Ga!Ng Javascript Mistakes Using HTML5
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Pragmatic Guide to Javascript
www.allitebooks.com What Readers Are Saying About Pragmatic Guide to J a v a S c r i p t I wish I had o w n e d this book when I first started out doing JavaScript! Prag- matic Guide to J a v a S c r i p t will take you a big step ahead in programming real-world JavaScript by showing you what is going on behind the scenes in popular JavaScript libraries and giving you no-nonsense advice and back- ground information on how to do the right thing. W i t h the condensed years of e x p e r i e n c e of one of the best JavaScript developers around, it’s a must- read with great reference to e v e r y d a y JavaScript tasks. Thomas Fuchs Creator of the script.aculo.us framework An impressive collection of v e r y practical tips and tricks for getting the most out of JavaScript in today’s browsers, with topics ranging from fundamen- tals such as form v a l i d a t i o n and JSON handling to application e x a m p l e s such as mashups and geolocation. I highly recommend this book for anyone wanting to be more productive with JavaScript in their web applications. Dylan Schiemann CEO at SitePen, cofounder of the Dojo T o o l k i t There are a number of JavaScript books on the market today, b u t most of them tend to focus on the new or inexperienced JavaScript programmer. -

THE FUTURE of SCREENS from James Stanton a Little Bit About Me
THE FUTURE OF SCREENS From james stanton A little bit about me. Hi I am James (Mckenzie) Stanton Thinker / Designer / Engineer / Director / Executive / Artist / Human / Practitioner / Gardner / Builder / and much more... Born in Essex, United Kingdom and survived a few hair raising moments and learnt digital from the ground up. Ok enough of the pleasantries I have been working in the design field since 1999 from the Falmouth School of Art and onwards to the RCA, and many companies. Ok. less about me and more about what I have seen… Today we are going to cover - SCREENS CONCEPTS - DIGITAL TRANSFORMATION - WHY ASSETS LIBRARIES - CODE LIBRARIES - COST EFFECTIVE SOLUTION FOR IMPLEMENTATION I know, I know, I know. That's all good and well, but what does this all mean to a company like mine? We are about to see a massive change in consumer behavior so let's get ready. DIGITAL TRANSFORMATION AS A USP Getting this correct will change your company forever. DIGITAL TRANSFORMATION USP-01 Digital transformation (DT) – the use of technology to radically improve performance or reach of enterprises – is becoming a hot topic for companies across the globe. VERY DIGITAL CHANGING NOT VERY DIGITAL DIGITAL TRANSFORMATION USP-02 Companies face common pressures from customers, employees and competitors to begin or speed up their digital transformation. However they are transforming at different paces with different results. VERY DIGITAL CHANGING NOT VERY DIGITAL DIGITAL TRANSFORMATION USP-03 Successful digital transformation comes not from implementing new technologies but from transforming your organisation to take advantage of the possibilities that new technologies provide. -

IADIS Conference Template
www.seipub.org/ie Information Engineering (IE) Volume 3, 2014 Performance and Quality Evaluation of jQuery Javascript Framework Andreas Gizas, Sotiris P. Christodoulou, Tzanetos Pomonis HPCLab, Computer Engineering & Informatics Dept., University of Patras Rion, Patras Received Jun 10, 2013; Revised Jun 21, 2013; Accepted Mar 12, 2014; Published Jun 12, 2014 © 2014 Science and Engineering Publishing Company Abstract devices. Mobile web is the name of this new field of The scope of this work is to provide a thorough web applications and JavaScript is expected to play a methodology for quality and performance evaluation of the major role in its development with the evolution of most popular JavaScript framework, the jQuery Framework, new devices and standards (ex. iPhone, Android) or as by taking into account well established software quality the heart of cross platform applications (like factors and performance tests. The JavaScript programming phonegap.com). There are also proposals