Internet Technologies
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Sistem Pendukung Keputusan Dalam Pemilihan Control Panel Virtual Private Server Menggunakan Metode AHP Dan SAW
Citec Journal, Vol. 5, No. 1, November 2017 – Januari 2018 ISSN: 2460-4259 14 Sistem Pendukung Keputusan Dalam Pemilihan Control Panel Virtual Private Server Menggunakan Metode AHP dan SAW Decision Support System in Selection of a Control Panel Virtual Private Server Using AHP and SAW Method Arwendra Adi Putra*1, Kusrini 2, Eko Pramono3 1,2,3Magister Teknik Informatika, Universitas Amikom Yogyakarta E-mail: [email protected], [email protected], [email protected] Abstrak Hosting dapat dibedakan menjadi berbagai macam type, salah satunya adalah Virtual Private Server (VPS). VPS merupakan sebuah cara untuk membagi sumber daya sebuah physical server menjadi server virtual. Sebuah VPS memerlukan control panel karena untuk mempermudah pengaturan seperti mengelola email, disk, database, penambahan domain, memonitor bandwidth dan backup data. Terdapat berbagai macam control panel dengan spesifikasi yang berbeda-beda. Pemilihan control panel tersebut sangat penting karena control panel tersebut harus disesuaikan dengan spesifikasi VPS. Berdasarkan permasalahan tersebut, diperlukan sistem yang dapat membantu dalam pengambilan keputusan dalam pemilihan control panel. Metode yang digunakan dalam penelitian ini adalah dengan menggunakan metode Analitical Hierarcy Process (AHP) dan Simple Additive Weighting (SAW). Metode AHP digunakan untuk mencari bobot variabel kriteria, sedangkan metode SAW digunakan untuk menentukan nilai akhir dan perangkingan. Hasil perangkingan alternatif control panel pada sistem ini menunjukkan hasil yang sama dengan hasil perangkingan dari pakar control panel, sehingga sistem ini dapat digunakan oleh pengguna sebagai dasar pengambilan keputusan dalam menentukan pemilihan alternatif control panel. Kata Kunci — control panel, VPS, AHP, SAW, sistem pendukung keputusan Abstract Hosting can be divided into various types, one of them is Virtual Private Server (VPS). -

Spam Experts Incoming Email Filter Eine Leistungsstarke Lösung Zum Schutz Von Netzwerken Vor Eingehenden Spams Und Malware, Dank Der Webhosts Zeit Und Geld Sparen
DATENBLATT Spam Experts Incoming Email Filter Eine leistungsstarke Lösung zum Schutz von Netzwerken vor eingehenden Spams und Malware, dank der Webhosts Zeit und Geld sparen. Eingehende Spam, Ransomware und Phishing-Versuche können für jeden Internetdienstanbieter ein Risiko darstellen. SolarWinds® Spam Experts hilft Webhosts und ISPs/ Telekommunikationsanbietern dabei, den E-Mail-Schutz zu verbessern. Das Lösungsangebot umfasst erschwingliche Filterung eingehender E-Mails. Diese Lösungen basieren auf der intelligenten Protection & Filtering Engine, die permanent aktualisiert wird, um neue Bedrohungen zu erkennen. Die Lösung kann in einer redundanten Cloud-Umgebung oder lokal bereitgestellt werden. FUNKTIONSWEISE Eingangsfilterung Der SolarWinds Spam Experts-Eingangsfilter ist eine Gatewaylösung. Die Aktivierung erfolgt über eine einfache DNS-Anpassung. Sobald die MX-Einträge geändert wurden, Internet Filterung Protokol- gehen alle eingehenden E-Mails zunächst an unser System, lierung wo sie gefiltert und anschließend an die unveränderten Ziel- Mailserver Ihrer Kunden übermittelt werden. Zentralisierte Verwaltung Die Lösung bietet erstklassige Abwehr, die vor Ihrer E-Mail- Infrastruktur ausgeführt wird, und trennt mittels erweiterter rchiierung uarantne Filterungsalgorithmen und Methoden zur Erkennung von Spam-Mustern rechtmäßige von unrechtmäßigen E-Mails. Mit Spam Experts lokal oder gehostete loud einer Genauigkeitsrate von fast 100 % bietet sie vollständigen Schutz für den Posteingang. Potenziell schädliche Mitteilungen werden in eine -

