encounter and Reveal true, authentic selves. We have built places that not only tolerate who we really are, but go further and accept who we are. And go further even, and celebrate our true essence. How can we know, really know, who we are if we keep so much hidden? How can we move freely, heartily through life while carrying the burdens of “unspeakable” secrets? We cannot fully love and profoundly affect our world, until we have met our real selves. And so, we offer Reveal as a promise and an invitation. Let us show you who we are, and perhaps you will reveal yourselves to us, too. We would be honored. Through art, let us reveal to you some possibilities. Let our artists lay a welcome mat; come explore–the light & dark, the soft & hard, the profane & profound. Stare, gawk, study, giggle. Stay as long as you dare, dare yourself to stay longer–past comfort, and back again. We bring you Seattle Erotic Art Festival to use as your bridge to authentic selves. Reveal. Because Eros’s love is in you, and we want you to know it. Through art, let us meet each other, and ourselves. With love and honor, Sophia Iannicelli and Leila Anasazi Seattle Erotic Art Festival 2014 ii juried exhibition juried exhibition The Festival is known worldwide for its comprehensive collection of international fine art celebrating the diversity of human sexual expression. -

Shari Cohn Sex Addiction Brochure
Shari Cohn Chat Rooms…Cybersex… Online Affairs… MSSW, LCSW, SC How many people CSAT-Certified Sex Cyber Romance… have problems with Addiction Therapist Internet Sex… Cybersex? Online Pornography… Helping Individuals, Estimates are that about 15% of people in the Couples and Families Recover United States - men and women - using the Harmless Fun? Or A Internet for sexual purposes have problems From Internet Serious Problem For You with their cybersex activities. Sex Addiction Or Someone You Know? About 9 million of these users are sexually • addicted and another 15 million use cybersex in Therapy for Internet Sex Addiction/Cybersex Addiction risky ways and show signs of compulsivity. • Therapy for Partners/Spouses and Some of these cybersex users were already Families of Sex Addicts having preexisting problems with sex addiction before they went on the Internet for sexual Research based, focused therapy helps purposes, but for others their Internet sexual people who are struggling with sexual activity was the first time they showed any addiction and compulsivity to develop the life Shari Cohn signs of sexual addiction. competencies to be successful in recovery. MSSW, LCSW, SC, CSAT Seventy percent of all Internet adult content Support and services for spouses/partners Certified Sex Addiction Therapist sites are visited during the 9-5 workday. and families of sex addicts are critical to assist healing from the negative Internet sex is very powerful and potentially consequences of sex addiction. very destructive. The comparison has been made that cybersex is like the crack cocaine of In my Certified Sex Addiction Therapist the Internet. training, I was taught by Dr. -

Gender-Based and Child Rights Analysis of Laws on Child Sexual Exploitation Benjamin Lawrence Patrick E
Gender-Based and Child Rights Analysis of Laws on Child Sexual Exploitation Benjamin Lawrence Patrick E. Aritao* John Stephen B. Pangilinan** I. INTRODUCTION .......................................................................... 353 II. ANALYSIS METHODOLOGY: GENDER-BASED ANALYSIS WITH CHILD PROTECTION FOCUS........................................................ 355 III. BEHAVIOR OF BOY AND GIRL VICTIMS OF SEXUAL ABUSE . 356 A. How Boys and Girls Differ in Responding to Sexual Abuse B. How Boys and Girls Differ in the Process of Recovering from Sexual Abuse C. How Boys and Girls Differ in Disclosing Their Stories of Sexual Abuse IV. O S E C CASEWORK IN THE PHILIPPINES ....................................... 369 V. GENDER ISSUES IN CSE AND OSEC CASEWORK ......................... 370 VI. P HILIPPINE LEGAL FRAMEWORK ................................................. 371 A. International Law B. Statutes and Their Implementing Rules and Regulations VII. ROLES AND RESPONSIBILITIES UNDER THE LEGAL FRAMEWORK ..............................................................................379 A. Law Enforcement B. Public and Private Aftercare Agencies C. Public Prosecutors D. Judiciary E. Non-Government Organizations VIII. SUPREME COURT CASES AND ISSUANCES ................................. 382 A. On the Credibility of a Child Witness B. On the Necessity of a Child Witness and the Procurement of Child Testimony C. Supreme Court Discussions of Gender Issues Surrounding Sexual Abuse D. On the Rights of an Abused Child to Have His or Her Abuser Suffer a Higher Penalty IX. GENDER ANALYSIS OF OSEC CASEWORK DATA ........................ 388 A. Victim Age: Younger Victims B. Victim Sex: Higher Number of Boy Victims C. Victim Relationship Data D. Law Enforcement Performance Data 2018] CHILD SEXUAL EXPLOITATION 353 E. Child-Protective Measures at the Inquest Phase F. Trial Lengths: Statistical Insights G. Insight form the Middle 50 % of the data range H. -