for language is widely used for web programming and employing JavaScript in server-side applications increasingly, for general purpose of computing. Since the (Server-Side JavaScript Reference v1.2). growth of its popularity and the beginning of web 2.0 era, many JavaScript frameworks have become available for Due to the plethora of applications that JavaScript programming rich client-side interactions in web serves and the variety of programming needs, applications. The jQuery project and its community serve frameworks have been created in order to help both today as a major part of web programmers. The main programmers and end-users. These frameworks aim to outcome of this work is to highlight the pros and cons of be a useful tool for simplifying JavaScript code jQuery in various areas of interest and signify which and development and repeat blocks of code by using just a where the weak points of its code are. -

Download Ebook ^ Javascript: Ajax, Cross-Site Scripting, Couchdb
W5CAMG0U1NWQ < PDF ^ JavaScript: Ajax, Cross-Site Scripting, CouchDB, WebKit, JQuery, Dojo Toolkit, Bookmarklet, ActionScript, V8,... JavaScript: A jax, Cross-Site Scripting, Couch DB, W ebKit, JQuery, Dojo Toolkit, Bookmarklet, A ctionScript, V 8, SpiderMonkey, Qooxdoo, Ext JS Filesize: 7.09 MB Reviews It becomes an amazing book which i actually have at any time study. It is actually loaded with wisdom and knowledge You wont sense monotony at at any time of your respective time (that's what catalogues are for regarding should you request me). (Rosina Schowalter V) DISCLAIMER | DMCA EUQW6UIGSWMD > Kindle « JavaScript: Ajax, Cross-Site Scripting, CouchDB, WebKit, JQuery, Dojo Toolkit, Bookmarklet, ActionScript, V8,... JAVASCRIPT: AJAX, CROSS-SITE SCRIPTING, COUCHDB, WEBKIT, JQUERY, DOJO TOOLKIT, BOOKMARKLET, ACTIONSCRIPT, V8, SPIDERMONKEY, QOOXDOO, EXT JS Books LLC, Wiki Series, 2011. Condition: New. This item is printed on demand for shipment within 3 working days. Read JavaScript: Ajax, Cross-Site Scripting, CouchDB, WebKit, JQuery, Dojo Toolkit, Bookmarklet, ActionScript, V8, SpiderMonkey, Qooxdoo, Ext JS Online Download PDF JavaScript: Ajax, Cross-Site Scripting, CouchDB, WebKit, JQuery, Dojo Toolkit, Bookmarklet, ActionScript, V8, SpiderMonkey, Qooxdoo, Ext JS R6UOTKQRMAXT « PDF \ JavaScript: Ajax, Cross-Site Scripting, CouchDB, WebKit, JQuery, Dojo Toolkit, Bookmarklet, ActionScript, V8,... See Also A Smarter Way to Learn JavaScript: The New Approach That Uses Technology to Cut Your Effort in Half Createspace, United States, 2014. Paperback. Book Condition: New. 251 x 178 mm. Language: English . Brand New Book ***** Print on Demand *****.The ultimate learn-by-doing approachWritten for beginners, useful for experienced developers who want to... Read PDF » Why We Hate Us: American Discontent in the New Millennium Random House USA Inc, United States, 2009. -
Ajax, State of The
AjAjaax,x, ststaattee ooff tthhee aarrtt Tarek Ziadé, Nuxeo [email protected] WWhhoo aamm ii ● I am engineer at Nuxeo ● I work on CPS, the famous ECM Plateform ;) ● I©ve been lately in charge of Ajax stuff in CPS ● I read Ajax related feeds before I go to bed WWhhaatt iiss AAjjaaxx ?? A dutch football club (a good one) A cleanser (really works) AA WWeebb 22..00 tteechchnnoollooggyy Asynchronous Javascript And XML WWhhaatt©©ss WWeebb 22..00 ?? TTiimm OO©©RReeiillllyy©©ss ©©ccoommppaacctt©© ddeeffiinniittiioonn:: Web 2.0 is the network as platform, spanning all connected devices; Web 2.0 applications are those that make the most of the intrinsic advantages of that platform: delivering software as a continually-updated service that gets better the more people use it, consuming and remixing data from multiple sources, including individual users, while providing their own data and services in a form that allows remixing by others, creating network effects through an "architecture of participation," and going beyond the page metaphor of Web 1.0 to deliver rich user experiences. MMaarrkkuuss AAnnggeerrmmeeiieerr©©ss vviieeww ooff WWeebb 22..00:: (courtesy of Markus Angermeier) WWeebb 22..00 AAppppss ✔ del.icio.us ✔ flickr ✔ Voo2do ✔ Digg ✔ Google Mail (Gmail) ✔ Writely ✔ Basecamp ✔ ... AjAjaaxx bbiigg ppiictctuurere 11//22 (courtesy of J. J. Garett) AjAjaaxx bbiigg ppiictctuurere 22//22 (courtesy of J. J. Garett) TThhee LLiistst ooff tthhiinnggss AjAjaaxx rereaallllyy bbririnnggss ✔ Increases interactivity ✔ Save bandwidth ✔ Helps avoiding some interactive -