'Building' Architects and Use of Open-Source Tools Towards Achievement of Millennium Development Goals
'Building' Architects and Use of Open-source Tools Towards Achievement of Millennium Development Goals. Oku, Onyeibo Chidozie Department of Architecture Faculty of Environmental Sciences Enugu State University of Science and Technology Email: [email protected] ABSTRACT Millennium Development Goals (MDGs) were established by the United Nations to improve the well-being of humans and their habitat. Whether they are the target beneficiaries or amongst the parties administering services for achieving the MDGs, humans must carry out these activities in a physical environment. Hence, the Seventh Goal of the MDG has an indirect and far-reaching relationship with the others because it deals with the sustainable development of the built environment. Architects deliver consultancy services that span the design, documentation and construction supervision of the built environment. This study sought to determine the extent to which these professionals can do this, with respect to the Seventh Millennium Development Goal, using mainly open-source tools. The study draws from literature reviews, end-user feedback or reports, interviews with developers of applicable open-source products, and statistics from a survey, launched in 2011, for capturing how architects use ICT in their businesses. Analysis of popular open-source technologies for the Architecture, Engineering and Construction (AEC) industry show a concentration of resources in favour of the later stages of the Architect's role, rather than the design and contract-drawing stages. Some of the better-implemented tools are either too cryptic for professionals who communicate in graphical terms, or heavily biased towards software engineering practices. The products that promise Building Information Modelling (BIM) capabilities are still at an early developmental stage. -

Tao-Of-Tmux Documentation 发布 V1.0.2
tao-of-tmux Documentation 发布 v1.0.2 Tony Narlock 2020 年 04 月 18 日 Contents 1 前言 3 1.1 关于本书 ............................................... 3 1.2 代码等风格说明 ........................................... 4 1.3 本书主要内容 ............................................. 4 1.4 打赏 .................................................. 5 1.5 书籍形式(Formats) ........................................ 5 1.6 勘误说明(Errata){#errata} ................................... 5 1.7 感谢 .................................................. 6 1.8 本书跟新和 tmux 的变动 ...................................... 6 2 tmux 初识 {#thinking-tmux} 7 2.1 terminal 的窗口管理器 ....................................... 8 2.2 多任务处理 .............................................. 9 2.3 在后台运行程序 ........................................... 10 2.4 Powerful combos ........................................... 11 2.5 小节 .................................................. 12 3 Terminal 基础知识(fundamentals){#terminal-fundamentals} 13 3.1 POSIX 标准 ............................................. 13 3.2 Terminal interface .......................................... 14 3.3 Terminal emulators ......................................... 15 3.4 Shell languages {#shell-languages} ................................ 15 3.5 Shell interpreters (Shells) {#shells} ................................ 15 3.6 小节 .................................................. 16 4 开始使用(Practical usage){#practical-usage} 17 4.1 前缀组合快捷键(prefix key ){#prefix-key} ........................... 17 4.2 Session persistence and the server model ............................. 19 -
Achieving Redundancy with Hosting Controller
Perspective In the perilous world of hosting one of the most sought-after features is failover capability. Most hosting providers desire a redundant setup in order to keep their content highly available (H.A) and minimize the chances of downtime in case of a disaster. Why is Redundancy Important? Hosting businesses usually require their data-centric internet applications to be served by more than one servers in a highly available cluster. Redundancy ensures that the data of a provider is always safe and readily available. Maximizing uptime is one of the prime goals of ISPs, ITSPs, Telcos, HSPs, MSPs and other Cloud providers. Redundancy can and does help. Hosting Controller Pushing Boundaries to accomplish end-to-end Redundancy Let’s explore the failover capabilities inherent in Hosting Controller Panel Exchange High Web DNS Replication Redundancy Availability Redundancy HC HC HC proposes the setup of an IIS Web manages the DNS redundancy in HC holds the ability of offering high Farm for achieving web a proficient manner. DNS zones availability and site resilience for redundancy. There are various can be replicated from the Exchange through its ways to design the infrastructure Primary DNS to the Secondary or holds the provision for control Primary/Secondary arrangement. of a Web Farm however HC Tertiary DNS for that matter. The panel redundancy through its This connotes the staging of recommends a Homogeneous replication is handled through simple multi portal server Exchange servers in a Web Farm with Shared Hosting Controller’s own capability. Primary/Secondary arrangement Configuration. interface. HC Master Control Portal Servers A successful installation of HC ends up creating an admin site in IIS called HostingController. -