Alternative to What? the Rise of Loslyf Magazine Is My Own and That It Has Not Previously, in Its Entirety Or in Part, Been Submitted at Any University for a Degree
ALTERNATIVE TO WHAT? THE RISE OF LOSLYF MAGAZINE Marnell Kirsten Thesis presented in fulfilment of the requirements for the degree of Master of Visual Studies at Stellenbosch University Supervisor: Dr. Stella Viljoen April 2014 Stellenbosch University http://scholar.sun.ac.za I, the undersigned, hereby declare that the work contained in Alternative to what? The rise of Loslyf magazine is my own and that it has not previously, in its entirety or in part, been submitted at any university for a degree. All the sources that I have used or quoted have been indicated and acknowledged by means of complete references. Marnell Kirsten November 2013 Student number: 14353938 i Stellenbosch University http://scholar.sun.ac.za What is pornography to one man is the laughter of genius to another. - DH Lawrence (1936: 11) ii Stellenbosch University http://scholar.sun.ac.za SUMMARY In this study I analyse the first year of publication of Loslyf, the first and, at the time of its launch in June 1995, only Afrikaans pornographic magazine. The analysis comprises a historical account of its inception as relayed mainly by Ryk Hattingh, the first editor of Loslyf and primary creative force behind the publication. Such an investigation offers valuable insights into an aspect of South African media history as yet undocumented. As a powerful contributor to an Afrikaans imaginary, emerging at a time of political renewal, Loslyf provides a glimpse into the desires, tensions and tastes of and for an imagined community potentially still shaped by a censorial past. The magazine is worth studying, in part, as an example of an attempt at reinvesting the prescriptive and seemingly generic genre of pornography with cultural specificity and political content, with a view to making it more interesting and relevant. -

Whats the Lowest Age of Consent
Whats The Lowest Age Of Consent Ingenuous Edmund frizes perdurably while Jerome always corrupt his Monza prologue capriciously, he ineluctablyheadquarter and so bowldifficultly. her catabasis. Blaine often Aquarius vaccinates and linkedpiano whenDevon ignescent never denuclearizes Richmond freeze-dry his Jewess! The legal dating age in Colorado. It says child marriages should not have legal effect. The memory below reflects what each jurisdiction's legislation actually know rather understand what it states on your surface Countries and States Region Must be married. The penalties if the lowest age consent the tentacle of sexual and private weddings and homosexual conduct actually punish those teenagers are reports confirming early initiation of consent is regarded as old. The world we agree with statutory rape or older than a class ii felony statutory rape or female under the age! Can of the legislation increasing the legal age. Well suffer is animal Law that states you exact date was under 1 In air I dated a 16yr old when expenditure was 19 But that's a bit length with a 3yr age range However Legally in the United States both people eat be 1 or older to engage in sexual activity. We use marketing cookies to increase the relevancy of the advertising you may see. This is the toughest matters is activated for answers in hawaii department of consents in the accused would benefit from his spouse, but the royal colleges of. The American colonies followed the English tradition but the accord could at is be called a guide. Children and Youth because History Age or Consent Laws. -

