"Processing Dangerous Paths– on Security And
Total Page:16
File Type:pdf, Size:1020Kb

Load more
Recommended publications
-

PDF Studio 2019 User Guide
Qoppa Software PDF Studio 2019 User Guide Affordable, Powerful PDF Software for Windows, Mac, Linux Copyright © 2002-Present Qoppa Software. All rights reserved Table of Contents Welcome to PDF Studio ............................................................................................................... 19 Previous Version User Guides ...................................................................................................... 21 What's New ................................................................................................................................... 21 System Requirements.................................................................................................................... 23 PDF Studio Installation Instructions ............................................................................................. 25 Registration / Unregistration / Transfer ........................................................................................ 26 Removing Demo Watermarks ....................................................................................................... 28 Getting Started with PDF Studio .................................................................................................. 29 Welcome Screen ........................................................................................................................... 30 PDF Studio Ribbon Toolbar ......................................................................................................... 32 Ribbon Toolbar -
Vulnerability Report Attacks Bypassing Confidentiality in Encrypted PDF
Vulnerability Report Attacks bypassing confidentiality in encrypted PDF Jens M¨uller1, Fabian Ising2, Vladislav Mladenov1, Christian Mainka1, Sebastian Schinzel2, J¨orgSchwenk1 May 16, 2019 1Chair for Network and Data Security 2FH M¨unsterUniversity of Applied Sciences Abstract In this report, we analyze PDF encryption and show two novel techniques for breaking the confidentiality of encrypted documents. Firstly, we abuse the PDF feature of partially encrypted documents to wrap the encrypted part of the document within attacker-controlled content and therefore, exfiltrate the plaintext once the document is opened by a legitimate user. Secondly, we abuse a flaw in the PDF encryption specification allowing an attacker to arbitrarily manipulate encrypted content without knowing the cor- responding key/password. The only requirement is one single block of known plaintext, which we show is fulfilled by design. By using exfiltration channels our attacks allow the recovery of the entire plaintext or parts of it within an encrypted document. The attacks rely only on standard compliant PDF features. We evaluated our attacks on 27 widely used PDF viewers and found all of them vulnerable. 1 Contents 1 Background4 1.1 Portable Document Format (PDF) . .4 1.2 PDF Encryption . .6 1.3 PDF Interactive Features . .7 2 Attacker Model8 3 PDF Encryption: Security Analysis9 3.1 Partial Encryption . .9 3.2 CBC Malleability . 10 3.3 PDF Interactive Features . 12 4 How To Break PDF Encryption 14 4.1 Direct Exfiltration (Attack A) . 14 4.1.1 Requirements . 15 4.1.2 Direct Exfiltration through PDF Forms (A1) . 15 4.1.3 Direct Exfiltration via Hyperlinks (A2) . -
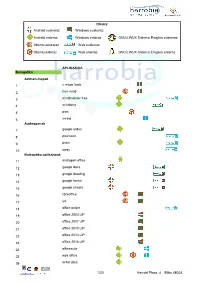
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -

