Magic Quadrant for Security Information and Event Management
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

RALLY SOFTWARE DEVELOPMENT CORP. (Name of Subject Company (Issuer))
UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 SCHEDULE TO Tender Offer Statement under Section 14(d)(1) or 13(e)(1) of the Securities Exchange Act of 1934 RALLY SOFTWARE DEVELOPMENT CORP. (Name of Subject Company (Issuer)) GRAND PRIX ACQUIISITION CORP. (Names of Filing Persons (Offeror)) a wholly owned subsidiary of CA, INC. (Names of Filing Persons (Offeror)) Common Stock, par value $0.001 per share (Title of Class of Securities) 751198102 (CUSIP Number of Class of Securities) Michael Bisignano Executive Vice President and General Counsel CA, Inc. 520 Madison Avenue New York, NY 10022 (800) 225-5524 Copy to: Mike Ringler Wilson Sonsini Goodrich and Rosati P.C. One Market Plaza, Spear Tower, Suite 3300 San Francisco, CA 94105 (415) 947-2000 (Name, Address and Telephone Numbers of Persons Authorized to Receive Notices and Communications on Behalf of Filing Persons) CALCULATION OF FILING FEE Transaction Valuation Amount of Filing Fee Not applicable(1) Not applicable(1) (1) In accordance with General Instruction D to Schedule TO, a filing fee is not required in connection with this filing as it relates solely to a preliminary communication made before the commencement of a tender offer. ¨ Check the box if any part of the fee is offset as provided by Rule 0-11(a)(2) and identify the filing with which the offsetting fee was previously paid. Identify the previous filing by registration statement number, or the Form or Schedule and the date of its filing. Amount Previously Paid: None Filing Party: Not applicable Form or Registration No.: Not applicable Date Filed: Not applicable x Check the box if the filing relates solely to preliminary communications made before the commencement of a tender offer. -
PRODUCTS Bomgar (Lieberman) Security Software Suites Software 5.00%
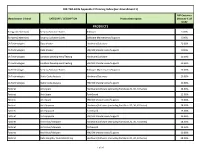
DIR-TSO-4135 Appendix C Princing Index (per Amendment 1) DIR Customer Manufacturer / Brand CATEGORY / DESCRIPTION Product Description Discount % off MSRP PRODUCTS Bomgar (Lieberman) Security Software Suites Software 5.00% Bomgar (Lieberman) Security Software Suites Software Maintenance/Support 5.00% CA Technologies Data Masker Hardware/Software 20.00% CA Technologies Data Masker HW/SW Maintenance/Support 9.00% CA Technologies Sandbox Development/Testing Hardware/Software 20.00% CA Technologies Sandbox Development/Testing HW/SW Maintenance/Support 20.00% CA Technologies Security Software Suites Software Maintenance/Support 20.00% CA Technologies Static Code Analysis Hardware/Software 20.00% CA Technologies Static Code Analysis HW/SW Maintenance/Support 20.00% Fortinet Anti-Spam Hardware/Software (excluding FortiGate 20, 30, 40 Series) 28.00% Fortinet Anti-Spam FortiGuard 15.00% Fortinet Anti-Spam HW/SW Maintenance/Support 10.00% Fortinet Anti-Spyware Hardware/Software (excluding FortiGate 20, 30, 40 Series) 28.00% Fortinet Anti-Spyware FortiGuard 15.00% Fortinet Anti-Spyware HW/SW Maintenance/Support 10.00% Fortinet Anti-Virus/Malware Hardware/Software (excluding FortiGate 20, 30, 40 Series) 28.00% Fortinet Anti-Virus/Malware FortiGuard 15.00% Fortinet Anti-Virus/Malware HW/SW Maintenance/Support 10.00% Fortinet Data Integrity/ Data Monitoring Hardware/Software (excluding FortiGate 20, 30, 40 Series) 28.00% 1 of 20 DIR-TSO-4135 Appendix C Princing Index (per Amendment 1) DIR Customer Manufacturer / Brand CATEGORY / DESCRIPTION Product -

Future Ready CA 2012 CSR 042682 CA CSR12 Execsummary V05 06/05/13 Page B
CA 2012 CSR 042682 CA_CSR12_ExecSummary_v05 06/05/13 page A CA Technologies Sustainability Summary 2012 CA Technologies is future ready CA 2012 CSR 042682 CA_CSR12_ExecSummary_v05 06/05/13 page B At CA Technologies, we believe that success comes from a relentless focus on innovation and execution. These concepts are not only vital to our software development, but also to our sustainability efforts. Innovation in sustainability means doing things better and smarter. It means making Since I last wrote to you about our the most of our resources, empowering people to do what they do best and using the power sustainability work at CA Technologies, we’re of diverse ideas to overcome challenges. And it means helping our customers do all of seeing the results of