A Survey on Identity and Access Management in Cloud Computing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Global Namespace Discovery Using a XRI Root-Of-Roots Assumed by ITU-T
Geneva, 21 September 2007 Global Namespace Discovery using a XRI root-of-roots assumed by ITU-T Tony Rutkowski Chair, ITU-T IdM FG Requirements WG [email protected] XRI detail slides courtesy of Reed Drummond OASIS Extensible Resource Identifier (XRI) TC International http://xri.net/=drummond.reed Telecommunication Union Identity Discovery Requirements 5.3 Discovery of authoritative Identify Provider resources, services, and federations. A critical IdM challenge in the very dynamic and diverse world of network services and applications is discovering current authoritative sources for the four core IdM categories described above or the federations that are associated with enabling discovery and access of the relevant IdM resources. It is not enough for the IdM capabilities to exist, if a relying party has no means for knowing who and how to reach and interoperate with the authoritative resources for asserted identities treated in the sub-section below. Identity Discovery Provider(s) Query(ies) to discover Identity Resources Response(s) Fig. 9. Identity Management Discovery Services A very significant number of contributions and use-cases during the entire activity period of the Focus Group dealt with Discovery capabilities and associated requirements. Discovery capabilities seem to be widely recognized as one of the most significant needs and gaps – including a consensus that the challenge of providing effective Discovery capabilities are therefore an essential part of trusted Identity Management. Some federations and communities surrounding Open Identity protocols have developed partial solutions to meet discovery needs within the boundaries of their user communities. However, there are no current means for global or inter-federation discovery. -

Gs Ins 006 V1.1.1 (2011-11)
ETSI GS INS 006 V1.1.1 (2011-11) Group Specification Identity and access management for Networks and Services; Study to Identify the need for a Global, Distributed Discovery Mechanism Disclaimer This document has been produced and approved by the Identity and access management for Networks and Services (INS) ETSI Industry Specification Group (ISG) and represents the views of those members who participated in this ISG. It does not necessarily represent the views of the entire ETSI membership. 2 ETSI GS INS 006 V1.1.1 (2011-11) Reference DGS/INS-006 Keywords access, control, ID, management, network, service ETSI 650 Route des Lucioles F-06921 Sophia Antipolis Cedex - FRANCE Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16 Siret N° 348 623 562 00017 - NAF 742 C Association à but non lucratif enregistrée à la Sous-Préfecture de Grasse (06) N° 7803/88 Important notice Individual copies of the present document can be downloaded from: http://www.etsi.org The present document may be made available in more than one electronic version or in print. In any case of existing or perceived difference in contents between such versions, the reference version is the Portable Document Format (PDF). In case of dispute, the reference shall be the printing on ETSI printers of the PDF version kept on a specific network drive within ETSI Secretariat. Users of the present document should be aware that the document may be subject to revision or change of status. Information on the current status of this and other ETSI documents is available at http://portal.etsi.org/tb/status/status.asp If you find errors in the present document, please send your comment to one of the following services: http://portal.etsi.org/chaircor/ETSI_support.asp Copyright Notification No part may be reproduced except as authorized by written permission. -

Extensible Resource Identifier (XRI) Resolution Version 2.0 Committee Draft 02 25 November 2007
Extensible Resource Identifier (XRI) Resolution Version 2.0 Committee Draft 02 25 November 2007 Specification URIs: This Version: http://docs.oasis-open.org/xri/2.0/specs/cd02/xri-resolution-V2.0-cd-02.html http://docs.oasis-open.org/xri/2.0/specs/cd02/xri-resolution-V2.0-cd-02.pdf http://docs.oasis-open.org/xri/2.0/specs/cd02/xri-resolution-V2.0-cd-02.doc Previous Version: N/A Latest Version: http://docs.oasis-open.org/xri/2.0/specs/xri-resolution-V2.0.html http://docs.oasis-open.org/xri/2.0/specs/xri-resolution-V2.0.pdf http://docs.oasis-open.org/xri/2.0/specs/xri-resolution-V2.0.doc Technical Committee: OASIS eXtensible Resource Identifier (XRI) TC Chairs: Gabe Wachob, AmSoft <[email protected]> Drummond Reed, Cordance <[email protected]> Editors: Gabe Wachob, AmSoft <[email protected]> Drummond Reed, Cordance <[email protected]> Les Chasen, NeuStar <[email protected]> William Tan, NeuStar <[email protected]> Steve Churchill, XDI.org <[email protected]> Related Work: This specification replaces or supercedes: • Extensible Resource Identifier (XRI) Resolution Version 2.0, Committee Draft 01, March 2005 • Extensible Resource Identifier (XRI) Version 1.0, Committee Draft 01, January 2004 This specification is related to: • Extensible Resource Identifier (XRI) Syntax Version 2.0, Committee Specification, December 2005 • Extensible Resource Identifier (XRI) Metadata Version 2.0, Committee Draft 01, March 2005 Declared XML Namespace(s) xri://$res xri://$xrds xri://$xrd XRI Resolution 2.0 Committee Draft 02 25 November 2007 Copyright © OASIS® 1993–2007. -

