Designing and Deploying Cisco NAC Appliance
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cisco NAC Network Module for Integrated Services Routers
Data Sheet Cisco NAC Network Module for Integrated Services Routers The Cisco ® NAC Network Module for Integrated Services Routers (NME-NAC-K9) brings the feature-rich Cisco NAC Appliance Server capabilities to Cisco 2800, 2900, 3800 and 3900 Series Integrated Services Routers. Cisco NAC Appliance (also known as Cisco Clean Access) is a rapidly deployable Network Admission Control (NAC) product that allows network administrators to authenticate, authorize, evaluate, and remediate wired, wireless, and remote users and their machines prior to allowing them onto the network. Product Overview The Cisco NAC Network Module for Integrated Services Routers (NME-NAC-K9) extends the Cisco NAC Appliance portfolio of products to smaller locations, helping enable network admission control (NAC) capabilities from the headquarters to the branch office (Figure 1). The integration of NAC Appliance Server capabilities into a network module for Integrated Services Routers allows network administrators to manage a single device in the branch office for data, voice, and security requirements, reducing network complexity, IT staff training needs, equipment sparing requirements, and maintenance costs. The Cisco NAC Network Module for Integrated Services Routers deployed at the branch office remediates potential threats locally before they traverse the WAN and potentially infect the network. Figure 1. Cisco NAC Network Module for Integrated Services Routers (NME-NAC-K9) The Cisco NAC Network Module for Integrated Services Routers is an advanced network security product that: ● Recognizes users, their devices, and their roles in the network: This first step occurs at the point of authentication, before malicious code can cause damage. ● Evaluates machines to determine their compliance with security policies: Security policies can vary by user type, device type, or operating system. -
Cisco Self Defending Network
Cisco Self Defending Network Mai 2007 Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 1 Intelligent Networking Using the Network to Enable Business Processes Cisco Network Strategy Utilize the Network to Unite Isolated Layers and Domains to Enable Business Processes Connectivity Intelligent Networking Business Networked Processes Infrastructure • Active participation in application and service delivery • A systems approach integrates Resilient technology layers to reduce Integrated complexity Adaptive • Flexible policy controls adapt this intelligent system to your Applications business though business rules and Services Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 2 When it comes to information security, what are the objectives? Adaptive On Demand Agile Align security practice Organization Organization and policy to business requirements. Security that’s a business enabler, not an inhibitor. Keep costs appropriate: It’s not necessarily about reducing costs, but rather, spending where it counts the most • The network touches all Reduce complexity of parts of the infrastructure the overall environment • It is uniquely positioned to Control and contain threats so help solve these issues they don’t control you Presentation_ID © 2006 Cisco Systems, Inc. All rights reserved. Cisco Confidential 3 Self-Defending Network Defined Efficient Security Management, Control, Operational Management and Response and Policy Control Advanced technologies and security services to -
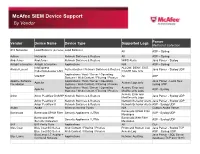
Mcafee SIEM Device Support by Vendor
McAfee SIEM Device Support By Vendor Vendor Device Name Device Type Supported Logs Parser Method of Collection A10 Networks Load Balancer (AX Series) Load Balancer All ASP – Syslog Adtran NetVanta Network Switches & Routers All ASP – Syslog Airdefense Airdefense Network Switches & Routers WIPS Alerts Java Parser - Syslog Airtight Interactive Airtight Interactive Applications N/A ASP – Syslog InfoExpress ALLOW, DENY, EXIT, Alcatel-Lucent Authentication / Network Switches & Routers Java Parser - Syslog UDP CyberGatekeeper LAN CGATE type only Applications / Host / Server / Operating VitalQIP All ASP Systems / Web Content / Filtering / Proxies Apache Software Applications / Host / Server / Operating Java Parser - Local files; Apache Access Logs only Foundation Systems / Web Content / Filtering / Proxies syslog UDP Applications / Host / Server / Operating Access, Error and Apache ASP - Syslog Systems / Web Content / Filtering / Proxies ModSecurity Logs Access, Error and Arbor Arbor Peakflow DoS/SP Network Switches & Routers Java Parser - Syslog UDP ModSecurity Logs Arbor Peakflow X Network Switches & Routers Network Behavior Alerts Java Parser - Syslog UDP Arbor Peakflow X Network Switches & Routers Network Behavior Alerts ASP - Syslog UDP Aruba Aruba Wireless Access Points N/A Custom Aruba Parser Barracuda SPAM Filter Barracuda Barracuda SPAM Filter Security Appliances / UTMs ASP - Syslog UDP Messages Barracuda Web Barracuda Web Filter Security Appliances / UTMs ASP - Syslog UDP Security Gateways Messages Bit9 Bit9 Parity Suite Applications -