many of our programs this, too. and initiatives. People throughout the company are increasingly involved in working toward Combining innovation and execution makes us Future Ready—the theme of this report—as a our goals. company and in our sustainability efforts. By pursuing strategies that decouple environmental impact with business growth, we are driving efficiencies at our offices around the world and Our GHG emissions have decreased by 25% advancing toward our commitment to reduce greenhouse gas (GHG) emissions by 35% by 2020 since 2006. While our results are flat in 2012 (using a 2006 baseline). over 2011, our goal of a 35% reduction by 2020 remains realistic. We were also honored As companies seek to do more with less, they will find a worthy partner in CA Technologies. to place fifth out of 500 in Newsweek’s 2012 Our products help customers manage and secure their IT environments, from mainframe to Green Rankings of U.S. -
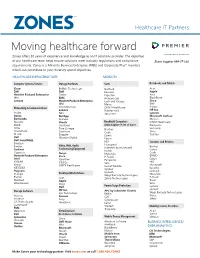
Moving Healthcare Forward Zones Offers 30 Years of Experience and Knowledge As an IT Solutions Provider
Healthcare IT Partners Moving healthcare forward Zones offers 30 years of experience and knowledge as an IT solutions provider. The expertise of our healthcare team helps ensure solutions meet industry regulations and compliance Zones Supplier #PP-IT-136 requirements. Zones is a Minority Business Enterprise (MBE) and Corporate Plus® member, which can contribute to your diversity spend objectives. HEALTHCARE INFRASTRUCTURE MOBILITY Computer Systems/Servers Storage Hardware Carts Notebooks and Tablets Cisco Buffalo Technology Bretford Acer Dell Dell Enovate Apple Hewlett Packard Enterprise Drobo Ergotron Asus IBM EMC Humanscale BlackBerry Lenovo Hewlett Packard Enterprise Lock and Charge Cisco IBM Metro Dell Networking & Communications Iron Mountain ONYX Healthcare Fujitsu Lenovo Rubbermaid HP Inc. Aruba NEC Spectrum Lenovo Avaya NetApp Microsoft Surface Barracuda Nutanix Motion Brocade Oracle Handheld Computers ONYX Healthcare Cisco Overland (Data Capture-Point of Care) Panasonic Citrix Pure Storage Brother Samsung CradlePoint Quantum Code Sony D-Link Seagate Dymo Toshiba Dell Western Digital Epson Dell SonicWALL HID Scanners and Printers Emerson Video, Web, Audio Honeywell Emulex Veeam Brother Conferencing Equipment Intermec by Honeywell Fortinet Kodak Canon Gigamon Avaya Motorola Code Hewlett Packard Enterprise Cisco P-Touch DYMO Intel ClearOne Panasonic Epson IOGEAR LifeSize Sato HID Kemp ONYX Healthcare Socket Mobile Honeywell NETGEAR Symbol Kyocera Polycom Lexmark Desktops/Workstations Unitech Q-Logic Wasp Barcode Technologies Motorola -
CA Amazon Web Services Monitoring
WHITE PAPER | NOVEMBER 2016 Amazon Web Services Monitoring The emerging opportunities for service providers and how CA Unified Infrastructure Management can help 2 | WHITE PAPER: AMAZON WEB SERVICES MONITORING ca.com Table of Contents Executive Summary 3 Cloud Services: A Key Element of Digital Transformation 3 The digital transformation imperative Challenges with traditional IT infrastructures Why cloud services are so vital to digital transformation AWS: A Strategic Enabler of Digital Business Transformation 4 AWS offerings AWS customers Customer Challenges 5 Large-scale, highly dynamic environments Limited monitoring Challenges of employing multiple tools The Opportunity for Service Providers: Managed Monitoring Services for AWS 6 The Solution: Deliver Compelling Managed Monitoring Services with CA Unified Infrastructure Management 7 Unified monitoring services powered by CA UIM Conclusion 10 3 | WHITE PAPER: AMAZON WEB SERVICES MONITORING ca.com Executive Summary Today, your customers are in the midst of a massive paradigm shift, undertaking digital business transformation so they can compete more effectively in their dynamic markets. As they seek out technologies that can help accelerate their digital transformation, IT decision makers are increasingly gravitating toward cloud offerings from Amazon Web Services (AWS). This paper offers a detailed look at the drivers that are prompting the adoption of AWS—and the challenges that enterprise IT teams are likely to confront when they start leveraging these services. The paper then introduces CA Unified Infrastructure Management (CA UIM) and shows how the solution enables service providers to deliver managed monitoring service offerings that address their customers’ emerging requirements. Cloud Services: A Key Element of Digital Transformation The digital transformation imperative To compete and win in the application economy, it’s critical for enterprises to pursue digital business “Ultimately, the transformation. -

