Vote Counting, Technology, and Unintended Consequences
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Black Box Voting Ballot Tampering in the 21St Century
This free internet version is available at www.BlackBoxVoting.org Black Box Voting — © 2004 Bev Harris Rights reserved to Talion Publishing/ Black Box Voting ISBN 1-890916-90-0. You can purchase copies of this book at www.Amazon.com. Black Box Voting Ballot Tampering in the 21st Century By Bev Harris Talion Publishing / Black Box Voting This free internet version is available at www.BlackBoxVoting.org Contents © 2004 by Bev Harris ISBN 1-890916-90-0 Jan. 2004 All rights reserved. No part of this book may be reproduced in any form whatsoever except as provided for by U.S. copyright law. For information on this book and the investigation into the voting machine industry, please go to: www.blackboxvoting.org Black Box Voting 330 SW 43rd St PMB K-547 • Renton, WA • 98055 Fax: 425-228-3965 • [email protected] • Tel. 425-228-7131 This free internet version is available at www.BlackBoxVoting.org Black Box Voting © 2004 Bev Harris • ISBN 1-890916-90-0 Dedication First of all, thank you Lord. I dedicate this work to my husband, Sonny, my rock and my mentor, who tolerated being ignored and bored and galled by this thing every day for a year, and without fail, stood fast with affection and support and encouragement. He must be nuts. And to my father, who fought and took a hit in Germany, who lived through Hitler and saw first-hand what can happen when a country gets suckered out of democracy. And to my sweet mother, whose an- cestors hosted a stop on the Underground Railroad, who gets that disapproving look on her face when people don’t do the right thing. -

Electronic Voting & Counting Technologies
ELECTION TECHNOLOGY SERIES Electronic Voting & Counting Technologies A Guide to Conducting Feasibility Studies Ben Goldsmith Senior Electoral Advisor Electronic Voting & Counting Technologies Ben Goldsmith Senior Electoral Advisor International Foundation for Electoral Systems Electronic Voting & Counting Technologies A Guide to Conducting Feasibility Studies Ben Goldsmith Senior Electoral Advisor May 2011 Any opinions, findings, conclusions or recommendations expressed in this publication are those of the author(s) and do not necessarily reflect the views of the International Foundation for Electoral Systems. ACKNOWLEDGEMENTS Electronic Voting & Counting Technologies: A Guide to Conducting Feasibility Studies Ben Goldsmith © 2011 by IFES. All rights reserved. International Foundation for Electoral Systems (IFES) 1850 K Street, NW Fifth Floor Washington, D.C. 20006 U.S.A. Notice of rights All rights reserved. No part of this report can be reproduced or transmitted in any form by any means without the prior permission of the publisher. Printed in USA ISBN: 1-931459-64-9 Photo Credits Cover: Ripple Effect Productions Page 36: Ripple Effect Productions Garie Briones Page 51: Lean Pasion Page 1: John Lawrence Page 59: Everton Bahl Grabski Page 9: Francisco Samões Page 70: Júlio Henrique da Silva Lopes Page 17: Ripple Effect Productions Page 75: Oliver Scott-Tomlin Page 25: João Cesário ACKNOWLEDGEMENTS Thanks are due to a number of colleagues and friends who were kind enough to take the time to review and comment on the initial drafts of this guide. Special thanks are due to Susanne Caarls, Peter Erben, Juhani Grossmann, Ole Holtved, Manuel Kripp, Ronan McDermott, Vladimir Pran, Amna Qayyum and Mike Yard, all of whom provided invaluable suggestions for improvements and additional areas which needed to be covered by the guide. -

On the Notion of “Software Independence” in Voting Systems
On the notion of “software independence” in voting systems Ronald L. Rivest John P. Wack Computer Science and Artificial Intelligence Laboratory Massachusetts Institute of Technology Cambridge, MA 02139 [email protected] National Institute of Standards and Technology (NIST) Information Technology Laboratory Gaithersburg, MD 20899 [email protected] DRAFT Version July 28, 2006 Abstract. This paper defines and explores the notion of “software in- dependence” in voting systems: A voting system is software-independent if an undetected change or error in its software cannot cause an undetectable change or error in an election outcome. We propose that software independent voting systems should be pre- ferred, and software-dependent voting systems should be avoided. VVPAT and some cryptographically-based voting systems are software-independent. Variations and implications of this definition are explored. This white paper is also for discussion by the Technical Guidelines Devel- opment Committee (TGDC) in its development of the Voluntary Voting System Guidelines (VVSG) of 2007. 