Online Anonymity 8
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cryptography
Pattern Recognition and Applications Lab CRYPTOGRAPHY Giorgio Giacinto [email protected] University of Cagliari, Italy Spring Semester 2019-2020 Department of Electrical and Electronic Engineering Cryptography and Security • Used to hide the content of a message • Goals – Confidentiality – Authenticity – Integrity • The text is modified by an encryption function – An interceptor should not be able to understand all or part of the message content http://pralab.diee.unica.it 2 Encryption/Decryption Process Key Key (Optional) (Optional) Original Plaintext Encryption Ciphertext Decryption Plaintext http://pralab.diee.unica.it 3 Keys and Locks http://pralab.diee.unica.it 4 Keys L F A Y B D E T C A R C S E E T Y H G S O U S U D H R D F C E I D B T E M E P Q X N R C I D S F T U A E T C A U R M F N P E C J N A C R D B E M K C I O P F B E W U X I Y M C R E P F N O G I D C N T M http://pralab.diee.unica.it 5 Keys L F A Y B D E T C A R C S E E T Y H G S O U S U D H R D F C E I D B T E M E P Q X N R C I D S F T U A E T C A U R M F N P E C J N A C R D B E M K C I O P F B E W U X I Y M C R E P F N O G I D C N T M http://pralab.diee.unica.it 6 Steganography - = http://pralab.diee.unica.it https://towardsdatascience.com/steganography-hiding-an-image-inside-another-77ca66b2acb1 7 Definitions • Cryptography algorithm C = E(K,M) A function E with two inputs – a message M – a key K that outputs – the encrypted message C The algorithm is based on a shared secret between the sender and the receiver K The Encryption Key http://pralab.diee.unica.it 8 Symmetric -

Poster: Introducing Massbrowser: a Censorship Circumvention System Run by the Masses
Poster: Introducing MassBrowser: A Censorship Circumvention System Run by the Masses Milad Nasr∗, Anonymous∗, and Amir Houmansadr University of Massachusetts Amherst fmilad,[email protected] ∗Equal contribution Abstract—We will present a new censorship circumvention sys- side the censorship regions, which relay the Internet traffic tem, currently being developed in our group. The new system of the censored users. This includes systems like Tor, VPNs, is called MassBrowser, and combines several techniques from Psiphon, etc. Unfortunately, such circumvention systems are state-of-the-art censorship studies to design a hard-to-block, easily blocked by the censors by enumerating their limited practical censorship circumvention system. MassBrowser is a set of proxy server IP addresses [14]. (2) Costly to operate: one-hop proxy system where the proxies are volunteer Internet To resist proxy blocking by the censors, recent circumven- users in the free world. The power of MassBrowser comes from tion systems have started to deploy the proxies on shared-IP the large number of volunteer proxies who frequently change platforms such as CDNs, App Engines, and Cloud Storage, their IP addresses as the volunteer users move to different a technique broadly referred to as domain fronting [3]. networks. To get a large number of volunteer proxies, we This mechanism, however, is prohibitively expensive [11] provide the volunteers the control over how their computers to operate for large scales of users. (3) Poor QoS: Proxy- are used by the censored users. Particularly, the volunteer based circumvention systems like Tor and it’s variants suffer users can decide what websites they will proxy for censored from low quality of service (e.g., high latencies and low users, and how much bandwidth they will allocate. -

N2N: a Layer Two Peer-To-Peer VPN
N2N: A Layer Two Peer-to-Peer VPN Luca Deri1, Richard Andrews2 ntop.org, Pisa, Italy1 Symstream Technologies, Melbourne, Australia2 {deri, andrews}@ntop.org Abstract. The Internet was originally designed as a flat data network delivering a multitude of protocols and services between equal peers. Currently, after an explosive growth fostered by enormous and heterogeneous economic interests, it has become a constrained network severely enforcing client-server communication where addressing plans, packet routing, security policies and users’ reachability are almost entirely managed and limited by access providers. From the user’s perspective, the Internet is not an open transport system, but rather a telephony-like communication medium for content consumption. This paper describes the design and implementation of a new type of peer-to- peer virtual private network that can allow users to overcome some of these limitations. N2N users can create and manage their own secure and geographically distributed overlay network without the need for central administration, typical of most virtual private network systems. Keywords: Virtual private network, peer-to-peer, network overlay. 1. Motivation and Scope of Work Irony pervades many pages of history, and computing history is no exception. Once personal computing had won the market battle against mainframe-based computing, the commercial evolution of the Internet in the nineties stepped the computing world back to a substantially rigid client-server scheme. While it is true that the today’s Internet serves as a good transport system for supplying a plethora of data interchange services, virtually all of them are delivered by a client-server model, whether they are centralised or distributed, pay-per-use or virtually free [1]. -