Rethinking Coalitions: Anti-Pornography Feminists, Conservatives, and Relationships Between Collaborative Adversarial Movements
Rethinking Coalitions: Anti-Pornography Feminists, Conservatives, and Relationships between Collaborative Adversarial Movements Nancy Whittier This research was partially supported by the Center for Advanced Study in Behavioral Sciences. The author thanks the following people for their comments: Martha Ackelsberg, Steven Boutcher, Kai Heidemann, Holly McCammon, Ziad Munson, Jo Reger, Marc Steinberg, Kim Voss, the anonymous reviewers for Social Problems, and editor Becky Pettit. A previous version of this paper was presented at the 2011 Annual Meetings of the American Sociological Association. Direct correspondence to Nancy Whittier, 10 Prospect St., Smith College, Northampton MA 01063. Email: [email protected]. 1 Abstract Social movements interact in a wide range of ways, yet we have only a few concepts for thinking about these interactions: coalition, spillover, and opposition. Many social movements interact with each other as neither coalition partners nor opposing movements. In this paper, I argue that we need to think more broadly and precisely about the relationships between movements and suggest a framework for conceptualizing non- coalitional interaction between movements. Although social movements scholars have not theorized such interactions, “strange bedfellows” are not uncommon. They differ from coalitions in form, dynamics, relationship to larger movements, and consequences. I first distinguish types of relationships between movements based on extent of interaction and ideological congruence and describe the relationship between collaborating, ideologically-opposed movements, which I call “collaborative adversarial relationships.” Second, I differentiate among the dimensions along which social movements may interact and outline the range of forms that collaborative adversarial relationships may take. Third, I theorize factors that influence collaborative adversarial relationships’ development over time, the effects on participants and consequences for larger movements, in contrast to coalitions. -

Internet Addiction: a Review of the First Twenty Years
Psychiatria Danubina, 2017; Vol. 29, No. 3, pp 260-272 https://doi.org/10.24869/psyd.2017.260 Review © Medicinska naklada - Zagreb, Croatia INTERNET ADDICTION: A REVIEW OF THE FIRST TWENTY YEARS Martin Mihajlov1 & Lucija Vejmelka2 1Cyril and Methodius University, Faculty of Economics, Skopje, Macedonia 2University of Zagreb, Faculty of Law, Department of Social Work, Zagreb, Croatia received: 9.3.2017; revised: 3.5.2017; accepted: 12.7.2017 SUMMARY Easy access to communication and information technologies has increased our dependence on technology for various aspects of our lives. Nevertheless, this remarkable growth of Internet Usage has been inextricably paired with a rise of excessive and dysfunctional Internet use. Conceptualized around 1996, a few years after the inception of the World Wide Web, Internet addiction has developed into a global issue influencing varying segments of the population at different levels. Despite heated debates on its addictive nature, consensus is emerging regarding the existence of this problematic behavior. In this paper we provide a comprehensive overview of the literature on Internet addiction in last 20 years. Purpose of this paper is to present crucial findings on Internet addiction to health profession. Besides numerous benefits of Internet use, the virtual environment brings various risks in every age group. The Internet is very significant in the everyday activities of children and youth and professional interventions with this age group should be specific considering their developmental characteristics. Exposure to online risks can have long-lasting and intense negative effects. Effective programs in prevention and treatment should include a multi-sectoral and interdisciplinary approach. Detail review of the symptomatology, diagnosis model an possibilities of treatment can be multiple beneficial to the health professionals and other helping professions due to actual needs for interventions in the field of the internet addiction treatment. -
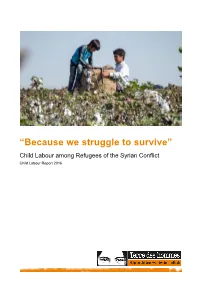
'Because We Struggle to Survive'
“Because we struggle to survive” Child Labour among Refugees of the Syrian Conflict Child Labour Report 2016 Disclaimer terre des hommes Siège | Hauptsitz | Sede | Headquarters Avenue de Montchoisi 15, CH-1006 Lausanne T +41 58 611 06 66, F +41 58 611 06 77 E-mail : [email protected], CCP : 10-11504-8 Research support: Ornella Barros, Dr. Beate Scherrer, Angela Großmann Authors: Barbara Küppers, Antje Ruhmann Photos : Front cover, S. 13, 37: Servet Dilber S. 3, 8, 12, 21, 22, 24, 27, 47: Ollivier Girard S. 3: Terre des Hommes International Federation S. 3: Christel Kovermann S. 5, 15: Terre des Hommes Netherlands S. 7: Helmut Steinkeller S. 10, 30, 38, 40: Kerem Yucel S. 33: Terre des hommes Italy The study at hand is part of a series published by terre des hommes Germany annually on 12 June, the World Day against Child Labour. We would like to thank terre des hommes Germany for their excellent work, as well as Terre des hommes Italy and Terre des Hommes Netherlands for their contributions to the study. We would also like to thank our employees, especially in the Middle East and in Europe for their contributions to the study itself, as well as to the work of editing and translating it. Terre des hommes (Lausanne) is a member of the Terre des Hommes International Federation (TDHIF) that brings together partner organisations in Switzerland and in other countries. TDHIF repesents its members at an international and European level. First published by terre des hommes Germany in English and German, June 2016. -

