7.4.2 DES Algorithm DES Is a Feistel Cipher Which Processes Plaintext Blocks of N =64Bits, Producing 64-Bit Ciphertext Blocks (Figure 7.8)
Total Page:16
File Type:pdf, Size:1020Kb

Load more
Recommended publications
-
25 Years of Linear Cryptanalysis -Early History and Path Search Algorithm
25 Years of Linear Cryptanalysis -Early History and Path Search Algorithm- Asiacrypt 2018, December 3 2018 Mitsuru Matsui © Mitsubishi Electric Corporation Back to 1990… 2 © Mitsubishi Electric Corporation FEAL (Fast data Encipherment ALgorithm) • Designed by Miyaguchi and Shimizu (NTT). • 64-bit block cipher family with the Feistel structure. • 4 rounds (1987) • 8 rounds (1988) • N rounds(1990) N=32 recommended • Key size is 64 bits (later extended to 128 bits). • Optimized for 8-bit microprocessors (no lookup tables). • First commercially successful cipher in Japan. • Inspired many new ideas, including linear cryptanalysis. 3 © Mitsubishi Electric Corporation FEAL-NX Algorithm [Miyaguchi 90] subkey 4 © Mitsubishi Electric Corporation The Round Function of FEAL 2-byte subkey Linear Relations 푌 2 = 푋1 0 ⊕ 푋2 0 푌 2 = 푋1 0 ⊕ 푋2 0 ⊕ 1 (푁표푡푎푡푖표푛: 푌 푖 = 푖-푡ℎ 푏푖푡 표푓 푌) 5 © Mitsubishi Electric Corporation Linear Relations of the Round Function Linear Relations 푂 16,26 ⊕ 퐼 24 = 퐾 24 K 푂 18 ⊕ 퐼 0,8,16,24 = 퐾 8,16 ⊕ 1 푂 10,16 ⊕ 퐼 0,8 = 퐾 8 S 0 푂 2,8 ⊕ 퐼 0 = 퐾 0 ⊕ 1 (푁표푡푎푡푖표푛: 퐴 푖, 푗, 푘 = 퐴 푖 ⊕ 퐴 푗 ⊕ 퐴 푘 ) S1 O I f S0 f 3-round linear relations with p=1 S1 f modified round function f at least 3 subkey (with whitening key) f bytes affect output6 6 © Mitsubishi Electric Corporation History of Cryptanalysis of FEAL • 4-round version – 100-10000 chosen plaintexts [Boer 88] – 20 chosen plaintexts [Murphy 90] – 8 chosen plaintexts [Biham, Shamir 91] differential – 200 known plaintexts [Tardy-Corfdir, Gilbert 91] – 5 known plaintexts [Matsui, Yamagishi -
The Data Encryption Standard (DES) – History
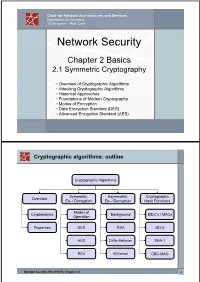
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -

Investigating Profiled Side-Channel Attacks Against the DES Key
IACR Transactions on Cryptographic Hardware and Embedded Systems ISSN 2569-2925, Vol. 2020, No. 3, pp. 22–72. DOI:10.13154/tches.v2020.i3.22-72 Investigating Profiled Side-Channel Attacks Against the DES Key Schedule Johann Heyszl1[0000−0002−8425−3114], Katja Miller1, Florian Unterstein1[0000−0002−8384−2021], Marc Schink1, Alexander Wagner1, Horst Gieser2, Sven Freud3, Tobias Damm3[0000−0003−3221−7207], Dominik Klein3[0000−0001−8174−7445] and Dennis Kügler3 1 Fraunhofer Institute for Applied and Integrated Security (AISEC), Germany, [email protected] 2 Fraunhofer Research Institution for Microsystems and Solid State Technologies (EMFT), Germany, [email protected] 3 Bundesamt für Sicherheit in der Informationstechnik (BSI), Germany, [email protected] Abstract. Recent publications describe profiled single trace side-channel attacks (SCAs) against the DES key-schedule of a “commercially available security controller”. They report a significant reduction of the average remaining entropy of cryptographic keys after the attack, with surprisingly large, key-dependent variations of attack results, and individual cases with remaining key entropies as low as a few bits. Unfortunately, they leave important questions unanswered: Are the reported wide distributions of results plausible - can this be explained? Are the results device- specific or more generally applicable to other devices? What is the actual impact on the security of 3-key triple DES? We systematically answer those and several other questions by analyzing two commercial security controllers and a general purpose microcontroller. We observe a significant overall reduction and, importantly, also observe a large key-dependent variation in single DES key security levels, i.e. -