Qooxdoo Interview Questions and Answers Guide
Qooxdoo Interview Questions And Answers Guide. Global Guideline. https://www.globalguideline.com/ Qooxdoo Interview Questions And Answers Global Guideline . COM Qooxdoo Job Interview Preparation Guide. Question # 1 What is Qooxdoo? Answer:- qooxdoo is an open source Ajax web application framework. It is an LGPL- and/or EPL-licensed multipurpose framework that includes support for professional JavaScript development, a graphical user interface (GUI) toolkit and high-level client-server communication. Read More Answers. Question # 2 Is qooxdoo freely available? Answer:- Yes. qooxdoo is Open Source, dual-licensed under LGPL/EPL, i.e. the "GNU Lesser General Public License (LGPL)" and the "Eclipse Public License (EPL)". As a recipient of qooxdoo, you may choose which license to receive the code under. Read More Answers. Question # 3 Who developed qooxdoo? Answer:- qooxdoo was initiated and is maintained by 1&1, the world's biggest web hosting company. There is a team of full-time core developers as well as many committers and contributors. Read More Answers. Question # 4 Which browsers are supported? Answer:- A qooxdoo application runs in all major web browsers - with identical look & feel. Read More Answers. Question # 5 Does qooxdoo come with a server? Answer:- No. If you already have an existing backend that serves HTTP (or HTTPS) requests, it's probably fine to continue using it. Optionally qooxdoo offers several RPC servers for an elegant client-server communication. BTW, during development of your client application the local file system often is sufficient, without the need to use a real server. Read More Answers. Question # 6 What languages and technologies do we need to know? Answer:- Not many. -
Comparing Javascript Libraries
www.XenCraft.com Comparing JavaScript Libraries Craig Cummings, Tex Texin October 27, 2015 Abstract Which JavaScript library is best for international deployment? This session presents the results of several years of investigation of features of JavaScript libraries and their suitability for international markets. We will show how the libraries were evaluated and compare the results for ECMA, Dojo, jQuery Globalize, Closure, iLib, ibm-js and intl.js. The results may surprise you and will be useful to anyone designing new international or multilingual JavaScript applications or supporting existing ones. 2 Agenda • Background • Evaluation Criteria • Libraries • Results • Q&A 3 Origins • Project to extend globalization - Complex e-Commerce Software - Multiple subsystems - Different development teams - Different libraries already in use • Should we standardize? Which one? - Reduce maintenance - Increase competence 4 Evaluation Criteria • Support for target and future markets • Number of internationalization features • Quality of internationalization features • Maintained? • Widely used? • Ease of migration from existing libraries • Browser compatibility 5 Internationalization Feature Requirements • Encoding Support • Text Support -Unicode -Case, Accent Mapping -Supplementary Chars -Boundary detection -Bidi algorithm, shaping -Character Properties -Transliteration -Charset detection • Message Formatting -Conversion -IDN/IRI -Resource/properties files -Normalization -Collation -Plurals, Gender, et al 6 Internationalization Feature Requirements -

A Fully In-Browser Client and Server Web Application Debug and Test Environment