1 Introduction The main purpose of this paper is to introduce and carefully define the ter- minology of “software-independent” and “software-dependent” voting systems, and to discuss their properties. This paper is definitional in character; there are no “results” as such. The contribution is to help provide crisp terminology for discussing voting systems and some recommendations for its usage in the VVSG 2007, currently under development by NIST and the TGDC. This paper starts by describing the problem that software-independence ad- dresses: complex and difficult-to-test software in voting systems. It then defines what constitutes a software-independent approach to voting system design. -
Randomocracy
Randomocracy A Citizen’s Guide to Electoral Reform in British Columbia Why the B.C. Citizens Assembly recommends the single transferable-vote system Jack MacDonald An Ipsos-Reid poll taken in February 2005 revealed that half of British Columbians had never heard of the upcoming referendum on electoral reform to take place on May 17, 2005, in conjunction with the provincial election. Randomocracy Of the half who had heard of it—and the even smaller percentage who said they had a good understanding of the B.C. Citizens Assembly’s recommendation to change to a single transferable-vote system (STV)—more than 66% said they intend to vote yes to STV. Randomocracy describes the process and explains the thinking that led to the Citizens Assembly’s recommendation that the voting system in British Columbia should be changed from first-past-the-post to a single transferable-vote system. Jack MacDonald was one of the 161 members of the B.C. Citizens Assembly on Electoral Reform. ISBN 0-9737829-0-0 NON-FICTION $8 CAN FCG Publications www.bcelectoralreform.ca RANDOMOCRACY A Citizen’s Guide to Electoral Reform in British Columbia Jack MacDonald FCG Publications Victoria, British Columbia, Canada Copyright © 2005 by Jack MacDonald All rights reserved. No part of this publication may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by an information storage and retrieval system, now known or to be invented, without permission in writing from the publisher. First published in 2005 by FCG Publications FCG Publications 2010 Runnymede Ave Victoria, British Columbia Canada V8S 2V6 E-mail: [email protected] Includes bibliographical references. -

PDF of Law As Amended to 14/12/2010
REPUBLIC OF LITHUANIA LAW ON REFERENDUM 4 June 2002 No IX-929 (As last amended on 14 December 2010 — No XI-1229) Vilnius The Seimas of the Republic of Lithuania, relying upon the legally established, open, just, harmonious, civic society and principles of a law - based State and the Constitution: the provisions of Article 2 that “the State of Lithuania shall be created by the People. Sovereignty shall belong to the Nation”; the provision of Article 3 that “no one may limit or restrict the sovereignty of the Nation and make claims to the sovereign powers belonging to the entire Nation”; the provision of Article 4 that “the Nation shall execute its supreme sovereign power either directly or through its democratically elected representatives”; and the provision of Article 9 that “the most significant issues concerning the life of the State and the Nation shall be decided by referendum”, passes this Law. CHAPTER I GENERAL PROVISIONS Article 1. Purpose of the Law This Law shall establish the procedure of implementing the right of the citizens of Lithuania to a referendum, the type of referendum and initiation, announcement, organising and conducting thereof. 2. The citizens of the Republic of Lithuania (hereinafter - citizens) or the Seimas of the Republic of Lithuania (hereinafter - Seimas) shall decide the importance of the proposed issue in the life of the State and the People in accordance with the Constitution of the Republic of Lithuania and this Law. Article 2. General Principles of Referendum 1. Taking part in the referendum shall be free and based upon the democratic principles of the right of elections: universal, equal and direct suffrage and secret ballot. -