The XDI RDF Model V11, 2008-10-21
The XDI RDF Model V11, 2008-10-21 This document is a work-in-progress from the OASIS XDI Technical Committee. Contributors to this draft include: • Drummond Reed, Cordance • Markus Sabadello, XDI.org • Paul Trevithick, Higgins Project A link to the current version of this document is maintained on the following XDI TC wiki page: http://wiki.oasis-open.org/xdi/XdiRdfModel The XDI RDF Model v11 2008-10-21 Page 2 Table of Contents Introduction .................................................................................................................................................... 3 Motivations..................................................................................................................................................... 3 About the Proposed XRI 3.0 Syntax Used in this Document.........................................................................4 Cross-References ....................................................................................................................................... 4 Global Context Symbols............................................................................................................................ 4 Global Cross-References ........................................................................................................................... 5 The XDI RDF Model...................................................................................................................................... 5 Basic Structure and Addressing................................................................................................................ -

Yadis Specification 1.0
Yadis Specification 1.0 Yadis Specification Version 1.0 18 March 2006 Joaquin Miller, editor www.yadis.org 1 Yadis Specification 1.0 Table of Contents 0 Introduction........................................................................................................................................................ 3 1 Scope..................................................................................................................................................................... 3 2 Normative References.........................................................................................................................................4 2.1 Requests for Comments............................................................................................................................. 4 2.2 W3C Recommendations.............................................................................................................................4 2.3 OASIS Specifications...................................................................................................................................4 3 Terms and Definitions....................................................................................................................................... 5 3.1 Implementor Terms.................................................................................................................................... 5 3.2 Definitions from other specifications...................................................................................................... -

Identity Management Challenges for Intercloud Applications
D. Nu~nez,I. Agudo, P. Drogkaris, and S. Gritzalis, \Identity Management Challenges for Intercloud Applications", 1st International Workshop on Security and Trust for Applications in Virtualised Environments (STAVE 2011) vol. 187, pp. 198-204, 2011. http://doi.org/10.1007/978-3-642-22365-5_24 NICS Lab. Publications: https://www.nics.uma.es/publications Identity Management Challenges for Intercloud Applications David Núñez1, Isaac Agudo1, Prokopios Drogkaris2 and Stefanos Gritzalis2 1 Department of Computer Science, E.T.S. de Ingeniería Informática, University of Málaga, E-29071 Málaga, Spain {dnunez, isaac}@lcc.uma.es 2 Laboratory of Information and Communication Systems Security, Department of Information and Communication Systems Engineering, University of the Aegean Samos, GR-83200, Greece {pdrogk, sgritz}@aegean.gr Abstract. Intercloud notion is gaining a lot of attention lately from both enterprise and academia, not only because of its benefits and expected results but also due to the challenges that it introduces regarding interoperability and standardisation. Identity management services are one of the main candidates to be outsourced into the Intercloud, since they are one of the most common services needed by companies and organisations. This paper addresses emerging identity management challenges that arise in intercloud formations, such as naming, identification, interoperability, identity life cycle management and single sign-on. Keywords: Cloud computing, identity management, intercloud, interoperability. 1 Introduction The adoption of the cloud computing design pattern is rapidly evolving as more and more organisations reach out for the benefits of distributed datacenters. One of the main advantages of cloud computing is that it provides a model of “utility computing”; that is, it is capable of offering on-demand provisioning of computing resources, such as storage, computation and networking. -