Security & Savings with Virtual Private Networks
Everybody’s connecting. Security & Savings with Virtual Private Networks In today’s New Economy, small businesses that might have dealt with just local or regional concerns now have to consider global markets and logistics. Many companies even have facilities spread across the country or throughout the world. At the same time security concerns of their network from hackers, Denial-of-Service (DoS) attacks and sending data over the Internet have become more widespread. Whether companies have a local, national, or global presence, they all need one thing: a way to maintain fast, secure, and reliable communications wherever their offices and workers are located. Until recently, such communications were only available by using leased telephone lines to maintain a Wide Area Network (WAN). Leased lines enabled companies to expand their private network beyond their immediate geographic area. Moreover, a WAN provided advantages over a public network like the Internet when it came to reliability, performance, and security. Unfortunately, leased lines are expensive to maintain, with costs rising as the distance between the offices increases. As the popularity of the Internet grew, businesses turned to it as a cost-effective way to extend their networks. The continuing popularity with the Internet has led to the evolution of Virtual Private Networks (VPNs). A VPN is a connection that allows private data to be sent securely over a shared or public network, such as the Internet. In fact, one of the driving forces behind VPNs is the Internet and its global presence. With VPNs, communication links between users and sites can be achieved quickly, inexpensively, and safely across the world. -

Copyrighted Material
Anonymizing 1 Your Activities In our daily lives we like to have a certain level of privacy. We have curtains on our win- dows, doors for our offices, and even special screen protectors for computers to keep out prying eyes. This idea of wanting privacy also extends to the use of the Internet. We do not want people knowing what we typed in Google, what we said in our Instant Message conversations, or what websites we visited. Unfortunately, your private information is largely available if someone is watching. When doing any number of things on the Internet, there are plenty of reasons you might want to go incognito. However, that does not mean you’re doing anything wrong or illegal. he justification for anonymity when researching malware and bad guys is pretty Tstraightforward. You do not want information to show up in logs and other records that might tie back to you or your organization. For example, let’s say you work at a finan- cial firm and you recently detected that a banking trojan infected several of your systems. You collected malicious domain names, IP addresses, and other data related to the malware. The next steps you take in your research may lead you to websites owned by the criminals. As a result, if you are not taking precautions to stay anonymous, your IP address will show up in various logs and be visible to miscreants. If the criminals can identify you or the organization from which you conduct your research, they may COPYRIGHTEDchange tactics or go into hiding, MATERIAL thus spoiling your investigation. -