LIBERATED: A fully in-browser client and server web application debug and test environment Derrell Lipman University of Massachusetts Lowell Abstract ging and testing the entire application, both frontend and backend, within the browser environment. Once the ap- Traditional web-based client-server application devel- plication is tested, the backend portion of the code can opment has been accomplished in two separate pieces: be moved to the production server where it operates with the frontend portion which runs on the client machine has little, if any, additional debugging. been written in HTML and JavaScript; and the backend portion which runs on the server machine has been writ- 1.1 Typical web application development ten in PHP, ASP.net, or some other “server-side” lan- guage which typically interfaces to a database. The skill There are many skill sets required to implement a sets required for these two pieces are different. modern web application. On the client side, initially, the In this paper, I demonstrate a new methodology user interface must be defined. A visual designer, in con- for web-based client-server application development, in junction with a human-factors engineer, may determine which a simulated server is built into the browser envi- what features should appear in the interface, and how to ronment to run the backend code. This allows the fron- best organize them for ease of use and an attractive de- tend to issue requests to the backend, and the developer sign. to step, using a debugger, directly from frontend code into The language used to write the user interface code is backend code, and to debug and test both the frontend most typically JavaScript [6]. -
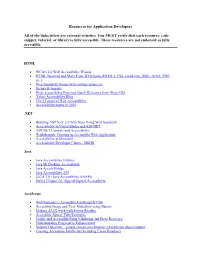
Resources for Application Developers All of the Links Below Are External
Resources for Application Developers All of the links below are external websites. You MUST verify that each resource, code snippet, tutorial, or library is fully accessible. These resources are not endorsed as fully accessible. HTML WCAG 2.0 Web Accessibility Wizard HTML Tutorials and More From W3Schools (HTML5, CSS, JavaScript, XML, AJAX, PHP, etc.) Web Standards Group (web coding resources) Scripts & Applets Web Accessibility Practices Quick Reference from Web-AIM Yahoo Accessibility Blog The 5 Layers of Web Accessibility Accessibility myths in 2010 .NET Building ASP.NET 2.0 Web Sites Using Web Standards Accessibility in Visual Studio and ASP.NET ASP.NET Controls and Accessibility Walkthrough: Creating an Accessible Web Application Accessibility at Microsoft Accessibility Developer Center - MSDN Java Java Accessibility Utilities Java SE Desktop Accessibility Java Access Bridge Java Accessibility API JLCA 3.0 - Java Accessibility (JAAPI) Swing Chapter 24. (Special topics) Accessibility JavaScript Web Semantics: Accessible JavaScript & CSS Accessible Image and Text Slideshow using JQuery Making AJAX work with Screen Readers Accessible JQuery Tabs Examples Usable and Accessible Form Validation and Error Recovery Understanding Progressive Enhancement Support Detection – simple checks on a browser’s JavaScript object support Creating Accessible JavaScript (Including Event Handlers) iCITA: Scripting Best Practices Progressive Enhancement: What It Is, And How To Use It? Slideshow With Buttons Replacing <noscript> -

Ext-JS Job Interview Questions and Answers
Ext-JS Job Interview Questions And Answers Interview Questions Answers https://interviewquestionsanswers.org/ About Interview Questions Answers Interview Questions Answers . ORG is an interview preparation guide of thousands of Job Interview Questions And Answers, Job Interviews are always stressful even for job seekers who have gone on countless interviews. The best way to reduce the stress is to be prepared for your job interview. Take the time to review the standard interview questions you will most likely be asked. These interview questions and answers on Ext-JS will help you strengthen your technical skills, prepare for the interviews and quickly revise the concepts. If you find any question or answer is incorrect or incomplete then you can submit your question or answer directly with out any registration or login at our website. You just need to visit Ext-JS Interview Questions And Answers to add your answer click on the Submit Your Answer links on the website; with each question to post your answer, if you want to ask any question then you will have a link Submit Your Question; that's will add your question in Ext-JS category. To ensure quality, each submission is checked by our team, before it becomes live. This Ext-JS Interview preparation PDF was generated at Saturday 6th February, 2021 You can follow us on FaceBook for latest Jobs, Updates and other interviews material. www.facebook.com/InterviewQuestionsAnswers.Org Follow us on Twitter for latest Jobs and interview preparation guides. https://twitter.com/InterviewQA If you need any further assistance or have queries regarding this document or its material or any of other inquiry, please do not hesitate to contact us. -