Block Ciphers and the Data Encryption Standard
Lecture 3: Block Ciphers and the Data Encryption Standard Lecture Notes on “Computer and Network Security” by Avi Kak ([email protected]) January 26, 2021 3:43pm ©2021 Avinash Kak, Purdue University Goals: To introduce the notion of a block cipher in the modern context. To talk about the infeasibility of ideal block ciphers To introduce the notion of the Feistel Cipher Structure To go over DES, the Data Encryption Standard To illustrate important DES steps with Python and Perl code CONTENTS Section Title Page 3.1 Ideal Block Cipher 3 3.1.1 Size of the Encryption Key for the Ideal Block Cipher 6 3.2 The Feistel Structure for Block Ciphers 7 3.2.1 Mathematical Description of Each Round in the 10 Feistel Structure 3.2.2 Decryption in Ciphers Based on the Feistel Structure 12 3.3 DES: The Data Encryption Standard 16 3.3.1 One Round of Processing in DES 18 3.3.2 The S-Box for the Substitution Step in Each Round 22 3.3.3 The Substitution Tables 26 3.3.4 The P-Box Permutation in the Feistel Function 33 3.3.5 The DES Key Schedule: Generating the Round Keys 35 3.3.6 Initial Permutation of the Encryption Key 38 3.3.7 Contraction-Permutation that Generates the 48-Bit 42 Round Key from the 56-Bit Key 3.4 What Makes DES a Strong Cipher (to the 46 Extent It is a Strong Cipher) 3.5 Homework Problems 48 2 Computer and Network Security by Avi Kak Lecture 3 Back to TOC 3.1 IDEAL BLOCK CIPHER In a modern block cipher (but still using a classical encryption method), we replace a block of N bits from the plaintext with a block of N bits from the ciphertext. -

US 2007/0043.668A1 Baxter Et Al
US 2007.0043.668A1 (19) United States (12) Patent Application Publication (10) Pub. No.: US 2007/0043.668A1 Baxter et al. (43) Pub. Date: Feb. 22, 2007 (54) METHODS AND SYSTEMS FOR Related U.S. Application Data NEGOTABLE-INSTRUMENT FRAUD PREVENTION (63) Continuation of application No. 10/371,984, filed on Feb. 20, 2003, now Pat. No. 7,072,868. (75) Inventors: Craig A. Baxter, Castle Rock, CO (US); John Charles Ciaccia, Parker, Publication Classification CO (US); Rodney J. Esch, Littleton, CO (US) (51) Int. Cl. G06Q 99/00 (2006.01) Correspondence Address: (52) U.S. Cl. ................................................................ 705/50 TOWNSEND AND TOWNSEND AND CREW, LLP (57) ABSTRACT TWO EMBARCADERO CENTER EIGHTH FLOOR SAN FRANCISCO, CA 94111-3834 (US) An authentication value is provided in a magnetic-ink field of a negotiable instrument. The authentication value is (73) Assignee: First Data Corporation, Greenwood derived from application of an encryption algorithm defined Village, CO (US) by a secure key. The authentication value may be used to authenticate the instrument through reapplication of the (21) Appl. No.: 11/481,062 encryption algorithm and comparing the result with the authentication value. The instrument is authenticated if there (22) Filed: Jul. 3, 2006 is a match between the two. 530 instrument Presented at Port of Sae instrument Conveyed to First Financial MCR line Scanned and instrument 534 Institution Authenticated at Point of Sale 538 Electronic Package Generated with MICR-Line Information andlor image 542 Electronic -