Analysis of Recent Attacks on Ssl/Tls Protocols A
ANALYSIS OF RECENT ATTACKS ON SSL/TLS PROTOCOLS A THESIS SUBMITTED TO THE GRADUATE SCHOOL OF APPLIED MATHEMATICS OF MIDDLE EAST TECHNICAL UNIVERSITY BY DUYGU OZDEN¨ IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF MASTER OF SCIENCE IN CRYPTOGRAPHY SEPTEMBER 2016 Approval of the thesis: ANALYSIS OF RECENT ATTACKS ON SSL/TLS PROTOCOLS submitted by DUYGU OZDEN¨ in partial fulfillment of the requirements for the de- gree of Master of Science in Department of Cryptography, Middle East Technical University by, Prof. Dr. Bulent¨ Karasozen¨ Director, Graduate School of Applied Mathematics Prof. Dr. Ferruh Ozbudak¨ Head of Department, Cryptography Assoc. Prof. Dr. Murat Cenk Supervisor, Cryptography, METU Examining Committee Members: Assoc. Prof. Dr. Murat Cenk Cryptography, METU Assoc. Prof. Dr. Ali Doganaksoy˘ Mathematics, METU Asst. Prof. Dr. Fatih Sulak Mathematics, ATILIM UNIVERSITY Date: I hereby declare that all information in this document has been obtained and presented in accordance with academic rules and ethical conduct. I also declare that, as required by these rules and conduct, I have fully cited and referenced all material and results that are not original to this work. Name, Last Name: DUYGU OZDEN¨ Signature : v vi ABSTRACT ANALYSIS OF RECENT ATTACKS ON SSL/TLS PROTOCOLS Ozden,¨ Duygu M.S., Department of Cryptography Supervisor : Assoc. Prof. Dr. Murat Cenk September 2016, 46 pages Transport Layer Security(TLS) and its predecessor Secure Socket Layer(SSL) are two important cryptographic, certificate based protocols that satisfy secure communication in a network channel. They are widely used in many areas such as online banking systems, online shopping, e-mailing, military systems or governmental systems. -
Cryptographic Control Standard, Version
Nuclear Regulatory Commission Office of the Chief Information Officer Computer Security Standard Office Instruction: OCIO-CS-STD-2009 Office Instruction Title: Cryptographic Control Standard Revision Number: 2.0 Issuance: Date of last signature below Effective Date: October 1, 2017 Primary Contacts: Kathy Lyons-Burke, Senior Level Advisor for Information Security Responsible Organization: OCIO Summary of Changes: OCIO-CS-STD-2009, “Cryptographic Control Standard,” provides the minimum security requirements that must be applied to the Nuclear Regulatory Commission (NRC) systems which utilize cryptographic algorithms, protocols, and cryptographic modules to provide secure communication services. This update is based on the latest versions of the National Institute of Standards and Technology (NIST) Guidance and Federal Information Processing Standards (FIPS) publications, Committee on National Security System (CNSS) issuances, and National Security Agency (NSA) requirements. Training: Upon request ADAMS Accession No.: ML17024A095 Approvals Primary Office Owner Office of the Chief Information Officer Signature Date Enterprise Security Kathy Lyons-Burke 09/26/17 Architecture Working Group Chair CIO David Nelson /RA/ 09/26/17 CISO Jonathan Feibus 09/26/17 OCIO-CS-STD-2009 Page i TABLE OF CONTENTS 1 PURPOSE ............................................................................................................................. 1 2 INTRODUCTION .................................................................................................................. -

In Computer Networks, A
Practical No.1 Date:- Title:- Installation of Proxy-Server Windows Server 2003 What is proxy server? In computer networks, a proxy server is a server (a computer system or an application program) that acts as an intermediary for requests from clients seeking resources from other servers. A client connects to the proxy server, requesting some service, such as a file, connection, web page, or other resource, available from a different server. The proxy server evaluates the request according to its filtering rules. For example, it may filter traffic by IP address or protocol. If the request is validated by the filter, the proxy provides the resource by connecting to the relevant server and requesting the service on behalf of the client. A proxy server may optionally alter the client's request or the server's response, and sometimes it may serve the request wit hout contacting the specified server. In this case, it 'caches' responses from the remote server, and returns subsequent requests for the same content directly . Most proxies are a web proxy, allowing access to content on the World Wide Web. A proxy server has a large variety of potential purposes, including: To keep machines behind it anonymous (mainly for security).[1] To speed up access to resources (using caching). Web proxies are commonly used to cache web pages from a web server.[2] To apply access policy to network services or content, e.g. to block undesired sites. To log / audit usage, i.e. to provide company employee Internet usage reporting. To bypass security/ parental controls. To scan transmitted content for malware before delivery. -
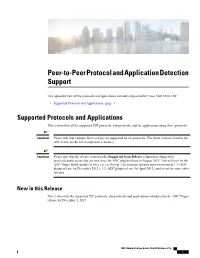
Peer-To-Peer Protocol and Application Detection Support
Peer-to-Peer Protocol and Application Detection Support This appendix lists all the protocols and applications currently supported by Cisco ASR 5500 ADC. • Supported Protocols and Applications, page 1 Supported Protocols and Applications This section lists all the supported P2P protocols, sub-protocols, and the applications using these protocols. Important Please note that various client versions are supported for the protocols. The client versions listed in the table below are the latest supported version(s). Important Please note that the release version in the Supported from Release column has changed for protocols/applications that are new since the ADC plugin release in August 2015. This will now be the ADC Plugin Build number in the x.xxx.xxx format. The previous releases were versioned as 1.1 (ADC plugin release for December 2012 ), 1.2 (ADC plugin release for April 2013), and so on for consecutive releases. New in this Release This section lists the supported P2P protocols, sub-protocols and applications introduced in the ADC Plugin release for December 1, 2017. ADC Administration Guide, StarOS Release 21.6 1 Peer-to-Peer Protocol and Application Detection Support New in this Release Protocol / Client Client Version Group Classification Supported from Application Release 6play 6play (Android) 4.4.1 Streaming Streaming-video ADC Plugin 2.19.895 Unclassified 6play (iOS) 4.4.1 6play — (Windows) BFM TV BFM TV 3.0.9 Streaming Streaming-video ADC Plugin 2.19.895 (Android) Unclassified BFM TV (iOS) 5.0.7 BFM — TV(Windows) Clash Royale -