Javascript for Web 2.0 Development Introduction
"Web Age Speaks!" Webinar Series JavaScript for Web 2.0 Development Introduction Mikhail Vladimirov Director, Curriculum Architecture [email protected] Web Age Solutions Providing a broad spectrum of regular and customized training classes in programming, system administration and architecture to our clients across the world for over ten years ©WebAgeSolutions.com 2 Overview of Talk Overview of ECMAScript 6 release Hybrid Mobile Web Development Overview of Popular JavaScript libraries: jQuery AngularJS Modernizr _Underscore.js ©WebAgeSolutions.com 3 JavaScript for Web 2.0 Development Some JavaScript Facts Who Owns JavaScript Name The "JavaScript" name is a trademark now owned by Oracle Corporation (US Patent and Trademark Office, copyright entry #75026640). ©WebAgeSolutions.com 5 ECMAScript… JavaScript is un-related to Java It was originally designed by Netscape to add scripting to their browser. It was called 'LiveScript'. Re-naming it to JavaScript was a marketing trick to get more attention to it It is more of a “Lisp in C's Clothing” with elements of functional programming (http://javascript.crockford.com/javascript.html ) Each browser’s JavaScript engine is an attempt to implement ECMAScript standard (first draft in 1997) Well-known implementations are JavaScript, JScript and ActionScript ©WebAgeSolutions.com 6 ECMAScript Release 6 (Work in Progress) Classes and modules ( import {func1} from ‘js/mylib’ ) Better variable scoping (let for the new block scope) Multiple return values (return {x, y}) -
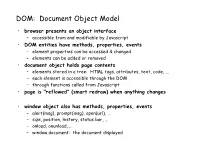
DOM: Document Object Model
DOM: Document Object Model • browser presents an object interface – accessible from and modifiable by Javascript • DOM entities have methods, properties, events – element properties can be accessed & changed – elements can be added or removed • document object holds page contents – elements stored in a tree: HTML tags, attributes, text, code, ... – each element is accessible through the DOM – through functions called from Javascript • page is "reflowed" (smart redraw) when anything changes • window object also has methods, properties, events – alert(msg), prompt(msg), open(url), ... – size, position, history, status bar, ... – onload, onunload, ... – window.document: the document displayed Basic events on forms <head> <script> function setfocus() { document.srch.q.focus(); } </script> </head> <body onload='setfocus();'> <H1>Basic events on forms</H1> <form name=srch action="http://www.google.com/search?q="+srch.q.value> <input type=text size=25 id=q name=q value="" onmouseover='setfocus()'> <input type=button value="Google" name=but onclick='window.location="http://www.google.com/ search?q="+srch.q.value'> <input type=button value="Wikipedia" name=but onclick='window.location="http://en.wikipedia.com/ wiki/"+srch.q.value'> <input type=reset onclick='srch.q.value=""' > </form> More examples... • in a form: <form> <input type=button value="Hit me" onClick='alert("Ouch! That hurt.")'> <P> <input type=text name=url size=40 value="http://"> <input type=button value="open" onClick='window.open(url.value)'> <P> <input type=text name=url2 size=40 value="http://"> <input type=button value="load" onClick='window.location=url2.value'> <P> <input type=button value="color it " onClick='document.bgColor=color.value'> <input type=text name=color value='type a color'> <input type=button value='make it white' onClick='document.bgColor="white"'> </form> • in a tag <body onLoad='alert("Welcome to my page")'> • on an image <img src="smiley.jpg" onMouseover='src="frowny.gif"' onMouseout='src="smiley.jpg"'> • etc.