Block Ciphers
Block Ciphers Chester Rebeiro IIT Madras CR STINSON : chapters 3 Block Cipher KE KD untrusted communication link Alice E D Bob #%AR3Xf34^$ “Attack at Dawn!!” message encryption (ciphertext) decryption “Attack at Dawn!!” Encryption key is the same as the decryption key (KE = K D) CR 2 Block Cipher : Encryption Key Length Secret Key Plaintext Ciphertext Block Cipher (Encryption) Block Length • A block cipher encryption algorithm encrypts n bits of plaintext at a time • May need to pad the plaintext if necessary • y = ek(x) CR 3 Block Cipher : Decryption Key Length Secret Key Ciphertext Plaintext Block Cipher (Decryption) Block Length • A block cipher decryption algorithm recovers the plaintext from the ciphertext. • x = dk(y) CR 4 Inside the Block Cipher PlaintextBlock (an iterative cipher) Key Whitening Round 1 key1 Round 2 key2 Round 3 key3 Round n keyn Ciphertext Block • Each round has the same endomorphic cryptosystem, which takes a key and produces an intermediate ouput • Size of the key is huge… much larger than the block size. CR 5 Inside the Block Cipher (the key schedule) PlaintextBlock Secret Key Key Whitening Round 1 Round Key 1 Round 2 Round Key 2 Round 3 Round Key 3 Key Expansion Expansion Key Key Round n Round Key n Ciphertext Block • A single secret key of fixed size used to generate ‘round keys’ for each round CR 6 Inside the Round Function Round Input • Add Round key : Add Round Key Mixing operation between the round input and the round key. typically, an ex-or operation Confusion Layer • Confusion layer : Makes the relationship between round Diffusion Layer input and output complex. -

Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, Newdes, RC2, and TEA
Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, NewDES, RC2, and TEA John Kelsey Bruce Schneier David Wagner Counterpane Systems U.C. Berkeley kelsey,schneier @counterpane.com [email protected] f g Abstract. We present new related-key attacks on the block ciphers 3- WAY, Biham-DES, CAST, DES-X, NewDES, RC2, and TEA. Differen- tial related-key attacks allow both keys and plaintexts to be chosen with specific differences [KSW96]. Our attacks build on the original work, showing how to adapt the general attack to deal with the difficulties of the individual algorithms. We also give specific design principles to protect against these attacks. 1 Introduction Related-key cryptanalysis assumes that the attacker learns the encryption of certain plaintexts not only under the original (unknown) key K, but also under some derived keys K0 = f(K). In a chosen-related-key attack, the attacker specifies how the key is to be changed; known-related-key attacks are those where the key difference is known, but cannot be chosen by the attacker. We emphasize that the attacker knows or chooses the relationship between keys, not the actual key values. These techniques have been developed in [Knu93b, Bih94, KSW96]. Related-key cryptanalysis is a practical attack on key-exchange protocols that do not guarantee key-integrity|an attacker may be able to flip bits in the key without knowing the key|and key-update protocols that update keys using a known function: e.g., K, K + 1, K + 2, etc. Related-key attacks were also used against rotor machines: operators sometimes set rotors incorrectly. -