Open Geospatial Consortium Inc
Open Geospatial Consortium Inc. Date: 2009-10-09 Reference number of this document: OGC 09-035 Version: 0.3.0 Category: OGC® Public Engineering Report Editor(s): Rüdiger Gartmann, Lewis Leinenweber OGC® OWS-6 Security Engineering Report Copyright © 2009 Open Geospatial Consortium, Inc. To obtain additional rights of use, visit http://www.opengeospatial.org/legal/. Warning This document is not an OGC Standard. This document is an OGC Public Engineering Report created as a deliverable in an OGC Interoperability Initiative and is not an official position of the OGC membership. It is distributed for review and comment. It is subject to change without notice and may not be referred to as an OGC Standard. Further, any OGC Engineering Report should not be referenced as required or mandatory technology in procurements. Document type: OpenGIS® Engineering Report Document subtype: NA Document stage: Approved for Public Release Document language: English License Agreement Permission is hereby granted by the Open Geospatial Consortium, ("Licensor"), free of charge and subject to the terms set forth below, to any person obtaining a copy of this Intellectual Property and any associated documentation, to deal in the Intellectual Property without restriction (except as set forth below), including without limitation the rights to implement, use, copy, modify, merge, publish, distribute, and/or sublicense copies of the Intellectual Property, and to permit persons to whom the Intellectual Property is furnished to do so, provided that all copyright notices on the intellectual property are retained intact and that each person to whom the Intellectual Property is furnished agrees to the terms of this Agreement. -
WEB SEMANTICO: Lo Stato Dell’Arte
UNIVERSITÀ DEGLI STUDI DI PADOVA FACOLTÀ DI INGEGNERIA Corso di Laurea in Ingegneria Informatica TESI DI LAUREA WEB SEMANTICO: lo stato dell’arte Relatore: Prof. Michele Moro Laureando: Davide Buongiorno ANNO ACCADEMICO 2008/2009 Università degli Studi di Padova – Facoltà di Ingegneria _____________________________________________________________________ 2 Web Semantico: lo stato dell’arte alla mia famiglia e a quanti mi hanno sostenuto in quest’impresa _____________________________________________________________________ 3 Università degli Studi di Padova – Facoltà di Ingegneria _____________________________________________________________________ 4 Web Semantico: lo stato dell’arte Indice Sommario 7 Introduzione 9 1. World Wide Web 13 1.1 Introduzione 13 1.2 Tim Berners-Lee e Robert Cailliau 14 1.3 Storia 15 1.4 HTML e XHTML 16 1.5 HTTP e HTTPS 20 1.6 World Wide Web Consortium (W3C) e W3C Italia (W3C-IT) 22 2. Introduzione al Web Semantico 27 2.1 Dal web statico al web dinamico. Web Services 27 2.2 Dal web statico al Web Semantico 36 2.2.1 Motori di ricerca 38 2.2.2 Agente semantico 39 2.2.3 Introduzione all’architettura del Web Semantico 41 2.2.4 Metadati 43 2.2.5 Ontologie 45 2.2.6 Conclusione ipotizzata da Berners-Lee 48 2.2.7 Evoluzione dal Web 1.0 al Web 3.0 49 2.3 W3C Semantic Web Activity 50 3. Architettura a livelli del Web Semantico 53 3.1 Unicode, URI, IRI, XRI 53 3.2 XML, XML Schema 61 3.3 RDF, RDF/XML, RDF Schema 72 3.4 OWL, OWL2, SPARQL, SKOS, RIF, SWRL 95 3.5 POWDER 126 _____________________________________________________________________ 5 Università degli Studi di Padova – Facoltà di Ingegneria 3.6 Logica, dimostrazioni, firme digitali e fiducia 133 4. -
2.2 Federated Identity Technologies
2007 Web Services and Identity 2.2 Federated Identity Technologies Eve Maler, Sun Microsystems www.xmlsummerschool.com ©Sun Microsystems 2007; licence to publish granted to CSW Group Ltd Introducing myself • Technology Director at Sun – Currently specialising in Sun-Microsoft interoperability and “identity R&D” • One of the original XML geeks – And an old SGMLer • Leadership roles in various standards efforts and technology projects: – Security Assertion Markup Language (SAML) – Liberty Alliance – Universal Business Language (UBL) – DocBook 2 Identity web services: two great tastes... • Most web services are ultimately performed on behalf of people and things with unique identities • Digital identities are often managed with the help of web services • Web services can do tasks (or help other humans do tasks) relating to you when you're offline 3 Topics we'll cover in this session • Opportunities, risks, use cases, and challenges for federated identity – Including the famous Single Sign-On • Examining three protocol technologies you need to know about, in light of the above (in roughly “chronological” order): – SAML – OpenID – Windows CardSpace (more in 2.3) • Resources for taking technology suitability assessments to the next level 4 2007 Opportunities, risks, use cases, and challenges for federated identity www.xmlsummerschool.com ©Sun Microsystems 2007; licence to publish granted to CSW Group Ltd Enterprise identity has grown out of directories 6 At the same time, the web identity experience has become personal 7 Federated means highly distributed: the good... Excellent! I can add partner Great! I can delegate sites quickly and still retain user authn and mgmt tasks, control over user info!... like password resets!.. -