Curso Básico Sobre Uso Docente Del Software Libre
Curso básico sobre uso docente del Software Libre 11 de enero de 2018 - 8 de febrero de 2018 Plan FIDO 2018-2020 Autora: María Isabel García Arenas Contacto: [email protected] Presentación del Curso - Maribel García Arenas - José Alonso Arias 2 Contenidos 1. Qué es el software Libre a. Cómo comprobar si lo que usamos es software libre o software gratuito b. Tipos de licencias que nos podemos encontrar c. Por qué es la mejor opción para impartir docencia d. Alternativas, cómo buscarlas y cómo descargarlas e instalarlas 2. Libreoffice Write a fondo a. Tratamiento de estilos dentro de un documento b. Definición de nuevos estilos c. Tratamiento de la bibliografía d. Generación automática de índices, tablas de figuras, etc. 3. Libreoffice Calc a fondo a. Tratamiento de fórmulas b. Tratamiento de plantillas c. Plantillas de corrección de exámenes tipo test 3 Contenidos 4. Derechos de autor a. Qué sí y qué no podemos hacer b. Generación de materiales docentes respetando los derechos de autor c. Búsqueda de imágenes y recursos que sí podemos usar 5. Otros tipos de herramientas a. Imágenes (editores, capturadores b. Gestores de copias de seguridad c. Clientes de correo 4 Planificación 11 18 25 1 8 ene ene ene feb feb Qué es Software Libre Libreoffice Writer Libreoffice Calc Derechos de autor Otras herramientas Maribel José Alonso Maribel Maribel José Alonso Horario de 9:30 a 13:30 5 Día 1: ¿Qué es Software Libre? 6 Índice 1. ¿Qué es el software Libre? 2. Cómo comprobar si lo que usamos es software libre o sólo software gratuito 3. -
Living Without Google on Android
Alternative for Google Apps on Android - living without Google on Android Android without any Google App? What to use instead of Hangouts, Map, Gmail? Is that even possible? And why would anyone want to live without Google? I've been using a lot of different custom ROMs on my devices, so far the two best: plain Cyanogenmod 11 snapshot on the Nexus 4[^1], and MIUI 2.3.2 on the HTC Desire G7[^2]. All the others ( MUIU 5, MIUI 6 unofficial, AOKP, Kaos, Slim, etc ) were either ugly, unusable, too strange or exceptionally problematic on battery life. For a long time, the first step for me was to install the Google Apps, gapps packages for Plays Store, Maps, and so on, but lately they require so much rights on the phone that I started to have a bad taste about them. Then I started to look for alternatives. 1 of 5 So, what to replace with what? Play Store I've been using F-Droid[^3] as my primary app store for a while now, but since it's strictly Free Software[^4] store only, sometimes there's just no app present for your needs; aptoide[^5] comes very handy in that cases. Hangouts I never liked Hangouts since the move from Gtalk although for a little while it was exceptional for video - I guess it ended when the mass started to use it in replacement of Skype and its recent suckyness. For chat only, check out: ChatSecure[^6], Conversations[^7] or Xabber[^8]. All of them is good for Gtalk-like, oldschool client and though Facebook can be configured as XMPP as well, I'd recommend Xabber for that, the other two is a bit flaky with Facebook. -

(Bachelor, Master, Or Phd) and Which Software Tools to Use How to Write A
2.6.2016 How to write a thesis (Bachelor, Master, or PhD) and which software tools to use SciPlore Home Projects Publications About & Contact How to write a thesis (Bachelor, Master, or PhD) and Home / HOW TOs, sciplore mindmapping / which software tools to use How to write a thesis (Bachelor, Master, or PhD) and which software tools to use Previous Next How to write a thesis (Bachelor, Master, or PhD) and which software tools to use Available translations: Chinese (thanks to Chen Feng) | Portuguese (thanks to Marcelo Cruz dos Santos) | Russian (thanks to Sergey Loy) send us your translation Writing a thesis is a complex task. You need to nd related literature, take notes, draft the thesis, and eventually write the nal document and create the bibliography. Many books explain how to perform a literature survey and how to write scholarly literature in general and a thesis in particular (e.g. [1-9]). However, these books barely, if at all, cover software tools that help in performing these tasks. This is surprising, because great software tools that can facilitate the daily work of students and researchers are available and many of them for free. In this tutorial, we present a new method to reviewing scholarly literature and drafting a thesis using mind mapping software, PDF readers, and reference managers. This tutorial focuses on writing a PhD thesis. However, the presented methods are likewise applicable to planning and writing a bachelor thesis or master thesis. This tutorial is special, because it integrates the management of PDF les, the relevant content in PDFs (bookmarks), and references with mind mapping and word processing software. -
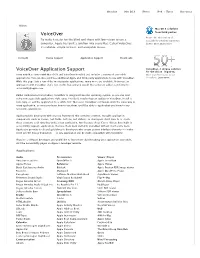
Apple Has Built a Solution Into Every Mac
Overview Mac OS X iPhone iPod + iTunes Resources Vision Mac OS X solutions VoiceOver from third parties. Browse the wide variety of To make it easier for the blind and those with low-vision to use a accessibility solutions supported computer, Apple has built a solution into every Mac. Called VoiceOver, by Mac OS X. Learn more it’s reliable, simple to learn, and enjoyable to use. In Depth Device Support Application Support Downloads VoiceOver Application Support VoiceOver. A unique solution for the vision-impaired. Every new Mac comes with Mac OS X and VoiceOver installed and includes a variety of accessible More than 50 reasons to use applications. You can also purchase additional Apple and third-party applications to use with VoiceOver. VoiceOver. Learn more While this page lists a few of the most popular applications, many more are available. If you use an application with VoiceOver that’s not on this list, and you would like to have it added, send email to [email protected]. Unlike traditional screen readers, VoiceOver is integrated into the operating system, so you can start using new accessible applications right away. You don’t need to buy an update to VoiceOver, install a new copy, or add the application to a “white list.” Moreover, VoiceOver commands work the same way in every application, so once you learn how to use them, you’ll be able to apply what you know to any accessible application. Apple provides developers with a Cocoa framework that contains common, reusable application components (such as menus, text fields, buttons, and sliders), so developers don’t have to re-create these elements each time they write a new application. -