Cisco NAC Guest Server Installation and Configuration Guide, Release 2.1
Cisco NAC Guest Server Installation and Configuration Guide Release 2.1 November 2012 Americas Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 527-0883 Text Part Number: OL-28256-01 THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

Community College Security Design Considerations SBA
Community College Security Design Considerations SBA As community colleges embrace new communication and collaboration tools, • Network abuse—Use of non-approved applications by students, faculty, and staff; transitioning from traditional classroom teaching into an Internet-based, media-rich peer-to-peer file sharing and instant messaging abuse; and access to forbidden education and learning environment, a whole new set of network security challenges content arise. Community college network infrastructures must be adequately secured to protect • Unauthorized access—Intrusions, unauthorized users, escalation of privileges, IP students, staff, and faculty from harmful content, to guarantee confidentiality of private spoofing, and unauthorized access to restricted learning and administrative data, and to ensure the availability and integrity of the systems and data. Providing a safe resources and secure network environment is a top responsibility for community college administrators and community leaders. • Data loss—Loss or leakage of student, staff, and faculty private data from servers and user endpoints Security Design • Identity theft and fraud—Theft of student, staff, and faculty identity or fraud on servers and end users through phishing and E-mail spam Within the Cisco Community College reference design, the service fabric network provides the foundation on which all solutions and services are built to solve the business The Community College reference design accommodates a main campus and one or challenges facing community colleges. These business challenges include building a more remote smaller campuses interconnected over a metro Ethernet or managed WAN virtual learning environment, providing secure connected classrooms, ensuring safety service. Each of these campuses may contain one or more buildings of varying sizes, as and security, and operational efficiencies. -

NAC) Market More Than Just NAC
Analysis of the Global Network Access Control (NAC) Market More than just NAC NE66-74 December 2014 NE66-74 1 Research Team Lead Analyst Contributing Analyst Chris Kissel Chris Rodriguez Industry Analyst Senior Analyst ICT – Network Security ICT – Network Security (623) 910-7986 (210) 477-8423 [email protected] [email protected] Research Director Strategic Review Committee Leader Michael Suby Frank Dickson Stratecast VP of Research Research Director ICT – Network Security Information and Network Security 720-344-4860 469-387-0256 [email protected] [email protected] NE66-74 2 List of Exhibits Chart Slide Number Executive Summary 8 Key Findings 9 Market Engineering Measurements 11 CEO’s Perspective 16 Introduction to the Research 17 Key Questions This Study Will Answer 18 Market Overview 19 Market Overview—Definitions 22 Distribution Channels 24 Debate About 802.1X 26 Drivers and Restraints—Total Market 28 Market Drivers 29 Drivers Explained 30 Market Restraints 35 Restraints Explained 36 Source: Frost & Sullivan NE66-74 3 List of Exhibits (continued) Chart Slide Number Forecasts and Trends—Total Market 40 Forecast Assumptions 41 Total NAC Unit Shipment 42 Total NAC Revenue Forecast 43 Total NAC Unit Shipment and Revenue Forecast 44 Total NAC Market―Pricing Trends and Forecast 46 Total NAC Market—Unit Shipment Forecast by Region 48 Total NAC Market—Revenue Forecast by Region 49 Total NAC Market—Unit Shipment Forecast by Distribution Channel 51 Total NAC Market—Revenue Forecast by Distribution Channel 52 Total -

Augmenting Perimeter Security Networks with Cisco Self-Defending Networks
Augmenting Perimeter Security Networks With Cisco Self-Defending Networks Mark Las 68-595 Security Project Table of Contents Abstract 3 Traditional Network Attacks 4 Virus 4 Worms 5 Trojan Horse 6 Denial-of-service/Distributed Denial-of-service 6 Spyware 10 Phishing 10 Traditional Network Defense/ Defense-in-Depth 11 Static Packet Filter 12 Stateful Firewall 13 Proxy Firewall 13 IDS/IPS 13 VPN Device 14 Ingress/Egress Filtering 15 Internal Firewalls 15 IDS Sensors 16 Host-centric (personal) firewalls 16 Antivirus software 17 Operating System Hardening 17 Configuration Management 17 Audits 18 Human Factor 18 Cisco Self-Defending Networks 19 DDoS Mitigation 19 Adaptive Security Appliance 22 Incident Control Services 24 Network Admission Control 25 802.1x 30 Host Intrusion Prevention 31 Cisco Security Centralized Management 33 Summary 34 2 Abstract Computer data networks are under constant attack and subject to an increasing variety of attacks. These attacks fall into several general categories that identify and separate them based on some key differences and methods. Many organizations have implemented perimeter security as a method for dealing with these threats and attacks. As attacks and threats have escalated and found ways through the perimeter, organizations have further extended the perimeter security approach with the concept of defense in depth, which provides a layered approach to protecting data networks beginning with the perimeter. Perimeter security is dependent on properly configured firewalls and routers. However, traditional packet-filtering firewalls only block network ports and computer addresses and do not address threats that occur at the application layer. Firewalls do not protect against traffic that is passed on open ports or encrypted VPN traffic. -