Secure Enterprise Mobility – with Ca Siteminder and Sap Mobile Platform 2
SECURE ENTEPRISE MOBILITY – WITH CA SITEMINDER AND SAP® MOBILE PLATFORM . Version 1.0 January 2013 White Paper SAP Co-Innovation Lab SECURE ENTERPRISE MOBILITY – WITH CA SITEMINDER AND SAP MOBILE PLATFORM 2 Acknowledgements This document is the work of a virtual project team at SAP Co-Innovation Lab, whose members include Guru Shetti (SAP), David Clegg (SAP), Lorra Moyer (SAP), Hyunsoo Shim (SAP), Kevin Liu (SAP), Carolyn Fitton (SAP), Jeffery Thurston (CA), Brink Tully (CA), Richard Wu (CA), Sumner Blount (CA). The team would like to thank all the colleagues from CA and SAP who helped with this project, including David Cruickshank, Roger Guedes, Heather Li, and Irakli Natsvlishvili for operational and infrastructure support at SAP Co- Innovation Lab. SECURE ENTERPRISE MOBILITY – WITH CA SITEMINDER AND SAP MOBILE PLATFORM 3 Content 1 At a Glance ..................................................................................................................................................... 4 2 Business Challenge ....................................................................................................................................... 4 3 Solution Overview .......................................................................................................................................... 5 4 Critical Differentiators ................................................................................................................................... 6 5 Related Products/Solutions ......................................................................................................................... -

United States Securities and Exchange Commission Washington, D.C
UNITED STATES SECURITIES AND EXCHANGE COMMISSION WASHINGTON, D.C. 20549 ______ FORM 8-K CURRENT REPORT Pursuant to Section 13 or 15(d) of the Securities Exchange Act of 1934 Date of Report: January 21, 2014 (Date of earliest event reported) CA, Inc. (Exact name of registrant as specified in charter) Delaware (State or other jurisdiction of incorporation) 1-9247 13-2857434 (Commission File Number) (IRS Employer Identification No.) One CA Plaza Islandia, New York 11749 (Address of principal executive offices) (Zip Code) (800) 225-5224 (Registrant’s telephone number, including area code) Not applicable (Former name or former address, if changed since last report) Check the appropriate box below if the Form 8-K filing is intended to simultaneously satisfy the filing obligation of the registrant under any of the following provisions (see General Instruction A.2. below): ¨ Written communications pursuant to Rule 425 under the Securities Act (17 CFR 230.425) ¨ Soliciting material pursuant to Rule 14a-12 under the Exchange Act (17 CFR 240.14a-12) ¨ Pre-commencement communications pursuant to Rule 14d-2(b) under the Exchange Act (17 CFR 240.14d-2(b)) ¨ Pre-commencement communications pursuant to Rule 13e-4(c) under the Exchange Act (17 CFR 240.13e-4(c)) Item 5.02 Departure of Directors or Certain Officers; Election of Directors; Appointment of Certain Officers; Compensatory Arrangements of Certain Officers. On January 21, 2014, CA, Inc. issued a press release announcing that, effective immediately, Adam Elster, the Company’s Executive Vice President, Mainframe and Customer Success, would succeed George J. Fischer as the Company’s Executive Vice President and Group Executive, Worldwide Sales and Services. -

Work Groups (International) Affiliations Organizational Structure And