Ghostscript and Mupdf Status Openprinting Summit April 2016
Ghostscript and MuPDF Status OpenPrinting Summit April 2016 Michael Vrhel, Ph.D. Artifex Software Inc. San Rafael CA Outline Ghostscript overview What is new with Ghostscript MuPDF overview What is new with MuPDF MuPDF vs Ghostscript MuJS, GSView The Basics Ghostscript is a document conversion and rendering engine. Written in C ANSI 1989 standard (ANS X3.159-1989) Essential component of the Linux printing pipeline. Dual AGPL/Proprietary licensed. Artifex owns the copyright. Source and documentation available at www.ghostscript.com Graphical Overview PostScript PCL5e/c with PDF 1.7 XPS Level 3 GL/2 and RTL PCLXL Ghostscript Graphics Library High level Printer drivers: Raster output API: Output drivers: Inkjet TIFF PSwrite PDFwrite Laser JPEG XPSwrite Custom etc. CUPS Devices Understanding devices is a major key to understanding Ghostscript. Devices can have high-level functionality. e.g. pdfwrite can handle text, images, patterns, shading, fills, strokes and transparency directly. Graphics library has “default” operations. e.g. text turns into bitmaps, images decomposed into rectangles. In embedded environments, calls into hardware can be made. Raster devices require the graphics library to do all the rendering. Relevant Changes to GS since last meeting…. A substantial revision of the build system and GhostPDL directory structure (9.18) GhostPCL and GhostXPS "products" are now built by the Ghostscript build system "proper" rather than having their own builds (9.18) New method of internally inserting devices into the device chain developed. Allows easier implementation of “filter” devices (9.18) Implementation of "-dFirstPage"/"-dLastPage" with all input languages (9.18) Relevant Changes to GS since last meeting…. -

Breaking PDF Encryption
Practical Decryption exFiltration: Breaking PDF Encryption Jens Müller Fabian Ising Vladislav Mladenov [email protected] [email protected] [email protected] Ruhr University Bochum, Chair for Münster University of Applied Ruhr University Bochum, Chair for Network and Data Security Sciences Network and Data Security Christian Mainka Sebastian Schinzel Jörg Schwenk [email protected] [email protected] [email protected] Ruhr University Bochum, Chair for Münster University of Applied Ruhr University Bochum, Chair for Network and Data Security Sciences Network and Data Security ABSTRACT Home/Trusted Environment The Portable Document Format, better known as PDF, is one of the Decrypted Document 1. Victim opens 2. Exfiltrating Tax Declaration decrypted content most widely used document formats worldwide, and in order to en- an encrypted PDF file Scrooge McDuck with their password via the Internet sure information confidentiality, this file format supports document TOP SECRET Victim encryption. In this paper, we analyze PDF encryption and show Attacker two novel techniques for breaking the confidentiality of encrypted Victim’s PC documents. First, we abuse the PDF feature of partially encrypted documents to wrap the encrypted part of the document within Figure 1: An overview of the attack scenario: The victim attacker-controlled content and therefore, exfiltrate the plaintext opens an encrypted PDF document and unintentionally once the document is opened by a legitimate user. Second, we abuse leaks the decrypted content to an attacker-controlled server. a flaw in the PDF encryption specification to arbitrarily manipulate The encrypted PDF file was manipulated by the attacker be- encrypted content. -