The Building Blocks in a Cisco NAC Appliance Design
C H A P T E R 3 The Building Blocks in a Cisco NAC Appliance Design Knowledge of how to properly design security solutions is what separates the professional from the amateur. Without a proper design, the eventual implementation will most likely be a disaster. One of the keys to success when designing a security solution is to first understand all the pieces you have to work with. I like to call these building blocks. After you achieve understanding, you then need to become skilled at manipulating the pieces in ways that best fit your environment. This chapter focuses on the building blocks available with the Cisco NAC Appliance solution. The purpose and function of each piece is covered. The requirements, scalability, and performance of these building blocks are also discussed. The next chapter discusses your options for manipulating these building blocks. Cisco NAC Appliance Solution Components A NAC Appliance solution is made up of the following components: • Mandatory components: — Cisco NAC Appliance Manager (Clean Access Manager) — Cisco NAC Appliance Server (Clean Access Server) • Optional components: — Cisco Clean Access Agent — Cisco NAC Appliance Network Scanner Each piece has a distinct role to play in the solution. In this section, you examine the roles of each in more detail. NOTE Cisco NAC Appliance was formerly known as Cisco Clean Access. The legacy name Clean Access is still widely used in the industry, but this book will use the new name: Cisco NAC Appliance. 24 Chapter 3: The Building Blocks in a Cisco NAC Appliance Design -