Camellia: a 128-Bit Block Cipher Suitable for Multiple Platforms
Copyright NTT and Mitsubishi Electric Corporation 2000 Camellia: A 128-Bit Block Cipher Suitable for Multiple Platforms † ‡ † Kazumaro Aoki Tetsuya Ichikawa Masayuki Kanda ‡ † ‡ ‡ Mitsuru Matsui Shiho Moriai Junko Nakajima Toshio Tokita † Nippon Telegraph and Telephone Corporation 1-1 Hikarinooka, Yokosuka, Kanagawa, 239-0847 Japan {maro,kanda,shiho}@isl.ntt.co.jp ‡ Mitsubishi Electric Corporation 5-1-1 Ofuna, Kamakura, Kanagawa, 247-8501 Japan {ichikawa,matsui,june15,tokita}@iss.isl.melco.co.jp September 26, 2000 Abstract. We present a new 128-bit block cipher called Camellia. Camellia sup- ports 128-bit block size and 128-, 192-, and 256-bit key lengths, i.e. the same interface specifications as the Advanced Encryption Standard (AES). Camellia was carefully designed to withstand all known cryptanalytic attacks and even to have a sufficiently large security leeway for use of the next 10-20 years. There are no hidden weakness inserted by the designers. It was also designed to have suitability for both software and hardware implementations and to cover all possible encryption applications that range from low-cost smart cards to high-speed network systems. Compared to the AES finalists, Camellia offers at least comparable encryption speed in software and hardware. An optimized implementation of Camellia in assembly language can en- crypt on a PentiumIII (800MHz) at the rate of more than 276 Mbits per second, which is much faster than the speed of an optimized DES implementation. In ad- dition, a distinguishing feature is its small hardware design. The hardware design, which includes key schedule, encryption and decryption, occupies approximately 11K gates, which is the smallest among all existing 128-bit block ciphers as far as we know. -

Known and Chosen Key Differential Distinguishers for Block Ciphers
Known and Chosen Key Differential Distinguishers for Block Ciphers Ivica Nikoli´c1?, Josef Pieprzyk2, Przemys law Soko lowski2;3, Ron Steinfeld2 1 University of Luxembourg, Luxembourg 2 Macquarie University, Australia 3 Adam Mickiewicz University, Poland [email protected], [email protected], [email protected], [email protected] Abstract. In this paper we investigate the differential properties of block ciphers in hash function modes of operation. First we show the impact of differential trails for block ciphers on collision attacks for various hash function constructions based on block ciphers. Further, we prove the lower bound for finding a pair that follows some truncated differential in case of a random permutation. Then we present open-key differential distinguishers for some well known round-reduced block ciphers. Keywords: Block cipher, differential attack, open-key distinguisher, Crypton, Hierocrypt, SAFER++, Square. 1 Introduction Block ciphers play an important role in symmetric cryptography providing the basic tool for encryp- tion. They are the oldest and most scrutinized cryptographic tool. Consequently, they are the most trusted cryptographic algorithms that are often used as the underlying tool to construct other cryp- tographic algorithms. One such application of block ciphers is for building compression functions for the hash functions. There are many constructions (also called hash function modes) for turning a block cipher into a compression function. Probably the most popular is the well-known Davies-Meyer mode. Preneel et al. in [27] have considered all possible modes that can be defined for a single application of n-bit block cipher in order to produce an n-bit compression function. -
Miss in the Middle
Miss in the middle By: Gal Leonard Keret Miss in the Middle Attacks on IDEA, Khufu and Khafre • Written by: – Prof. Eli Biham. – Prof. Alex Biryukov. – Prof. Adi Shamir. Introduction • So far we used traditional differential which predict and detect statistical events of highest possible probability. Introduction • A new approach is to search for events with probability one, whose condition cannot be met together (events that never happen). Impossible Differential • Random permutation: 휎 푀0 = 푎푛푦 퐶 표푓 푠푖푧푒 푀0. • Cipher (not perfect): 퐸 푀0 = 푠표푚푒 퐶 표푓 푠푖푧푒 푀0. • Events (푚 ↛ 푐) that never happen distinguish a cipher from a random permutation. Impossible Differential • Impossible events (푚 ↛ 푐) can help performing key elimination. • All the keys that lead to impossibility are obviously wrong. • This way we can filter wrong key guesses and leaving the correct key. Enigma – for example • Some of the attacks on Enigma were based on the observation that letters can not be encrypted to themselves. 퐸푛푖푔푚푎(푀0) ≠ 푀0 In General • (푀0, 퐶1) is a pair. If 푀0 푀0 → 퐶1. • 푀 ↛ 퐶 . 0 0 Some rounds For any key • ∀ 푘푒푦| 퐶1 → 퐶0 ↛ is an impossible key. Cannot lead to 퐶0. Some rounds Find each keys Decrypt 퐶1back to 퐶0. IDEA • International Data Encryption Algorithm. • First described in 1991. • Block cipher. • Symmetric. • Key sizes: 128 bits. • Block sizes: 64 bits. ⊕ - XOR. ⊞ - Addition modulo 216 ⊙ - Multiplication modulo 216+1 Encryption security • Combination of different mathematical groups. • Creation of "incompatibility“: ∗ • 푍216+1 → 푍216 ∗ • 푍216 → 푍216+1 ∗ ∗ Remark: 푍216+1 doesn’t contain 0 like 푍216 , so in 푍216+1 0 will be converted to 216 since 0 ≡ 216(푚표푑 216). -