Everyone's Guide to Bypassing Internet Censorship
EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of Toronto September, 2007 cover illustration by Jane Gowan Glossary page 4 Introduction page 5 Choosing Circumvention page 8 User self-assessment Provider self-assessment Technology page 17 Web-based Circumvention Systems Tunneling Software Anonymous Communications Systems Tricks of the trade page 28 Things to remember page 29 Further reading page 29 Circumvention Technologies Circumvention technologies are any tools, software, or methods used to bypass Inter- net filtering. These can range from complex computer programs to relatively simple manual steps, such as accessing a banned website stored on a search engine’s cache, instead of trying to access it directly. Circumvention Providers Circumvention providers install software on a computer in a non-filtered location and make connections to this computer available to those who access the Internet from a censored location. Circumvention providers can range from large commercial organi- zations offering circumvention services for a fee to individuals providing circumven- tion services for free. Circumvention Users Circumvention users are individuals who use circumvention technologies to bypass Internet content filtering. 4 Internet censorship, or content filtering, has become a major global problem. Whereas once it was assumed that states could not control Internet communications, according to research by the OpenNet Initiative (http://opennet.net) more than 25 countries now engage in Internet censorship practices. Those with the most pervasive filtering policies have been found to routinely block access to human rights organi- zations, news, blogs, and web services that challenge the status quo or are deemed threatening or undesirable. -

Threat Modeling and Circumvention of Internet Censorship by David Fifield
Threat modeling and circumvention of Internet censorship By David Fifield A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor J.D. Tygar, Chair Professor Deirdre Mulligan Professor Vern Paxson Fall 2017 1 Abstract Threat modeling and circumvention of Internet censorship by David Fifield Doctor of Philosophy in Computer Science University of California, Berkeley Professor J.D. Tygar, Chair Research on Internet censorship is hampered by poor models of censor behavior. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not just as a set of capabilities|such as the ability to monitor network traffic—but as a set of priorities constrained by resource limitations. My research addresses the twin themes of modeling and circumvention. With a grounding in empirical research, I build up an abstract model of the circumvention problem and examine how to adapt it to concrete censorship challenges. I describe the results of experiments on censors that probe their strengths and weaknesses; specifically, on the subject of active probing to discover proxy servers, and on delays in their reaction to changes in circumvention. I present two circumvention designs: domain fronting, which derives its resistance to blocking from the censor's reluctance to block other useful services; and Snowflake, based on quickly changing peer-to-peer proxy servers. I hope to change the perception that the circumvention problem is a cat-and-mouse game that affords only incremental and temporary advancements. -

Free Cgi Proxy Script
Free cgi proxy script click here to download There have been many other proxy software scripts in the past, such as Glype, PHProxy, CGIProxy, Surrogafier, ASProxy, Zelune but all have either perished. This CGI script (or other) acts as an HTTP, HTTPS, or FTP proxy. Here's a demo (username "free", password "speech"), that lets you browse. Surf the web with phpMyProxy. phpMyProxy is a free, light and powerful php proxy script programed by www.doorway.ru If you use this template, keep the link to Free CSS Templates intact. cgi proxy script free download. Guacamole Install Script The script installs dependencies and configure the OS automatically for you in order to obtain. FREE CGI Web Proxy List contains list of cgi/php proxies that are publicly accessed at the moment. Public CGI (Web, PHP) anonymous proxy free list. WEB/WWW servers) servers running a proxy in the form of a CGI script/program (Common. Are you looking to start your own PHP/CGI/Perl web proxy site? We have created an up-to-date list of free and working web-based proxy scripts available for. Proxy website with hosted proxy bypass scripts. Proxy scripts (also known as CGI proxies) work by modifiying the content of the requested page to send subsequent requests back to All are powerful, easily customizable and free. Download CGIProxy. This CGI script (or other) acts as an HTTP, HTTPS, or FTP proxy. Through it, you can retrieve any resource that is accessible from the. start your proxy site with these 3 great free proxy scripts.