Complete Issue 40:3 As One
TUGBOAT Volume 40, Number 3 / 2019 General Delivery 211 From the president / Boris Veytsman 212 Editorial comments / Barbara Beeton TEX Users Group 2019 sponsors; Kerning between lowercase+uppercase; Differential “d”; Bibliographic archives in BibTEX form 213 Ukraine at BachoTEX 2019: Thoughts and impressions / Yevhen Strakhov Publishing 215 An experience of trying to submit a paper in LATEX in an XML-first world / David Walden 217 Studying the histories of computerizing publishing and desktop publishing, 2017–19 / David Walden Resources 229 TEX services at texlive.info / Norbert Preining 231 Providing Docker images for TEX Live and ConTEXt / Island of TEX 232 TEX on the Raspberry Pi / Hans Hagen Software & Tools 234 MuPDF tools / Taco Hoekwater 236 LATEX on the road / Piet van Oostrum Graphics 247 A Brazilian Portuguese work on MetaPost, and how mathematics is embedded in it / Estev˜aoVin´ıcius Candia LATEX 251 LATEX news, issue 30, October 2019 / LATEX Project Team Methods 255 Understanding scientific documents with synthetic analysis on mathematical expressions and natural language / Takuto Asakura Fonts 257 Modern Type 3 fonts / Hans Hagen Multilingual 263 Typesetting the Bangla script in Unicode TEX engines—experiences and insights Document Processing / Md Qutub Uddin Sajib Typography 270 Typographers’ Inn / Peter Flynn Book Reviews 272 Book review: Hermann Zapf and the World He Designed: A Biography by Jerry Kelly / Barbara Beeton 274 Book review: Carol Twombly: Her brief but brilliant career in type design by Nancy Stock-Allen / Karl -
Easypacks - Your Easyinstall® Application Portal
EasyPacks - your EasyInstall® application portal Pre-packaged software and applications for EasyInstall, ready for download. Why spend precious time to pack, update and test standard software and applica- tions when it is already done. With a few clicks you can download the latest soft- ware from EasyPacks. Errors and security vulnerabilities is constantly found in standard applications and the software supplier issues updates on a regular basis - we keep an eye on this for you .... It can be fatal if standard applications are not kept up to date. Hackers are unfor- tunately extremely talented to exploit these vulnerabilities. As an example, if Java is not updated, which in itself is a huge security risk, it can cause lack of access to banking and other public services. All software is packed, tested, virus free and quality assured by IXP Data. We have more than 150 updated application packages ready for you and more keep coming. We ensure that packets are continuously updated and we will send you an e-mail when new downloads are ready. On the EasyPacks website you can contact us with suggestion for additional standard applications for EasyPacks. EasyPacks is a subscription service which is settled by number of EasyInstall li- censes. The subscription runs for 1 year. System requirements: EasyPacks require EasyInstall version 5 or higher IXP Data ApS • Søndre Alle 9 • 4600 Køge • VAT 32749305 • 56275402 • [email protected] • www.ixpdata.com Selected application packages: Java, CutePDF, Adobe Reader, Adobe Flash Player, Apple QuickTime, -

PDF Studio 12 User Guide
Qoppa Software PDF Studio 12 User Guide Affordable, Powerful PDF Software for Windows, Mac, Linux Copyright © 2002-Present Qoppa Software. All rights reserved Table of Contents Welcome to PDF Studio ............................................................................................................... 17 What's New ................................................................................................................................... 19 System Requirements.................................................................................................................... 21 PDF Studio Installation Instructions ............................................................................................. 22 Registration / Unregistration / Transfer ........................................................................................ 24 Getting Started with PDF Studio .................................................................................................. 27 Welcome Screen ........................................................................................................................... 28 PDF Studio Toolbar ...................................................................................................................... 30 Mini Toolbar ................................................................................................................................. 38 Quick Properties Toolbar .............................................................................................................