Development of the Advanced Encryption Standard
Volume 126, Article No. 126024 (2021) https://doi.org/10.6028/jres.126.024 Journal of Research of the National Institute of Standards and Technology Development of the Advanced Encryption Standard Miles E. Smid Formerly: Computer Security Division, National Institute of Standards and Technology, Gaithersburg, MD 20899, USA [email protected] Strong cryptographic algorithms are essential for the protection of stored and transmitted data throughout the world. This publication discusses the development of Federal Information Processing Standards Publication (FIPS) 197, which specifies a cryptographic algorithm known as the Advanced Encryption Standard (AES). The AES was the result of a cooperative multiyear effort involving the U.S. government, industry, and the academic community. Several difficult problems that had to be resolved during the standard’s development are discussed, and the eventual solutions are presented. The author writes from his viewpoint as former leader of the Security Technology Group and later as acting director of the Computer Security Division at the National Institute of Standards and Technology, where he was responsible for the AES development. Key words: Advanced Encryption Standard (AES); consensus process; cryptography; Data Encryption Standard (DES); security requirements, SKIPJACK. Accepted: June 18, 2021 Published: August 16, 2021; Current Version: August 23, 2021 This article was sponsored by James Foti, Computer Security Division, Information Technology Laboratory, National Institute of Standards and Technology (NIST). The views expressed represent those of the author and not necessarily those of NIST. https://doi.org/10.6028/jres.126.024 1. Introduction In the late 1990s, the National Institute of Standards and Technology (NIST) was about to decide if it was going to specify a new cryptographic algorithm standard for the protection of U.S. -

Cryptanalysis of a Reduced Version of the Block Cipher E2
Cryptanalysis of a Reduced Version of the Block Cipher E2 Mitsuru Matsui and Toshio Tokita Information Technology R&D Center Mitsubishi Electric Corporation 5-1-1, Ofuna, Kamakura, Kanagawa, 247, Japan [email protected], [email protected] Abstract. This paper deals with truncated differential cryptanalysis of the 128-bit block cipher E2, which is an AES candidate designed and submitted by NTT. Our analysis is based on byte characteristics, where a difference of two bytes is simply encoded into one bit information “0” (the same) or “1” (not the same). Since E2 is a strongly byte-oriented algorithm, this bytewise treatment of characteristics greatly simplifies a description of its probabilistic behavior and noticeably enables us an analysis independent of the structure of its (unique) lookup table. As a result, we show a non-trivial seven round byte characteristic, which leads to a possible attack of E2 reduced to eight rounds without IT and FT by a chosen plaintext scenario. We also show that by a minor modification of the byte order of output of the round function — which does not reduce the complexity of the algorithm nor violates its design criteria at all —, a non-trivial nine round byte characteristic can be established, which results in a possible attack of the modified E2 reduced to ten rounds without IT and FT, and reduced to nine rounds with IT and FT. Our analysis does not have a serious impact on the full E2, since it has twelve rounds with IT and FT; however, our results show that the security level of the modified version against differential cryptanalysis is lower than the designers’ estimation.