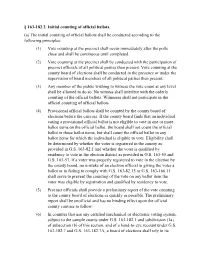
§ 163-182.2. Initial Counting of Official Ballots. (A) the Initial Counting Of
§ 163-182.2. Initial counting of official ballots. (a) The initial counting of official ballots shall be conducted according to the following principles: (1) Vote counting at the precinct shall occur immediately after the polls close and shall be continuous until completed. (2) Vote counting at the precinct shall be conducted with the participation of precinct officials of all political parties then present. Vote counting at the county board of elections shall be conducted in the presence or under the supervision of board members of all political parties then present. (3) Any member of the public wishing to witness the vote count at any level shall be allowed to do so. No witness shall interfere with the orderly counting of the official ballots. Witnesses shall not participate in the official counting of official ballots. (4) Provisional official ballots shall be counted by the county board of elections before the canvass. If the county board finds that an individual voting a provisional official ballot is not eligible to vote in one or more ballot items on the official ballot, the board shall not count the official ballot in those ballot items, but shall count the official ballot in any ballot items for which the individual is eligible to vote. Eligibility shall be determined by whether the voter is registered in the county as provided in G.S. 163-82.1 and whether the voter is qualified by residency to vote in the election district as provided in G.S. 163-55 and G.S. 163-57. If a voter was properly registered to vote in the election by the county board, no mistake of an election official in giving the voter a ballot or in failing to comply with G.S. -

IC 3-11.5-5 Chapter 5. Counting of Absentee Ballots Cast on Paper Ballots
IC 3-11.5-5 Chapter 5. Counting of Absentee Ballots Cast on Paper Ballots IC 3-11.5-5-1 Applicability of chapter; counties of application Sec. 1. (a) This chapter applies in a county only if the county election board adopts a resolution making this chapter applicable in the county. (b) A copy of a resolution adopted under this section shall be filed with the election division. (c) A county election board may not adopt a resolution under this section less than: (1) sixty (60) days before an election is to be conducted; or (2) fourteen (14) days after an election has been conducted. (d) A resolution adopted under this section takes effect immediately and may only be rescinded by the unanimous vote of the entire membership of the county election board. As added by P.L.3-1993, SEC.176 and P.L.19-1993, SEC.2. Amended by P.L.2-1996, SEC.202; P.L.3-1997, SEC.335. IC 3-11.5-5-2 Applicability of chapter; paper ballot cast votes Sec. 2. This chapter applies to the counting of absentee ballots cast on paper ballots. As added by P.L.3-1993, SEC.176 and P.L.19-1993, SEC.2. IC 3-11.5-5-3 Time for counting ballots Sec. 3. (a) Except as provided in subsection (b), immediately after: (1) the couriers have returned the certificate from a precinct under IC 3-11.5-4-9; and (2) the absentee ballot counters or the county election board have made the findings required under IC 3-11-10 and IC 3-11.5-4 for the absentee ballots cast by voters of the precinct and deposited the accepted absentee ballots in the envelope required under IC 3-11.5-4-12; the absentee ballot counters shall, in a central counting location designated by the county election board, count the absentee ballot votes for each candidate for each office and on each public question in the precinct. -

Cost of Counting the Vote