There Are Two Dedicated Dspace IRC (Internet Relay Chat) Channels (I.E
IRC Code of Conduct All DSpace support channels, mailing lists and meetings follow the LYRASIS Code of Conduct. We ask you to remain respectful in all discussions. We also encourage you to report any violations of the code of conduct to LYRASIS (see the Code of Conduct for more details). DSpace chat has moved to Slack Our old IRC channels are essentially unmonitored these days. Instead, we recommend joining our DSpace.org Slack for any chat-based support. You are also welcome to email your question to the dspace-tech Mailing List as an alternative, or choose one of the other DSpace Sup port options. There are two dedicated DSpace IRC (internet relay chat) channels (i.e. "rooms") on the irc.freenode.net server: #dspace (irc://irc.freenode.net/dspace) - all DSpace discussions and live Q & A. This channel is unlogged. #duraspace (irc://irc.freenode.net/duraspace) - Old duraspace community channel (no longer used). As of July 2018, this channel is unlogged. Pri or years logs are still available/archived. If you do not have access to an IRC client, or are new to IRC, the following web interfaces are very easy way to get started: Login to #dspace IRC at: http://webchat.freenode.net?channels=dspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Login to #duraspace IRC at: http://webchat.freenode.net?channels=duraspace Enter in a nickname of your choice (e.g. firstName_lastName) & click "Connect" Or you can login to both IRC channels at the same time: http://webchat.freenode.net?channels=duraspace,dspace For a list of IRC client software, see: http://en.wikipedia.org/wiki/Comparison_of_Internet_Relay_Chat_clients Many current Instant Messaging (IM) clients also support IRC. -

Internet Evidence Finder Report
Patrick Leahy Center for Digital Investigation (LCDI) Internet Evidence Finder Report Written and Researched by Nick Murray 175 Lakeside Ave, Room 300A Phone: 802/865-5744 Fax: 802/865-6446 http://www.lcdi.champlin.edu July 2013 IEF Report 6/28/2013 Page 1 of 33 Patrick Leahy Center for Digital Investigation (LCDI) Disclaimer: This document contains information based on research that has been gathered by employee(s) of The Senator Patrick Leahy Center for Digital Investigation (LCDI). The data contained in this project is submitted voluntarily and is unaudited. Every effort has been made by LCDI to assure the accuracy and reliability of the data contained in this report. However, LCDI nor any of our employees make no representation, warranty or guarantee in connection with this report and hereby expressly disclaims any liability or responsibility for loss or damage resulting from use of this data. Information in this report can be downloaded and redistributed by any person or persons. Any redistribution must maintain the LCDI logo and any references from this report must be properly annotated. Contents Introduction ............................................................................................................................................................. 5 Prior Work: .......................................................................................................................................................... 7 Purpose and Scope: ............................................................................................................................................ -

Freiesmagazin 06/2011
freiesMagazin Juni 2011 Topthemen dieser Ausgabe Ubuntu 11.04 – Vorstellung des Natty Narwhal Seite 4 Am 28. April 2011 wurde Ubuntu 11.04 freigegeben. Der Artikel gibt einen Überblick über die Neuerungen der Distribution mit besonderem Augenmerk auf das neue Desktop-System „Unity“, welches im Vorfeld bereits für viel Furore sorgte. (weiterlesen) GNOME 3.0: Bruch mit Paradigmen Seite 15 Mit der Freigabe von GNOME 3 bricht der Entwicklerkreis rund um die Desktopumgebung mit vielen gängigen Paradigmen der Benutzerführung und präsentiert ein weitgehend überarbeite- tes Produkt, das zahlreiche Neuerungen mit sich bringt. Drei wesentliche Punkte sind in die neue Generation der Umgebung eingegangen: eine Erneuerung der Oberfläche, Entfernung von unnötigen Komponenten und eine bessere Außendarstellung. (weiterlesen) UnrealIRC – gestern „Flurfunk“, heute „Chat“ Seite 24 Ungern brüllt man Anweisungen von Büro zu Büro. Damit Angestellte miteinander kommunizie- ren können, wird vielerorts zum Telefon gegriffen. Wird bereits telefoniert, muss die dienstliche E-Mail herhalten, um Kommunikationsbedürfnisse zu befriedigen. Was aber, wenn die Leitung belegt und das Senden einer E-Mail derzeit nicht möglich ist? Ein Chat ist die Lösung für das Problem. (weiterlesen) © freiesMagazin CC-BY-SA 3.0 Ausgabe 06/2011 ISSN 1867-7991 MAGAZIN Editorial Traut Euch und macht mit Wer nicht wagt, der nicht gewinnt Dies gilt im Übrigen für fast alles im Leben: sei Inhalt Die Reaktionen auf unsere These im Editorial es die Frage nach einer Gehaltserhöhung, das des letzten Monats [1] waren recht gut. Zur Erin- erste zögerliche Gespräch mit seinem Schwarm Linux allgemein nerung: Wir fragten, ob – nach der bescheidenen oder der Umzug ins Ausland, um eines neues Le- Ubuntu 11.04 – Vorstellung von Natty S. -