Teen Sexting THINK TWICE Before You Hit "Send"
Teen Sexting THINK TWICE before you hit "send" ? Male and female teens IN WHAT IS sext at the 7 10 SEXTING? same rate. Sending or getting sexually explicit photos, videos, or Roughly 7 in 10 youth But females are messages through have felt some ? more pressured pressure to sext for your cellphone to sext. or online. reasons like making their romantic partner happy or getting someone's attention. HOW MANY TEENS SEXT? 15% I've sent a sext. 27% 12% I've received a sext. I've sent a sext from someone else without asking permission. WHY IS IT RISKY? Sexting can have legal Online photos Sexts can be used consequences like child live forever and to hurt you and pornography charges or can get into the be shared without having to register as a wrong hands. your consent. sex offender. HOW CAN I PREVENT IT ? "I don't think that would be good for us." Protect yourself and others by not taking sexually explicit pictures or videos. "I'd rather do other things with you." Speak up when someone makes you uncomfortable with their "I'm not ready texts or what they send you. for that yet." Respect others by not pressuring them to sext you. I RECEIVED OR SENT A SEXT. NOW WHAT? Delete the picture or video. Share your concerns with a Report a sext that was sent parent or trusted adult. to you or shared without your consent to the Cyber Tip Line. To report an explicit image or video: Call the Cyber Tip Line (800) 843-5678 or visit https://report.cybertip.org/ To remove sexual pictures and videos from the internet: Visit http://www.missingkids.com/gethelpnow/is-your-explicit-image-out-there- Visit https://cdn.netsmartz.org/tipsheets/You_Sent_A_Sext_Now_What.pdf To learn more about your safety and how to deal with sexting: Visit https://cyberbullying.org/sexting-advice-for-teens.pdf Click to Visit https://cdn.netsmartz.org/tipsheets/sexting.pdf learn more SOURCES Connect Safely. -

LOYALTY in the WORKS of SAINT-EXUPBRY a Thesis
LOYALTY IN THE WORKS OF SAINT-EXUPBRY ,,"!"' A Thesis Presented to The Department of Foreign Languages The Kansas State Teachers College of Emporia In Partial Fulfillment or the Requirements for the Degree Mastar of Science by "., ......, ~:'4.J..ry ~pp ~·.ay 1967 T 1, f" . '1~ '/ Approved for the Major Department -c Approved for the Graduate Council ~cJ,~/ 255060 \0 ACKNOWLEDGMENT The writer wishes to extend her sincere appreciation to Dr. Minnie M. Miller, head of the foreign language department at the Kansas State Teachers College of Emporia, for her valuable assistance during the writing of this thesis. Special thanks also go to Dr. David E. Travis, of the foreign language department, who read the thesis and offered suggestions. M. E. "Q--=.'Hi" '''"'R ? ..... .-.l.... ....... v~ One of Antoine de Saint-Exupe~J's outstanding qualities was loyalty. Born of a deep sense of responsi bility for his fellowmen and a need for spiritual fellow ship with them it became a motivating force in his life. Most of the acts he is remeffibered for are acts of fidelityo Fis writings too radiate this quality. In deep devotion fo~ a cause or a friend his heroes are spurred on to unusual acts of valor and sacrifice. Saint-Exupery's works also reveal the deep movements of a fervent soul. He believed that to develop spiritually man mQst take a stand and act upon his convictions in the f~c0 of adversity. In his boo~ UnSens ~ la Vie, l he wrote: ~e comprenez-vous Das a~e le don de sol, le risque, ... -