Cost of Counting the Vote The Price of Upgrading Voting Systems in 43 U.S. Counties By Aquene Freechild and Hamdi Soysal, Public Citizen’s Democracy Is For People Campaign May 31, 2018 - Amid serious concerns about whether our elections are secure from hackers and computer error, many state and local governments are looking to replace out-of-date paperless voting systems with paper ballot and electronic scanner systems. Pricing of voting equipment is often opaque, and in many cases, prices are negotiated on a local level. To bring some much-needed clarity to the issue, this report examines how much 43 county governments in 10 states paid for voting equipment. With this information in hand, local election officials and citizens can make the most of limited election equipment dollars. The states are: California, Florida, Iowa, Kentucky, Minnesota, Ohio, Oregon, Pennsylvania, Texas and Virginia. Our key finding: While most precinct ballot scanners cost around $5,000 to $6,000, some counties have been able to negotiate more favorable pricing. However, a few counties paid a much higher than average price for their equipment. Our key conclusion: It’s important that counties band together or engage state authorities where appropriate to negotiate prices and get the best contract terms for voting equipment. Leasing equipment is an option for county officials to address the security threats quickly without committing to buying new systems on a short time frame. Limited Federal Funding In the 2018 federal spending bill passed by Congress in March 2018, lawmakers made $380 million in election security funding available to states for replacing paperless voting systems, implementing post-election audits and securing election databases. -

The New Jersey Voting-Machine Lawsuit and the AVC Advantage DRE Voting Machine
The New Jersey Voting-machine Lawsuit and the AVC Advantage DRE Voting Machine Andrew W. Appel∗ Maia Ginsburg Harri Hursti Brian W. Kernighan Princeton University Princeton University Princeton University Christopher D. Richards Gang Tan Penny Venetis Princeton University Lehigh University Rutgers School of Law – Newark Abstract As a result of a public-interest lawsuit, by Court order we were able to study, for one month, the hardware and source code of the Sequoia AVC Advantage direct-recording electronic voting machine, which is used throughout New Jersey (and Louisiana), and the Court has permitted us to publicly describe almost everything that we were able to learn. In short, these machines are vulnerable to a wide variety of attacks on the voting process. It would not be in the slightest difficult for a moderately determined group or individual to mount a vote-stealing attack that would be successful and undetectable. 1 Litigation and legislation in New Jersey In October 2004 a group of public-interest plaintiffs, represented by Professor Penny Venetis of the Rutgers Law School, sued the State of New Jersey (in NJ Superior Court) over the State’s use of direct-recording electronic (DRE) voting machines in New Jersey. By 2004, most of New Jersey’s counties had adopted the Sequoia AVC Advantage full-face DRE. Currently 18 out of New Jersey’s 21 counties use this DRE. The plaintiffs argued that the use of DRE voting machines is illegal and unconstitutional: illegal, because they violate New Jersey election laws requiring that all votes be counted accurately and that voting machines be thoroughly tested, accurate, and reliable; and unconstitutional, because they violate the New Jersey constitution’s requirement that all votes count.1 The plaintiffs argued that one cannot trust a paperless DRE machine to count the vote. -

Supreme Court of the United States ______
No. 19-1399 IN THE Supreme Court of the United States ______________________________ SHELBY ADVOCATES FOR VALID ELECTIONS, ET AL., Petitioners, v. TRE HARGETT, ET AL. Respondents. ______________________________ On Petition for a Writ of Certiorari to the United States Court of Appeals for the Sixth Circuit ______________________________ BRIEF OF AMICI CURIAE INDIVIDUAL ELECTION SECURITY EXPERTS IN SUPPORT OF CERTIORARI ______________________________ Courtney Hostetler John D. Graubert Ronald Fein Counsel of Record John Bonifaz Megan C. Keenan Ben Clements Ryan Miller FREE SPEECH FOR PEOPLE Jeremy Patashnik 1320 Centre St. #405 COVINGTON & BURLING LLP Newton, MA 02459 One CityCenter (617) 249-3015 850 Tenth Street, NW Washington, DC 20001 [email protected] (202) 662-6000 July 22, 2020 Counsel for Amici Curiae i TABLE OF CONTENTS Page TABLE OF AUTHORITIES ....................................... ii INTERESTS OF AMICI CURIAE .............................. 1 SUMMARY OF ARGUMENT ..................................... 2 ARGUMENT ............................................................... 4 I. ABSENT IMMEDIATE REVIEW, VOTING MACHINES IN SHELBY COUNTY WILL CONTINUE TO CAUSE FLAWED ELECTIONS. ...................................... 