Spamexperts Incoming Email Filter a Powerful Solution to Safeguard Networks from Inbound Spam and Malware, Helping Web Hosts Save Time and Money
DATASHEET SpamExperts Incoming Email Filter A powerful solution to safeguard networks from inbound spam and malware, helping web hosts save time and money. Inbound spam, ransomware, and phishing attempts can put any internet service provider at risk. N-able™ SpamExperts helps web hosts and ISPs/telcos strengthen email protection. Services include affordable inbound filtering driven by a continuously updated Intelligent Protection & Filtering Engine to meet emerging threats. The solution can be deployed in a redundant cloud environment or on premises. How it works: N-able SpamExperts incoming spam filter is an email gateway solution. Activation is done with a simple DNS adjustment. Once the MX records are changed, all inbound email goes to our system first, where it is filtered and then relayed to the unchanged destination mail servers of your clients. It provides first-level defense running in front of your mail infrastructure and separates legitimate from unsolicited email with the help of advanced filtering algorithms and spam pattern detection methods. It offers full inbox protection with a nearly 100% accuracy rate. Potentially harmful messages are queued in quarantine and can be managed by end users. Helps save resources and money • Protects networks against the latest email-based threats. • Saves network resources with an efficient first-level incoming filter defense. • Helps save money with competitive and affordable licenses. Offers dual deployment options and integrates with a broad range of tools • Cloud or on-premises deployment. • Free add-ons to integrate with the most popular control panels and other email collaboration tools. • Multiple branding options available. Global statistics Gives customers and users visibility and control over their email flows • Empowers users to manage their email flows and gain real-time visibility into threats. -

Coleman-Coding-Freedom.Pdf
Coding Freedom !" Coding Freedom THE ETHICS AND AESTHETICS OF HACKING !" E. GABRIELLA COLEMAN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright © 2013 by Princeton University Press Creative Commons Attribution- NonCommercial- NoDerivs CC BY- NC- ND Requests for permission to modify material from this work should be sent to Permissions, Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TW press.princeton.edu All Rights Reserved At the time of writing of this book, the references to Internet Web sites (URLs) were accurate. Neither the author nor Princeton University Press is responsible for URLs that may have expired or changed since the manuscript was prepared. Library of Congress Cataloging-in-Publication Data Coleman, E. Gabriella, 1973– Coding freedom : the ethics and aesthetics of hacking / E. Gabriella Coleman. p. cm. Includes bibliographical references and index. ISBN 978-0-691-14460-3 (hbk. : alk. paper)—ISBN 978-0-691-14461-0 (pbk. : alk. paper) 1. Computer hackers. 2. Computer programmers. 3. Computer programming—Moral and ethical aspects. 4. Computer programming—Social aspects. 5. Intellectual freedom. I. Title. HD8039.D37C65 2012 174’.90051--dc23 2012031422 British Library Cataloging- in- Publication Data is available This book has been composed in Sabon Printed on acid- free paper. ∞ Printed in the United States of America 1 3 5 7 9 10 8 6 4 2 This book is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE !" We must be free not because we claim freedom, but because we practice it. -