Work Groups (International) Organizational Structure and Governance Work Groups Regional Roundtables The domestic and international forums each have a Our Mission o APAC Steering Committee that make up the Board of Our mission is to impact the evolution of global benefits and o EMEA Directors. The Steering Committees meet quarterly create leading edge innovations. We develop and improve o India and the Board of Directors meets at least annually. the global market while supporting the culture, philosophy, o CaLATAM The decision making is held within the organization and benefits strategy of our member companies. through the all-member Forum level where Global Retirement approvals of new members and the budget are What We Do Global Wellness made. We are a coalition comprised of high-tech companies that Global Expansion impact the evolution of global benefits. SVEF supports Quarterly Meetings two forums: domestic and international, both of which have Affiliations distinct memberships and focus on comprehensive The domestic and international forums each hold employee benefits. We benchmark benefit plan and program Pacific Business Group on Health quarterly all-member meetings that are pivotal points designs to support the sharing of best practices and lessons Pacific Business Group on Health (PBGH) is one of the work and support valued professional learned. The group leverages our purchasing power to bring of the nation’s leading coalitions focused on networking. The meetings are hosted at employer improvement and change to the practice of employee healthcare. Respected as a purchaser voice about sites in the Silicon Valley region. benefits management. reform, the mission of PBGH is to moderate cost and improve quality. -

CA Identity and Access Management MSO
SERVICES DESCRIPTION CA Identity and Access Management MSO At a Glance For your clients today, identities represent the new security perimeter—the only way to deliver timely access to resources while safeguarding sensitive assets. While IT organizations need to support identity and access management (IAM) for an increasing number of cloud-based services, applications and users, they lack the time, tools and expertise required to do so. With the CA Identity and Access Management Managed Service Offering (MSO), you can deliver robust IAM services that address this urgent market demand. This pre- packaged offering equips you with the sophisticated platform and resources you need to deliver advanced IAM services to market—with minimal up-front investment and risk. The Market The Increasingly Urgent Demand for IAM Whether they’re government agencies or enterprises of virtually any size, your clients have As organizations grow increasingly reliant to contend with increasingly persistent and sophisticated adversaries and attacks. These on a mix of internally sourced and cloud- organizations also have to manage the efforts required to comply with increasingly stringent based services—while security threats continue to escalate—the demand for strong regulatory mandates, or face escalating fines when they fall short of these requirements. IAM capabilities grows more urgent and Given these realities, relying on static user names and passwords is an approach that is widespread. increasingly proving to be a weak link in an organization’s defenses. This weakness is being exacerbated by the shifting business and technological environment The Need your clients operate in today. As these organizations continue their move to the cloud and Security teams are being tasked with other externally hosted environments, the dynamics of managing security also change delivering IAM services and applications that substantially. -

Ca Unified Infrastructure Management for Sap
DATA SHEET CA Unifed Infrastructure Management for SAP At a Glance CA Unified Infrastructure Management (CA UIM) for SAP enables your IT teams to proactively monitor and manage service levels of your SAP implementations, including SAP ABAP, SAP HANA and SAP NetWeaver. The solution delivers insights that help prevent downtime and ensure SLA compliance, offering detailed quality-of-service metrics, comprehensive usage metering, service-centric insights and sophisticated alarms. By offering dashboards and templates and comprehensive coverage of SAP and non-SAP systems and services, the solution helps make it fast and easy for administrators to gain maximum benefits from their monitoring implementation. Key Benefits/Results Business Challenges SAP is at the heart of many organizations’ most mission-critical business processes. If SAP • Speed issue resolution. Gain deep, systems, databases and supporting IT infrastructure are not functioning optimally, critical actionable insights into SAP infrastructures and the services running on them, so your business functions—such as order-to-cash or financial close—can slow down or even staff can spot and address issues faster. become completely unavailable. • Reduce cost and complexity. Leverage Performance issues need to be spotted and addressed quickly, before internal or external unified views for monitoring the user experience suffers. However, identifying performance issues across multitier SAP performance of your SAP and non-SAP environments, so you can eliminate the implementations can be time consuming and challenging. To effectively troubleshoot need to manage multiple tools. issues within complex SAP environments, administrators need a comprehensive view of relevant performance metrics from across all the tiers within SAP implementations and • Boost operational efficiency. -