4 A. The Voting Machines At Issue Are Fundamentally Deficient. ............................5 B. The Voting Machines At Issue Cannot Be Reliably Audited. .................................. 12 C. As a Result of the Sixth Circuit’s Ruling, the Voting Machines At Issue Will Continue To Harm Voters. ................. 15 II. THE SIXTH CIRCUIT’S DECISION CONFLICTS WITH ELEVENTH CIRCUIT PRECEDENT PERMITTING PLAINTIFFS TO CHALLENGE SIMILAR HARMS TO THEIR VOTING RIGHTS. ........... 17 CONCLUSION .......................................................... 27 APPENDIX: List of Individual Election Security Experts ............ 1a ii TABLE OF AUTHORITIES Page(s) Cases Andrade v. NAACP of Austin, 345 S.W.3d 1 (Tex. 2011) ..................................... 20 City of Los Angeles v. Lyons, 461 U.S. 95 (1983) ............................................... -

Election Fraud Facts & Details
Election Fraud Facts & Details Supporting Files for all items listed can be found at the following URL: https://ufile.io/by3q159v 1 FOREIGN INFLUENCE & NATIONAL SECURITY CONCERNS IN US ELECTIONS 1.1 The core software utilized by Dominion, the 2nd largest US voting machine vendor, originates from intellectual property of Smartmatic; a company that was founded in communist Venezuala with links to Chavez. A. Smartmatic Ties to Hugo Chávez Warned About in 2006 B. SmartMatic Sells Sequoia Voting Systems to US Holding Company After CFIUS Probe C. Sequoia Admits that while they can change the source code (e.g. Software), Smartmatic still owns the intellectual property of the software. D. Dominion Buys Sequoia from Smartmatic and Diebold from ES&S 1.2 ES&S, Dominion, and Hart Intercivic represent 92% of voting machine market and have a long history of significant security vulnerabilities that could be exploited by a nation state in ways that would be difficult to detect. E. Map - Voting Machine Usage in the US F. Defcon 27 - Voting Machine Hacking Village - Vulnerablity Report G. Defcon 26 - Voting Machine Hacking Village - Vulnerablity Report.pdf H. History of ES&S and Diebold (Now Dominion) Vulnerabilities and Voting Inconsistiencies I. Antrim-Michigan-Forensics-Report-121320-v2-Redacted 1.3 An affidavit and scholarly statistical paper attest to Smartmatic rigging Venezualian elections. Smartmatic has also been accused of rigging elections in the Philippines and India J. Venezuala Smartmatic Affidavit K. Statistical Science - 2011 - Volume 26 - Number 4 - Analysis of the 2004 Venezuala Referendum - Official Results Verses the Petition Signatures L. Smartmatic Voting Technology Firm Linked to Alleged Fraud in Elections in Philippines, Venezuela M. -
Security Evaluation of ES&S Voting Machines and Election
Security Evaluation of ES&S Voting Machines and Election Management System Adam Aviv Pavol Cernˇ y´ Sandy Clark Eric Cronin Gaurav Shah Micah Sherr Matt Blaze faviv,cernyp,saender,ecronin,gauravsh,msherr,[email protected] Department of Computer and Information Science University of Pennsylvania Abstract EVEREST was the first major study of ES&S voting sys- tems, despite the system’s popularity (ES&S claims to be This paper summarizes a security analysis of the DRE the world’s largest e-voting systems vendor [1], support- and optical scan voting systems manufactured by Election ing more than 67 million voter registrations with 97,000 Systems and Software (ES&S), as used in Ohio (and many touchscreen voting machines installed in 20 states and other jurisdictions inside and outside the US). We found 30,000 optical ballot readers present in 43 states [4]), and numerous exploitable vulnerabilities in nearly every com- only the second comprehensive study that examined all ponent of the ES&S system. These vulnerabilities enable components – from backend registration systems to fron- attacks that could alter or forge precinct results, install tend ballot casting – of any electronic voting system. In a corrupt firmware, and erase audit records. Our analysis ten week period, our seven-member team was tasked with focused on architectural issues in which the interactions analyzing the nearly 670,000 lines of source code that between various software and hardware modules leads to comprise the ES&S system, encompassing twelve pro- systemic vulnerabilities that do not appear to be easily gramming languages and five hardware platforms1.