Getting Started with Ubuntu 12.04
Getting Started withUbuntu 12.04 Second Edition The Ubuntu Manual Team Copyright © – by e Ubuntu Manual Team. Some rights reserved. cba is work is licensed under the Creative Commons Aribution–Share Alike . License. To view a copy of this license, see Appendix A, visit http://creativecommons.org/licenses/by-sa/./, or send a leer to Creative Commons, Second Street, Suite , San Francisco, California, , USA. Geing Started with Ubuntu . can be downloaded for free from http:// ubuntu-manual.org/ or purchased from http://ubuntu-manual.org/buy/ gswue/en_US. A printed copy of this book can be ordered for the price of printing and delivery. We permit and even encourage you to dis- tribute a copy of this book to colleagues, friends, family, and anyone else who might be interested. http://ubuntu-manual.org Second Edition Revision number: Revision date: -- :: + Contents Prologue Welcome Ubuntu Philosophy A brief history of Ubuntu Is Ubuntu right for you? Contact details About the team Conventions used in this book Installation Geing Ubuntu Trying out Ubuntu Installing Ubuntu—Geing started Finishing Installation Ubuntu installer for Windows e Ubuntu Desktop Understanding the Ubuntu desktop Unity Using Launcher e Dash Workspaces Managing windows Browsing files on your computer Nautilus file manager Searching for files and folders on your computer Customizing your desktop Accessibility Session options Geing help Working with Ubuntu All the applications you need Geing online Browsing the web Reading and composing email Using instant messaging Microblogging Viewing and editing photos Watching videos and movies Listening to audio and music Burning CDs and DVDs Working with documents, spreadsheets, and presentations Ubuntu One Hardware Using your devices Hardware identification . -
Acl Zope-Plone3 Zope-Externaleditor 0. Poppler-Utils 0. Xtrans-Dev
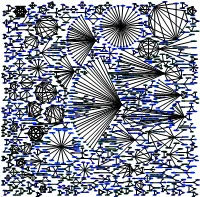
libdevel-declare-perl libisc50 libparrot1.4.0 libgssrpc4 gcj-4.4-jre libbeecrypt7 0. python-logilab-astng libbind9-50 libcontext-preserve-perl 0. 2.43902439024 odbcinst1debian1 1.06382978723 0. 0. 0. 0. 0. 0. 2.40963855422 0. gnome-mime-data 0. 1.06382978723 0. libbeecrypt-dev 0. 0. libisccc50 0. libparrot-dev 0. parrot 0. pike7.6-gdbm pike7.6 libplasma-ruby1.8 gcj-4.4-jdk libgcj10-awt 0. 0. libasn1-8-heimdal libkdb5-4 libkadm5srv6 0. 0. 0. 0. libpoconet8-dbg 1.230228471 libcommons-net-java 0. kdegames-card-data pylint kbreakout odbcinst 0. 0. 4.42477876106 0. 0. libmono-system2.0-cil 0.0. libmono-security2.0-cil 0. 0. 0. 3.84615384615 libmoosex-declare-perl 0. 0. 0. sendmail-cf kbounce librpm-dev gcj-jdk 0. libdns50 libpococrypto8-dbg 1.22807017544 libgnomevfs2-0 libhx509-4-heimdal 3.84615384615 kdegames-mahjongg-data 2.66666666667 1.28205128205 0. 4.42477876106 0. 0. 0. 2.63157894737 2.66666666667 0. 0. libgcj10-dev libisccfg50 0. parrot-minimal libkrb5-dev kblocks unixodbc python-logilab-common 0. libplasma-ruby 0. 0. kamera gcj 0. kcron 2.7027027027 0. 0. 0. 0. 0. 0. 0. 0. libatk1-ruby1.8 0. 0. 0. libgnomevfs2-common sensible-mda sendmail sendmail-bin salliere libcsv-java 0. caudium 2.66666666667 pike7.6-image 0. libpoconetssl8-dbg 0. 0. 0. 0. libroken18-heimdal kdesnake 4. 2.66666666667 kblackbox 0. 0. 0. 0. 0. kcolorchooser 0. 0. knetworkconf 0. libaliased-perl 0. 0. 0. plasma-scriptengine-ruby 0. 0. gcj-jre libmalaga7 0.0. 1.33333333333 0. mono-2.0-gac 0.