CA Privileged Access Manager for Amazon Web Services (AWS)
DATA SHEET CA Privileged Access Manager for Amazon Web Services (AWS) At A Glance Quickly deployable and delivering fast time to protection, CA Privileged Access Manager enhances security capabilities of the AWS Management Console and Management APIs, facilitates compliance and minimizes costs. Available as a virtual appliance, CA Privileged Access Manager is designed to prevent security breaches in EC2 environments by consistently controlling privileged user activities, proactively enforcing security policies, protecting sensitive administrative credentials, and monitoring and recording privileged user activity across virtual, cloud and physical environments. KEY BENEFITS Business Challenges • Deploy the solution quickly. Privileged user accounts are your most valuable assets—and the most likely to be exploited by external hackers or insider threats. One compromised privileged • Protect AWS management console and account can cause irreparable damage to your infrastructure, intellectual property APIs, as well as EC2 instances. and brand. And the attack surface is expanding as you move to virtualized and cloud • Control privileged access across all environments. Recognizing these risks, many emerging standards and regulations are IT resources. requiring mandatory controls and auditing of privileged user access and activity. • Apply unified cross-platform privileged In addition, as organizations adopt DevOps, new risks are being introduced. Automation user credentials protection. tools like CA’s Automation solutions, Chef and Puppet leverage AWS Management APIs • Monitor, react and record everything. and Amazon software development kits (SDKs). Developers create command line scripts • Ensure security and privacy regulatory and programs to perform AWS administrative and operational tasks and embed these compliance. scripts within the automation tools. Unfortunately, a single set of credentials is often • Provide for positive privileged user used for all cloud management APIs across all automation initiatives, creating a single authentication. -
Runscope Build Trust in Your Apis with Runscope
Solution Brief Runscope Build Trust in your APIs with Runscope At A Glance Key Benefits In the application economy, customer experience is key. End users expect • Be the first to know when an API is a flawless experience all day every day, and a broken or poorly performing down. Your customers shouldn’t be API could mean a lost opportunity. For app owners and DevOps teams the ones telling you about downtime. who need to deliver a five-star customer experience, Runscope provides proactive monitoring of APIs to ensure you know if problems exist before • Gain a global view of API your customers do. This allows you to minimize the business impact of app performance. Wherever your issues caused by your APIs or the third-party APIs you leverage. Runscope is customers are located, ensure API a SaaS-based synthetic monitoring solution that enables you to easily ensure performance isn’t affecting their app the APIs you rely on are up, performant, and returning the expected data. experience. • Easily ensure API integrity. Verify APIs are returning correct data. Business Challenges • Ensure SLAs are met. Monitor API Downtime can have far-reaching impacts on any business. Without proper performance in minutes. visibility of the APIs running your applications, diagnosing and solving the problem means using up valuable time and resources. API monitoring • Solve API problems as a team. From surfaces issues directly from the internal and third-party APIs that power development to ops, easily create and your apps. It works by running API checks on a continuous schedule to give share tests to monitor your APIs.