Small Enterprise Design Profile Reference Guide Last Updated: July 8, 2010
Small Enterprise Design Profile Reference Guide Last Updated: July 8, 2010 Building Architectures to Solve Business Problems ii Small Enterprise Design Profile Reference Guide About Cisco Validated Design (CVD) Program The CVD program consists of systems and solutions designed, tested, and documented to facilitate faster, more reliable, and more predictable customer deployments. For more information visit www.cisco.com/go/designzone. ALL DESIGNS, SPECIFICATIONS, STATEMENTS, INFORMATION, AND RECOMMENDATIONS (COLLECTIVELY, "DESIGNS") IN THIS MANUAL ARE PRESENTED "AS IS," WITH ALL FAULTS. CISCO AND ITS SUPPLIERS DIS- CLAIM ALL WARRANTIES, INCLUDING, WITHOUT LIMITATION, THE WARRANTY OF MERCHANTABILITY, FIT- NESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THE DESIGNS, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAM- AGES. THE DESIGNS ARE SUBJECT TO CHANGE WITHOUT NOTICE. USERS ARE SOLELY RESPONSIBLE FOR THEIR APPLICATION OF THE DESIGNS. THE DESIGNS DO NOT CONSTITUTE THE TECHNICAL OR OTHER PROFESSIONAL ADVICE OF CISCO, ITS SUPPLIERS OR PARTNERS. USERS SHOULD CONSULT THEIR OWN TECHNICAL ADVISORS BEFORE IMPLEMENTING THE DESIGNS. RESULTS MAY VARY DEPENDING ON FACTORS NOT TESTED BY CISCO. CCDE, CCENT, Cisco Eos, Cisco Lumin, -
Cisco NAC Appliance Improves Security for Education Networks
White Paper Cisco NAC Appliance Improves Security for Education Networks Summary Educational institutions face difficult challenges related to the protection of their information networks. The severity and frequency of worms and viruses have increased at the same time that dependence on the network for delivery of critical teaching tools and services has increased. These problems are exacerbated by three characteristics unique to these institutions and their networks: Spiking. Educational networks, especially those on campuses with residential halls, experience a surge of new users at the start of each semester. During times of worm and virus activity, helpdesks are often overwhelmed by the number of infected computers. Values. The underlying philosophy of educational institutions is often one of openness and shared learning. Imposing network controls similar to those used by corporations is inconsistent with these core values. Diverse users. Unlike corporate networks, which exist mainly to support employees, educational networks support a large array of constituents: students, faculty, administrators, visiting scholars, guests and community users, conference attendees, to name a few. Managing these diverse groups with their diverse needs represents a significant challenge. Cisco has developed Cisco NAC Appliance, a network admissions control (NAC) product that automatically detects, isolates, and cleans infected or vulnerable devices that attempt to access the network. With Cisco NAC Appliance, administrators can define security policies as broadly or narrowly as they like as they apply to a defined group of users. Cisco NAC Appliance aims to balance the unique network-related challenges educational institutions face with a robust, effective policy enforcement mechanism that dramatically reduces threats to the network. -
Genian-Nac-Admin-Guide.Pdf
Genian NAC GENIANS, INC. Sep 16, 2021 관리자 가이드 1 Network Access Control의 이해 3 2 Genian NAC 구축 9 3 Genian NAC 설치 29 4 네트워크 자산 모니터링 57 5 네트워크 접근제어 91 6 네트워크 연결 프로세스 191 7 사용자 인증 207 8 엔드포인트 제어 265 9 위험감지 335 10 로그 및 이벤트 관리 345 11 시스템관리 363 12 API 가이드 439 13 로그포맷 449 14 FAQ 451 15 Troubleshooting 453 16 Release Note 483 17 Security Advisories 527 i ii Genian NAC 관리자 가이드 1 Genian NAC 2 관리자 가이드 CHAPTER ONE NETWORK ACCESS CONTROL의 이해 1.1 NAC란 무엇인가? 네트워크 접근제어 (Network Access Control) 는 네트워크에 접속하는 장치에 대해 접속 가능 여부를 확인하여 인가된 장치만이 접속할 수 있도록 제한하는 것에서 출발하였다. 이 같은 접속 제어는 통상 802.1X 라 불리는 기술을 통하여 제공되었는데 이때 AAA(Authentication, Authorization, Accounting)라 불리는 3가지 중요한 기능이 제공된다. Authentication Authentication은 네트워크에 접속하는 사용자나 장치에 대해 검증하는 과정이다. 통상적으로 사용자명/비밀번호를 통해 제공되는데 경우에 따라서는 장치의 MAC 주소가 인증의 수단으로 사용되기도 한다. Authorization Authorization은 인증된 장치가 어떤 네트워크 자원에 대해서 접근할 수 있는지에 대해 결정하는 과정이다. 인증된 장치의 종류나 식별된 사용자의 그룹에 따라 접근할 수 있는 네트워크, 서비스 및 시간대를 제한할 수 있다. Accounting Accounting은 장치가 네트워크를 접근한 기록을 남겨 향후 과금이나 보안상의 목적으로 사용할 수 있도록 해주는 과정이다. 이를 통해 어떤 장치를 누가, 언제, 어디서, 어떻게 사용했는지 확인할 수 있다. 이 같은 AAA 기능이 네트워크 접근제어의 기본 기술로 오랜 기간 사용되었는데 최근 네트워크 단말들의 다양한 보안 문제로 인해 단말의 보안 규제 준수상태에 따라 네트워크 접속 가능 여부를 결정하길 원하게 되었다. 이에 단말의 사용자에 대한 식별을 뛰어넘어 장치의 종류가 무엇인지 장치의 현재 보안설정이나 상태를 확인하여 관리자가 정한 조건에 부합하는 단말만이 네트워크에 접속할 수 있도록 해주는 제품군을 NAC라는 명칭으로 부르게 되었다. -

Cisco NAC Network Module for Integrated Services Routers
Data Sheet Cisco NAC Network Module for Integrated Services Routers The Cisco ® NAC Network Module for Integrated Services Routers (NME-NAC-K9) brings the feature-rich Cisco NAC Appliance Server capabilities to Cisco 2800 and 3800 Series Integrated Services Routers. Cisco NAC Appliance (also known as Cisco Clean Access) is a rapidly deployable Network Admission Control (NAC) product that allows network administrators to authenticate, authorize, evaluate, and remediate wired, wireless, and remote users and their machines prior to allowing them onto the network. Product Overview The Cisco NAC Network Module for Integrated Services Routers (NME-NAC-K9) extends the Cisco NAC Appliance portfolio of products to smaller locations, helping enable network admission control (NAC) capabilities from the headquarters to the branch office (Figure 1). The integration of NAC Appliance Server capabilities into a network module for Integrated Services Routers allows network administrators to manage a single device in the branch office for data, voice, and security requirements, reducing network complexity, IT staff training needs, equipment sparing requirements, and maintenance costs. The Cisco NAC Network Module for Integrated Services Routers deployed at the branch office remediates potential threats locally before they traverse the WAN and potentially infect the network. Figure 1. Cisco NAC Network Module for Integrated Services Routers (NME-NAC-K9) The Cisco NAC Network Module for Integrated Services Routers is an advanced network security product that: ● Recognizes users, their devices, and their roles in the network: This first step occurs at the point of authentication, before malicious code can cause damage. ● Evaluates machines to determine their compliance with security policies: Security policies can vary by user type, device type, or operating system.