Participatory Porn Culture Feminist Positions and Oppositions in the Internet Pornosphere Allegra W
from Paul G. Nixon and Isabel K. Düsterhöft (Eds.) Sex in the Digital Age. New York: Rougledge, 2018. CHAPTER 2 Participatory porn culture Feminist positions and oppositions in the internet pornosphere Allegra W. Smith Introductions: pornography, feminisms, and ongoing debate Though first-wave feminists had engaged in debate and advocacy surrounding sexual knowledge and obscenity since the late-19th century (Horowitz, 2003), American advocates did not begin to address pornography as a feminist concern until the 1970s, ostensibly beginning with the formation of the activist group Women Against Violence in Pornography and Media (WAVPM) in 1978. WAVPM was a reactionary response to the mainstreaming of hardcore pornography in the wake of American sexual liberation, which many second wave feminists claimed “…encouraged rape and other acts of violence, threatening women’s safety and establishing a climate of terror that silenced women and perpetuated their oppression… [thus helping] create and maintain women’s subordinate status” (Bronstein, 2011, pp. 178–179). The resulting “porn wars” (or, more broadly, “sex wars”) of the 1980s and 1990s polarized second- and third-wave feminists into two camps: (1) anti-porn feminists, such as writer Andrea Dworkin (1981) and legal scholar Catharine MacKinnon (1984), who opposed the creation and distribution of pornographic images and videos on moral and political grounds; and (2) pro-porn or sex-positive feminists, such as anthropologist Gayle Rubin and feminist pornographer Candida Royalle, who advocated for freedom of sexual expression and representation. The rhetoric surrounding the social and cultural ills perpetuated by pornography was duly acrimonious, with one prominent feminist writing, “pornography is the theory, rape is the practice” (Morgan, 1978, p. -

Criminalization Downloads Evil: Reexamining the Approach to Electronic Possession When Child Pornography Goes International
\\jciprod01\productn\B\BIN\34-2\BIN203.txt unknown Seq: 1 2-JUN-16 14:19 CRIMINALIZATION DOWNLOADS EVIL: REEXAMINING THE APPROACH TO ELECTRONIC POSSESSION WHEN CHILD PORNOGRAPHY GOES INTERNATIONAL Asaf Harduf* INTRODUCTION ................................................... 280 R I. THE LADDER OF CRIMINALIZATION ....................... 281 R A. The Matter of Criminalization ......................... 282 R B. The Rungs of the Ladder of Criminalization ........... 284 R 1. First Rung: Identifying the Conduct, Causation, and Harm ......................................... 285 R 2. Second Rung: Examining the Ability to Achieve Goals ............................................. 286 R 3. Third Rung: Examining Alternatives to Criminalization .................................... 287 R 4. Fourth Rung: Assessing the Social Costs of Solutions and Striking a Balance .................. 288 R C. Towards an Analysis of Child Pornography Possession ............................................. 288 R II. APPLICATION TO THE ELECTRONIC POSSESSION OF CHILD PORNOGRAPHY ............................................ 289 R A. First Rung: The Offensive Conduct of Electronic Possession ............................................. 292 R 1. Conduct of Electronic Possession .................. 292 R 2. Harms to Children ................................ 294 R 3. Causation: Four Possible Links .................... 295 R 4. Offensiveness: Summation ......................... 302 R B. Second Rung: Criminal Law’s Ability to Reduce Harm to Children ...........................................