Domain 12: Guidance for Identity & Access Management V2.1
Domain 12: Guidance for Identity & Access Management V2.1 Prepared by the Cloud Security Alliance April 2010 Domain 12: Guidance for Identity & Access Management V2.1 Introduction The permanent and official location for this Cloud Security Alliance Domain 12 Guidance for Identity & Access Management research is: http://www.cloudsecurityalliance.org/guidance/csaguide-dom12.pdf This research is a component of the Trusted Cloud Initiative, sponsored by Novell, Inc. © 2010 Cloud Security Alliance. All rights reserved. You may download, store, display on your computer, view, print, and link to the Cloud Security Alliance “Domain 12 Guidance for Identity & Access Management” at http://www.cloudsecurityalliance.org/guidance/csaguide-dom12- v2.10.pdf subject to the following: (a) the Guidance may be used solely for your personal, informational, non-commercial use; (b) the Guidance may not be modified or altered in any way; (c) the Guidance may not be redistributed; and (d) the trademark, copyright or other notices may not be removed. You may quote portions of the Guidance as permitted by the Fair Use provisions of the United States Copyright Act, provided that you attribute the portions to the Cloud Security Alliance Domain 12 Guidance for Identity & Access Management research Version 2.1 (2010). Copyright © 2010 Cloud Security Alliance 2 Domain 12: Guidance for Identity & Access Management V2.1 Identity and Access Management Contributors: Subra Kumaraswamy, Sitaraman Lakshminarayanan, Michael Reiter, Joseph Stein, Yvonne Wilson INTRODUCTION -
Identity and Access Management in the Cloud
White Paper www.novell.com Identity and Access Management in the Cloud Cloud Security Alliance Research Paper Sponsored by Novell Foreward At a time when companies are looking for ways to cut costs, cloud computing looks like an attractive alternative, one which you would think most cash-strapped IT departments would take a long look at. But a recent survey of mostly IT professionals conducted by Novell finds a strong mistrust for cloud computing in the workplace, while at the same time, a surprisingly wide acceptance for personal use. The survey was conducted using members of Novell's Cool Solutions Community from July to September, 2009. 453 people responded, of which 81 percent identified themselves as IT professionals. The respondents were from a variety of geographic locations including the US, India, China, Australia, Canada, South Africa and western Europe. The company sizes varied from 25 or less to more than 5000, with 44.6 percent working for companies with more than 1000 employees. When asked to list the top 5 things they feared or mistrusted about cloud computing in the workplace, security came in on top, with 34.6 percent listing it as their top choice. This is not surprising as many other surveys have indicated the same mistrust and confusion among end-users of the cloud. So, what is the truth – is cloud more secure than the enterprise or is it totally insecure. The answer is probably somewhere in the middle. This paper is an in-depth look at the identity and access management issues in the cloud. It goes into the different aspects of managing identities such as provisioning, federation, compliance as well newly emerging models of having identities in the cloud. -
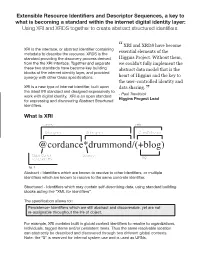
Cordance*Drummond/(+Blog) Global Context Separator Tag Service Idenififer
Extensible Resource Identifiers and Descriptor Sequences, a key to what is becoming a standard within the internet digital identity layer: Using XRI and XRDS together to create abstract structured identifiers. “ XRI and XRDS have become XRI is the interface, or abstract identifier containing essential elements of the metadata to describe the resource. XRDS is the standard providing the discovery process derived Higgins Project. Without them, from the the XRI interface. Together and separate we couldn’t fully implement the these two standards have become key building abstract data model that is the blocks of the internet identity layer, and provided synergy with other Oasis specifications. heart of Higgins and the key to the user-controlled identity and XRI is a new type of internet identifier, built upon data sharing. the latest IRI standard and designed expressively to - Paul Trevithick” XRI work with digital identity. XRI is an open standard Higgins Progect Lead for expressing and discovering Abstract Structured identifiers. What is XRI Authority Path Subsegment Subsegment Cross Reference @cordance*drummond/(+blog) Global Context Separator Tag service Idenififer fig. 1 Abstract - Identifiers which are known to resolve to other identifiers, or multiple identifiers which are known to resolve to the same concrete identifier. Structured - Identifiers which may contain self-describing data, using standard building blocks acting like “XML for identifiers”. The specification allows for: Persistence- Identifiers which are still abstract and discoverable, yet are not re-assignable throughout the life of object. For example, XRI contains built in global context identifiers to esolver to organizations, individuals, tagged items and/or persistent items.